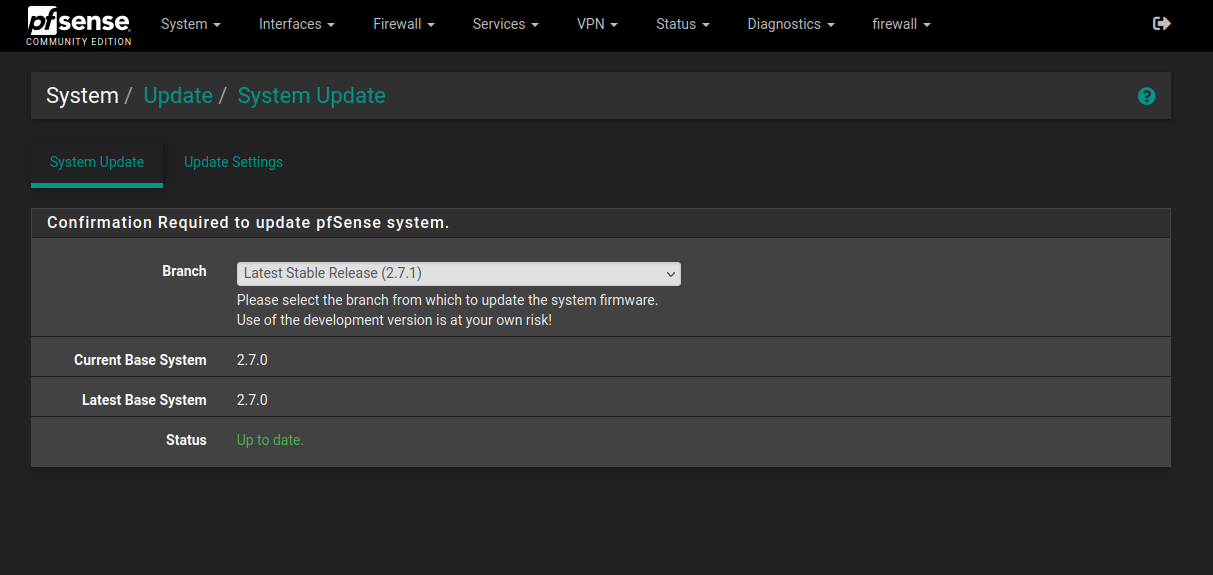
Upgrade pfsense CE 2.7.0 to 2.7.1
-
Cheers mate.
I only hit this snag when going from 2.7.0 to 2.7.2 on my work CARP cluster, so I missed it in the change notes for 2.7.1, which I have successfully upgraded to on several smaller systems. The update was showing but I usually like to do a pre-emptive reboot before an upgrade on a box with six months uptime. It stopped showing up after the reboot. Rehashing the certs sorted that out.
Well, the secondary is back up so let's fail over to it and see how it goes (I'm at home doing this from the outside!) ...
(edit) ... the primary has rebooted. It too forgot about the 2.7.2 update. I ran the cert rehash twice because I might have not waited long enough the first time - about one minute! I have been using the web GUI Diagnostics -> Command Prompt to run certctl.
... wait for reboot, AD DC still pinging over IPv6 IPSEC VPN ...
... its just come back up.. Leave CARP maint mode ... all good. My monitoring systems (Icinga1 and 2) didn't go berserk, so the 70 odd VPNs held up through out.
