Blocking SSH - Firewall Rule Troubles - SOLVED
-
So, I did mention it in the original post, but the "Public" net is the one that is advertised by us via BGP. Consider it a DMZ of hosts - 64.141.y.x. To permit routing to those hosts via the two WAN interfaces, do I not need to implicitly allow traffic to them, to avoid the default block rule???
-
Yes.
Please post all applicable interfaces, subnets, and rules. Trying to help you with everything obfuscated is nearly impossible. PM if you must. They're just IP addresses.
-
You would need to allow the services you want to run on those IP.. that sure and the hell wouldn't be a any any ;)
-
So if I am serving Internet to multiple commercial/industrial customers on that network, shouldn't I be passing everything to them and letting them control their own firewalling? I will take new screenshots of all rules and post them in a minute…
-
Okay, soooo….
Shaw WAN (WAN1) - 64.141.127.248/29
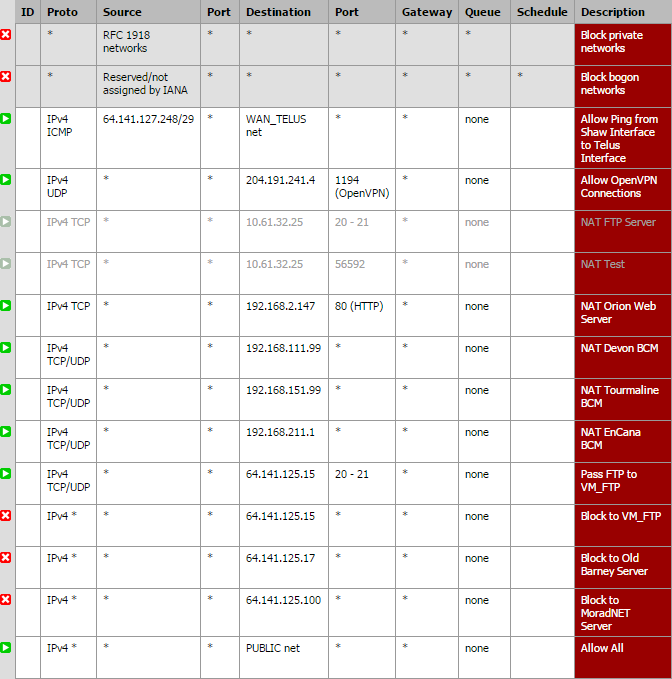
Telus WAN (WAN2) - 204.191.241.0/29
Public (~DMZ) - 64.141.125.0/24 - advertised on both WANs via BGPShaw WAN Rules:
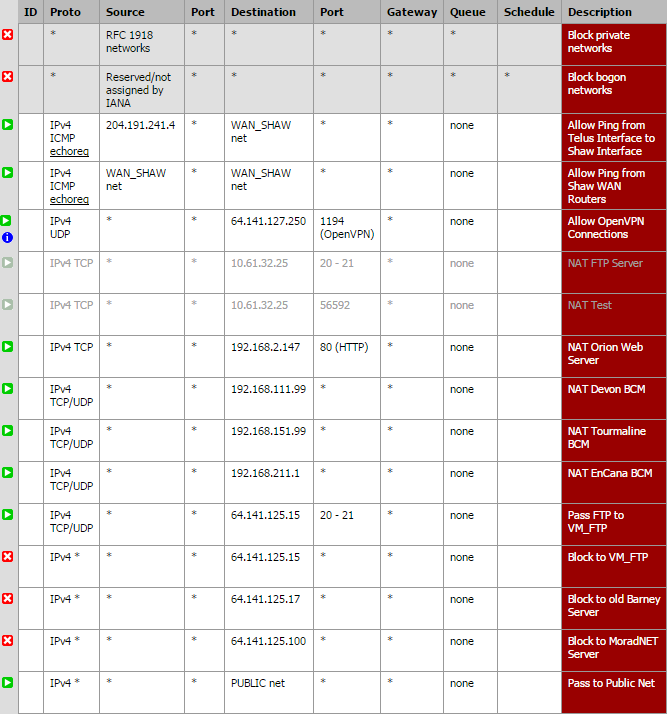
Telus WAN Rules:
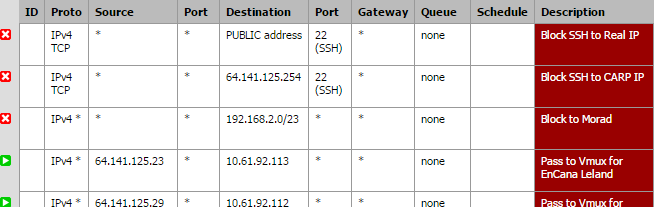
Pubic Interface Rules:

All of these are for VoIP devices - companies host POTS lines here and we connect them to VoIP adapters and transport to their remote facilities via our microwave network.
