1 WAN interface, 3 LAN interfaces, OpenVPN allow communication to all networks
-
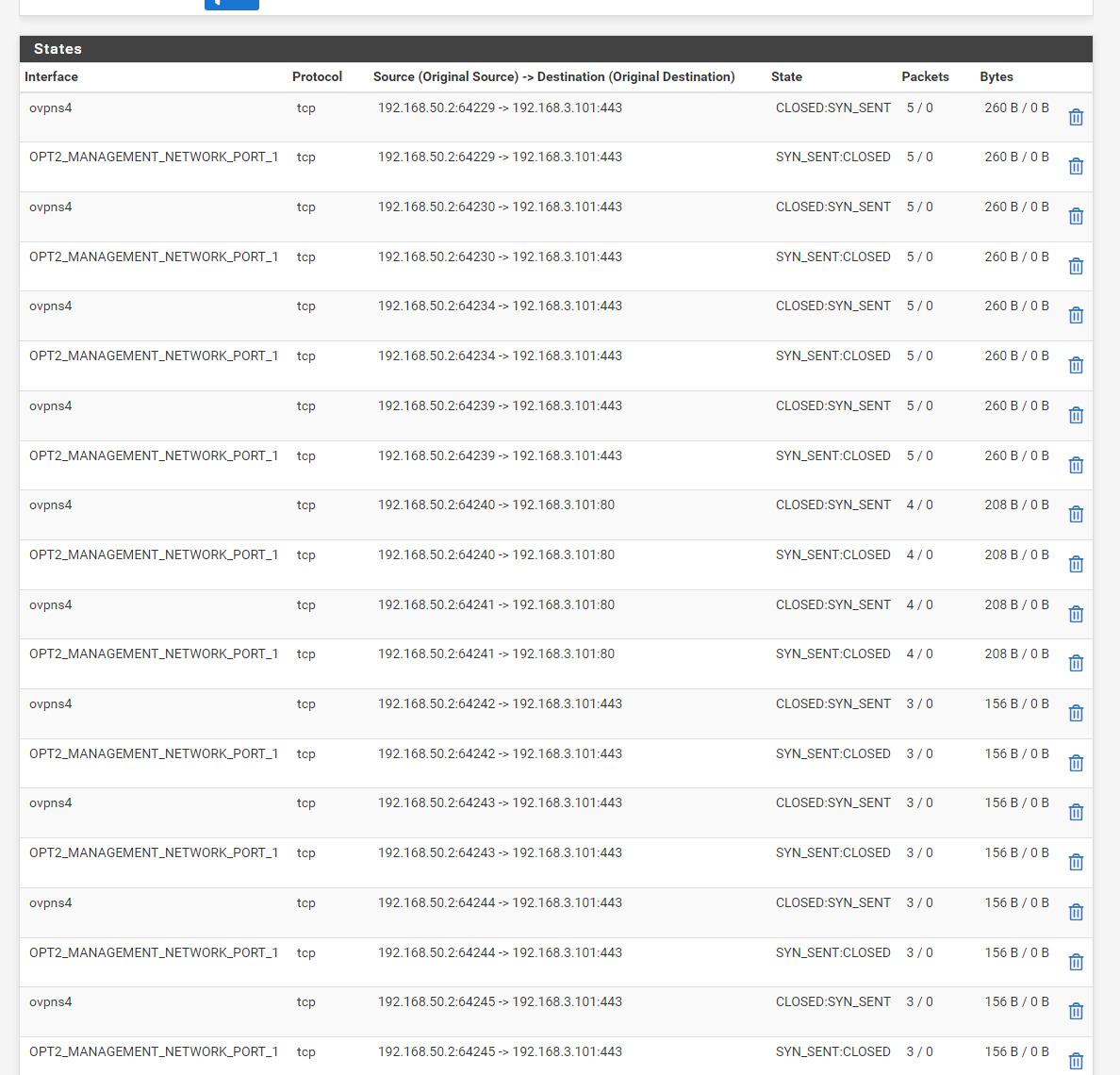
On the real server setup, I am able to see the states when going to the 192.168.3.0/24 from the VPN net 192.168.50.0/24. I'm not sure what to make of it.
