After upgrade to pf+ 23.09 Surricata says it's starting but..
-
@frunkAF How are you getting these detailed logs? When I look at suricata.log, it's quite sparse even with verbose logging enabled. Same for the system log:
2023-11-07 14:46:10.910729-05:00 php-fpm 555 Starting Suricata on DMZ(hn5) per user request... 2023-11-07 14:46:11.031247-05:00 php 34566 [Suricata] Updating rules configuration for: DMZ ... 2023-11-07 14:46:11.747641-05:00 php 34566 [Suricata] Enabling any flowbit-required rules for: DMZ... 2023-11-07 14:46:11.786034-05:00 php 34566 [Suricata] Building new sid-msg.map file for DMZ... 2023-11-07 14:46:14.228814-05:00 php 34566 [Suricata] Suricata START for DMZ(hn5)... 2023-11-07 14:46:15.909440-05:00 kernel - pid 40984 (suricata), jid 0, uid 0: exited on signal 11 (core dumped) -
@xpxp2002 said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
@frunkAF How are you getting these detailed logs? When I look at suricata.log, it's quite sparse even with verbose logging enabled. Same for the system log:
2023-11-07 14:46:10.910729-05:00 php-fpm 555 Starting Suricata on DMZ(hn5) per user request... 2023-11-07 14:46:11.031247-05:00 php 34566 [Suricata] Updating rules configuration for: DMZ ... 2023-11-07 14:46:11.747641-05:00 php 34566 [Suricata] Enabling any flowbit-required rules for: DMZ... 2023-11-07 14:46:11.786034-05:00 php 34566 [Suricata] Building new sid-msg.map file for DMZ... 2023-11-07 14:46:14.228814-05:00 php 34566 [Suricata] Suricata START for DMZ(hn5)... 2023-11-07 14:46:15.909440-05:00 kernel - pid 40984 (suricata), jid 0, uid 0: exited on signal 11 (core dumped)Different kinds of information are logged in
suricata.logversus the system log. The Suricata package has two separate components: (1) a binary daemon that is compiled from upstream source code; and (2) a PHP-based GUI package that runs on the pfSense operating system.The PHP code logs things it does to the pfSense system log. The binary Suricata daemon logs its activity mostly to the
suricata.log(but will also log some things to the pfSense system log). -
@bmeeks said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
@frunkAF said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
Whatever '<Error> -- Hyperscan returned fatal error -1.' is seems to be the issue?
Yes. What kind of hardware are you using? Specifically, what is the CPU type and architecture?
Hyperscan is enabled by default in the build options for pfSense. In the past it has not been an issue. There is an outside chance that the hyperscan library is not correct on your system following the update. But that's just one guess.
I would start by removing the package, rebooting the firewall, and then installing the package again to be sure it pulls down all the correct shared libraries. Netgate experienced a prolonged outage at their primary data center last night according to a post elsewhere on the forum. It may be you were affected by that depending on where you are located in the world and how "day time working hours" at your location corresponded to the overnight Netgate network outage.
I'm running an x86 AMD Ryzen 5 4600G.
I removed the package, rebooted, and reinstalled and it looks like so far so good...
