Firewall review
-
@Jarhead said in Firewall review:
default Block All on all interfaces
Block all to pfsense and allow all from pfsense? is it correct?
-
@Jarhead said in Firewall review:
coming in
I want to use ports which me allow coming out not come in
-
@Antibiotic said in Firewall review:
What this svp?
That's local language for S'il vous plait, or "Please".
-
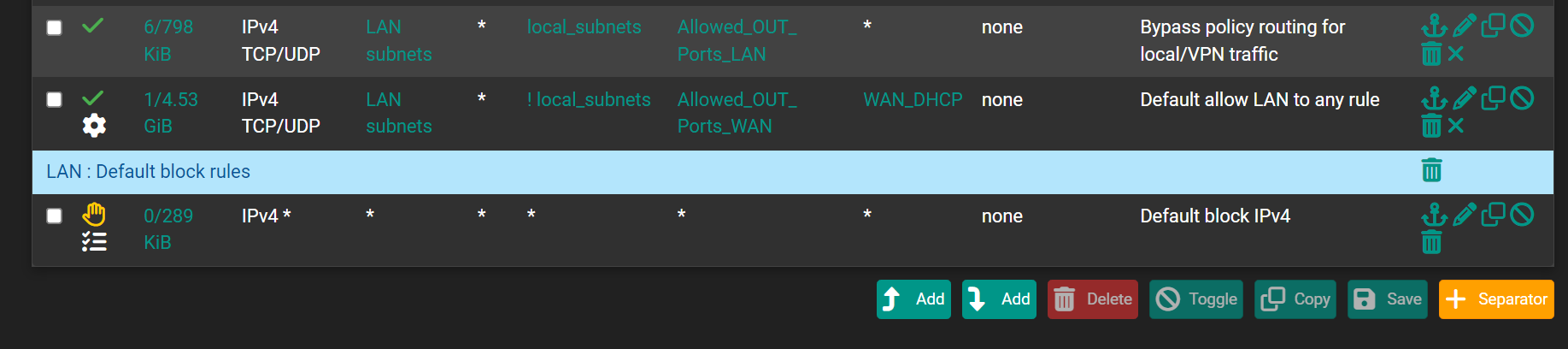
@Gertjan Ok my friend, so suspect my rules were incorrect))))
I did default:
And will searching how to make in correct way, what I want.
Fisrt rule restrict ports using only, what me allow to use inside local subnets
Second rule restrict ports using, what me allow to use outside local subnets to internet. I do not know for this moment, how to make this correct, will search examples with a images by words difficult to imaging. -
@Antibiotic said in Firewall review:
@Jarhead said in Firewall review:
default Block All on all interfaces
Block all to pfsense and allow all from pfsense? is it correct?
You're not understanding still. All traffic is evaluated "entering" the interface that network is attached to.
So yes, block all to pfSense if you wanna say it that way, but not allow all from pfSense because it depends on where that traffic is coming from.
If it's from another interface on pfSense and blocked on that interface, it wouldn't be allowed from pfSense.@Antibiotic said in Firewall review:
@Jarhead said in Firewall review:
coming in
I want to use ports which me allow coming out not come in
So then you have to block or allow the traffic on the interface attached to pfSense.
If you have a pc on OPT1, and you want to block it's traffic to the LAN, you put the block rule on OPT1. That blocks that pc's out as you're calling it.