-
@stephenw10 I am in the same state followed the same steps too. The only package I recall upgrading on 2.7.0 was pfBlockerNG
My list of installed packages:
darkstat 3.1.3_6
lldpd 0.9.11_2
pfBlockerNG-devel 3.2.0_7
WireGuard 0.2.0_2pkg-static version (with 2.7.0 branch selected)
Updating pfSense-core repository catalogue... Fetching meta.conf: Fetching packagesite.pkg: pfSense-core repository is up to date. Updating pfSense repository catalogue... Fetching meta.conf: Fetching packagesite.pkg: pfSense repository is up to date. All repositories are up to date. beep-1.0_1 = bind-tools-9.18.14 = bsnmp-regex-0.6_2 = bsnmp-ucd-0.4.5 = bwi-firmware-kmod-3.130.20 = ca_root_nss-3.89.1 = ccid-1.5.1 = check_reload_status-0.0.15 = choparp-20150613 = cpdup-1.22 = cpustats-0.1_1 = curl-8.1.0 = cyrus-sasl-2.1.28 = darkstat-3.0.721 = dbus-1.14.6,1 = devcpu-data-20230513 = devcpu-data-amd-20230424 = devcpu-data-intel-20230512 = dhcp6-20080615.2_4 = dhcpleases-0.5_1 = dmidecode-3.5 = dnsmasq-2.89_1,1 = dpinger-3.3 = expat-2.5.0 = expiretable-0.6_2 = filterdns-2.2 = filterlog-0.1_9 = gettext-runtime-0.22_1 > glib-2.76.2,2 = gmp-6.2.1 = gnugrep-3.11 = grepcidr-2.0 = hostapd-2.10_5 = icu-73.2,1 > iftop-1.0.p4 = igmpproxy-0.4,1 = indexinfo-0.3.1 = ipmitool-1.8.18_3 = iprange-1.0.4 = isc-dhcp44-client-4.4.3P1 = isc-dhcp44-relay-4.4.3P1 = isc-dhcp44-server-4.4.3P1 = jansson-2.14 = jq-1.7_1 > json-c-0.16 = ldns-1.8.3 = libargon2-20190702 = libedit-3.1.20221030,1 = libevent-2.1.12 = libffi-3.4.4 = libgcrypt-1.9.4_1 = libgpg-error-1.47 = libiconv-1.17 = libidn2-2.3.4 = libinotify-20211018 = libltdl-2.4.7 = liblz4-1.9.4,1 = libmaxminddb-1.7.1_1 > libmcrypt-2.5.8_3 = libnghttp2-1.52.0 = libpsl-0.21.2_3 = libsodium-1.0.18 = libssh2-1.10.0_1,3 = libucl-0.8.2 = libunistring-1.1 = libuv-1.45.0 = libxml2-2.10.4_1 > libxslt-1.1.37 = lighttpd-1.4.72 > links-2.29,1 = lldpd-1.0.14 = lua-resty-core-0.1.26 = lua-resty-lrucache-0.13 = lua54-5.4.6 > luajit-openresty-2.1.20230410 = lzo2-2.10_1 = minicron-0.0.2 = miniupnpd-2.3.3,1 = mobile-broadband-provider-info-20221107 = mpd5-5.9_16 = mpdecimal-2.5.1 = net-snmp-5.9.1_3,1 = nettle-3.9.1 > nginx-1.24.0_6,3 = nss_ldap-1.265_14 = ntp-4.2.8p15_5 = oniguruma-6.9.8_1 = openldap26-client-2.6.4 = opensc-0.23.0_1 = openvpn-2.6.4 = openvpn-auth-script-1.0.0.3 = pam_ldap-186_1 = pam_mkhomedir-0.2 = pcre-8.45_3 = pcre2-10.42 = pcsc-lite-1.9.9,2 = perl5-5.32.1_3 = pfSense-2.7.0 = pfSense-Status_Monitoring-php82-1.8_3 = pfSense-base-2.7.0 = pfSense-boot-2.7.0 = pfSense-default-config-2.7.0 = pfSense-kernel-pfSense-2.7.0 = pfSense-pkg-WireGuard-0.2.0_2 = pfSense-pkg-darkstat-3.1.3_6 = pfSense-pkg-lldpd-0.9.11_2 = pfSense-pkg-pfBlockerNG-devel-3.2.0_7 > pfSense-rc-2.7.0 = pfSense-repo-2.7.0_2 = pfSense-repoc-20230616 = pfSense-upgrade-1.0_33 = pftop-0.8_2 = php82-8.2.11 > php82-bcmath-8.2.6 = php82-bz2-8.2.6 = php82-ctype-8.2.6 = php82-curl-8.2.6 = php82-dom-8.2.6 = php82-filter-8.2.6 = php82-gettext-8.2.6 = php82-gmp-8.2.6 = php82-intl-8.2.11 > php82-ldap-8.2.6 = php82-mbstring-8.2.6 = php82-opcache-8.2.6 = php82-openssl_x509_crl-1.3_2 = php82-pcntl-8.2.6 = php82-pdo-8.2.6 = php82-pdo_sqlite-8.2.6 = php82-pear-1.10.13 = php82-pear-Auth_RADIUS-1.1.0_4 = php82-pear-Cache_Lite-1.8.3,1 = php82-pear-Crypt_CHAP-1.5.0_2 = php82-pear-HTTP_Request2-2.5.1,1 = php82-pear-Mail-1.4.1,1 = php82-pear-Net_IPv6-1.3.0.b4_2 = php82-pear-Net_SMTP-1.10.1 = php82-pear-Net_Socket-1.2.2 = php82-pear-Net_URL2-2.2.1 = php82-pear-XML_RPC2-1.1.5 = php82-pecl-mcrypt-1.0.6 = php82-pecl-radius-1.4.0b1_2 = php82-pecl-rrd-2.0.3 = php82-pfSense-module-0.95 = php82-phpseclib-2.0.17 = php82-posix-8.2.6 = php82-readline-8.2.6 = php82-session-8.2.6 = php82-shmop-8.2.6 = php82-simplexml-8.2.6 = php82-sockets-8.2.6 = php82-sqlite3-8.2.6 = php82-sysvmsg-8.2.6 = php82-sysvsem-8.2.6 = php82-sysvshm-8.2.6 = php82-tokenizer-8.2.6 = php82-xml-8.2.6 = php82-xmlreader-8.2.6 = php82-xmlwriter-8.2.6 = php82-zlib-8.2.6 = pkcs11-helper-1.29.0 = pkg-1.20.8_3 > py311-maxminddb-2.4.0 > py311-setuptools-63.1.0_1 > py311-sqlite3-3.11.6_8 > python311-3.11.6 > qstats-0.2 = radvd-2.19_2 = rate-0.9_2 = readline-8.2.1 = rrdtool-1.8.0_2 = rsync-3.2.7 = scponly-4.8.20110526_5 = smartmontools-7.3 = sqlite3-3.43.1,1 > ssh_tunnel_shell-0.2_1 = sshguard-2.4.2_2,1 = strongswan-5.9.10_2 = uclcmd-0.2.20211204 = unbound-1.17.1_3 = voucher-0.1_2 = vstr-1.0.15_1 = whois-5.5.7 = wol-0.7.1_4 = wpa_supplicant-2.10_6 = wrapalixresetbutton-0.0.8 = xinetd-2.3.15_2 = xxhash-0.8.2 > zstd-1.5.5 > -
