Recommendation cheap unit for a 74 years old senior citizen :-)
-
Yes indeed.
To be honest, I trust my little ISP 100x more, than any third party public/payed VPN endpoint, which actually does nothing else but aggregates traffic in order be more easily captured…
I see one reason to use VPNs like this though, for example to access geo-protected content from outside the allowed area. For example, to use BBC's iPlay service from outside UK. But that won't give me any privacy, at least looking from UK...
-
Do we have any figures for Snort or VPN on the APU? I'm sure there are some.
Again in German:
https://forum.pfsense.org/index.php?topic=73885.msg403913#msg403913
Looks fairly capable.Steve
Thank you Lord Steve ;D
I accidentally found this morning on page 6 of the thread you refer to this:
@JAP:
Ich verwende das Teil als VPN-Router mit dem CYBERGHOST Dienst OpenVpn Verschlüsselung AES-256-CBC.
Durchsatz auf einem 16Mbits Anschluss 13Mbits konstant im download mit OpenVpn.
Fakt ist 100% mehr Durchsatz als mit einem handlsüblichen Router wie Asus RT-AC66U,da geht noch mehr.
Wegen der Leds u. des Pushbuttons warte gespannt.So he loses around 20% using the VPN, but that is with the AES-256-CBC. I use BF-CBC, and I have no clue if that will make a (dramatic) difference when I use the APU. I use it on the first box in my sig, suggested to me by an extremely knowledgeable and kind person on this board, so I take it my CPU and board are more powerful than the little APU.
But perhaps BF-CBC is less a struggle for the CPU, so it might be less performance loss? Or the other way around of course.
-
I was always wondering, how can you trust any third party to forward all your traffic thorugh? What's the guarantee, that they are not doing exactly the opposite of what they say? I mean, capturing all the traffic and forwarding it to NSA is the easiest way to do it like this. And they take your money also, making you believe that you are actually privacy-protected. From who?
Yes, that's the problem with VPNs. You can be reasonably confident that the traffic between you and the VPN end point is secure (as long as you're not using an NSA sponsored encryption!) but that is all. After it is decrypted at the end point all your traffic is visible to anyone operating the end point or to any further hops before it's final destination. Now that may not be an issue. If your goal is to hide your traffic from your ISP, for example, then you've done that.
Yes indeed.
To be honest, I trust my little ISP 100x more, than any third party public/payed VPN endpoint, which actually does nothing else but aggregates traffic in order be more easily captured…
I see one reason to use VPNs like this though, for example to access geo-protected content from outside the allowed area. For example, to use BBC's iPlay service from outside UK. But that won't give me any privacy, at least looking from UK…
Could I ask what you mean with the part in bold? How is this easier?
My reasoning for using a VPN is this: I actually don't trust my ISP enough, nor any other ISP in my country. Since the NSA stories it is clear that governments around the world all spy on their citizens massively. Only some days ago Vodafone declared that in the UK the government is automatically, without any warrants and judges, tapping all cell phones. So my reasoning is: what is easier for governments to do than to tell all national ISP's to not ask questions when the men in black arrive and install mysterious black boxes in their server rooms? So goes my reasoning: it is not that easy for any national government to install mysterious black boxes in server rooms of ISP's/VPN-providers in other countries. So if my VPN exit point is not in The Netherlands but in Germany, at least my own government can not automatically see what I do. The German government of course can, but they will probably not be interested in me, as I am not living in their country. Of course, should I be a criminal whom the Dutch government is after, they might, and probably will, ask the German government to tap me via the VPN-exit point in Germany. But knowing our neighbors, they will probably want some international warrant for that. So what I've effectively achieved (at least that is what I am assuming) is that I've put automatic surveillance into manual surveillance.
Now I am not doing anything illegal, but I still don't like this 'big data that will bite you in 20 years from now when the world without doubt has turned into a massively ugly place'. My assumption from automatic to manual should have taken care of that.
