upgraded to pfsense 2.8.0, WiFi devices report intermittent 'no internet access'
-
-
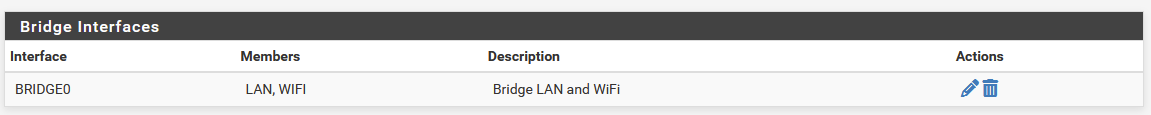
Yes, I do have a bridge and I expect that I will have to remove it and connect interfaces LAN & WiFi via rules.
-
You shouldn't have to you just need to make sure traffic is opening states on the correct interface.
Do you have bridge filtering set to the bridge members or the bridge itself?
Do you have the bridge assigned?
-
@stephenw10
I only have the bridge because when adding external AP the tutorials I looked at said I need it.
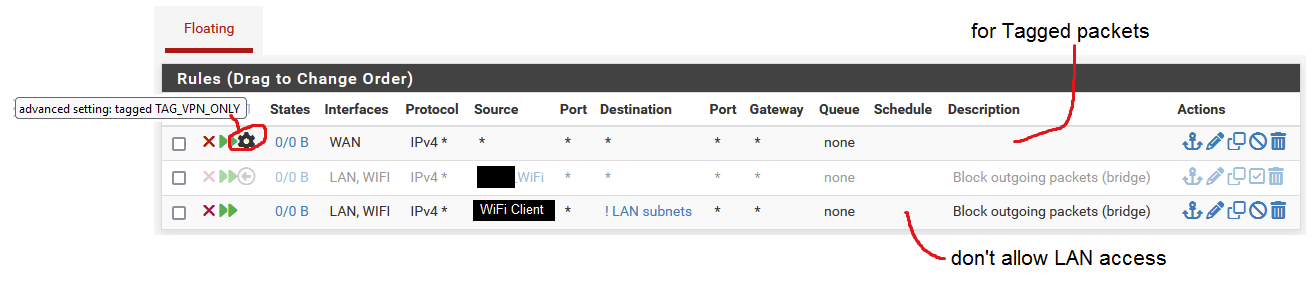
I don't have it assigned to anything. I don't filter on it. I don't explicitly use it for anything.In 'Floating' rules I had entries because under WiFi interface I have a rule that WiFi should not go out to 'LAN subnet'. I don't want WiFi devices to reach my LAN in general, unless explicitly allowed (via rules). Sometimes, the "WiFi Client" from the picture with Floating rules I posted reached my LAN and I wasn't sure why so I put a Floating rule to forbid it. The Floating rules are executed before any other in the firewall.
-
@skubany2 your last rule there where you say don't allow lan access is wrong.. That is a ! lan subnets - it would block everything that is NOT the lan subnets.
none of those rules show any hits..
-
I would guess that traffic from the clients is coming in the WIFI interface and going out the LAN because that's where the subnet is defined. The bridge allows that to work because everything uses the same subnet but pf sees that as asymmetric.
Unless you need to filter between the wired and wireless segments you should move filtering to the bridge, assign the bridge and add the subnet on the bridge directly with neither member having a subnet defined.
-
This is such a borked up config.. Why are you bridging? Why would you bridge if you don't want to allow wifi talk to lan?
I take it your again hiding your rfc1918 space where you put in wifi clients - so these are different networks - again why bridge?
What exactly are you trying to accomplish - there is almost never a good reason to bridge..
If you want to leverage a port on pfsense for your AP - then put it on its own network, and just allow what you want. If you want wifi on the same network as lan plug your AP into your switch.
If you want multiple networks on your AP via vlans and one of those is your lan network - then have a vlan capable switch and again plug your AP into your switch.
-
Commonly such a setup is used when you want to have wired and wireless clients in the same subnet but also want to filter traffic between them.
I hadn't, until now, considered how interface bound states might affect that.

But, I agree, it's almost always better to just use two subnets and not bridge them.
-
@johnpoz
You are right, I misspoke. The "WiFi Client" is not supposed to go out to the internet. I almost never use that client though. -
@johnpoz said in upgraded to pfsense 2.8.0, WiFi devices report intermittent 'no internet access':
This is such a borked up config.. Why are you bridging? Why would you bridge if you don't want to allow wifi talk to lan?
If you want to leverage a port on pfsense for your AP - then put it on its own network, and just allow what you want. If you want wifi on the same network as lan plug your AP into your switch.
