Accessing a bridged Vigor120 modem
-
There is no need to use VLANs with this setup.
You just need to add an additional standard interface and assign your WAN physical NIC to it. Everything else looks good.One thing to watch out for is that using this hack the V120 can take a little while to respond at first, like 5-10secs. So don't instantly assume it hasn't worked. Once connected it's as fast as normal.
Steve
-
Hi Steve, thanks for the reply. I added the VLAN because I couldn't seem to assign another interface to the same NIC:
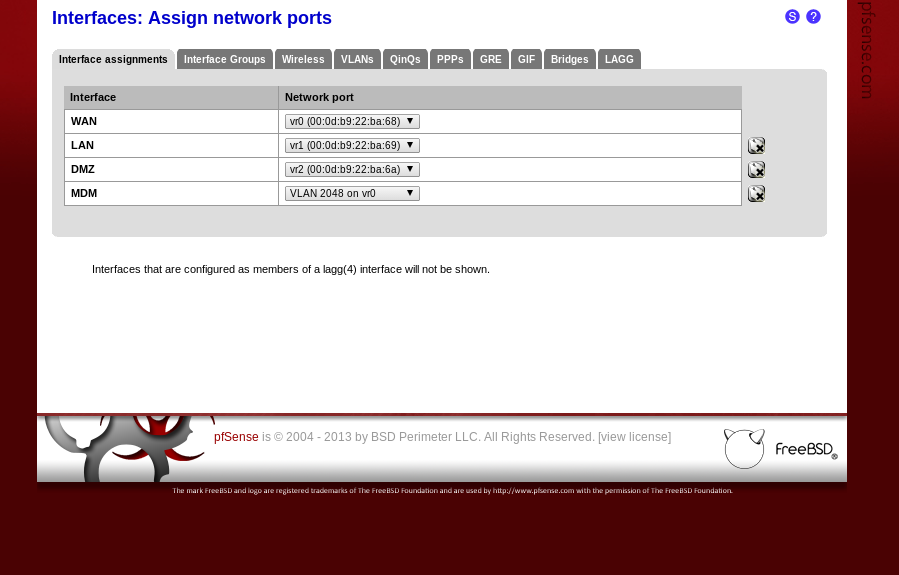
Even with the MDM interface and the VLAN removed, there is no "add" button (and adding act=add to the url results in the error "No more interfaces available to be assigned"). Is there another way of adding an interface that I'm missing?
-
Hmm, usually the WAN interface would be assigned to PPPoE0 leaving the physical interface available.
How are you connecting to the internet?Steve

-
My Vigor is connected via MPoA, and the WAN interface using DHCP. I've just noticed that according to Draytek's FAQ, this setup is virtually unique to my UK ISP (O2)…
-
Ah, OK. Much trickier then!
You would need to add an IP alias (virtual IP) to the WAN interface in the modem subnet. Then either the wide subnet hack or other methods described in the docs. I've never had to do that so I can't be too specific.Steve
-
I set up a virtual IP of 192.168.0.1/24, which worked very briefly - I could access the Vigor, but the connection was very slow, and multiple iframes within the admin page then reported "connection refused". Shortly after that it disappeared altogether again - connections now time out. Also for anyone else reading this in the future, don't forget to turn off the "Block private networks" option for the WAN interface.
Considering the route from the modem is known to work, I think it's likely the route to it that is failing. I tried adding a filter rule on the WAN interface to reject anything with a destination of 192.168.0.0/24 (as a test), but my connection to 192.168.0.2 still just timed out. Do virtual IPs bypass rules configured for their interface?
-
Hmm. I don't know if I'm honest.
Which type of virtual IP did you choose?You might be better off using one of the original techniques described in the docs for 1.2.3. Back then the PPPoE interface used the physical NIC assignment so the situation was similar to your current setup.
Steve
-
I tried adding a filter rule on the WAN interface to reject anything with a destination of 192.168.0.0/24 (as a test), but my connection to 192.168.0.2 still just timed out. Do virtual IPs bypass rules configured for their interface?
Interface firewall rules apply to packets entering the box from that interface, not packets leaving the box on that interface.
-
Hi guys, thanks for the responses, and apologies for the delay in replying. Entirely coincidentally (something it took me 2 weeks to establish), my Vigor 120 is now dropping packets for no reason. Since Draytek has told me packet dropping is likely to be a faulty device, and considering they're quite expensive (I'm 2 months out of warranty, of course), I have a TP-Link TD-8616 on order instead.
The TD-8616 advertises bridging capabilities, so I may be back in this thread shortly. If not, thanks again. :)
-
Hi again! I've been using my TD-8616 for a year now, and want to have another shot at getting it accessible from my LAN using Steve's method above.
My new ISP uses PPPoE, so I've got an interface assigned to the physical NIC as in the original guide (and unlike earlier in the topic). I have the netmask for the modem set to 255.255.0.0 to allow it to return packets, but the modem's LAN doesn't share a switch with the LAN I want to access it from. Should it? As it stands the modem isn't responding and I'm wondering if that's the issue.
-
The modem shouldn't share a switch with your LAN side clients. pfSense is in between firewalling the traffic. It will route the traffic between the subnets though so it's not a problem.
Not all devices can work with the /16 subnet, the V120 happens to do so but it's a hack. My router I use as an access point cannot talk to anything outside its own /24. I'm yet to find a good solution for it.
You can always use NAT to access it though as described for 1.2.3.Steve
-
The modem shouldn't share a switch with your LAN side clients. pfSense is in between firewalling the traffic. It will route the traffic between the subnets though so it's not a problem.
Not all devices can work with the /16 subnet, the V120 happens to do so but it's a hack. My router I use as an access point cannot talk to anything outside its own /24. I'm yet to find a good solution for it.
You can always use NAT to access it though as described for 1.2.3.Steve
Thanks Steve, I actually just got it working using the 2.0 method - for the outbound NAT rule I borrowed a little from the 1.2.3 method. These are my settings:
Interface: OPT
Source: 192.168.1.0/24 (my lan subnet)
Source Port: *
Destination: 192.168.0.0/24 (my modem subnet)
Destination Port: *
NAT Address: OPT address
NAT Port: *
Static Port: NOI also have the modem's subnet configured to /24 again, if that's worth mentioning.
-
Nice. :)
One thing to be aware of is that to add NAT rules you will have had to switch to manual outbound NAT. That means that you have to remember to add NAT rules for any interfaces you now add, new NICs, VLANs, VPNs etc.
An alternative is to leave outbound NAT set to auto and add a gatway to the modem access interface. pfSense will now NAT that connection. Make sure your real WAN gateway is set as default though or your'll loose all internet access!
In 2.2 there will be a hydrid NAT mode where rules are auto generated but manual rules can be added. That will negate this issue.Steve