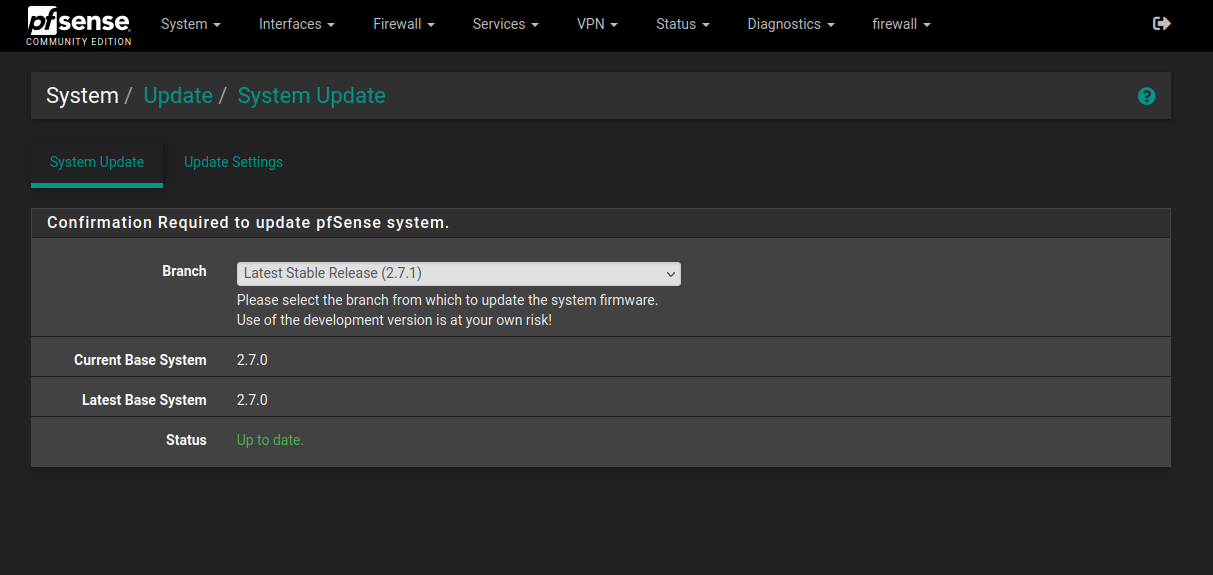
Upgrade pfsense CE 2.7.0 to 2.7.1
-
@reberhar said in Upgrade pfsense CE 2.7.0 to 2.7.1:
I may have found it. The translation address is the virtual IP. This would do as you say. Then only the primary node can receive the update messages.
Translation
Address
192.168.1.254 (WAN VIP)
Type
Connections matching this rule will be mapped to theUsually when we see this the rule has a source of 'any' which is almost always wrong.
-
@GeorgeCZ58 said in Upgrade pfsense CE 2.7.0 to 2.7.1:
So I again take USB mem stick and install 2.7.0, which is working correctly. Any idea ?
Did you try installing 2.7.1 clean?
-
@GeorgeCZ58 said in Upgrade pfsense CE 2.7.0 to 2.7.1:
So I again take USB mem stick and install 2.7.0, which is working correctly. Any idea ? Seems like a lot of changes in "minor" update was done , it should not be 2.7.1, but 2.8.0...
In my own testing with a Fresh Installation of CE 2.7.0 within a VM: I was able to confirm what stephenw10 mentioned:
If you want to remain on 2.7.0 and have pulled in the newer pkg version you will need to set the repo back to 2.7.0 then rehash the certs and force upgrade pkg back to the version from that: 1.19.1_2.
Then you should be able to pull in other pkgs and will not need to rehash certs again.
The Day following CE 2.7.1's Announcement, there were already some System Patches, therefore if you are able to install the "System_Patches" Package and apply them (and Reboot), some of those Patches might apply to this case with your Intel NUC?
Last week with CE 2.7.0 (before I knew about having to rehash the certs following every Boot/reBoot or downgrading to pkg-1.19.1_2), a Fresh Installation of CE 2.7.1 is what had worked for me with my ZimaBoard.
-
@stephenw10 I will try. So practicaly I will do the same, but will not apply old config... we will see.
-
@GeorgeCZ58 said in Upgrade pfsense CE 2.7.0 to 2.7.1:
@stephenw10 I will try. So practicaly I will do the same, but will not apply old config... we will see.
That is the "Power" of pfSense, your OLD Config should work just fine!
