Multiple IPv6 Prefix Delegation over AT&T Residential Gateway for pfSense 2.4.5
-
Thank you for making me aware of this. Everything is working great.
Here is a link to a DUID generator that I found. -
I thought everything was working great. The bridge mode is working perfectly.
IPv6 is another story. I get IPV6 address on WAN and LAN but when I go to test it at various sites it fails. I have everything configured per the Netgate guide that @ttmcmurry posted.
Do I need to enable the DHCPv6 server? The guide did not state anything about that. -
@AiC0315 The recipe here covers prefix acquisition from the ATT Gateway. It's not a full v6 configuration guide for pfSense.
For example, v6 traffic needs to be enabled via System > Advanced > Networking > AllowIPv6 and firewall rules that support v6 have to be created.
Try to figure out where the traffic is being blocked and whether DNS v6 name resolution is working, e.g.,
traceroute -6 www.google.com -
@marcg
Thanks, I was able to find the extra settings. All is working now. -
@ttmcmurry Thanks for the heads-up on this. But looking at the new advanced options I was not able to figure out how to translate the current script into input to the new settings. Would you or someone else be able to create a post on how to do it?
Thanks!
-
I still don't understand the dumbass state limit from att.
first they should migrate all of their RG communication to ipv6 and free the only ipv4 to user
second, they should use STATELESS rules for PD'd ipv6 + ipv4.
this 8k limit feels very much arbitrary, as if it's intended to limit the number of devices for residential users
(it's not an issue for the box to support >1 million states: https://johnleach.co.uk/posts/2009/06/17/netfilter-conntrack-memory-usage/) -
This post is deleted! -
This post is deleted! -
Great write-up and work!
I've got a question on how I'd implement this given my desired configuration. I currently have a Netgate 7100, which has a block of static IPs assigned to the LAN interface, which I'm using as a DMZ. One of the public IPs is assigned to my UniFi UDM SE, which handles the majority of my internal networks.
I'd like to be able to hand off multiple /64 networks from the Netgate 7100 to the UDM SE, so it can then assign them to the various private LANs I have. What would the configuration look like on the pfSense, and is this even possible?
Thanks!
-
-
@johnpoz Thanks for the response. I'm familiar with that article, but the instructions put together by @ttmcmurry seem to indicate the only way to have pfSense request the additional PDs is to assign that request to each of the switch ports on the Netgate 7100. Currently, I've got the switch carved up into two WAN connections, a connection to the DMZ, and an Admin LAN. I don't want to assign anything on the Admin LAN, just the DMZ systems and the second router that is there. Would I just need to have each of the id-assoc pd stanzas all using DMZ as the port, and it would then hand those off to the downstream router?
interface lagg-0.4090 { send ia-na 0; send ia-pd 0; send ia-pd 1; send ia-pd 2; send ia-pd 3; send ia-pd 4; send ia-pd 5; send ia-pd 6; send ia-pd 7; request domain-name-servers; request domain-name; script "/var/etc/dhcp6c_wan_script.sh"; }; id-assoc na 0 { }; id-assoc pd 0 { prefix-interface lagg-0.4091 { sla-id 0; sla-len 0; }; }; id-assoc pd 1 { prefix-interface lagg-0.4091 { sla-id 0; sla-len 0; }; }; ... -
Having issues with CE 2.7.1. I am able to ping from WAN, but no device on LAN can ping out to internet IPv6 address.
LAN device can ping WAN and WAN can ping the LAN device's IPv6 address, but the LAN device can't ping an internet IPv6 address. The LAN interface from pfSense can't even ping the internet IPv6 address.
Also I am able to traceroute from the WAN. Traceroute from the pfSense LAN interface just shows:
1 * * * 2 * * * 3 * * *This was working on a prior pfSense+, but since I've lost all data on my server I have had to start from scratch.
Can someone please help? I'm pulling my hair out over this nonsense.
-
@fox-hound Does
ifconfig -a inet6-- via ssh or Diagnostics>CommandPrompt -- show v6 addresses on the expected interfaces? Do you have LAN-side firewall rules that permit outbound v6 traffic? -
@marcg Yes, both the WAN and LAN interfaces show IPv6 addresses. The LAN-side firewall has the default allow any for IPv6.
Traceroute from a LAN device with an IPv6 address shows the first hop being pfSense, but stops after that:
traceroute to 2001:4860:4860::8888 (2001:4860:4860::8888), 30 hops max, 80 byte packets 1 pfsense.home.lan (2600:1700:1d42:X:X:X:X:3fd) 0.455 ms 0.401 ms 0.347 ms 2 * * * 3 * * * -
@fox-hound Is System>Advanced>Networking>IPv6Options>AllowIPv6 checked?
Does the same traceroute succeed from the BGW's Diagnostics>Troubleshoot>TestInternetAccess dialogue?
-
@marcg Yes it is checked. Traceroute only succeeds from WAN, not from the LAN interface
-
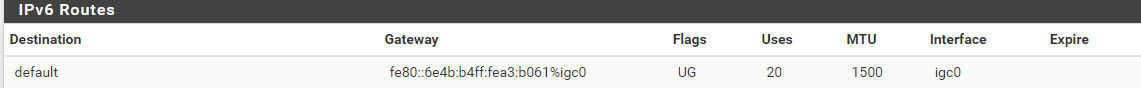
Just double checked the WAN interface for pfSense. It looks like DHCPv6 gave the AT&T router's link-local IPv6 address as the gateway on WAN?
-
@fox-hound I also see the BGW320's LAN-side LLA as the default v6 route on pfSense+ 23.09. The BGW320 is running 4.25.4. v6 is working for me.
-
@marcg Looks like I'm having an issue with the RG.
Checked the logs and my ICMPv6 packets are showing up with the reason: "Policy (filtersets, etc.)".
I had disabled packet filtering and the firewall on the RG, so I'm not sure what is happening.
-
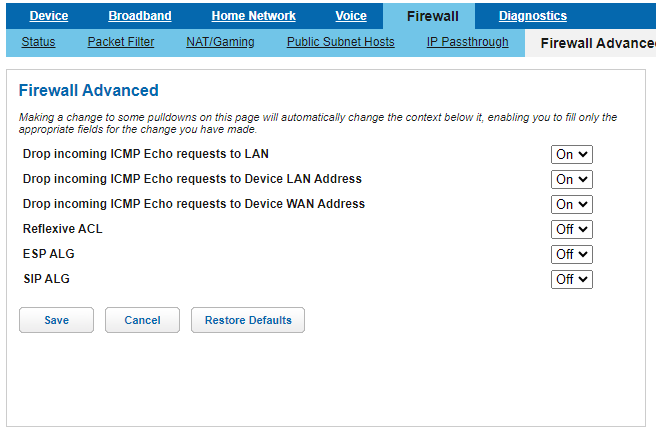
@fox-hound I see those in the logs as well with the BGW320's packet filters disabled. Maybe because of the following settings.
FWIW, I have a suspicion that the BGW sometimes reverses source and destination addresses its state table display and maybe firewall logs. I'll have flows that I know are initiated outwards from the LAN and are listed in the pfSense state table as such, but show as initiated inwards on the BGW. I look at the BGW's logs with a grain of salt. More details here.