No WAN access from inside LANs...
-
@njaimo said in No WAN access from inside LANs...:
that pfSense decided the laptop was "persona non-grata" and then wrote its MAC address in a database used to block access to the interfaces on the firewall ?
No.. are you running a captive portal - if so then you could block a mac..
Does the laptop get a IP from pfsense dhcp server? Are you running static arp in the dhcp server? do you have anything set for deny unknowns or the like in dhcp server?
pfsenes doesn't have a db of macs that it just magically says not going to talk to this guy ;)
-
@johnpoz Thanks for the tips !
not running captive portal, but do have Static ARP option checked on the DHCP Server service page on all 3 interfaces, though not sure what I did, nor what it does.... should I uncheck it ?
..?
-
@njaimo said in No WAN access from inside LANs...:
though not sure what I did, nor what it does....
Then why would you of checked it?
Static as it clearly states - "Only the machines listed below will be able to communicate with the firewall on this interface."
Ie the ones you had created reservations for.. in the static mappings section at the bottom of the dhcp server settings page.
Yes you should uncheck using static arp - unless you clear on what it does and why you would want to use it ;)
-
@johnpoz ...got it. I do have static IP's specified for the 2 other nets (LAN, and IOT), and do have the same box chacked on those, as well as the box on each static IP specifying "create a static ARP table entry".
So went ahead and unchecked the Static ARP option on the DMZ interface, where I have no Static IP entries on the DHCP server page., saved,, and then reconnected the laptop network app, it aquired a DHCP lease (192.168.4.11), but I am still unable to ping the interface gateway (192.168.4.1)... and still no internet access...
-
@njaimo what are you rules on your dmz interface? New interfaces have no rules like the default any on the lan. You have to create them - so unless you have a rule that allows it you would not be able to ping.
btw just creating reservations doesn't mean you should use static arp - going to make it painful adding any new machines, etc. Static arp is a specific use case - where you want complete control and help preventing anything from changing its mac to bypass firewall rules and use a different IP, etc. It really has no use on a home network, even one locked down.. It is to used to mitigate a specific type of attack or issue that might be seen on a network.. Again unless you specifically understand what it is and what it does and why you would want to use it - I would suggest you not set that.
-
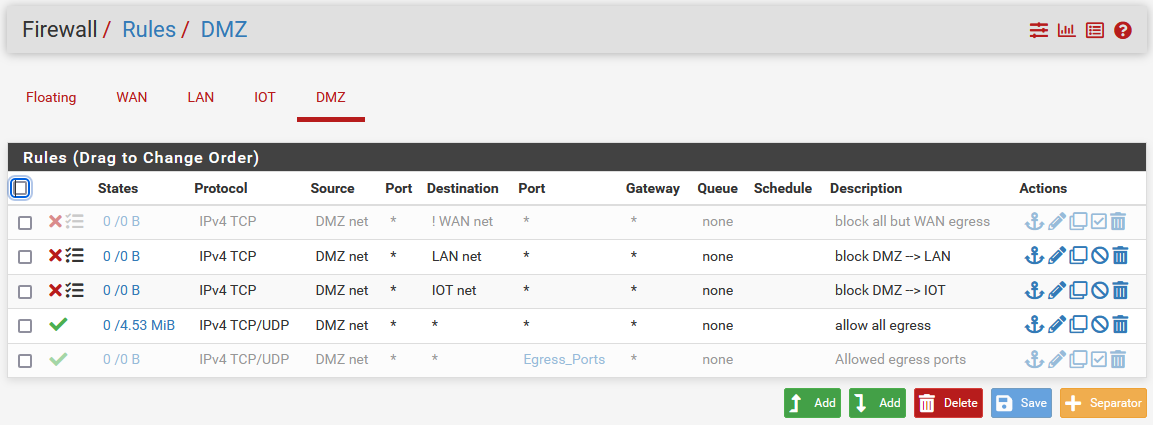
@johnpoz here they are, I am blocking traffic to the two other nets, to keep it isolated
-
@njaimo tcp/udp is not icmp - so no those rules would not allow you to ping anything really.
-
@johnpoz ....got it on the ARP, Thank You. Let me change the rule and check.
-
@njaimo btw see my edit above about static arp.. Unless you have a specific use case that would call for that, it really shouldn't be checked.
-
success ! Where can I send you a beer ? ..or two ?
wondering though, while having specified the TCP/UDP traffic as I have it above, should I have not had internet access ? like Google ?
-
@njaimo yeah those would allow access to the internet for tcp/udp, but not if you had your static arp issue, etc. And your blocking access to lan and iot - what are you pointing to for dns on this dmz.. If it was say your lan IP then no you wouldn't of been able to use dns. Which kind of needed to get to say www.google.com ;)
Or if you if you had messed with your outbound nat rules, and taken them off auto without correctly setting nat, etc.
-
learned something new, Thank You !! Thank you All !
-
@njaimo so you're all sorted? If you are unclear on what some feature does, some advice ;) Ask before clicking it - hahah
-
@johnpoz ...got it ! :) Thanks.
BTW -- one more stupid question while I am in the hole for now... ?