Also, there are no rules in the floating tab.
-
To be honest anyone that would run a ssh server that allows passwords is asking for trouble, whenever I bring up something that has ssh enabled - first thing I do is enable public key and turn off password auth.
I'm all for more security. What do you mean? Do you use a hardware credential? On these two systems I am the only one that ever uses SSH for access (but limited access).
-
public key auth - look it up. Takes 2 seconds to implement.
So your routing traffic to this segment behind pfsense. So pfsense has an IP in this network, and it listens on ssh because you enable ssh. So block ssh to that interface IP.
So this segment
Public (~DMZ) - 64.141.125.0/24Pfsense is what 64.141.125.1 ?? Block traffic to pfsense IP from the public internet - I agree your customers need to do their own firewall if not using your services for that.
-
That's what I had done originally - I had rules to block SSH to the interface's real IP and the CARP IP. I will add them again right now.
-
And you mention you see stuff in the logs for attempted auth.. And what IP are they authing too?
If that is the IP I can validate if ssh is open to the public.
-
That's what I had done originally…
I did the same. My rules don't seem to work after I enable the SSH server via the checkbox.
Floating:
block IPv4 TCP/UDP * 22 (SSH) WAN address 22 (SSH) * noneWAN:
block IPv4 TCP/UDP * 22 (SSH) WAN address 22 (SSH) * none -
I just added the rules again and changed the port back to default 22. You can try to SSH to 64.141.125.250, .251 or .254 (CARP).
-
I just added the rules again and changed the port back to default 22. You can try to SSH to 64.141.125.250, .251 or .254 (CARP).
They are all open. Sounds like your rules aren't working either.
-
Source is not going to be 22 source could be ANY, and ssh is not UDP..
And yes that is open!! on the 250, 251 and 254
login as:
Password for admin@router1.morad:
251 shows
steve.morad -
Ah, yep. Good point. I'll make the change and try again.
-
dude you should not have to put in any rules.. There is a default DENY!! Are you allowing traffic in like the OP?
if your going to block it has to be above your allow rule - post your rules.
If you have an allow for that segment, then above it put in a block to those specific addresses.
-
For me, I pretty much never put in a source port. As others have said, they are usually random, so no point. And also, I put them right at the top - since they are handled from the top down, start with the most specific and go from there.
-
My DMZ, or Public routed interface rules look like this now…
-
so anherman - are you rules in place to block it then? Cuz they are still open. 2 all 3 IPs.
So you have a 1:1 nat setup or something? Or your just routing the traffic?
-
Yup, those rules are active. No, no 1:1 set up at all. I do have some inbound stuff set up, but specific ports like 21, 80, 443, etc. Although I do have a couple that I have all ports forwarded to 3 customer devices, just because I don't know what ports they use - those are the ones noted in the middle of the WAN rules (noted as BCM access). But those are other IPs. Dumb question, how can I see what IP's they are trying to get authed on? My pfflowd packages aren't working, so I'm not sure how to look.
-
For me, I pretty much never put in a source port. As others have said, they are usually random, so no point. And also, I put them right at the top - since they are handled from the top down, start with the most specific and go from there.
Yeah it was towards the end of the day when I put that original rule in. I've since modified it to read as:
block IPv4 TCP * * WAN address 22 (SSH) * none
I've corrected both the Floating and the WAN but I'm still telling you, SSH is open. The default deny isn't working in this case. Once that SSH server is enabled, it's WAN accessible on my box.
My top 3 rules on the WAN tab (apologies on the formatting):
block * Reserved/not assigned by IANA * * * * * * Block bogon networks
block * Private_Networks * * * * none (custom rule)
block IPv4 TCP * * WAN address 22 (SSH) * none Block SSH remote accessI don't have any 1:1 going either.