AT&T Gateway bypass/true bridge using new authbridge
-
The DNS ACL is enabled and enforced by going to Services > DNS Resolver > Advanced settings.
Checking "Disable Auto-added Access Control"
Then go to Services > DNS Resolver > Access Lists
Create a pass rule for your LANs
Create a deny rule for the ONT and the AT&T DHCP server.
If you want to get super particular, you can find the actual AT&T DNS server on the AT&T router and add that to the deny rules too.Also under System > General Setup
Uncheck DNS Server Override and Select either "Use Local DNS, fall back to remote DNS Servers" or "Use Local DNS, ignore remote DNS servers." And add your favorite DNS Servers under DNS Server Settings.AT&T does a bunch of weird crap with their DNS, such as DNS "Error Assist". You are pre-enrolled in them selling your DNS data, and can "opt-out" on their website.
"ATTHelp
Sign in to your AT&T account.
Once signed in, click on your name and select View Profile.
Now select Communication Preferences, then Privacy Settings.
From here, you should be able to select DNS Error Assist, and see an option to opt out."https://www.reddit.com/r/homelab/comments/wkypc3/att_users_dont_forget_to_turn_off_dns_error_assist/?rdt=42954
-
You could also try disabling EEE on the igb NIC. I disable it on mine anyways, and it works fine over WAN. My igb NIC is an 82576.
dev.igb.0.eee_control="0"
My em NIC works fine as a WAN interface too in the bypass. It is an 82573.
dev.em.0.eee_control="0"
hw.em.eee_setting="0" -
Having this same issue with my pace gateway, have you figured out a solution to get it to work yet?
-
What issue exactly? Quite a few things in this thread.
-
As Stephen indicated, more details needed.
If you have an external ONT, it's possible to rather easily pull certs from a 210 (possibly others).
https://github.com/mozzarellathicc/attcerts
The 210 can be found for cheap on ebay. Going this route eliminates a useless piece of a equipment remaining connected, not to mention gaining a port.
With the newer pf (CE 2.7x) and plus (23.09?) - which ever versions they introduced openssl3, there are additional steps needed to make eapol authentication work using wpa_supplicant. You can refer to this lovely reddit post which details the requirements quite nicely. - https://www.reddit.com/r/PFSENSE/comments/18jz0uc/installing_att_bypass_on_a_clean_install_of/ .
If you have a 320 with no external ONT, there's still ways of bypassing but more involved. You will need to obtain an sfp ont module and have a switch w/port to accept such modules.
-
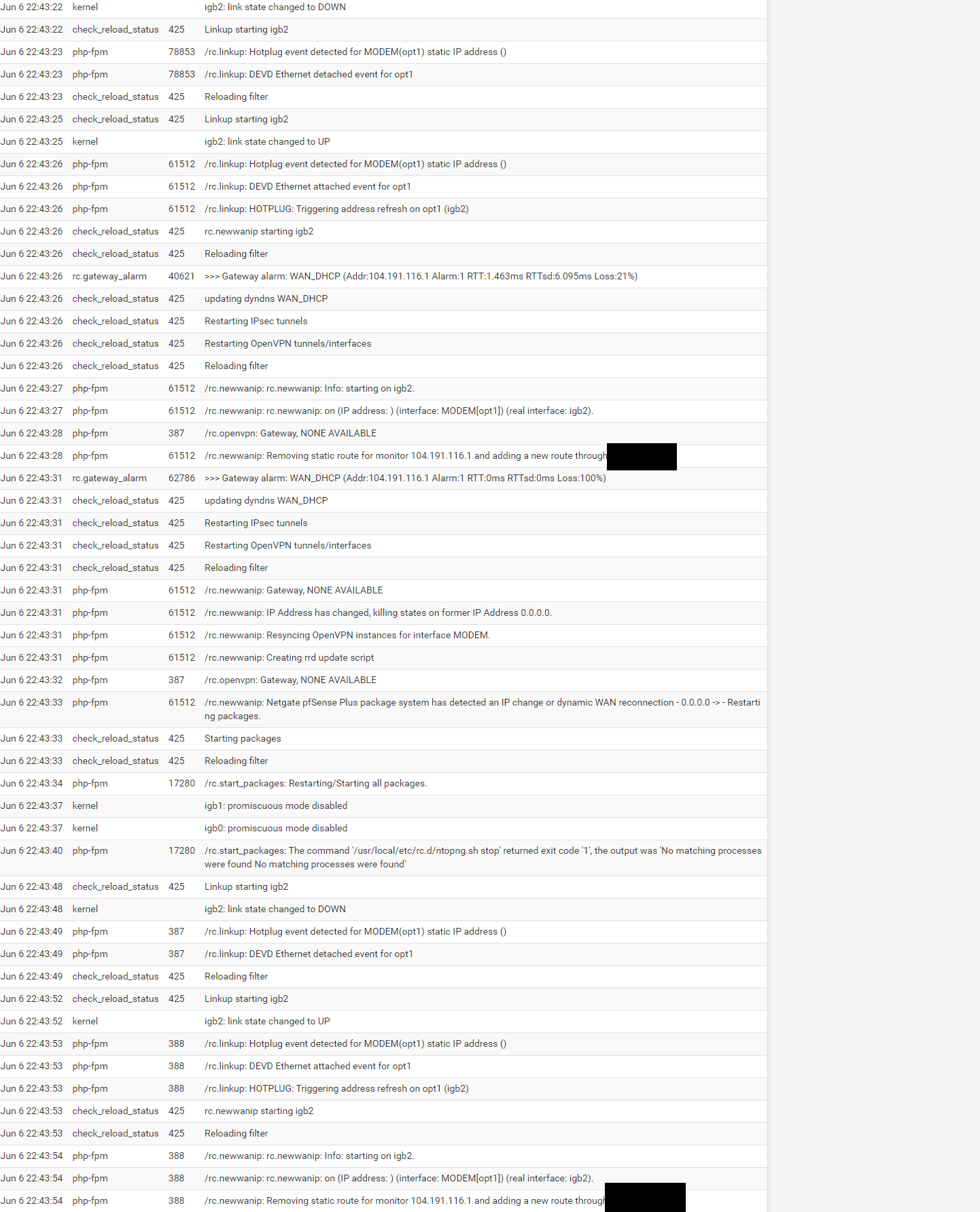
@stephenw10 I follow the configuration recipe, and internet connectivity seems to work for a little bit, but then in the gateway monitor packet loss slowly starts to increase and then internet connectivity is gone. I haven't been able to see if connectivity comes back after a while but restarting pfsense brings it back for about another 5 minutes and then it is gone.
Definition of internet connectivity (being able to ping 1.1.1.1 for example). both from pfsense and client device.
-
@GPz1100 I'm not sure if with the Pace 5268ac this is possible as I haven't found anything about someone being able to get the certificates off of it without some hardware hacking.
-
Is it only rebooting that brings it back? Does reconnecting the WAN or rebooting the modem bring it back for example? Or resaving the WAN perhaps?
-