Unless I am wrong, which is not to be ruled out as I am Dutch, and most of us are plain stupid ;D
Please correct me if my reasoning is wrong somewhere?
-
@Hollander:
so I take it my CPU and board are more powerful than the little APU.
Yes, significantly.
@Hollander:
But perhaps BF-CBC is less a struggle for the CPU, so it might be less performance loss?
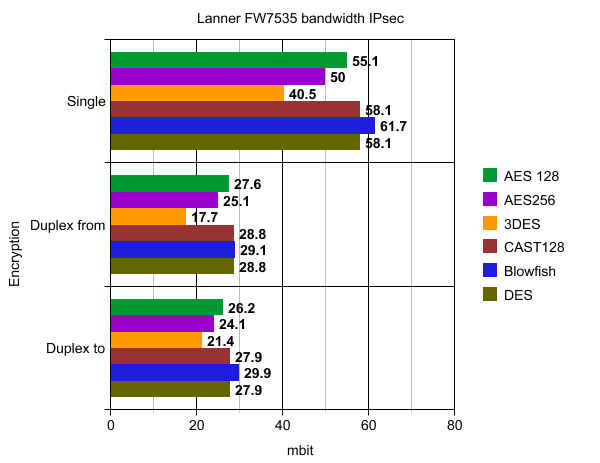
Yes, Blowfish appears to be faster than AES-256, especially if you have Blowfish set to it's default 128bits. See Seth's nice graph from an Atom D510:
Steve
-
@Hollander:
My reasoning for using a VPN is this: I actually don't trust my ISP enough, nor any other ISP in my country. Since the NSA stories it is clear that governments around the world all spy on their citizens massively. Only some days ago Vodafone declared that in the UK the government is automatically, without any warrants and judges, tapping all cell phones. So my reasoning is: what is easier for governments to do than to tell all national ISP's to not ask questions when the men in black arrive and install mysterious black boxes in their server rooms? So goes my reasoning: it is not that easy for any national government to install mysterious black boxes in server rooms of ISP's/VPN-providers in other countries. So if my VPN exit point is not in The Netherlands but in Germany, at least my own government can not automatically see what I do. The German government of course can, but they will probably not be interested in me, as I am not living in their country. Of course, should I be a criminal whom the Dutch government is after, they might, and probably will, ask the German government to tap me via the VPN-exit point in Germany. But knowing our neighbors, they will probably want some international warrant for that. So what I've effectively achieved (at least that is what I am assuming) is that I've put automatic surveillance into manual surveillance.
Now I am not doing anything illegal, but I still don't like this 'big data that will bite you in 20 years from now when the world without doubt has turned into a massively ugly place'. My assumption from automatic to manual should have taken care of that.
Unless I am wrong, which is not to be ruled out as I am Dutch, and most of us are plain stupid ;D
Please correct me if my reasoning is wrong somewhere?
Are you serious? To my knowledge Denmark doesnt work together with the NSA. In Germany it is known that ALL citizens are spied by the NSA and that germany is one of some "heavily spied" Nations worldwide - like Afghanistan and IRAK.
Our cancellor "Angela Merkel" didn't want to do anything against this, it is even KNOWN that the german "Geheimdienst" cooperates heavy with the NSA.
Some folks now have startet a complaint against the US Nation and the NSA because of massive spying. The "Bundeststaatsanwaltschaft" (I would call it the most important Lawyer in Germany) has REFUSED to start an investigation!If you are lucky your traffic is routed via USA or Great Britain to Germany, which woldn't help you at all.
I started using pfsense at home for exactly the reason to protect my home as much as possible.
Use encryption whenever possible, but don't trust any company or nation!
-
@Hollander:
So if my VPN exit point is not in The Netherlands but in Germany, at least my own government can not automatically see what I do.
