Which kind of VIP to use? (5 statics)
-
For ping to work, you have to create a rule to allow it. It is denied by default.
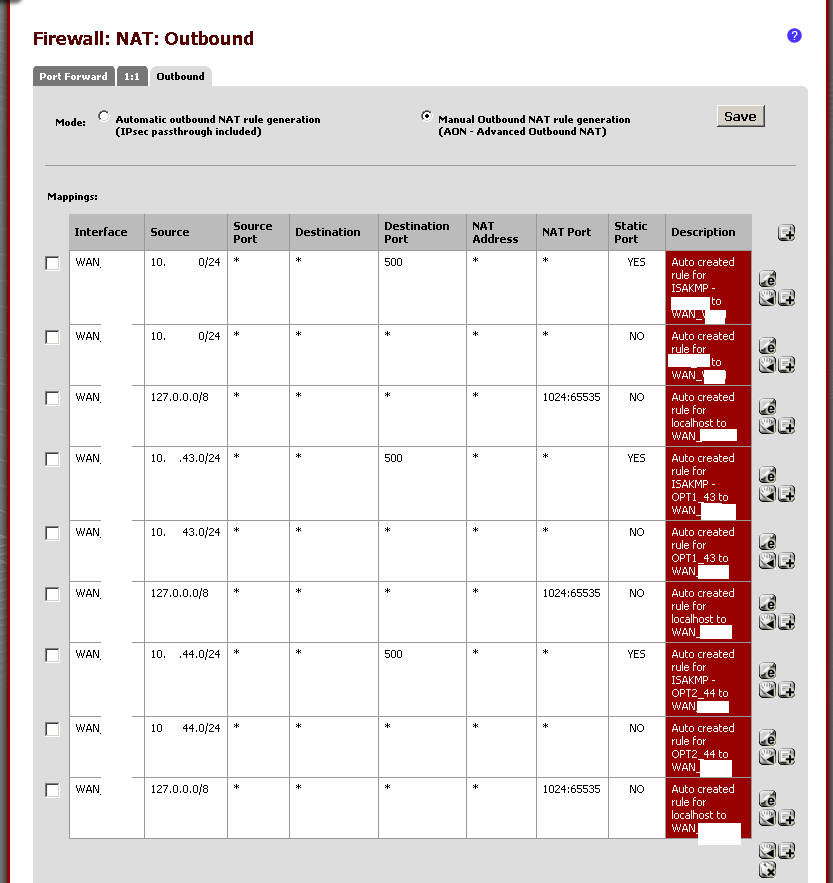
If you could, screen shot the Outbound NAT table and we can help see if it looks right. -
For ping to work, you have to create a rule to allow it. It is denied by default.
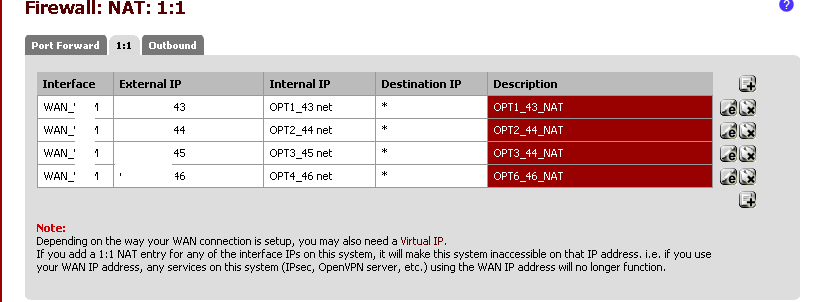
If you could, screen shot the Outbound NAT table and we can help see if it looks right.So I have all five subnets working however I still cant reach the internet from the VIP's and I also can't ping them (knowing that I may not yet have set up the proper ICMP alow rule for each VIP). My ISP can only see the #1 static working, not the four VIP's.
Here are the rules I have. I simply copies what the machine did when it switched over from auto to manual and auto populated the rules.
