Simple VLAN for PFSense + Unifi AP-AC-LR
-
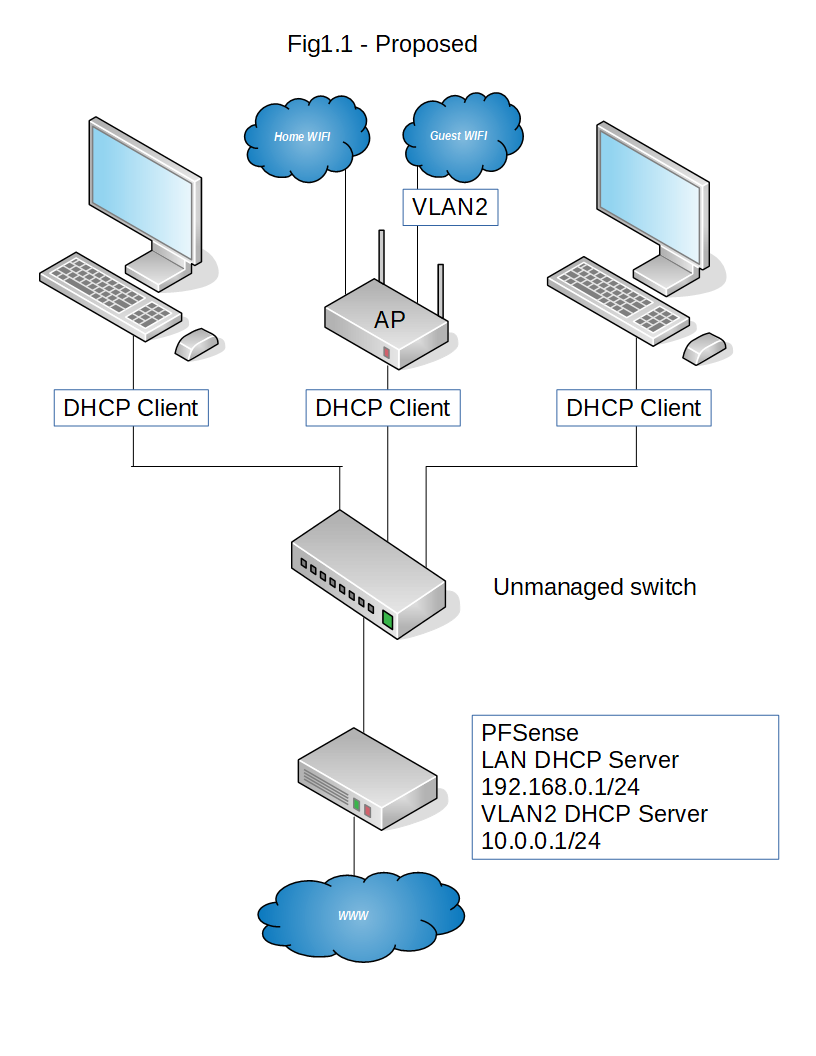
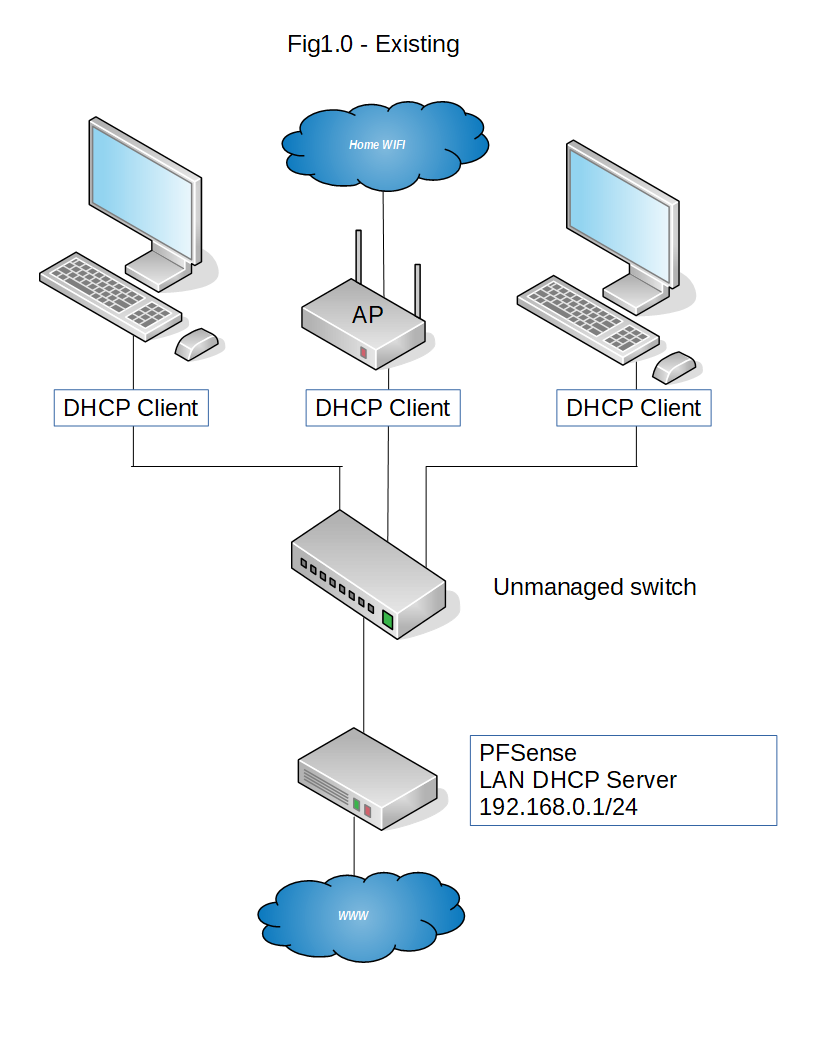
If the AP connects to the first switch ( switch-1 in my example ) this only needs to support VLANS.