Yes, that's true. However what they can see is that for some reason you are choosing to encrypt all your traffic and send it to another country. Like it or not that's probably going to cause someone to be suspicious. That's just the world we live in unfortunately. Just need to persuade many more people to start using 100% encrypted traffic for yours not to look unusual. ::)
Steve
-
German secret service is the LAST to trust, except for Five Eye and the Sweds (deep in the rectum of the US…) and the Danish, doing the surveillance of the German mobile net for the US and the CSC story and and and...
The aim is "master the internet", i.e. 100% coverage.
I'm 100% sure my tunnels are decrypted ALL THE TIME I use them, from compromised encryption standards, etc. pp.
Read about the people behind OpenSSL, not that funny.
Cisco buying Snort, not funny AT ALL.Deal with it. The net is fu**ed up, totally, completely and for a very long time, if there will be any form of privacy at all in the future.
-
@Hollander:
My reasoning for using a VPN is this: I actually don't trust my ISP enough, nor any other ISP in my country. Since the NSA stories it is clear that governments around the world all spy on their citizens massively.
Long story short, I think you are walking straight into their trap by using a VPN like this. A VPN solution like this doesn't even need any black box to capture the unencrypted data. I'm 100% sure that these VPN companies are nothing more than one of the many tools NSA and their brothers to get the data. As stephenw10 said, by using it constantly you're doing nothing else than attract attention to yourself.
Actually, there's nothing to hide by using home internet decently. Torrents and stuff could cause an issue, but they could easily track you through the VPN if they would (since you are in a contract with the VPN provider, you already gave all the data about yourself when you paid for the service - and that makes even easier to track you down than researching through your own country's ISP databases or blackboxes).
A 74 years old senior citizen has nothing to be afraid concerning privacy IMHO… by the time anybody would want to use his data against him, he would most probably not using internet anymore...
-
I would like to thank you all very much for your inputs and help. I will go on and buy the APU for my neigbor.
Your insights on the VPN are food for thought, and therefor much appreciated also ;D
-
@chemlud:
German secret service is the LAST to trust, except for Five Eye and the Sweds (deep in the rectum of the US…) and the Danish, doing the surveillance of the German mobile net for the US and the CSC story and and and…
Herr Mitterwald seems to think Denmark is still to be trusted, and I vaguely recall there is a VPN provider over there who salutes himself for that.
@chemlud:
Read about the people behind OpenSSL, not that funny.
Deal with it. The net is fu**ed up, totally, completely and for a very long time, if there will be any form of privacy at all in the future.
Could I ask which story of the people behind OpenSSL?
And, if I may; how do you deal with it then? Nothing at all?
-
Hum, sorry, I forgot, one last question: do I need to put a SSD in there, or can I stick with an SDHC card or something like that? (I had trouble understanding the stuff about ´USB connectors´ in the other thread. I know nothing except for connecting a HDD to a SATA-connection, and a USB is a stick that sticks outside my computer ;D
It is not easy for a stupid Dutch person btw to type on a German layout keyboard, as I am currently doing: each sentence takes about 10 minutes ;D ;D ;D
-
It depends on what you end up running on it. Use an SD card of you aren't going to be using Snort or Squid.
Steve
-
It depends on what you end up running on it. Use an SD card of you aren't going to be using Snort or Squid.
Steve
Thank you Knight Steve ;D
I've changed my mind: I will not buy an APU.
The reason is the people that know, on this forum, are recommending switching from Snort to Suricata. I did this yesterday as a test. My RAM is now 72% of 8 GB, so 5,6 GB. the APU has only 4 GB. And who knows what the future will bring for Suricata. I want to give the old senior citizen something he can use for the next 10 years.
This box looks nice:
http://www.mini-box.com/M350S-enclosure-with-picoPSU-80-and-60W-adapter
(Via: https://forum.pfsense.org/index.php?topic=70936.0).
Now of course is to find an appropriate motherboard and CPU - not too expensive for this old man. There once was a great great man on this very forum who helped me get my Intel board and Celeron CPU as a good match. You never know if he will pull something out of his magical hat again ;D
-
I must have missed my name in the honours list. ;)
That is a surprisingly high memory usage even for Snort. I'm guessing you have a lot of rules and have the filtering algorithm set to something memory hungry.