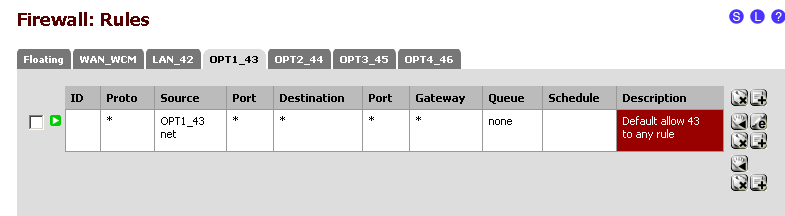
If there is anything else I can paste up please ask for it and I'll be happy to share. I am unable to hit the internet like this so something isnt configured properly either on the VIP side or on the NAT'ing side… I have not built any rules for any of the subnets - is that the simple item I overlooked? Thx.
-
If you have not created the rules in each of the interface tabs in the firewall, you are going to by default block all access. Also, you do not need the 1:1 NATs, please remove them. Use only port forwards for the inbound services you absolutely need.
-
If you have not created the rules in each of the interface tabs in the firewall, you are going to by default block all access. Also, you do not need the 1:1 NATs, please remove them. Use only port forwards for the inbound services you absolutely need.
This is what I have for the rules tabs:
I am confused why you say to delete the 1:1 NAT in favor of port forwarding. These are remote desktop sessions behind the other static IP's not web servers so depending in what they are running it could require many many port forwarding mappings.
Do I need a rule under the WAN tab to allow from WAN to each interface or is that automatic with the VIP's? As of now there are only rules on the WAN tab regarding the static #1 not the other statics or other subnets.
Thx so much for your help.
EDIT: I can ping each static IP from it's respective subnet but still I can not reach the internet even with the rule to allow as I posted just above.
EDIT #2 - when I did nothing else but delete the 1:1 NAT's now I can get to the internet from each subnet but for some reason the traffic is only going through the primary IP, not the VIP's (when I go to ip chicken it gives me the primary IP) Should I put the 1:1 NATs back?
-
With the above setup/rules the VIP's are still dead to the outside world.
My ISP can only see that one of my 5 IP's are "configured" as they say.
I can ping them and see them from the LANs though.
-
The 1:1 NAT is for using and external IP for an internal IP. Remove them. Your systems are not servers so they only need outbound rules not inbound. Port Forwards and 1:1 are for servers behind a firewall and not systems. In the manual outbound NAT you MUST specify which VIP you want each subnet to use. The way you have it posted, you are going to use the WAN interface address.
-
I can't thank you enough!!! That worked!
Thanks - I will try and document this for others but at a minimum I will help others.
-
Now I have one final question - I kept it here but it may be a routing question??
Now that I have started to move over a few test machines to the static IP's I am realizing that I can't re-connect to them. Is the process for setting up ports, remote desktop and VNC pass through the same with VIP's or is that also more complicated.
Thx.
-
If you are trying to connect to them from the internet, the process is the same. If you are looking for inter-LAN communication, you should be able to access them via their internal IP address in the new subnet. The allow all rule you have on each LAN should pass all the communications.
If you want to restrict that, you are going to have to create a series of aliases and change the default rule.
If you are using DNS names, then I would use the DNS forwarder's override to create a split-brained DNS. This way if you are internal and you are using the pfSense firewall for DNS services, then when someone from the inside requests the DNS name they will get the internal address. But if you are on the internet, you get the VIP address.
I am sure there are more options as well depending on what exactly you are doing.
-
If you are trying to connect to them from the internet, the process is the same. If you are looking for inter-LAN communication, you should be able to access them via their internal IP address in the new subnet. The allow all rule you have on each LAN should pass all the communications.
If you want to restrict that, you are going to have to create a series of aliases and change the default rule.
If you are using DNS names, then I would use the DNS forwarder's override to create a split-brained DNS. This way if you are internal and you are using the pfSense firewall for DNS services, then when someone from the inside requests the DNS name they will get the internal address. But if you are on the internet, you get the VIP address.
I am sure there are more options as well depending on what exactly you are doing.
I got it sorted and I want to thank you publicly (not just by PM). I learned a lot during the process and I will make an effort to check the forum to try and help others.
Thanks again!! I appreciate the help.