If your second switch only hosts 192.168.0.0/24 devices you can connect any dumb switch to the switch that supports VLANs, the port on switch-1 to switch-2 would just need to be an untagged port and you could only carry the single subnet to the second switch.
-
@bbcmodelb said in Simple VLAN for PFSense + Unifi AP-AC-LR:
OK, so unlike my simplified diagram, I've actually got 2x switches between the pfsense and the Unfi AP - do they BOTH need to be managed in this scenario?
Should you use managed switches, they'd have to be configured with trunk ports facing both pfSense and the AP, with all other ports configured as access ports. If you have more than one switch, you have to do the same for every switch that's between pfSense and the AP. Also, if you have multiple switches, you want to avoid loops, unless you're sure the switches support spanning tree or equivalent. All managed switches should, but some unmanaged switches don't.
-
Ah, that's at least worth a try.
Newbie alert - so, a non VLAN device, say a wired PC on the LAN requests an IP address from the PFSense box - what governs whether the PFSense gives it a LAN based IP (192.168.0.x) or VLAN based IP (10.0.0.x) ?
-
Got it
-
@bbcmodelb said in Simple VLAN for PFSense + Unifi AP-AC-LR:
Ah, that's at least worth a try.
Newbie alert - so, a non VLAN device, say a wired PC on the LAN requests an IP address from the PFSense box - what governs whether the PFSense gives it a LAN based IP (192.168.0.x) or VLAN based IP (10.0.0.x) ?
You probably want to read up on VLANs. However, the difference between VLAN frames and regular frames is the VLAN tag. This tag is a 4 byte value that's inserted into the Ethernet frame where the Ethertype/length field normally is, with the original Ethertype/length frame immediately following. So, the only difference between VLAN and regular frames is the content of the 2 bytes following the source MAC address and the additional 4 bytes in length. It's also possible to have 2 levels of VLAN, but you wouldn't see that outside of carrier networks. The network adapter in the device is configured for whatever VLANs are desired.
-
BTW you can have up to 8 SSIDs on the AP, not that I'd advise having that many.
-
@jknott said in Simple VLAN for PFSense + Unifi AP-AC-LR:
@bbcmodelb said in Simple VLAN for PFSense + Unifi AP-AC-LR:
Ah, that's at least worth a try.
Newbie alert - so, a non VLAN device, say a wired PC on the LAN requests an IP address from the PFSense box - what governs whether the PFSense gives it a LAN based IP (192.168.0.x) or VLAN based IP (10.0.0.x) ?
You probably want to read up on VLANs. However, the difference between VLAN frames and regular frames is the VLAN tag. This tag is a 4 byte value that's inserted into the Ethernet frame where the Ethertype/length field normally is, with the original Ethertype/length frame immediately following. So, the only difference between VLAN and regular frames is the content of the 2 bytes following the source MAC address and the additional 4 bytes in length. It's also possible to have 2 levels of VLAN, but you wouldn't see that outside of carrier networks.
Ah, the PFSense is evaluating each packet and determining whether it has this tag or not. If it has the tag, it chooses the appropriate interface to pass the packets to. I'll go and read that link, thanks.
-
@bbcmodelb said in Simple VLAN for PFSense + Unifi AP-AC-LR:
Ah, the PFSense is evaluating each packet and determining whether it has this tag or not. If it has the tag, it chooses the appropriate interface to pass the packets to. I’ll go and read that link, thanks.
Not so much pfSense as the network adapter and operating system. VLANs work at layer 2 and pfSense at layer 3. PfSense simply sees another interface to work with.
-
Got it, so prior to creating the VLAN on the PFSense box, PFSense would discard any packets it received with a VLAN tag, in this case from the AP guest SSID?
-
What are the DHCP clients on your home LAN.
Some devices support VLANs, my Mac I can create an untagged and tagged interface.
Maybe have a play about.
-
@bbcmodelb said in Simple VLAN for PFSense + Unifi AP-AC-LR:
Got it, so prior to creating the VLAN on the PFSense box, PFSense would discard any packets it received with a VLAN tag, in this case from the AP guest SSID?