What seems like only a few years ago (more like 10 at least!) I used to run IPCop here at home. At the time I had an 8/0.5Mbps DSL connection and the hardware I was running was a Cyrix-333 with 196MB RAM. I ram Squid and Snort on that machine with no noticeable slow down. Here's a guy filing a bug report because Snort won't run in 96MB! It's hard for me to get my head around the current Snort requirements given that. ;)There are many people using the M350 it seems to be well tested.
I'm yet to find a board that seems as suitable for a moderately powerful firewall as the DQ77KB. Supermicro have some pretty nice options, for example: http://www.supermicro.com/products/motherboard/celeron/X10/X10SBA.cfm
Don't know if anyone else has tried them yet and they're expensive. There are other manufacturers coming out with similar boards though. Celeron J1800/1900, dual Intel NICs, mini-ITX, DC power-able seems like a sweet spot for a home firewall.Steve
-
I must have missed my name in the honours list. ;)
:o ??? :P
(The man I was referencing knows who I mean - he keeps on refusing to let me buy him a coffee ;D )
That is a surprisingly high memory usage even for Snort. I'm guessing you have a lot of rules and have the filtering algorithm set to something memory hungry.
What seems like only a few years ago (more like 10 at least!) I used to run IPCop here at home. At the time I had an 8/0.5Mbps DSL connection and the hardware I was running was a Cyrix-333 with 196MB RAM. I ram Squid and Snort on that machine with no noticeable slow down. Here's a guy filing a bug report because Snort won't run in 96MB! It's hard for me to get my head around the current Snort requirements given that. ;)It apparently is a (rather serious) problem with Suricata. At the peak this morning it was running 94% ( :o ). That is almost 8 GB of RAM. Then I stopped it and went back to Snort.
It was running on 4 interfaces, with Snort subscription 'security' and all ET rules except for two (I'm playing with it, I know it is overkill). On Suricata, like said, it ran between 70-95%, on Snort it is back to 32%.
There are many people using the M350 it seems to be well tested.
I'm yet to find a board that seems as suitable for a moderately powerful firewall as the DQ77KB. Supermicro have some pretty nice options, for example: http://www.supermicro.com/products/motherboard/celeron/X10/X10SBA.cfm
Don't know if anyone else has tried them yet and they're expensive. There are other manufacturers coming out with similar boards though. Celeron J1800/1900, dual Intel NICs, mini-ITX, DC power-able seems like a sweet spot for a home firewall.Steve
Thanks for this suggestion, Steve ;D It indeed is an expensive board, and given that socket (not 1155), it is probably not upgradeble(?)
I was looking at the supermicro X10SLV: http://www.supermicro.com/products/motherboard/Core/H81/X10SLV.cfm
That is upgradeable I think(?),
Bye,
-
Indeed that is upgradable. Just as an example Asrock make a number of boards for embedded integration some of which are virtually identical the that Supermicro. For example:
http://www.asrock.com/ipc/overview.asp?Model=IMB-180
A different CPU socket but otherwise very similar. No idea where you could buy that though. ::)Steve
-
The similar asrock board is not rangeley, but rather avoton. No quick assist, only two Ethernet, and that asrock board is tuned for storage.
I have had an APU on a 1gps/1gps connection for a few days (yes, to my home), it tops out at just under 300Mbps. The same Mac gets over 900mpbs directly connected.
I'll be replacing the APU shortly.
-
Not jealous of your home gigabit connection at all! ::) is that Google fibre or have you got others offering 1Gbps in Austin now?
I think there would be quite a few people interested in what hardware you choose to run for that connection Jim.Steve
-
This is Grande. AT&T is also offering 1Gbps/1Gbps in ATX, but even though they have fiber on the side of my house, they don't want to offer me the service.
When Google arrives, I'll be keeping both.