Nov 7 11:58:08 suricata 9703 [1:2525008:860] ET 3CORESec Poor Reputation IP group 9 [Classification: Misc Attack] [Priority: 2] {TCP} 168.80.174.100:59081 -> <WAN_IP>:1010 Nov 7 11:58:08 suricata 9703 [1:2400016:3793] ET DROP Spamhaus DROP Listed Traffic Inbound group 17 [Classification: Misc Attack] [Priority: 2] {TCP} 168.80.174.100:59081 -> <WAN_IP>:1010 Nov 7 11:57:39 suricata 9703 [1:2402000:6815] ET DROP Dshield Block Listed Source group 1 [Classification: Misc Attack] [Priority: 2] {TCP} 198.235.24.117:51685 -> <WAN_IP>:40000 Nov 7 11:55:52 suricata 9703 [100935] <Notice> -- Threads created -> RX: 1 W: 12 FM: 1 FR: 1 Engine started. Nov 7 11:55:26 suricata 9703 [100935] <Warning> -- flowbit 'file.onenote' is checked but not set. Checked in 61666 and 1 other sigs Nov 7 11:55:26 suricata 9703 [100935] <Warning> -- flowbit 'file.xls&file.ole' is checked but not set. Checked in 30990 and 1 other sigs Nov 7 11:55:26 suricata 9703 [100935] <Warning> -- flowbit 'file.pdf&file.ttf' is checked but not set. Checked in 28585 and 1 other sigs Nov 7 11:55:26 suricata 9703 [100935] <Warning> -- flowbit 'file.zip&file.silverlight' is checked but not set. Checked in 28582 and 2 other sigs Nov 7 11:55:11 suricata 99330 [100591] <Notice> -- This is Suricata version 7.0.0 RELEASE running in SYSTEM mode Nov 7 11:55:11 SuricataStartup 99192 Suricata START for WAN(43800_ix0)... Nov 7 11:50:39 SuricataStartup 93389 Suricata STOP for WAN(43800_ix0)...Is there a way for me to check the shared libraries I pulled down via a hash or something to see if I am affected?
-
@frunkAF said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
Is there a way for me to check the shared libraries I pulled down via a hash or something to see if I am affected?
No, I don't have the current versions to share with you. If it is running fine, then I suspect a library version was the issue with Hyperscan. I'm pretty sure there was a recent new build of that from Intel.
-
@xpxp2002: I also see in your system log snippet that you appear to be running on a Hyper-V instance since the interface name is
hn5. Your issue might be a problem with Hyper-V settings or an incomplete installation as another user experienced.I would start by removing the Suricata package, rebooting the Hyper-V virtual machine running pfSense, and then install the Suricata package again. It will remember and recover your existing installation settings.
-
@bmeeks Interesting. I didn't realize that interface naming was specific to Hyper-V.
I initially upgraded from 23.05.1 before the outage overnight, and aside from this Suricata issue, everything went smoothly. Been running the same Suricata config here for years.
I did try a reinstall and a reboot separately yesterday, but neither helped. I'll try those steps as you suggested in that order once I can take another quick outage tonight.
-
@xpxp2002 said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
I didn't realize that interface naming was specific to Hyper-V.
Yep. Interfaces named
hnin FreeBSD denote Hyper-V virtual NICs. Other users have reported problems with the latest pfSense versions on Hyper-V. I did not read and digest every post, but I do recall seeing issues posted. I think it mostly has to do with the latest FreeBSD 14-CURRENT kernel, but it might also be a quirk with a package like Suricata that has to talk to the NICs. -
@bmeeks said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
@frunkAF said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
Is there a way for me to check the shared libraries I pulled down via a hash or something to see if I am affected?
No, I don't have the current versions to share with you. If it is running fine, then I suspect a library version was the issue with Hyperscan. I'm pretty sure there was a recent new build of that from Intel.
Can confirm that suricata has now been working all day for me.
Fix was to remove the suricata package, reboot, and reinstall the suricata package.
-
@bmeeks said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
@xpxp2002: I also see in your system log snippet that you appear to be running on a Hyper-V instance since the interface name is
hn5. Your issue might be a problem with Hyper-V settings or an incomplete installation as another user experienced.I would start by removing the Suricata package, rebooting the Hyper-V virtual machine running pfSense, and then install the Suricata package again. It will remember and recover your existing installation settings.
I performed these steps tonight, but after the reinstall Suricata still cores when run in blocking mode.
-
@xpxp2002 said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
I performed these steps tonight, but after the reinstall Suricata still cores when run in blocking mode.
It very well may be a problem within the Hyper-V host. In some of the previous posts I read some folks fixed issues by swapping the type of virtual machine if I recall correctly. Maybe changing from Generation 2 to Generation 1 or something like that ???
