Unbound seems to be restarting frequently
-
I had to go back to DNS Forwarder (dnsmasq) because of this. Thank God it's still inthere and only a checkbox away.
-
I know a bug report is not really the place for arguing about the merits of a solution, but I respectfully maintain some of my caution in https://forum.pfsense.org/index.php?topic=89589.msg568394#msg568394 , especially in relation to ky41083's assertion that there is no need ever to restart Unbound.
Changes in local-data can be handled via unbound-control as ky41083 says - though the inability to remove just the A or AAAA record will likely require some care, as both can exist for the same local host and there is no guaranteed temporal relationship between changes in A and AAAA. In particular, DHCP and DHCPv6 are entirely separate and not synchronous.
Unlike ky41083, I cannot see any alternative to restarting Unbound if there are configuration changes made to Unbound beyond changes to local data, as SIGHUP and unbound-control reload unfortunately amount to a reload at present (i.e. cache flush and re-read of the configuration files). unbound-control does not allow for on-the-fly reconfiguration of all aspects of Unbound. This is why I suggested a diff based approach on the forums as one possibility.
These are, of course, implementation points. I agree that Unbound should be reconfigured on-the-fly whenever possible. In time, I hope that Unbound will get saner SIGHUP handling, but this will likely be a lot of work.
Unfortunately, I have no time to work on this issue at present.
You are under thinking the problem and over thinking the solution.
Quickly now…
DHCPv4 & DHCPv6 are entirely separate and not synchronous, agreed. DNS records are only removed when a lease expires, right? How many milliseconds do you think will differ between v4 and v6 leases being obtained by the same host? So deleting just the A or just the AAAA record, vs removing them both at the same time, matters how much, in the real world? Milliseconds, that you can no longer resolve an internal host via DNS, which has been off for (DHCP lease period) anyhow.
If this causes issues for you, make your DHCPv4 & DHCPv6 lease expiration times identical, or fix your DHCP clients that aren't requesting v4 and v6 leases at the same time for who knows why.
If this is causing internal host overrides to be removed, you're putting persistent local host DNS records in the wrong place. DNS is where you put external DNS redirects. DHCP reservations is where you put persistent local host DNS records so they never get removed.
Please, I would love a correct list of things that cannot be changed without restarting Unbound, from someone that's not me.
-
This solved it for me:
https://forum.pfsense.org/index.php?topic=102470.msg578573#msg578573
- John -
Ring a ding ding same here.
Though I had track disabled, I had to just completely disable IPv6 in sys/adv/networking. -
This solved it for me:
https://forum.pfsense.org/index.php?topic=102470.msg578573#msg578573
- John -
Ring a ding ding same here.
Though I had track disabled, I had to just completely disable IPv6 in sys/adv/networking.There is an issue in Unbound, I will have to disable DNSBL so that there is no "server:include: /var/unbound/pfb_dnsbl.conf" in Unbound custom options window.
see my posts: https://forum.pfsense.org/index.php?topic=113193.0 and https://forum.pfsense.org/index.php?topic=114277.0
so far no response from pfSense Dev teams.
-
I also have found unbound is restarted whenever wan ipv6 is renewed on dhcp6.
so First this occurs
/rc.newwanipv6: rc.newwanipv6:then gateway etc. been set
After this occurscheck_reload_status Reloading filterAt same time in resolver log unbound is restarted.
Now with only small dnsbl lists loaded in pfblockerng this is not a major issue as I have found even uncached queries on my pfsense box are faster than when I used the asus ac68 as my router, however each unbound restart does also have to process the dnsbl lists which is a slow process if I have large lists loaded.
I will look at the pfsense code and see if I can submit a fix that will be accepted, its probably easy to hack this like someone did earlier in the thread but ideally a clean solution would be found that can be accepted as a improvement, since there is no need to restart unbound just for renewing the same ipv6 prefix.
using"SECOIT GmbH" code, is ok but I think will stop unbound been reloaded when dnsbl gets updated daily on my box, so instead I commented out a line in rc.newwanipv6 which forces a unbound restart. Later after sleep I will look into only skipping the unbound restart in rc.newwanipv6 when its not on bootup and when the actual ipv6 on the pfsense box has not changed, so in other words add a check to see if the new ipv6 matches the previous, if it does skip the reload.
-
I have WAN and LAN IPv6 both static and I am also affected by it.