@matthewgcampbell I recommend following the path of least resistance. Contact att, tell 'em your gateway is disconnecting and request they send you a newer one. Ask if you can get the bgw210. Once in hand, attempt to get certs from it and forgo the whole L2 proxy business. You'll eliminate a useless piece of hardware and gain stability.
Or just buy a 210 on ebay or the certs.
I have no experience with the proxy method, while it may work, ultimately keeps the useless turd (att gateway) still in the loop to some extent. This may cause weird behavior depending on what the mothership may be trying to do.
In general, once eapol authenticated, you stay authenticated until the link is severed (wan cable disconnected), or att reboots the OLT requiring another auth. Otherwise, sessions can last weeks and months. As for wan dhcp; att dhcp servers issue leases good for 1 hr. They start renewing around the 30 min mark. As far as I know, ipv4 dhcp lease is needed before any data starts to flow, or ipv6 is available. Meaning you can't just set wan to the same static values and have it work.
I've been using wpa_supplicant bypass with external ont going on 5 years now, att knows im bypassed but they've never raised an issue about it. They know because i've had other issues (routing/peering) that required filing fcc complaints to get any attention. Upper level tech support I spoke with never mentioned bypass in any manner. Hope this helps.
-
@stephenw10 Resaving the WAN would bring it back, I haven't tried unplugging, but rebooting also fixed it.
-
@GPz1100 said in AT&T Gateway bypass/true bridge using new authbridge:
In general, once eapol authenticated, you stay authenticated until the link is severed (wan cable disconnected), or att reboots the OLT requiring another auth. Otherwise, sessions can last weeks and months. As for wan dhcp; att dhcp servers issue leases good for 1 hr. They start renewing around the 30 min mark. As far as I know, ipv4 dhcp lease is needed before any data starts to flow, or ipv6 is available. Meaning you can't just set wan to the same static values and have it work.
This is the part that has me confused, it seems to pass traffic for a little bit (5 minutes) and then stops. But according to this that shouldn't be possible.
-
@matthewgcampbell I have never experienced a scenario where it passes traffic for a short amount of time then stops, at least not in the context of eapol auth related. It either passes or it doesn't. Then again I've never done any proxy bypasses either, can't really comment on odd behavior as a result.
I assume you're following this - https://docs.netgate.com/pfsense/en/latest/recipes/authbridge.html ?
You might want to give a try to one of the proxy scripts here - https://github.com/MonkWho/pfatt/tree/master . This is what we used before vlan0 compliant wpa_supplicant and dhclient.
Edit, one other idea to try is the old dumb switch bypass method.
I can't find a good write up but in essence you connect ethernet from ont and gateway to a dumb switch (preferably not netgear). Wait until the lights on the modem are all green and stop flashing. Disconnect gateway cable while leaving ONT/switch connected. Connect cable from the modem to your pfsense wan port (again, you're not touching the ONT/switch cable). Pfsense should be configured for dhcp on wan.
See if you experience the same disconnect issues after x amount of time. If you do, try a release /renew on the wan. If it doesn't pull an ip, try rebooting pfsense only. This whole time, the link between the ONT and switch should remain connect and as far as ONT concerned, remain authenticated.