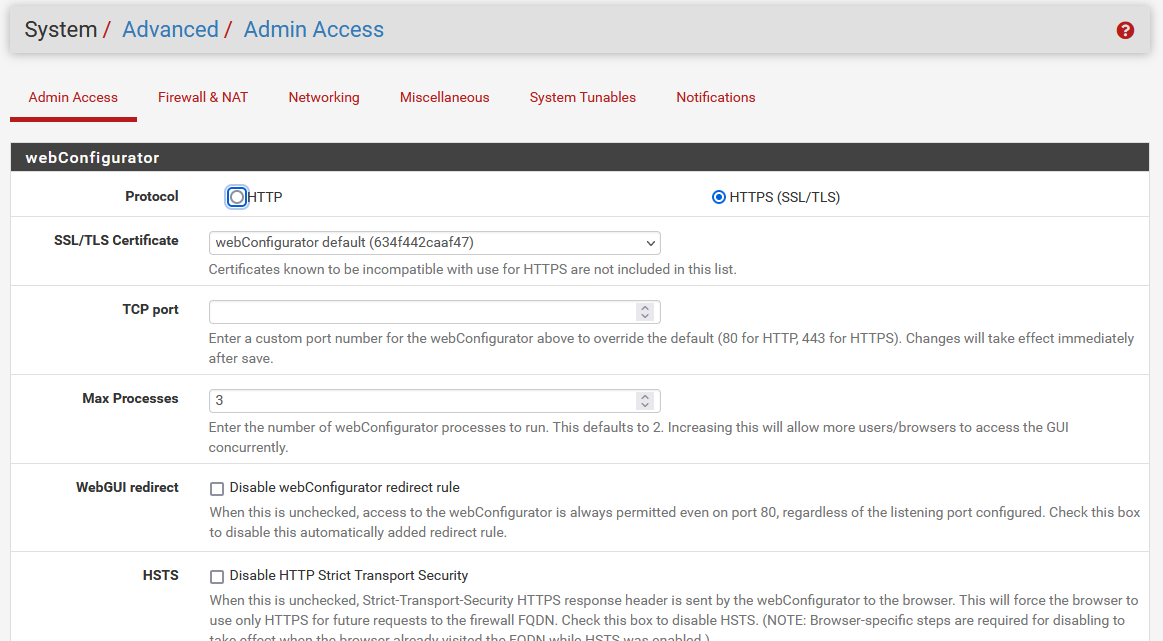
Logging into the pfSense GUI via https, if I screw up my password just once, I get locked out for a time... I have looked where I can maybe change this, but have not been able to find it, which is why I had created yet another user with a different password, but it did not help, once I got locked out, I could not even try an alternate user... What am I screwing up on ?
-
@njaimo hmmm - I have never ran into such a thing.. But then again I don't have that enabled.. Nobody can get to my gui but my machine anyway ;)
https://docs.netgate.com/pfsense/en/latest/config/advanced-admin.html#login-protection
Is that something else you clicked on? ;) I don't recall if that is enabled by default - I wouldn't think so?? But long time since I have used default configs, since when I update even when clean I normally load my last config, etc.
edit: hmm looks like it is enabled by default - did you alter the default settings?
edit2: I just added my PC IP to bypass list, just in case ;) As you say we learn something new everyday - heheh
edit3: And I use a password manager to enter the password, which is quite long and complex that would be just a PITA to enter by hand.. So I can not recall the last time I would of entered the password wrong ;)
-
@johnpoz ...since this is my home, I do not have had need to use ssh from outside, and figured it woudl be easiest to access the GUI via https and a web browser in the net. ...ANd I had a bad case of "click-itis"... LOL
I see there is a max of "10" down in "login protection" on the same page, but I get locked out after the first try, and it takes about 30 minutes to let me try again... I do not recall editing any default settings on this...
-
@njaimo not sure what ssh has to do with anything? Did you open the webgui to the internet?
Did you look in your log for login attempts? What does it say your level of attack was?
-
Your IP will get blocked by sshguard for a few minutes if you try to login and fail three times. If you then fail again it will block you for longer.
You can just add your IP to the whitelist to prevent sshguard triggering against it.sshguard monitors all login attempts not just ssh, confusingly!
Steve
-
Thank you for the replies ! ...sorry for the delay, had to be away from home this morning.
I get blocked after just one failed login (seems its been like that for years) but I do can log in from the other net, which I had not tried before, thank you for that tip. Here is the log, seems the failed logging is considered a level-10
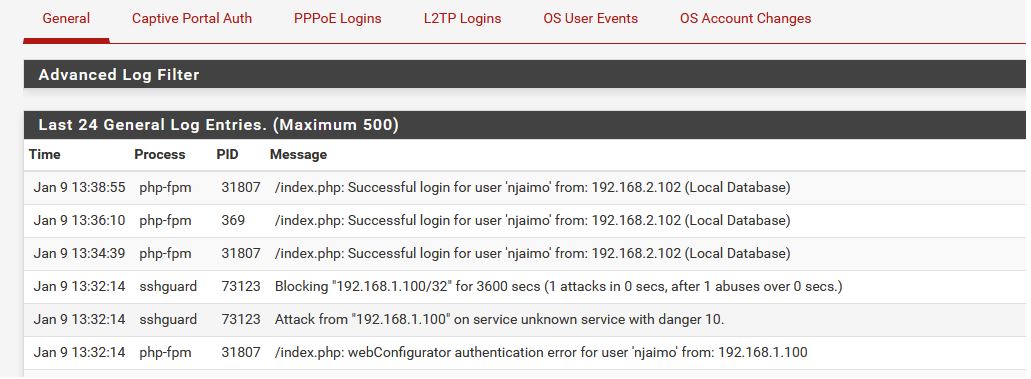
-
this is what I enter to access while on Firefox browser
https://192.168.1.1/index.php