Although it doesn't seem to matter if the target http address is real or not, but I guess that doesn't matter, looks like it's making an attempt?
-
The states are correct but there is no translation. Did you add an appropriate OBN rule there too?
-
I see those states no matter if the OBN is there or not.
-
What OBN rule are you setting there?
-
-
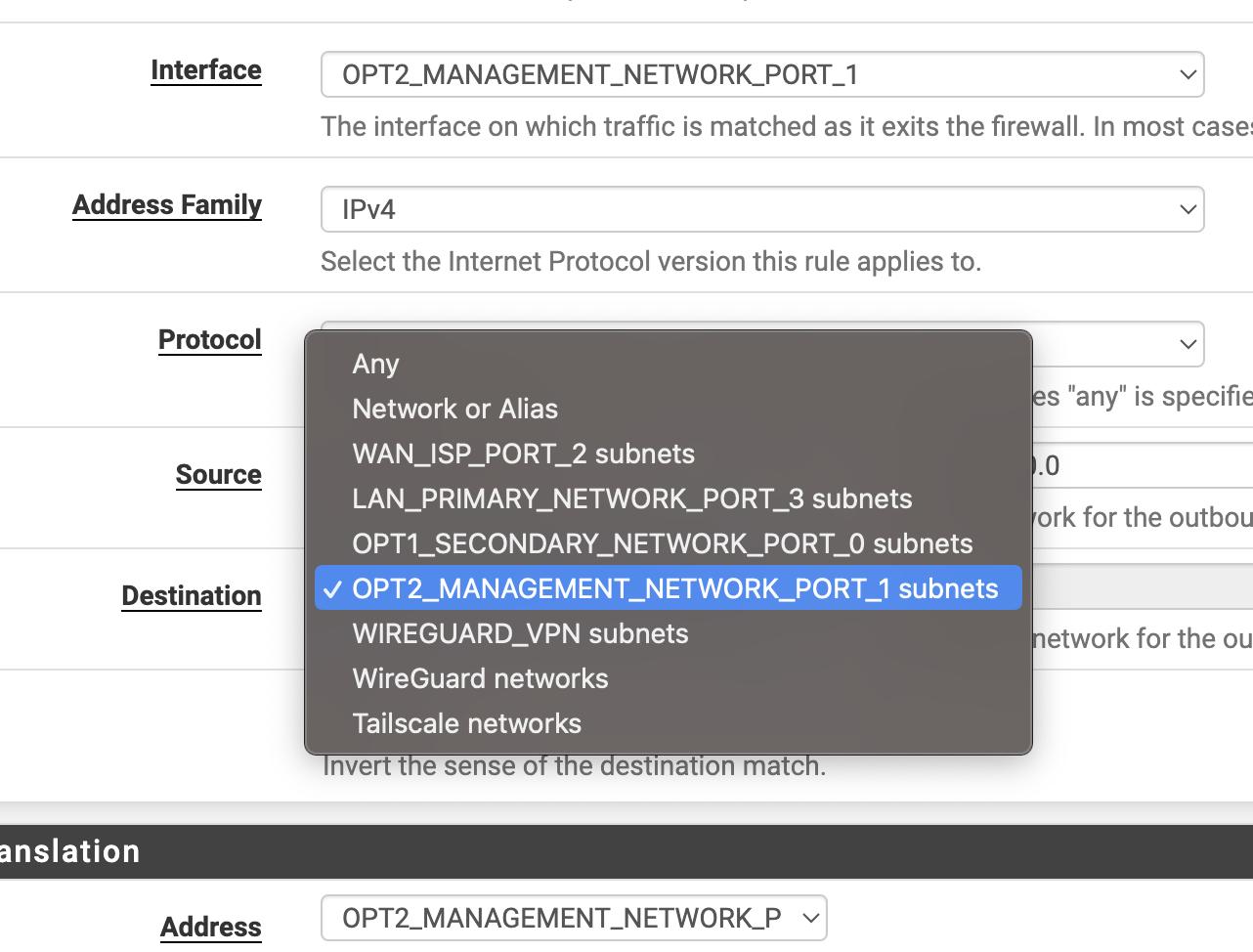
Is that destination the address or subnet? It needs to be the OPT2 subnet there to match.