-
For 2.3.x users without DNSBL active, this fixes everything. Someone could easily make a diff patch for DNSBL based on it as well:
https://forum.pfsense.org/index.php?topic=119467.msg661037#msg661037 -
hi, same problem. IPv6 every 15 minutes starts unbound and with dnsbl it tooks a long time..
ky41083, your link doesn't work, same here https://redmine.pfsense.org/issues/5413
Any solution? cache or not is not realy the problem, no answer is what I get.
pfadmin
-
+1 I am affected by this as well. Whenever the DHCP logs show "Sending HUP signal to dns daemon(17620)" the DNS logs show that unbound has reset.
-
+1 I am affected by this as well. Whenever the DHCP logs show "Sending HUP signal to dns daemon(17620)" the DNS logs show that unbound has reset.
+1. Same problem for me too. I was using using DHCP on my Windows Server originally without problem but have now since switched to using pfSense for DHCP as the layout and customization is better suited to my liking. Since changing, I have noticed Unbound stopping from DHCP interfering with it like you say and others here have said. I took some screen shots of the logs too if it could be of assistance.
I also use pfBlockerNG with DNSBL also.
Cheers.
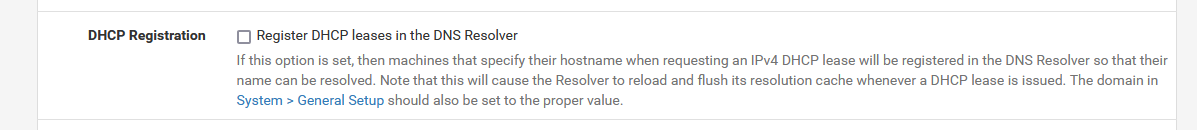
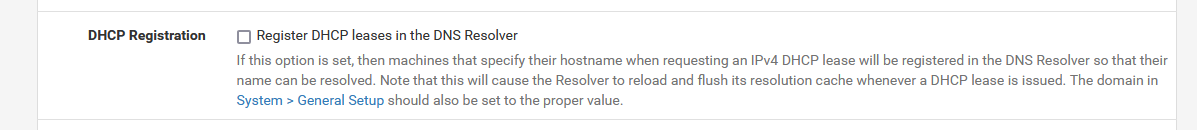
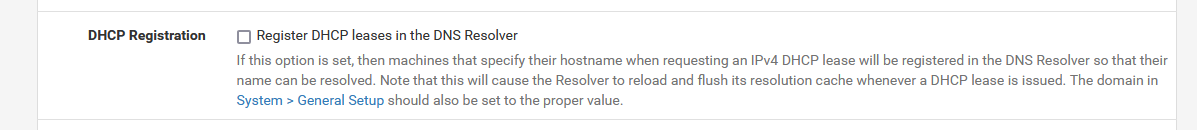
[Edit: Unchecking Register DHCP leases in the DNS Resolver appears to have resolved it for me. Leaving the static mappings checked seems to be fine so far though, I'll report back later otherwise.]
-
+1 i have the same issue now since a couple of days without changing anything! Running on 2.4.2-DEVELOPMENT because i need the PPPOE Vlan Tag functionality which is not working with the latest stable.
Nov 15 14:32:17 unbound 58529:0 info: start of service (unbound 1.6.6). Nov 15 14:32:17 unbound 58529:0 notice: init module 1: iterator Nov 15 14:32:17 unbound 58529:0 notice: init module 0: validator Nov 15 14:32:17 unbound 58529:0 notice: Restart of unbound 1.6.6. Nov 15 14:32:17 unbound 58529:0 info: server stats for thread 1: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:17 unbound 58529:0 info: server stats for thread 1: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:17 unbound 58529:0 info: server stats for thread 0: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:17 unbound 58529:0 info: server stats for thread 0: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:17 unbound 58529:0 info: service stopped (unbound 1.6.6). Nov 15 14:32:17 unbound 58529:0 info: start of service (unbound 1.6.6). Nov 15 14:32:17 unbound 58529:0 notice: init module 1: iterator Nov 15 14:32:17 unbound 58529:0 notice: init module 0: validator Nov 15 14:32:14 unbound 15323:0 info: 0.065536 0.131072 3 Nov 15 14:32:14 unbound 15323:0 info: 0.016384 0.032768 1 Nov 15 14:32:14 unbound 15323:0 info: lower(secs) upper(secs) recursions Nov 15 14:32:14 unbound 15323:0 info: [25%]=0.032768 median[50%]=0.0873813 [75%]=0.109227 Nov 15 14:32:14 unbound 15323:0 info: histogram of recursion processing times Nov 15 14:32:14 unbound 15323:0 info: average recursion processing time 0.067271 sec Nov 15 14:32:14 unbound 15323:0 info: server stats for thread 1: requestlist max 1 avg 0.25 exceeded 0 jostled 0 Nov 15 14:32:14 unbound 15323:0 info: server stats for thread 1: 4 queries, 0 answers from cache, 4 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:14 unbound 15323:0 info: 0.065536 0.131072 1 Nov 15 14:32:14 unbound 15323:0 info: lower(secs) upper(secs) recursions Nov 15 14:32:14 unbound 15323:0 info: [25%]=0 median[50%]=0 [75%]=0 Nov 15 14:32:14 unbound 15323:0 info: histogram of recursion processing times Nov 15 14:32:14 unbound 15323:0 info: average recursion processing time 0.081054 sec Nov 15 14:32:14 unbound 15323:0 info: server stats for thread 0: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:14 