-
@SteveITS Thank you!
Precisely the error
Precisely the solution. -
Can the config from 2.7.0 be used in 2.7.1?
-
@Waqar-UK yes, in general restoring to a later version is fine: https://docs.netgate.com/pfsense/en/latest/backup/restore-different-version.html
-
@stephenw10 Actually this rule was created by the wizard when I setup HA. The source is not ANY.
I can understand why this does what it does. I am puzzling how to exactly repair this. Of course the wizard was written by the good netgate folks.
@reberhar said in Upgrade pfsense CE 2.7.0 to 2.7.1:
I may have found it. The translation address is the virtual IP. This would do as you say. Then only the primary node can receive the update messages.
Translation
Address
192.168.1.254 (WAN VIP)
Type
Connections matching this rule will be mapped to theUsually when we see this the rule has a source of 'any' which is almost always wrong.
-
This post is deleted! -
@reberhar said in Upgrade pfsense CE 2.7.0 to 2.7.1:
The source is not ANY.
What exactly is the rule you are using there?
-
@stephenwInterface
I think the 12.0.0.0 ones are for the firewall. I have included the lan ones, but I don't think the problem lives there.
Roy
DisabledDisable this rule
Do not NATEnabling this option will disable NAT for traffic matching this rule and stop processing Outbound NAT rules
In most cases this option is not required.
Interface
WAN
The interface on which traffic is matched as it exits the firewall. In most cases this is "WAN" or another externally-connected interface.
Address Family
IPv4+IPv6
Select the Internet Protocol version this rule applies to.
Protocol
Any
Choose which protocol this rule should match. In most cases "any" is specified.
Source
Network or Alias
Type
127.0.0.0
/
8
Source network for the outbound NAT mapping.
Port or Range
Destination
Any
Type
/
24
Destination network for the outbound NAT mapping.
Port or Range
Not
Invert the sense of the destination match.
Translation
Address
WAN address
Type
Connections matching this rule will be mapped to the specified address. If specifying a custom network or alias, it must be routed to the firewall.
Port or Range
Enter the external source Port or Range used for remapping the original source port on connections matching the rule.Port ranges are a low port and high port number separated by ":".
Leave blank when Static Port is checked.
Static Port
Misc
No XMLRPC Sync
Prevents the rule on Master from automatically syncing to other CARP members. This does NOT prevent the rule from being overwritten on Slave.
Description
Auto created rule - localhost to WAN
A description may be entered here for administrative reference (not parsed).Interface
WAN
The interface on which traffic is matched as it exits the firewall. In most cases this is "WAN" or another externally-connected interface.
Address Family
IPv4+IPv6
Select the Internet Protocol version this rule applies to.
Protocol
Any
Choose which protocol this rule should match. In most cases "any" is specified.
Source
Network or Alias
Type
127.0.0.0
/
8
Source network for the outbound NAT mapping.
Port or Range
Destination
Any
Type
/
24
Destination network for the outbound NAT mapping.
500
Port or Range
Not
Invert the sense of the destination match.
Translation
Address
WAN address
Type
Connections matching this rule will be mapped to the specified address. If specifying a custom network or alias, it must be routed to the firewall.
Port or Range
Enter the external source Port or Range used for remapping the original source port on connections matching the rule.
Port ranges are a low port and high port number separated by ":".
Leave blank when Static Port is checked.
Static Port
Misc
No XMLRPC Sync
Prevents the rule on Master from automatically syncing to other CARP members. This does NOT prevent the rule from being overwritten on Slave.
Description
Auto created rule for ISAKMP - localhost to WAN
A description may be entered here for administrative reference (not parsed).
WAN
The interface on which traffic is matched as it exits the firewall. In most cases this is "WAN" or another externally-connected interface.
Address Family
IPv4+IPv6
Select the Internet Protocol version this rule applies to.
Protocol
Any
Choose which protocol this rule should match. In most cases "any" is specified.
Source
Network or Alias
Type
10.5.0.0
/
24
Source network for the outbound NAT mapping.
Port or Range
Destination
Any
Type
/
24
Destination network for the outbound NAT mapping.
500
Port or Range
Not
Invert the sense of the destination match.
Translation
Address
192.168.1.254 (WAN VIP)
Type
Connections matching this rule will be mapped to the specified address. If specifying a custom network or alias, it must be routed to the firewall.
Port or Range
Enter the external source Port or Range used for remapping the original source port on connections matching the rule.Port ranges are a low port and high port number separated by ":".