-
It's the subnet. Does I need this Outbound rule when setting the OPT2 (192.168.3.0/24) as local networks in the OpenVPN config?
 .
. -
Yes you still need the rule because hosts in the OPT2 subnet will block access from the VPN subnet directly.
That rule should match if the subnets are correct.
-
Is there a way to just have the vpn clients land on the OPT2 subnet? Would that solve the problem?
-
Yes, you can setup the VPN as TAP and bridge the interfaces. But that will only work for one interface and you have 3. And it introduces a bunch of other things you don't want so I wouldn't recommend it.
Adding an OBN rule that matches will allow this to work. The best solution is to just allow it on the hosts though.
Make sure the rules are actually loading in Status > Filter Reload. Make sure it returns without errors.
-
Ok, I'm confused now.
Looks as if rules are being loaded without error.
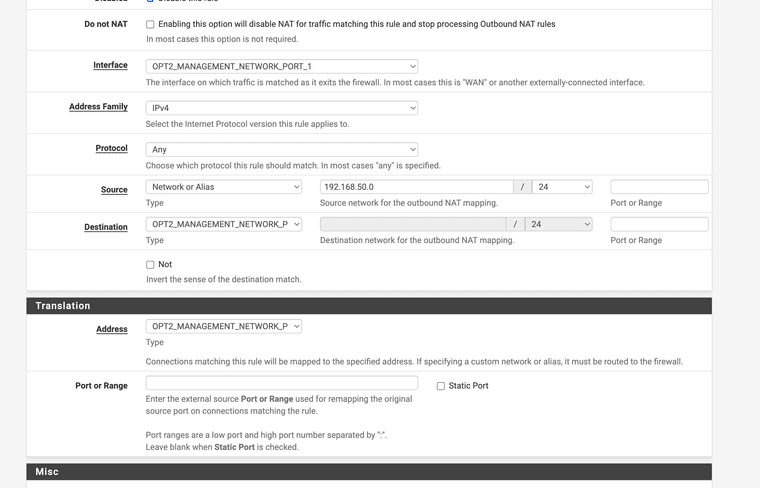
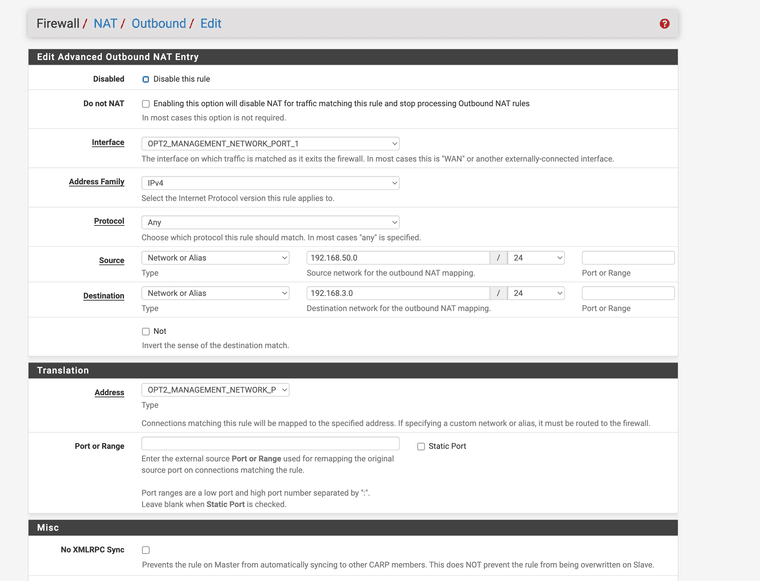
This is my Outbound rule
-
Yet you still see the states with no NAT applied?
-
I still can’t get it to work on my test setup, but I was able to solve the production issue.
It was the Cisco switches breaking comms between the devices and the firewall. No fix yet, other than to use a dumb switch. The traffic flowed just fine right away, I was able to provision the nodes with no issue.
I’m still seeing some weird timeouts with the VPN, could be a timeout issue, not sure
Thanks so much for all of your help
-
Ah, well that's a much better solution. Adding NAT in there is always a workaround.
That NAT looks like it should match and be applied though.