unbound 15323:0 info: server stats for thread 0: 1 queries, 0 answers from cache, 1 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:14 unbound 15323:0 info: service stopped (unbound 1.6.6). Nov 15 14:32:11 unbound 15323:0 info: start of service (unbound 1.6.6). Nov 15 14:32:11 unbound 15323:0 notice: init module 1: iterator Nov 15 14:32:11 unbound 15323:0 notice: init module 0: validator Nov 15 14:32:11 unbound 15323:0 notice: Restart of unbound 1.6.6. Nov 15 14:32:11 unbound 15323:0 info: server stats for thread 1: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:11 unbound 15323:0 info: server stats for thread 1: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:11 unbound 15323:0 info: server stats for thread 0: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:11 unbound 15323:0 info: server stats for thread 0: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:11 unbound 15323:0 info: service stopped (unbound 1.6.6). Nov 15 14:32:11 unbound 15323:0 info: start of service (unbound 1.6.6). Nov 15 14:32:11 unbound 15323:0 notice: init module 1: iterator Nov 15 14:32:11 unbound 15323:0 notice: init module 0: validator Nov 15 14:32:08 unbound 83784:0 info: 0.131072 0.262144 1 Nov 15 14:32:08 unbound 83784:0 info: 0.065536 0.131072 1 Nov 15 14:32:08 unbound 83784:0 info: 0.016384 0.032768 2 Nov 15 14:32:08 unbound 83784:0 info: 0.001024 0.002048 1 Nov 15 14:32:08 unbound 83784:0 info: lower(secs) upper(secs) recursions Nov 15 14:32:08 unbound 83784:0 info: [25%]=0.018432 median[50%]=0.028672 [75%]=0.114688 Nov 15 14:32:08 unbound 83784:0 info: histogram of recursion processing times Nov 15 14:32:08 unbound 83784:0 info: average recursion processing time 0.062189 sec Nov 15 14:32:08 unbound 83784:0 info: server stats for thread 1: requestlist max 2 avg 0.666667 exceeded 0 jostled 0 Nov 15 14:32:08 unbound 83784:0 info: server stats for thread 1: 6 queries, 0 answers from cache, 6 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:08 unbound 83784:0 info: 1.000000 2.000000 1 Nov 15 14:32:08 unbound 83784:0 info: 0.524288 1.000000 1 Nov 15 14:32:08 unbound 83784:0 info: 0.131072 0.262144 1 Nov 15 14:32:08 unbound 83784:0 info: 0.008192 0.016384 1 Nov 15 14:32:08 unbound 83784:0 info: lower(secs) upper(secs) recursions Nov 15 14:32:08 unbound 83784:0 info: [25%]=0.016384 median[50%]=0.262144 [75%]=1 Nov 15 14:32:08 unbound 83784:0 info: histogram of recursion processing times Nov 15 14:32:08 unbound 83784:0 info: average recursion processing time 0.753388 sec Nov 15 14:32:08 unbound 83784:0 info: server stats for thread 0: requestlist max 3 avg 1.25 exceeded 0 jostled 0 Nov 15 14:32:08 unbound 83784:0 info: server stats for thread 0: 5 queries, 1 answers from cache, 4 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:08 unbound 83784:0 info: service stopped (unbound 1.6.6). Nov 15 14:32:05 unbound 83784:0 info: start of service (unbound 1.6.6). Nov 15 14:32:05 unbound 83784:0 notice: init module 1: iterator Nov 15 14:32:05 unbound 83784:0 notice: init module 0: validator Nov 15 14:32:05 unbound 83784:0 notice: Restart of unbound 1.6.6. Nov 15 14:32:05 unbound 83784:0 info: server stats for thread 1: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:05 unbound 83784:0 info: server stats for thread 1: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:05 unbound 83784:0 info: server stats for thread 0: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:05 unbound 83784:0 info: server stats for thread 0: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:05 unbound 83784:0 info: service stopped (unbound 1.6.6). Nov 15 14:32:05 unbound 83784:0 info: start of service (unbound 1.6.6). Nov 15 14:32:05 unbound 83784:0 notice: init module 1: iterator Nov 15 14:32:05 unbound 83784:0 notice: init module 0: validator Nov 15 14:32:02 unbound 39724:0 info: 0.008192 0.016384 1 