I don't run Hyper-V but use VMware instead. There is a history of various issues with Hyper-V and FreeBSD guests.
-
I am also running on hyper-V and had no problem.
But now with another VM on 2.7.1-RC I have that problem (Legacy Mode). It is running on proxmox (which runs on hyper-v). The Available Packages list is empty right now so I can not reinstall Suricata. Will do it ASAP.Edit: Doesn't help in my case, will retry with a fresh config. But now the list is again empty...
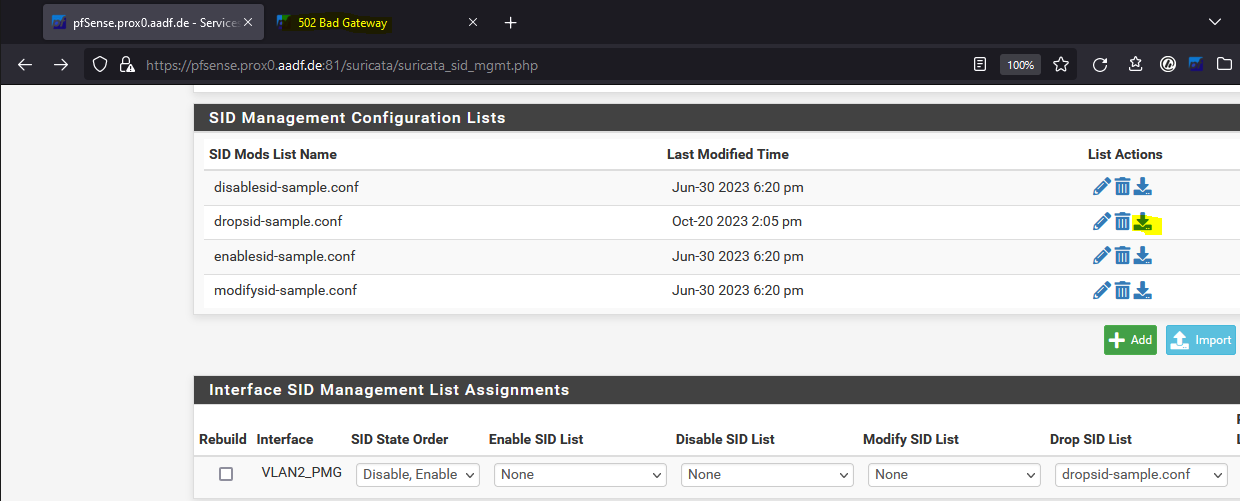
Noticed a download problem with the SID mgmt lists in both, it will give me a 502 error, bad gateway.
Edit: Fresh install without using old config seems to work so far.
-
Running on a Dell PowerEdge R350 with IX Intel 10-Gigabit X540-AT2 nics with the following settings:
- Hardware Checksum Offloading: Enabled
- Hardware TCP Segmentation Offloading: Disabled
- Hardware Large Receive Offloading: Disabled
Things were running fine until the 23.09 update. I tried the above remedies without success. Full uninstall, reboot, reinstall (making sure config was not saved). It definitely happens as soon as you enable blocking. We're using legacy mode and only block SRC ip's on a couple of specific LAN segments with only emerging-p2p.rules enabled. Here's a copy of the brief suricata.log showing the error at the end.