So you have to think about what each interface, or device, can access, and create rules to do that. -
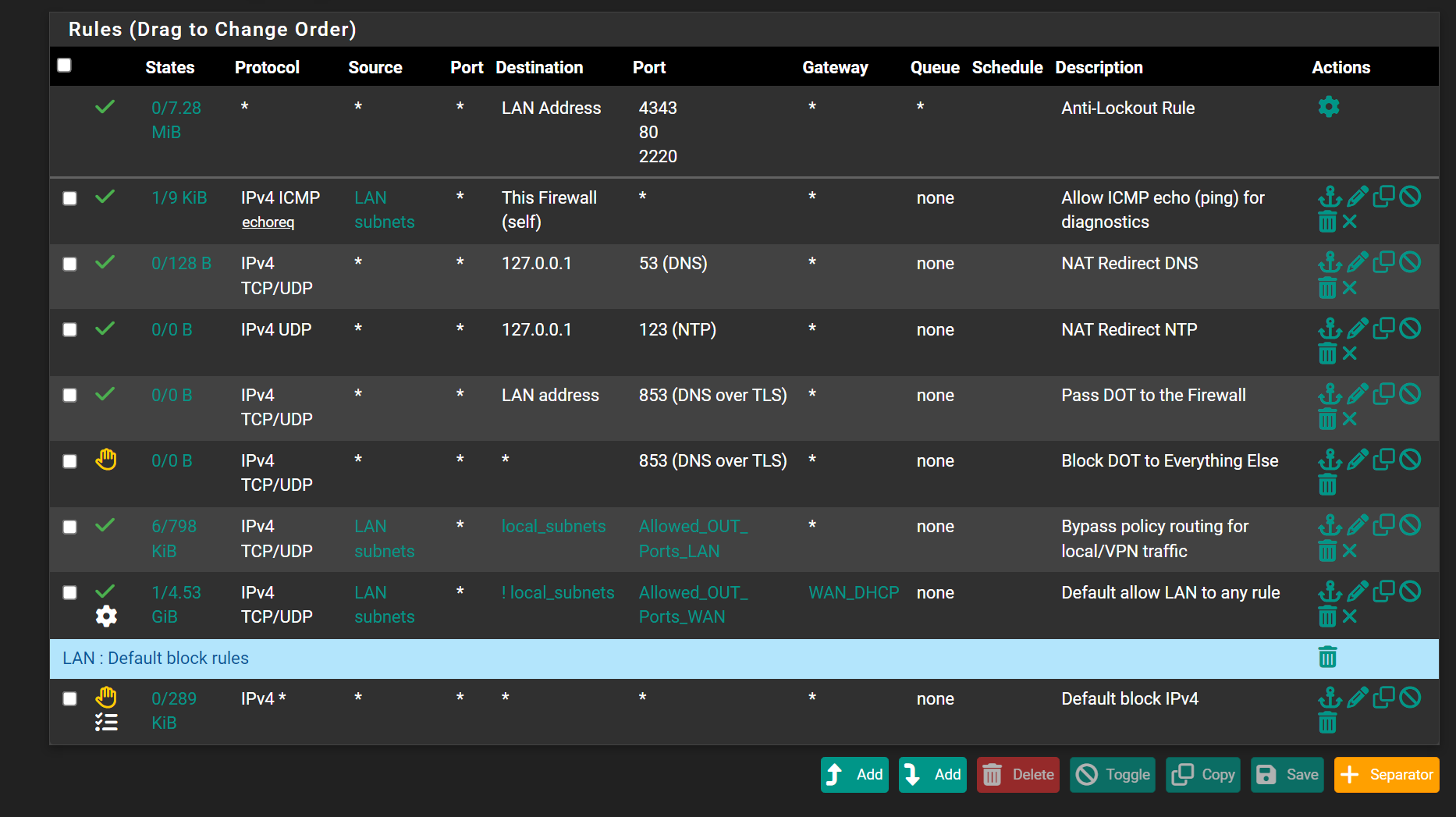
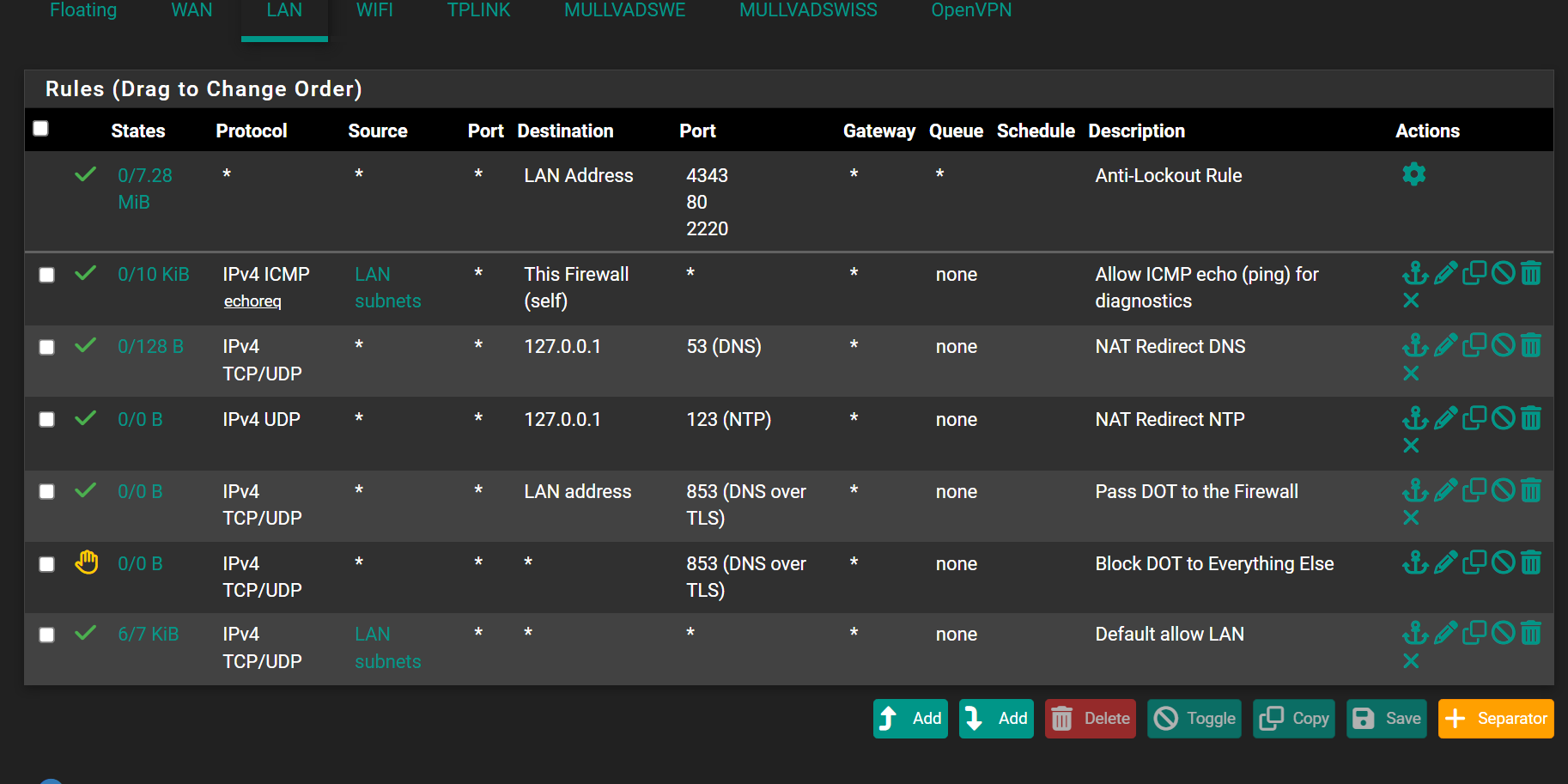
@Jarhead said in Firewall review:
If it's from another interface on pfSense and blocked on that interface, it wouldn't be allowed from pfSense
When you install pfsense this one is default rule on LAN
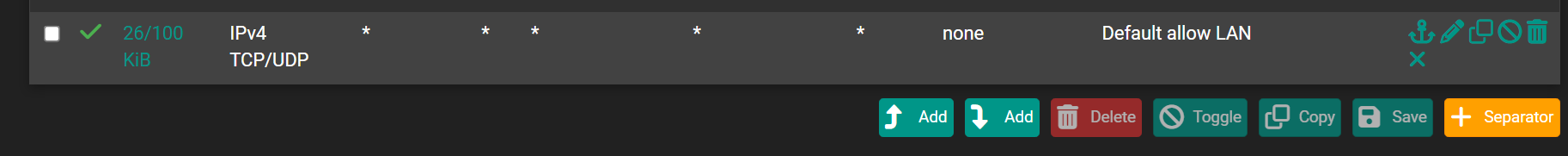
Sorry protocol also any , it mean all allow out from interface LAN
-
@Jarhead said in Firewall review:
So then you have to block or allow the traffic on the interface attached to pfSense.
tHAT WJY , ME ASKING CORRECT EXAMPLE TO ALLOW ONLY PORTS WHAT ME WANT TO COMMUNICATE ON SUBNETS AND COMMUNICATE WITH INTERNET. DO NOT HAVE A BIG EXPIRIENCE ,THAT ALL WHAT I WANT
-
@Antibiotic It means allow all traffic from the LAN subnet to anywhere it wants to go.