What error do you see when you run:
pkg-static -d update? -
@reberhar Hi All,
Right after I updated to 2.7.2 I had an odd problem with my primary CARP cluster server. DNS was not arriving at the LAN devices, although it was arriving at the DNS Lookup in the diagnostic menus. I rebooted the system and I thought the problem went away, but I was apparently mistaken.So tonight it happened again. Reboot did not help. I even changed it and pfBlocker to Python Mode wondering if there was some kind of corruption error I could overwrite. It did not help. Again in the Diagnostics drop down in DNS Lookup everything is fine, but now joy on the lan. So I turned on Forwarding Mode and that worked. I would sooner use recursive mode, not to mention that something is obviously broken that I want to fix.
Its almost like it falls behind because sometime it partially resolves on the lan device.
I will keep plugging away at it until I get it, but any suggestions are greatly appreciated.
Roy
-
Does DNS Lookup show success for all configured DNS servers? Including 127.0.0.1?
-
@stephenw10 Yes, all look well.
-
Hmm, should be fine from any clients using it then. Perhaps the clients are not using Unbound in pfSense? Or perhaps that DNS traffic is being blocked by the firewall rules? Or forced out of gateway so it never reaches the LAN IP?
-
@stephenw10 Hi Steve,
I thought about lots of things, secure DNS, etc. The thing is the rest of the bandwidth is intact. I finally disabled and re-enabled the DNS resolver from the gui and it came back for now. I thought about the cache but that seems like it can't be the problem. It won't resolve without the cache functioning. And dig finds the root and the name server. -
Unbound doesn't stop running? If it did then localhost should show no reply in DNS Lookup.
-
@stephenw10 Hi Steve, Yes 127.0.0.1 gives good and accurate response. This should not be possible. However, at other times in dealing with DNS I have seen nslookup function on the client computer before the pfSense DNS diagnostic tool. Not this time however.
I am hoping that this just goes away. :)
-
Hmm, well I wouldn't expect it to but.....

-
@stephenw10 I know better than to expect it to go away, but I can't think about it right now. I have other servers to (t)fry. If and when I figure it out I will post what I find. The hardest part is the disruptions for my users.
Thanks for your help.
-
@reberhar So Steve, I have a question.
We use Comcast which frequently has significant latency. During the latency times I note that DNS requests backup, causing latency reports because dpinger requests get lost in the pile. Buffer bloat, of course can be a problem. I have read articles about that mentioning that our desire to maintain network requests in a linear fashion might sometimes be misplaced.
So I use priq on my shaper. Is there someway to make that queue smaller? I do note that at the time of the recent problems there is no signficant latency reflected in the gui on the WAN. The logs do reflect very recent latency however. This doesn´t seem like it can be the problem because localhost is resolving DNS requests from the Diagnostics Lookup when I do the testing. And reqular non DNS traffic does not seem to be affected. Stuff that is already in the state table continues to work.
I am just trying to think outside of the box.