[100377 - Suricata-Main] 2023-11-14 11:06:51 Notice: suricata: This is Suricata version 7.0.0 RELEASE running in SYSTEM mode [100377 - Suricata-Main] 2023-11-14 11:06:51 Info: cpu: CPUs/cores online: 8 [100377 - Suricata-Main] 2023-11-14 11:06:51 Info: suricata: Setting engine mode to IDS mode by default [100377 - Suricata-Main] 2023-11-14 11:06:51 Info: app-layer-htp-mem: HTTP memcap: 67108864 [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Creating automatic firewall interface IP address Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:755a to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface bge0 IPv6 address fe80:0000:0000:0000:c65a:b1ff:fea8:aebb to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface bge0 IPv4 address 10.0.0.33 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface lo0 IPv6 address 0000:0000:0000:0000:0000:0000:0000:0001 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface lo0 IPv6 address fe80:0000:0000:0000:0000:0000:0000:0001 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface lo0 IPv4 address 127.0.0.1 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.653 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.653 IPv4 address 172.16.48.1 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.897 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:755a to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.897 IPv4 address 12.146.29.52 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.895 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:755a to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.895 IPv4 address 12.220.13.22 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.896 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:755a to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.896 IPv4 address 12.220.13.39 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.892 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:755a to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix1.892 IPv4 address 0.0.0.0 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.651 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.401 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.402 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.600 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.647 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.647 IPv4 address 172.16.64.1 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.648 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.650 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.650 IPv4 address 172.16.128.1 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.652 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.654 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.660 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.661 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.700 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Adding firewall interface ix0.711 IPv6 address fe80:0000:0000:0000:a236:9fff:fe7c:7558 to automatic interface IP Pass List. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: logopenfile: alert-pf output device (regular) initialized: block.log [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Loading and parsing Pass List from: /usr/local/etc/suricata/suricata_40419_ix0.650/passlist. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Pass List /usr/local/etc/suricata/suricata_40419_ix0.650/passlist processed: Total entries parsed: 9, IP addresses/netblocks/aliases added to No Block list: 8, IP addresses/netblocks ignored because they were covered by existing entries: 1. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: Created Firewall Interface IP Change monitor thread for auto-whitelisting of firewall interface IP addresses. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-pf: pfSense Suricata Custom Blocking Module initialized: pf-table=snort2c block-ip=src kill-state=yes block-drops-only=no passlist-debugging=no [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: logopenfile: fast output device (regular) initialized: alerts.log [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: alert-syslog: Syslog output initialized [107064 - ] 2023-11-14 11:06:51 Info: alert-pf: Firewall Interface IP Address Change monitoring thread IM#01 has successfully started. [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: detect: 1 rule files processed. 119 rules successfully loaded, 0 rules failed [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: threshold-config: Threshold config parsed: 0 rule(s) found [100428 - Suricata-Main] 2023-11-14 11:06:51 Info: detect: 119 signatures processed. 0 are IP-only rules, 81 are inspecting packet payload, 37 inspect application layer, 0 are decoder event only [100428 - Suricata-Main] 2023-11-14 11:06:52 Info: runmodes: Using 1 live device(s). [107065 - RX#01-ix0.650] 2023-11-14 11:06:52 Info: pcap: ix0.650: running in 'auto' checksum mode. Detection of interface state will require 1000 packets [107065 - RX#01-ix0.650] 2023-11-14 11:06:52 Info: pcap: ix0.650: snaplen set to 1518 [100428 - Suricata-Main] 2023-11-14 11:06:52 Notice: threads: Threads created -> RX: 1 W: 8 FM: 1 FR: 1 Engine started. [107065 - RX#01-ix0.650] 2023-11-14 11:06:52 Info: checksum: No packets with invalid checksum, assuming checksum offloading is NOT used [107067 - W#02] 2023-11-14 11:08:39 Error: spm-hs: Hyperscan returned fatal error -1.You can see that it runs for just a couple of minutes. A suricata.core file does get produced in the /root/ dir. It eventually fails even if I strip it down to a single LAN.
Curious if someone could post the XML of config export from a known working instance. Perhaps there is a specific setting that needs to flip?
Thanks
-
@PalisadesTahoe:
You are hitting a Hyperscan library error according to this entry from the log you posted:[107067 - W#02] 2023-11-14 11:08:39 Error: spm-hs: Hyperscan returned fatal error -1.What version of the Hyperscan library is installed? It should be 5.4.0 if I recall correctly. You can check what's on your system with this command at a shell prompt:
pkg info | grep hyperscanIf you have altered the Pattern Matching algorithm, try setting it back to "Auto".