Not quite. When the computer running pfSense receives a VLAN frame, that frame is directed to the VLAN interface and the VLAN tag is stripped off. Going the other way, a frame sent out through the VLAN interface has the tag added, before being sent out the port. The VLAN tags are used to create virtual networks that logically appear to be separate, as though they were physically separate.
-
@nogbadthebad said in Simple VLAN for PFSense + Unifi AP-AC-LR:
Some devices support VLANs, my Mac I can create an untagged and tagged interface.
My desktop system, running Linux, supports VLANs, but my notebook, running the same version of Linux, does not. I doubt devices such as tablets or smart phones support VLANs.
-
@jknott said in Simple VLAN for PFSense + Unifi AP-AC-LR:
Not quite. When the computer running pfSense receives a VLAN frame, that frame is directed to the VLAN interface and the VLAN tag is stripped off.
What if the computer running pfSense hasn't yet got the VLAN interface created? Will it ignore the packet?
-
@jknott That's interesting - I'm going to go take a look at my network adapter's available settings! Thanks!
-
@bbcmodelb said in Simple VLAN for PFSense + Unifi AP-AC-LR:
What if the computer running pfSense hasn’t yet got the VLAN interface created? Will it ignore the packet?
Yes, it will ignore any VLAN frame that it's not configured for. For example, if you enable VLAN 10, frames for VLAN 11, 20, 3000 etc., will be ignored. Also, one feature of switches is they forward frames based on MAC addresses. If a device hasn't had traffic through a port, traffic for that device will not go through that. However, somethings, such as broadcasts will be sent to all ports or frames for a device that has yet to be learned about by the switch. Bottom line, devices are unlikely to see many VLAN frames that's they're not configured for.
-
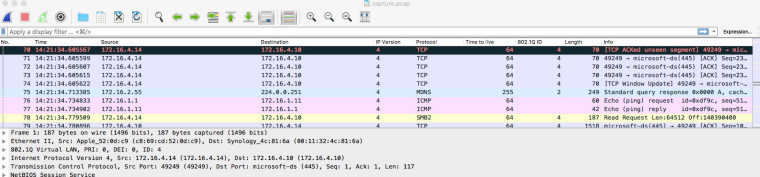
In your case the AP will be doing the tagging of the packets coming from the guest Wi-Fi.
If you do a packet capture using tcdpump on eth0 you'll see tagged and untagged packets.
ssh admin@ap-1 'tcpdump -i eth0 src not 172.16.2.20 and dst not 172.16.2.20 -w -' > ~/capture.pcap
Where 172.16.2.20 is the device i'm sshing from.
-
Ah, thats interesting, so I can actually view the tagged / untagged traffic - thanks for the info
-
Yes you need to find a packet with a vlan id in and add it as a column or create a new column and set it as follows:-

-
@bbcmodelb said in Simple VLAN for PFSense + Unifi AP-AC-LR:
Ah, thats interesting, so I can actually view the tagged / untagged traffic - thanks for the info
Yep, Wireshark is a very useful tool for understanding network issues. For example, by looking at that capture, you can see it's an Ethernet II (also known as DIX) frame, which is 1 of 2 types, the other being IEEE 802.3. The only significant difference between them is the Ethertype/length field I mentioned. If it's 1500 or less, it's the size of the data carried by the frame. If 1536 or more, it's Ethertype, which describes the payload type. In this example, a VLAN frame. When you have Wireshark running, you can expand the fields to see the actual contents. If 802.3 length, then it imposes a hard limit of 1500 bytes, which many incorrectly assume to be the maximum IP MTU. However, IP uses Ethernet II, which has no length limit and, in fact, up to 65K MTU is supported, provided layer 2 supports it. Way back in the dark ages, the hardware limited the frame size to 1518 bytes, which meant there wasn't room for both a VLAN tag and full 1500 byte MTU. However, that limit was removed 20 years ago with frame expansion, so no modern hardware should have a problem with VLAN tags.
BTW, pfSense includes "Packet Capture", which can be used to capture frames. However, it doesn't display as much as Wireshark, so you may want to capture with Packet Capture and then download the capture to view with Wireshark.
-
Hmmm, I've implemented a solution using unmanaged switches, and connected my smartphone to the new GUEST wifi, where the pfsense box IS giving it the correct IP address 10.0.0.x, but when I try to access a website, nothings appearing almost as if its a firewall / nat issue?
pfSense box config
interfaces > interfaces assignments > vlans > add >
tag, 2
parent interface, em3 (lan)
priority, 0interfaces > interfaces assignements > add >
description, GUEST
ipv4 config, static
ipv4 addr, 10.0.0.1
upstream gateway, nonefirewall > nat > outbound > add
10.0.0.0 / 24
src * dest *
Nat address, Wan Addressfirewall > rules > add
source, GUEST address
dest *
gateway WAN_DHCP
passservices > DHCP server > GUEST
scope 10.0.0.10 - 10.0.0.254Anything I've missed?