Once traffic is allowed into the firewall, it can then go anywhere.Don't know how else to say this, traffic is either allowed or blocked as it enters the interface from the network directly attached to that interface.
If you're LAN is 192.168.1.0/24 and you have a pc at 192.168.1.2, and you want to block it from accessing the internet, you put the rule on the LAN interface, not the WAN. -
@Jarhead said in Firewall review:
from accessing the internet
i DO NOT WANT TO BLOCK INTERNET, JUST WANT TO RESTRICT TO PORTS NUMBERS WIHCH I WANT
-
@Jarhead said in Firewall review:
you put the rule on the LAN interface, not the WAN.
My friend if you have a time and desire can you please just simple show 2 examples
First allow only ports to use by local subnets which you set in your aliasesSecond allow to communicate with internet outside of pfsense with ports which you set in second aliases
-
@Antibiotic said in Firewall review:
@Jarhead said in Firewall review:
you put the rule on the LAN interface, not the WAN.
My friend if you have a time and desire can you please just simple show 2 examples
First allow only ports to use by local subnets which you set in your aliasesSecond allow to communicate with internet outside of pfsense with ports which you set in second aliases
I don't understand what you mean by either of those.
Give an exact example of what you want. -
@Jarhead Yes , if possible and this action do not hurt you
-
@Antibiotic No, I'm asking you to give an exact example of what you want to do.
-
@Gertjan Actually "If you please"
Ted
-
@Jarhead
Dude i think going communication between forest and sea. If you can read , I post what i want to do! If you do not want, than no problem -
@Antibiotic Ok. Good luck.
-
@tedquade said in Firewall review:
Actually "If you please"
@Jarhead said in Firewall review:
you put the rule on the LAN interface, not the WAN.
My friend if you have a time and desire can you please just simple show 2 examples
First allow only ports to use by local subnets which you set in your aliasesSecond allow to communicate with internet outside of pfsense with ports which you set in second aliases
-
@Antibiotic I never needed loopback rules for my system.
-
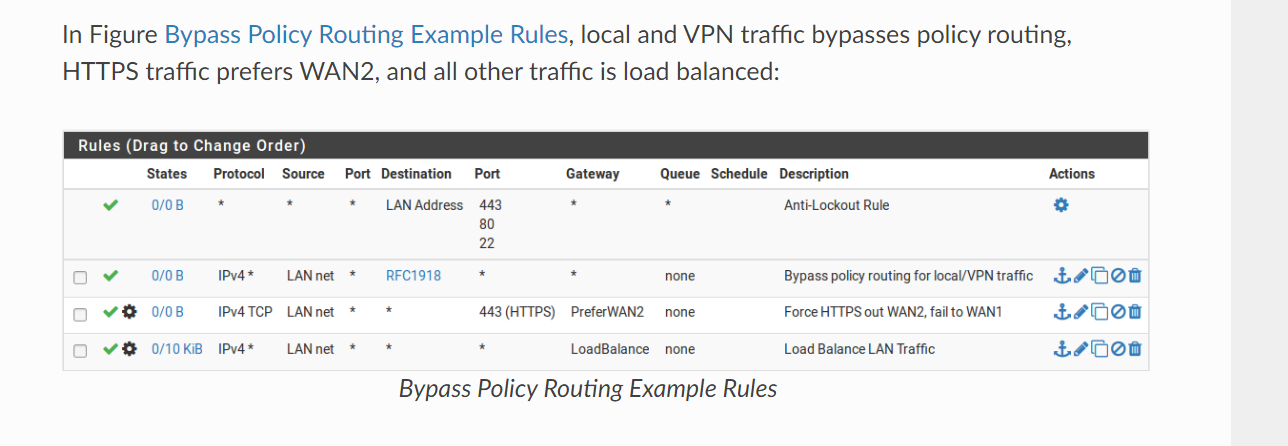
Wan you only need to set what you want coming in. Anything originating from LAN that is approved will get out. So a VPN port if needed would be an example of a WAN rule. But I have only 1 wan rule everything else is block, my LAN has the rules
-
@Gertjan said in Firewall review:
(I presume you already removed the "LAN subnets" from Source)
Source LAN subnet going to WAN gateway, by NetGate docs rule. Why need to remove source?
I'm understood that rule correct apply to interface belong, but totally can be LAN subnet only direct to WAN gateway or VPN gateway only?