-
@bmeeks Thank for taking a look. Pattern Matching is set to Auto and is indeed at version 5.4.0:
[23.09-RELEASE][admin@SRV-pfSense-PT]/root: pkg info | grep hyperscan hyperscan-5.4.0 High-performance multiple regex matching library -
@PalisadesTahoe said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
@bmeeks Thank for taking a look. Pattern Matching is set to Auto and is indeed at version 5.4.0:
[23.09-RELEASE][admin@SRV-pfSense-PT]/root: pkg info | grep hyperscan hyperscan-5.4.0 High-performance multiple regex matching libraryI also see you are still running version 7.0.0 of the binary. There is, or will soon be posted, a new 7.0.2 version of the Suricata package. Update to that as soon as it shows up for you.
-
@PalisadesTahoe:
Check out this bug report on the upstream Suricata Redmine: https://redmine.openinfosecfoundation.org/issues/6195. There is a new 7.0.2 version of the Suricata package that should build tonight and show up. That package contains the latest 7.0.2 binary from upstream which contains a fix for the Hyperscan error.Currently you are running the 7.0.0 binary.
-
@bmeeks
I'll give it a go once it shows up, but looking at the bug, it seems related to dealing with a change in a rule pattern after an update which shouldn't be happening to us. But perhaps there are some other bug fixes in 7.0.2 that might remedy this issue. I'll report back after the update is available and applied. Thanks again. Cheers. -
@PalisadesTahoe said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
I'll give it a go once it shows up, but looking at the bug, it seems related to dealing with a change in a rule pattern after an update which shouldn't be happening to us. But perhaps there are some other bug fixes in 7.0.2 that might remedy this issue. I'll report back after the update is available and applied. Thanks again. Cheers.
Since you are using only the ET-Open P2P rules, I can try to see if this is reproducible for me in a virtual machine. Unfortunately I don't have a pfSense Plus test environment. I only have 2.7.0 CE and 2.8.0 CE Development virtual environments to test with.
There was a change made in FreeBSD itself back in August that altered how the kill states system function call works. The Legacy Blocking Code attempts to perform that system call as part of killing the states associated with any IP it adds to the blocking table, snort2c. As an experiment, you could try turning off the Kill States option for the interfaces under the INTERFACE SETTINGS tab. That would bypass calling that modified kernel code. You would need to restart Suricata on the interface after changing and saving that setting. If it works then, that gives me a strong hint of where to concentrate troubleshooting.
The consequence of disabling that option is any active states for a blocked IP will remain open and traffic would continue to flow. So, until the open states timed out, that would essentially convert the IPS to more IDS.
-
@bmeeks
Sad to report that turning off Kill States had no affect. Hyperscan still fails after a few minutes of running. Is it possible to increase debugging of the process in order to get more detail in the logs? Or if you have any other ideas, I'm happy to be the testing lab. Thanks. -
@PalisadesTahoe said in After upgrade to pf+ 23.09 Surricata says it's starting but..:
@bmeeks
Sad to report that turning off Kill States had no affect. Hyperscan still fails after a few minutes of running. Is it possible to increase debugging of the process in order to get more detail in the logs? Or if you have any other ideas, I'm happy to be the testing lab. Thanks.No, there is nothing much to enable debugging wise unless the Suricata binary daemon is compiled with debugging enabled, and we do not do that on the production builds.
Let's see if the 7.0.2 binary makes any difference with respect to the Hyperscan error.
I really thing the Signal 11 core dump is related to killing states in the Legacy Blocking Module. Seeing that in Snort now, and it has the same code. There was a change in FreeBSD in the kill states kernel system call. A Netgate developer made some changes in the Legacy Blocking Module code to sync up with the FreeBSD changes, but I'm thinking those changes might have introduced a bug.