Wondering how to port forward to my Name Server and other locations after leaving Airport Extreme behind.
-
I wouldn't host public dns to the public if I had a 10ge pipe.. So your domain only has 1 NS? That is borked right there and to be honest any registrar normally wouldn't even let you do that.. 2 NS is a min..
if you want to host your web site off your link, sure have at it. But there is zero reason to be hosted there as well. If you want to play and learn about dns - great.. Do it off site, do t for your local domains..
Just no reason to host public dns on your connection. HE will give you free dns for like 50 domains, dnsmadeasy will for like $30 year you can do 10 domains with like 10million queries on an anycast network.. ts not going to go down.
You have a power outage and your offline.. You have to reboot your router and your offline, etc.
Again going to ask what is in front of pfsense when you plug it in? If pfsense gets as rfc1918 address on its wan.. Then the nat device in front of pfsense has to forward to pfsense wan IP anything you would want to forward.
There are a bajillion hosting sites or where you can get your own vps and do whatever it is you want. The onl;y thing that should be hosted out of your house is maybe your plex server to your friends and family. And they better be ok with it going offline any time you want to play with something, etc..
-
Your opinion of the methodologies is understood, but it's not what I'm asking about. How I should or shouldn't do something is completely up to subjective opinion. I'm neither hosting for myself nor anyone else for any reason other than to learn how it works, so it doesn't matter how many NS's I have, or connections, or etc. I'm focusing on function at this point.
When I plug in pfSense, on one side (WAN) there's a cable modem, on the other side (LAN), there's a small ethernet switch. The WAN is static (issued by the isp) and thus, statically set in pfSense. At the end of the power cord is a wall with 110v power. I wish I could say that between me and the wall are superpowers that yield extraordinary lighting effects, but I cannot.
Not much more than that.
All I want to do is correctly configure pfSense so my name server can be found and so port 80 and 443 forward to apache properly instead of being served by pfSense.
-
So if you get a public IP on pfsense wan, then its as simple as clickity clickity port forward.. It really is that simple.
Go through the troubleshooting guide I linked to already if your having problems. The first thing to check is that traffic actually hits pfsense wan.
If it takes you more than a min to troubleshoot a port forwarding problem - then you do not understand the basics. Please walk through the troubleshooting guide and point out anything you have questions on how to do or where its failing.
here is how to port forward in pfsense
https://www.netgate.com/docs/pfsense/nat/forwarding-ports-with-pfsense.htmlIf your having problems look to the troubleshooting guide I linked to above.
Since your static on your public IP.. Send me a chat/pm with your domain and I will look to what it lists as the NS and can validate that your putting that on pfsense wan, etc. etc.
-
I think the root of the problem would be one of the following:
pfSense is already setup to resolve DNS
pfSense is already hijacking port 80 and 443 for access to pfSense remotely.I was able to port forward other ports, for example, but these 3 (53 / 80 / 443) stumped me...but, as was mentioned above, it may be because I also didn't forward UDP.
I'll give that a shot and see if I can't work this out. I managed to fire up a LAMP server and configure all of that crap correctly, so I should be able to figure this out.
My previous tech life was riddled with Microsoft products and their ungodly vocabulary.
-
@arretx said in Wondering how to port forward to my Name Server and other locations after leaving Airport Extreme behind.:
configure all of that crap correctly, so I should be able to figure this out.
Ok ;) hehehe following a bouncing ball guide for a LAMP server is a bit different then troubleshooting network/firewall issues. But I have faith in you!
Pfsense is not hijacking anything.. What ports do you think it should default to for its web admin interface? And yes it runs resolver by default on yes 53 which is the port DNS works on..
Not sure where your getting the idea that if pfsense is using the ports that you can not forward them through pfsense? You could have issues with nat reflection ok... But just because pfsense listens on 80, doesn't mean you can not forward 80 on a port forward. How exactly are you checking that these ports your forwarding are working? A common misconception is that you can check that they are forwarded from inside pfsense. Just by hitting the wan IP of pfsense from lan side hoping to be forwarded back in (nat reflection) to some other box on your lan - that is not valid way to test port forwards.
Here - all of 30 seconds to forward dns through pfsense. And yeah pfsense is running unbound on 53.. I fired up a 2k12r2 windows box.. Enabled dns server on it - which I had done for a previous thread asking about dns overrides and then from the outside did a query direct to my pfsense public IP, here you go bing bang zoom.
