Find Lan device IP in WAN Interface Logs
-
I was trying to find solution other than activating suricata on many Lan interfaces as it will consume much ram and i have limited ram .. so activated it on wan to save ram ... But it will be weird to not able to find any kind of logs to show this detailed WAN LAN traffic !!
-
@tomdd33 ips has no insight into what initiated the traffic when on wan. It only sees the packets leaving the wan.
You could also log allowed traffic on the lan side, now the firewall will have a log of all outbound traffic from the lan - and you can see who went where, even after the state has gone away.
-
I will try that .. thanks for the tip
-
@tomdd33 think of it this way.
If "someone" writes a letter in a house, and put its in an envelope for the mail man to pick up in their mailbox. While the mailman knows hey this letter is from this house 123 on Bourbon Street. And hey it says its from billy (the source port for example).. Does he really know who wrote the letter inside the house, maybe it was billys wife susan, or their son kevin..
The mailman only knows whats on the outside of the envelope..
-
Yes i get what you clarify but my thoughts was that all these small transitions are under one big box which is pfsense core so i thought there might be some sort of logs for these transitions ... But of course suricata itself won't be able to determine that on its own from wan side
-
@tomdd33 what your asking might be possible looking at the big picture sure.. But then again the IPS is just a package running on pfsense. Its not actually "part" of pfsense.
Not like the info is not there - but the IPS would have to grab that info, say maybe from the state table - and then log that on its own so you could look in the ips and see it all correlated for you.
Maybe @bmeeks could chime in on such a feature.. He is the man when it comes to the ips packages on pfsense.
I know this subject has come up before - and the solution if you want to see who created traffic that ips alerts/blocks/etc you need to run the ips instance on the lan side.
-
Regarding logging traffic, what is the best way to do so ?
-
@tomdd33 if you want to see everything allowed, prob just easy to enable pass logging
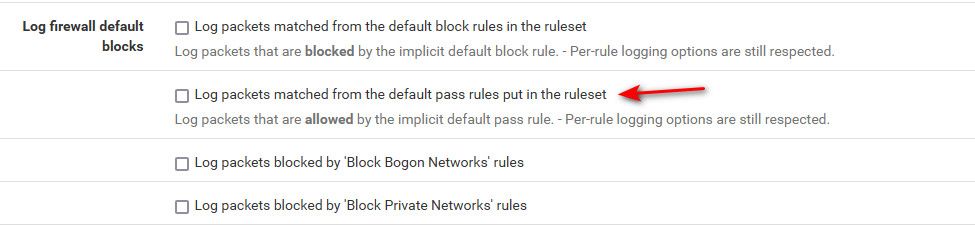
Or you can just go into your interface rules and set whatever rule you have allowing traffic to actually log. By default when you create new rules they are not set to log.
-
Using ntop-ng will get you all the data you might want but if you're already RAM limited I wouldn't recommend that.
You can always export everything using netflow to external netflow server if you really want to log everything.
Steve
-
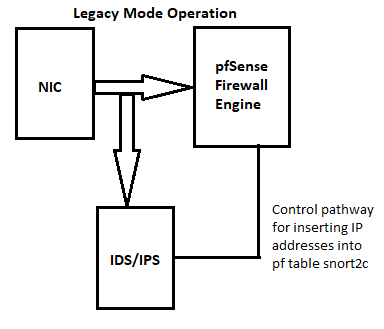
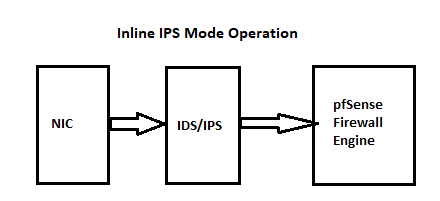
Since I was tagged in this thread, I'll take a second and repeat the description of how the IDS/IPS packages (Snort and Suricata) are plumbed up.
The packages receive inbound traffic directly from the NIC on an interface BEFORE that traffic hits the firewall. For outbound traffic on an interface, it's exactly the opposite. The IDS/IPS sees it after the firewall has processed it.
This really only matters when you run the IDS/IPS on the WAN. In that scenario the IDS/IPS will see inbound traffic BEFORE the firewall has processed it. So all the inbound destination IP addresses will be the WAN's public IP (assuming you are using NAT). For outbound traffic heading towards the Internet, the IDS/IPS will see all the source IP addresses as being the WAN's public IP (again, assuming NAT is in use) because by the time the IDS/IPS sees the traffic NAT has already been applied.
Thus, to see local network hosts show up in alerts with their native local IP, it is better to run the IDS/IPS on an internal firewall interface (LAN, DMZ, etc.). You really never need an instance on your WAN. The IDS/IPS is not to protect your firewall after all. If your firewall needs an IDS/IPS to protect it, perhaps you need to consider a different firewall ...
 . When you run an instance on an internal interface, all traffic still must traverse the IDS/IPS in order to reach hosts hanging off that interface, so security is not reduced.
. When you run an instance on an internal interface, all traffic still must traverse the IDS/IPS in order to reach hosts hanging off that interface, so security is not reduced.I have frequently shared these two diagrams that illustrate the traffic flow for both Legacy Blocking Mode and Inline IPS Mode.
-
@bmeeks said in Find Lan device IP in WAN Interface Logs:
perhaps you need to consider a different firewall
This applies in another way to this thread. He states that his box doesn't have the resources to run on multiple interfaces.
So a bigger box that could do what he wants to do would solve the problem ;)
Another option would be to route downstream between his multiple networks, and just use a transit from this downstream router to pfsense where the IPS runs. Now it would see all traffic going to the internet, and only be on 1 interface.
Problem with that solution is you loose pfsense firewall ability between local networks unless you were running another instance of pfsense as the downstream router, and ips would not see any inter vlan traffic either. Just stuff going outbound..
-
I think bigger box would be fine .. keep in mind i virtualized pfsense vm on a server with 5GB of ram just for it anly 2 instances of suricata activated one on wan and other on one of my lan interfaces and that consumes about 3GB on normal and adding one more instance increase it to 4.5 and go to swap part :D