Nov 15 14:32:02 unbound 39724:0 info: lower(secs) upper(secs) recursions Nov 15 14:32:02 unbound 39724:0 info: [25%]=0 median[50%]=0 [75%]=0 Nov 15 14:32:02 unbound 39724:0 info: histogram of recursion processing times Nov 15 14:32:02 unbound 39724:0 info: average recursion processing time 0.011720 sec Nov 15 14:32:02 unbound 39724:0 info: server stats for thread 1: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:02 unbound 39724:0 info: server stats for thread 1: 4 queries, 2 answers from cache, 2 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:02 unbound 39724:0 info: 0.131072 0.262144 1 Nov 15 14:32:02 unbound 39724:0 info: lower(secs) upper(secs) recursions Nov 15 14:32:02 unbound 39724:0 info: [25%]=0 median[50%]=0 [75%]=0 Nov 15 14:32:02 unbound 39724:0 info: histogram of recursion processing times Nov 15 14:32:02 unbound 39724:0 info: average recursion processing time 0.152199 sec Nov 15 14:32:02 unbound 39724:0 info: server stats for thread 0: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:32:02 unbound 39724:0 info: server stats for thread 0: 2 queries, 0 answers from cache, 2 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:32:02 unbound 39724:0 info: service stopped (unbound 1.6.6). Nov 15 14:31:59 unbound 39724:0 info: failed to prime trust anchor -- DNSKEY rrset is not secure . DNSKEY IN Nov 15 14:31:59 unbound 39724:0 info: start of service (unbound 1.6.6). Nov 15 14:31:59 unbound 39724:0 notice: init module 1: iterator Nov 15 14:31:59 unbound 39724:0 notice: init module 0: validator Nov 15 14:31:59 unbound 39724:0 notice: Restart of unbound 1.6.6. Nov 15 14:31:59 unbound 39724:0 info: server stats for thread 1: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:31:59 unbound 39724:0 info: server stats for thread 1: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:31:59 unbound 39724:0 info: server stats for thread 0: requestlist max 0 avg 0 exceeded 0 jostled 0 Nov 15 14:31:59 unbound 39724:0 info: server stats for thread 0: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting Nov 15 14:31:59 unbound 39724:0 info: service stopped (unbound 1.6.6). Nov 15 14:31:59 unbound 39724:0 info: start of service (unbound 1.6.6). Nov 15 14:31:59 unbound 39724:0 notice: init module 1: iterator -
Similar issue on 2.4.1. already posted in pfblocker forum as i thought the error occurres from that side.
Nov 14 23:03:28 unbound 45240:0 info: start of service (unbound 1.6.6). Nov 14 23:02:57 unbound 45240:0 info: service stopped (unbound 1.6.6). Nov 14 23:02:57 unbound 45240:0 info: start of service (unbound 1.6.6). Nov 14 23:02:25 unbound 45240:0 info: service stopped (unbound 1.6.6). Nov 14 23:00:08 filterdns adding entry 2a02:26f0:6a:280::3d5 to pf table certbot for host acme-v01.api.letsencrypt.org Nov 14 23:00:08 filterdns adding entry 2a02:26f0:6a:293::3d5 to pf table certbot for host acme-v01.api.letsencrypt.org Nov 14 23:00:08 filterdns adding entry 104.74.107.171 to pf table certbot for host acme-v01.api.letsencrypt.org -
are there any further investigations?
do you need more information/ logs? -
Similar issue on 2.4.1. already posted in pfblocker forum as i thought the error occurres from that side.
Nov 14 23:03:28 unbound 45240:0 info: start of service (unbound 1.6.6). Nov 14 23:02:57 unbound 45240:0 info: service stopped (unbound 1.6.6). Nov 14 23:02:57 unbound 45240:0 info: start of service (unbound 1.6.6). Nov 14 23:02:25 unbound 45240:0 info: service stopped (unbound 1.6.6). Nov 14 23:00:08 filterdns adding entry 2a02:26f0:6a:280::3d5 to pf table certbot for host acme-v01.api.letsencrypt.org Nov 14 23:00:08 filterdns adding entry 2a02:26f0:6a:293::3d5 to pf table certbot for host acme-v01.api.letsencrypt.org Nov 14 23:00:08 filterdns adding entry 104.74.107.171 to pf table certbot for host acme-v01.api.letsencrypt.orgExact same issue here. Im on version 2.4.2.