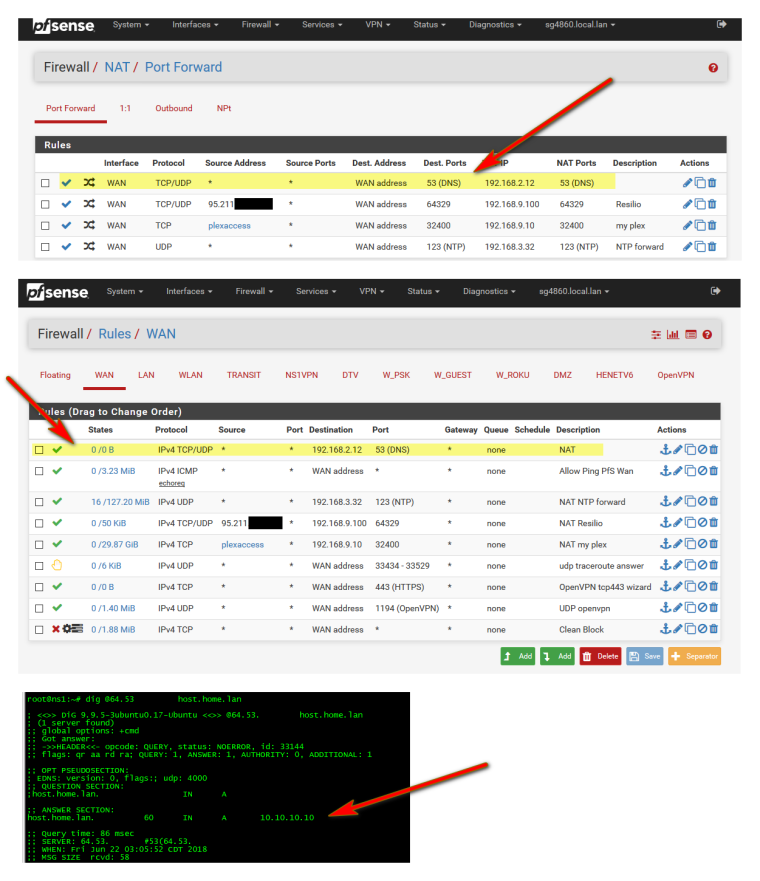
So again - be more than happy to help you troubleshoot your problem.. Can do the same thing with 80 and 443 even if pfsense is using them for its gui.. Maybe you were testing them from your lan and that is why they are not working since you didn't setup nat reflection? Maybe your trying to hit them via fqdn, and since your dns is not working they are not resolving for your nat reflection or from public?
-
Haha...touche. You're right. It's only hijacking it because it's doing something I wasn't expecting and alas, I shall stomp my feet around and protest in agony. Makes perfect sense that it would be assigned to 80 and 443. Lol.
Regarding testing, I would either use something like pingdom or just disconnect my mobile device from the lan and use my data connection.
It's also highly likely that I didn't set the Firewall / Rules / WAN setting and only did Port Forwarding..


I'll check back in when I get it rolling correctly.
-
I would personally set up something like hurricane's free DNS as a slave to pull the zones from your local server and only list them as NS records. That way you:
- Increase reliability at least a thousand-fold.
- Don't have to list your local IP address in an NS record.
-
Exactly you could do a hidden master setup.
Which would be way up the curve when learning dns.. And would be WAY better than actually letting the public internet query to your home connection. An that being the only NS for your domain(s)..
Hosting anything out of your house is really never going to make sense from cost perspective or maint/uptime point of view. Unless your talking your own personal access to stuff in your home. Or like your media library to your friends an family where it just doesn't make sense to pay for storage of the TB of media files elsewhere. But then again their are many plex servers in the cloud that are very cost effective and if you have a lot of friends and family ;)
You can host dns for FREE on actual system that doesn't ever go down and is anycast and both ipv4 and ipv6.. Why would you be worried about hosting it. Providing its connectivity is not learning anything about dns..
Here is what I am going to say, with years of running dns.. If your hosting it yourself and its not just your local dns - your doing it wrong! ;)
Sure run bind, play with all its features local.. This has zero to do with providing the public with the name services to resolve your services. Host that with someone that does that sort of thing..
You can run bind off pfsense - the gui makes it easy to play with to get the basics stuff down. I WOULD NOT SUGGEST that be your public NS for your domain(s).. Unbound is a great little resolver - can do some neat stuff with it.. Its not designed to be a authoritative ns.
-
@derelict said:
Don’t have to list your local IP address in an NS record.
What's problematic about that if it's a fixed IP?
-
Because people are sensitive to things like that especially at home.
It is also likely to be a bit tranistory even if static.
But the real issue is reliability.
A DNS provider is going to be many, many times more reliable than some residential connection.
-
OK, so it's no technical issue, more a personal one.
Thanks for the clarification. -
Ok the hiding the IP might be personal. But the real reason you might hide your SOA (hidden master dns) is so it doesn't get queried.. So you have your NS local and you can control. On a slow link, etc. But your NSers that everyone uses is out on real connections UP 24x7 and hopefully geographically diverse.
You can also do a hidden secondary, or slave - where the NS at your location is not in the delegation so doesn't get queried but will maintain a copy of your zone that you can use if the other NSers are down, etc. Or that you can query locally, etc.