Blocking SSH - Firewall Rule Troubles - SOLVED
-
Source is not going to be 22 source could be ANY, and ssh is not UDP..
And yes that is open!! on the 250, 251 and 254
login as:
Password for admin@router1.morad:
251 shows
steve.morad -
Ah, yep. Good point. I'll make the change and try again.
-
dude you should not have to put in any rules.. There is a default DENY!! Are you allowing traffic in like the OP?
if your going to block it has to be above your allow rule - post your rules.
If you have an allow for that segment, then above it put in a block to those specific addresses.
-
For me, I pretty much never put in a source port. As others have said, they are usually random, so no point. And also, I put them right at the top - since they are handled from the top down, start with the most specific and go from there.
-
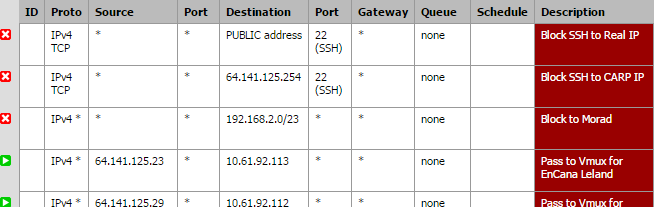
My DMZ, or Public routed interface rules look like this now…
-
so anherman - are you rules in place to block it then? Cuz they are still open. 2 all 3 IPs.
So you have a 1:1 nat setup or something? Or your just routing the traffic?
-
Yup, those rules are active. No, no 1:1 set up at all. I do have some inbound stuff set up, but specific ports like 21, 80, 443, etc. Although I do have a couple that I have all ports forwarded to 3 customer devices, just because I don't know what ports they use - those are the ones noted in the middle of the WAN rules (noted as BCM access). But those are other IPs. Dumb question, how can I see what IP's they are trying to get authed on? My pfflowd packages aren't working, so I'm not sure how to look.
-
For me, I pretty much never put in a source port. As others have said, they are usually random, so no point. And also, I put them right at the top - since they are handled from the top down, start with the most specific and go from there.
Yeah it was towards the end of the day when I put that original rule in. I've since modified it to read as:
block IPv4 TCP * * WAN address 22 (SSH) * none
I've corrected both the Floating and the WAN but I'm still telling you, SSH is open. The default deny isn't working in this case. Once that SSH server is enabled, it's WAN accessible on my box.
My top 3 rules on the WAN tab (apologies on the formatting):
block * Reserved/not assigned by IANA * * * * * * Block bogon networks
block * Private_Networks * * * * none (custom rule)
block IPv4 TCP * * WAN address 22 (SSH) * none Block SSH remote accessI don't have any 1:1 going either.
-
ok heres another thing - once you create the rules to block. You have to kill the states.. So for example got in.. You need to kill all the states from my IP, or flush them all. Or have to wait til they expire.
-
I actually added the rules, and then I turned SSH on and back to 22. Would that have not allowed the states to begin with? Or no?
-
no that would not have flushed the states in the firewall. That just tells the box to listen or not listen.
-
Okay, I just reset all states - that should confuse some people. I will watch the logs now…
-
so you do understand its not just ssh that is open

-
If you PM a login - I would be happy to take a look to what is going on.
And ssh is still open.. If you flushed the states.. You go something major issue here.. Either your rules are not being applied or you have something that in front of it allowing it.
pfctl -sa
Lets take a look at the rules..
-
PM sent. Thanks John.
Just joking. Apparently I hit the email button instead.
-
I don't even know where to start with what's wrong with your rules. You might want to start over.
Of course everything is open. You are connecting to something on PUBLIC net. He has pass any any rules for that subnet from WAN1/WAN2.
-
Ok first thing I see is you have that allow any any rule on multiple interfaces.. So wan_shaw has any any to public net, and there is no blocks on that interface. So when I do a trace to that IP I hit..
13 49 ms 49 ms 47 ms 66.163.70.2
14 55 ms 52 ms 64 ms 64.141.125.254What what connection is that 66.163.. So you have that allow on all your interfaces?
-
Looks like that 66.163.70.2 is the router on our Shaw WAN - the address that I hit there is 64.141.127.249.
-
Ok I put in a rule on your shaw wan to block ssh to your .250, 251, 254
And I it looks blocked now.
-
Ok I added logging to the rule, and you can see blocked from my attempt to all 3 of them
Your going to want to go through these connections and block services to pfsense interfaces. So for example I was able to remote in.. that should clearly be something you only allow when you want it.. And put in specific rule for ;)