It is solved when disabling DHCP registrations in DNS.
-
Please help! PfSense makes my internet unusable :(
Nov 18 10:58:23 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:57:51 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:47:31 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:47:00 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:47:00 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:46:28 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:41:26 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:40:55 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:31:13 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:30:42 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:27:40 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:27:08 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:12:35 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:12:04 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:10:21 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:09:49 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:09:08 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:08:37 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:02:36 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:02:05 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 10:02:05 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 10:01:33 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:47:30 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:46:59 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:46:59 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:46:27 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:31:13 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:30:42 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:30:03 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:29:32 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:16:18 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:15:47 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:14:59 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:14:27 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:12:44 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:12:12 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:11:02 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:10:30 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:02:33 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:02:02 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 09:02:02 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 09:01:30 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:47:29 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:46:58 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:46:58 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:46:26 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:31:13 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:30:42 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:24:07 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:23:36 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:20:02 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:19:31 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:19:26 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:18:55 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:17:22 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:16:51 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:15:07 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:14:36 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:02:30 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:01:59 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 08:01:59 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 08:01:27 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:47:28 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:46:57 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:46:57 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:46:25 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:34:07 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:33:36 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:31:13 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:30:42 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:25:38 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:25:07 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:21:50 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:21:19 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:19:46 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:19:14 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:17:31 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:16:59 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:02:27 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:01:56 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 07:01:56 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 07:01:25 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:55:00 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:54:28 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:46:56 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:46:24 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:43:53 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:43:22 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:43:22 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:42:51 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:31:13 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:30:41 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:24:14 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:23:42 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:22:09 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:21:37 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:19:54 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:19:23 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:02:24 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:01:53 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 06:01:53 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 06:01:22 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:47:26 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:46:55 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:46:55 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:46:23 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:43:33 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:43:02 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:41:43 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:41:11 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:31:44 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:31:12 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:31:12 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:30:41 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:26:36 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:26:04 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:24:32 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:24:01 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:22:18 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:21:46 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:02:21 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:01:50 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 05:01:50 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 05:01:19 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 04:46:54 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 04:46:22 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 04:44:23 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 04:43:52 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 04:31:12 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 04:30:41 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 04:29:30 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 04:28:59 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 04:28:59 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 04:28:28 unbound 41920:0 info: service stopped (unbound 1.6.6). Nov 18 04:26:56 unbound 41920:0 info: start of service (unbound 1.6.6). Nov 18 04:26:24 unbound 41920:0 info: service stopped (unbound 1.6.6). -
At the risk of necroposting, here is a related bug for unbound [1] and related merge request [2].
[1] https://redmine.pfsense.org/issues/5413
[2] https://github.com/pfsense/FreeBSD-ports/pull/751 -
This issue is causing issues on my fairly new deployment. I'd call it a deal-breaker had I found it sooner.
Does anyone have any insight as to whether it will be fixed or not?
s
-
Fixed :
!
-
@gertjan said in Unbound seems to be restarting frequently:
Fixed :
!
How is that fixed? It is still HUPping the resolver, and flushing the cache.
s
-
@swixo said in Unbound seems to be restarting frequently:
@gertjan said in Unbound seems to be restarting frequently:
Fixed :
!
How is that fixed? It is still HUPping the resolver, and flushing the cache.
s
Usually, it is the renewal of DHCP leases which results in the DHCP service restarting
unbound(the DNS resolver, or forwarder, if using forwarding mode) so that it will reload its database of hostname/IP pairs. Unchecking that box prevents DHCP from registering the hosts' new leases with DNS. That, in turn, meansunbounddoes not get restarted frequently.,Another source of frequent
unboundrestarts is using the pfBlockerNG-devel package and its DNSBL feature. This is especially true with the new Python module integration. This setup can give the same symptoms as the DHCP leases scenario described above.I will not disagree that there are better ways to fix this -- namely patching the DHCP system so that it uses the
unboundcontrol app to selectively load domains instead of flushing the entire cache and starting over with everything as it does now. But unless and until the pfSense developer team makes a change, the only two known solutions are to turn off the "Register DHCP leases in the DNS Resolver" option, and/or stop using the features of pfBlockerNG-devel that fiddle withunboundand frequently restart it.
