Configuration of NAT Reflection to access external domain not working
-
With NAT reflection traffic goes through pfSense, but it needs to go to the WAN IP since that is what is being NATted. If you're sending traffic to the LAN IP of pfSense NAT won't happen there if the NAT rule is on the WAN.
-
It actually doesn't go through the firewall to WAN and back. It is redirected on the interface the connection is established into.
You will probably need to post screenshots.
-
By "through pfSense" I meant a NAT connection touches pfSense. Split DNS would be when the hostname resolves to an internal IP and the connection goes direct to the LAN IP of the server and doesn't touch pfSense. Split DNS should not be necessary if NAT reflection is set up correctly...?
-
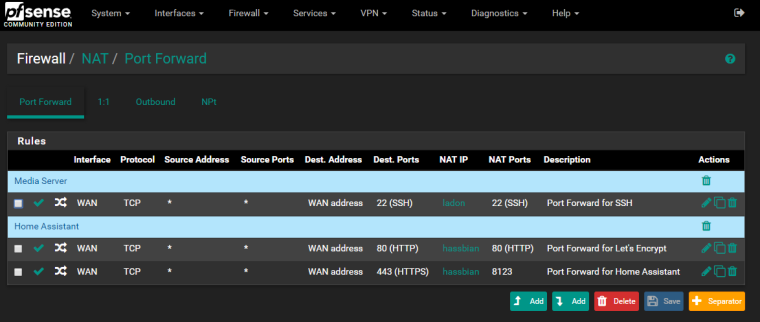
@derelict What pages would you like to see? Port Forwards, Firewall Rules, Advanced System Settings? Something else?
-
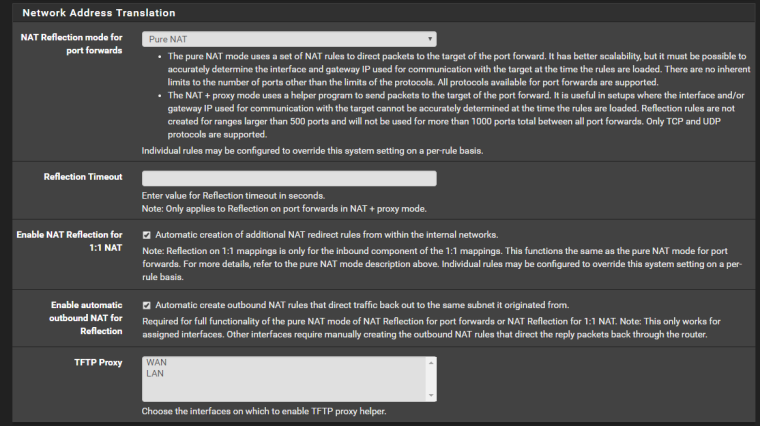
Port forwards and NAT reflection settings probably.
-
-
Did you get the webgui off of 80/443?
-
Yep. It's on 8443 now.
-
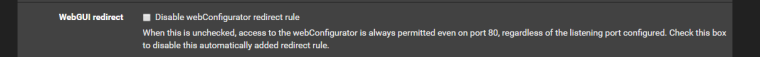
And the WebGUI http to https redirect is disabled? Port forwards coming into WAN override that but not for NAT-reflected connections.
Split DNS is a more elegant solution to this problem.
-
+1 split DNS
-
@derelict said in Configuration of NAT Reflection to access external domain not working:
And the WebGUI http to https redirect is disabled? Port forwards coming into WAN override that but not for NAT-reflected connections.
Split DNS is a more elegant solution to this problem.
If this is what you're talking about, then no. I can change it. Let me know. I don't know that it'll have an impact since I'm only listening on 80 when I'm attempting to renew Let's Encrypt certs.
Did you see my second post about my Split DNS configuration? TTS for Google Home doesn't work when it is configured that way.