If you want multiple networks on your AP via vlans and one of those is your lan network - then have a vlan capable switch and again plug your AP into your switch.
The config is at least 8 years old. I used to have pfSense run on a laptop with WiFi adapter. When moving my pfSense to a custom PC I decided that it is more flexible to have an external AP rather than internal. That way I can change AP in the future easily. Also choice of AP would not be dictated by support provided by Unix on which pfSense is based. To add an external AP to pfSense I jumped online to see how others do it. The tutorials I saw used bridging and so did I. I didn't really understand why but it worked so I was happy. I'm more versed now at working with pfSense and understand networking better than in the past, though as you can see I'm far from an expert.
I will be going (attempting) the route of running AP off of a dedicated pfSense port. This will give me the separation of LAN and WiFi and should work with 'Interface Bound States' in pfSense. I have an idea how to achieve that, so we'll see if it works.
-
Yup that will work if you don't need them on the same subnet.
Or moving the filtering and subnet assignment to the bridge interface would also work.
-
I am now configured with 'Interface Bound States' and no longer bridged.
Thanks for your help guys.
I like this way better. Better organized and more precise.
-
Nice. Yes that's a much better setup if you don't need them on the same subnet.

-
A related question. As I moved to unbridged LAN and WiFi networks, I noticed that a device on WiFi interface can't reach a device on LAN interface using it's host name. Using IP works.
What do I need to change in my firewall to fix this? I assume DNS is not propagating correctly.
When the two networks were bridged, this was not an issue.
-
Hmm, by default both subnets would use the pfSense interface IP as the DNS server. The would be Unbound in pfSense and if LAN devices are registered there then they should resolve for both subnets.
First try resolving from the wifi client and see how it fails. Perhaps that device is using a hardcoded DNS server? Did you ever include firewall rules to redirect DNS?
-
When the WiFi client is wired (cable) then it can access the other device via it's host name, because they're both on LAN at that point.
WiFi client is assigned DNS Servers by DHCP Server running on WiFi interface. I tried adding LAN's DNS Server as secondary entry under WiFi interface's DHCP Server but that did not change anything. I did notice at that point that WiFi client was showing two DNS Servers configured, instead of the usual one.
I did not explicitly set any DNS redirection firewall rules.
-
@skubany2 said in upgraded to pfsense 2.8.0, WiFi devices report intermittent 'no internet access':
I did notice at that point that WiFi client was showing two DNS Servers configured, instead of the usual one.
And they are both the pfSense interface addresses? Or are you using other DNS servers?
If you try to resolve one of these hosts on a wifi client what error do you see?
-
@stephenw10 said in upgraded to pfsense 2.8.0, WiFi devices report intermittent 'no internet access':
And they are both the pfSense interface addresses?
Yes.
The issue is on my parent's network and they're far away from me. On my home network I have WiFi client running VNC Server so I'll use that for testing. Using VNC I can connect from LAN to WiFi client fine when using it's IP, but when I use it's host name VNC can't resolve the name.
While testing with VNC when I capture packets on the LAN interface I see LLMNR (Link-local Multicast Name Resolution) requests and NBNS (NetBIOS Name Service) requests for the host name but don't think they're being responded to by anyone. Nothing of interest on WiFi or WAN interfaces.
-
How are you testing? Try to dig at pfSense on each address directly like:
2.8.1-RELEASE][admin@cedev-2.stevew.lan]/root: dig @172.21.16.1 +short plusdev-2.stevew.lan 172.21.16.167 [2.8.1-RELEASE][admin@cedev-2.stevew.lan]/root: dig @192.168.126.1 +short plusdev-2.stevew.lan 172.21.16.167One thing you might be seeing is the client device not sending the domain the in query automatically for servers outside the domain.
But both IP addresses should be able to resolve the FQDN. The are both the same server server and data.
-
I've done some testing yesterday. Testing was largely about reaching shared folder on LAN client from WiFi client. I was testing host name vs IP.
I have to make sure that DNS queries are not blocked. In my configuration WiFi interface in general can only reach WAN, not LAN and I have many disabled rules that I activate (one at a time) when I need to reach a LAN client.
I noticed that turning off Windows firewall on the LAN client helped in allowing WiFi client to reach it but I think this was in the case of using IP. Host name still did not work. Windows firewall was never an issue but that is when I only had Win7 machines at home. Now that I have added Win11 to the mix they might not be playing nice with each other with default settings.
Adding secondary DNS (of the other interface) under each interface's DHCP Server may also be needed. I will also look at the DNS Resolver and Forwader to see if I need to change anything there.
I will be testing DNS (rules/settings) and Windows firewall settings while running packet capture. This will take a few days but I know what to focus on and will report back with my findings.