Leave blank when Static Port is checked.
Static Port
Misc
No XMLRPC Sync
Prevents the rule on Master from automatically syncing to other CARP members. This does NOT prevent the rule from being overwritten on Slave.
Description
Auto created rule for ISAKMP - LAN to WANAnd
Interface
WAN
The interface on which traffic is matched as it exits the firewall. In most cases this is "WAN" or another externally-connected interface.
Address Family
IPv4+IPv6
Select the Internet Protocol version this rule applies to.
Protocol
Any
Choose which protocol this rule should match. In most cases "any" is specified.
Source
Network or Alias
Type
10.5.0.0
/
24
Source network for the outbound NAT mapping.
Port or Range
Destination
Any
Type
/
24
Destination network for the outbound NAT mapping.
Port or Range
Not
Invert the sense of the destination match.
Translation
Address
192.168.1.254 (WAN VIP)
Type
Connections matching this rule will be mapped to the specified address. If specifying a custom network or alias, it must be routed to the firewall.
Port or Range
Enter the external source Port or Range used for remapping the original source port on connections matching the rule.Port ranges are a low port and high port number separated by ":".
Leave blank when Static Port is checked.
Static Port
Misc
No XMLRPC Sync
Prevents the rule on Master from automatically syncing to other CARP members. This does NOT prevent the rule from being overwritten on Slave.
Description
Auto created rule - LAN to WAN
A description may be entered here for administrative reference (not parsed). -
Really hard to read that and know for sure. A screenshot would be better.
But... that looks OK as far as I can see.
-
I am unable to upgrade from 2.7.0. Running 'certctl rehash' has not resolved anything for me. Update system log:
Updating repositories metadata...
Updating pfSense-core repository catalogue...
Fetching meta.conf: . done
Fetching packagesite.pkg: . done
Processing entries: . done
pfSense-core repository update completed. 4 packages processed.
Updating pfSense repository catalogue...
Fetching meta.conf: . done
Fetching packagesite.pkg: ...... done
Processing entries:
Processing entries............. done
pfSense repository update completed. 549 packages processed.
All repositories are up to date.
Upgrading -upgrade... failed. -
Try running the upgrade from the actual command line with:
pfSense-upgrade -dThat will show you more useful error output.
-
@stephenw10 Hi Stephen, yes I agree, hard to read, but I have been unsuccessful at uploading screenshots to this interface. I can run pfSense pretty well, and I think I will find my problem, I always have so far, but this interface is a little cumbersome.
So what image formats does this interface accept? Cut and paste certainly does not work, and I think I failed at trying to get png from a screenshot to upload. Please excuse me while I unzip my ignorance.
After all the years of posting here you'd think I'd have figured this out.
Roy
-
Hmm, just accepts most things I try (png, jpeg) but the rules could be more relaxed for admin users.
If not though you can always link to an image somewhere else.
Or alternatively show the outbound NAT rules from the /tmp/rules.debug file like:
# Outbound NAT rules (manual) nat on $WAN inet proto { tcp udp } from 192.168.54.0/24 to any -> 172.21.16.22/32 port 1024:65535 # Test # Outbound NAT rules (automatic) # Subnets to NAT table <tonatsubnets> { 127.0.0.0/8 ::1/128 192.168.22.0/24 172.25.10.0/24 192.168.251.0/25 } nat on $WAN inet from <tonatsubnets> to any port 500 -> 172.21.16.22/32 static-port nat on $WAN inet6 from <tonatsubnets> to any port 500 -> (em0) static-port nat on $WAN inet from <tonatsubnets> to any -> 172.21.16.22/32 port 1024:65535 nat on $WAN inet6 from <tonatsubnets> to any -> (em0) port 1024:65535 -
@reberhar copy/paste may need a certain number of upvotes? Stuff like changing signature does.
-
@SteveITS Link then ... I can understand why you might want to do that.
I have forum entries on different platforms. I just haven't spent enough time helping these good folks. I remember how confusing it was at first. Yet, pfSense has been worth the struggle. Now I watch the people I supervise struggle, but that's ok. Productive failures are good teachers.
Thanks for your help.
-
@reberhar said in Upgrade pfsense CE 2.7.0 to 2.7.1:
So what image formats does this interface accept? Cut and paste certainly does not work, and I think I failed at trying to get png from a screenshot to upload.
I always paste the screen shot into a paint program, clip / redact as required, save as a jpeg, then in the forum click on the picture icon to upload