I need HELP on DNS RESOLVER!
-
@johnpoz said in I need HELP on DNS RESOLVER!:
a VPN to c
I have couple trying bucks on gcloud I gonna try it on here. Which vpn type am I need to set?
And In turkish netgate forum I was ask some peoples and they were already try to passthrough with TLS but we can resolve thats hostnames but we cannot do more, ISP isnt allowing handshakes.
-
Handshakes to what? So your being blocked from talking to 1.1.1.1 on port 843??
You need a vpn box - doesn't matter what type, ipsec, openvpn, L2tp past your blocks if you want to be able to query for dns through that vpn.
-
This post is deleted! -
@gertjan said in I need HELP on DNS RESOLVER!:
https://serverfault.com/questions/404840/when-do-dns-queries-use-tcp-instead-of-udp
There are DNS over TLS providers other than CloudFlare and Quad9. Some of them even offer service on port 443, which might be useful if the blocking you are seeing is targeted specifically at DNS and DNS over TLS. You might want to test some of these to see if you can get around the block without resorting to a VPN.
https://dnsprivacy.org/wiki/display/DP/DNS+Privacy+Test+Servers
-
-
No you need something on the other end of the vpn to connect too ;) It could be a service sure.. You can not have a vpn without 2 ends to the tunnel..
It is not possible to do DPI inside a tls tunnel without decryption of the tunnel - ie MITM... So if your saying your ISP/Gov is doing DPI on your traffic inside a tls tunnel a vpn is not going to help you either ;)
-
Hummm.
Government is decrypting VPN ? Pretty serious then.
I'm pretty sure they can't. The States ..... don't ask ^^
Thy will probably block known VPN end-points ... they are all known.
Or they "discover" initial handshaking when the tunnel is set up, and "drop that. -
Yeah its easy enough to block tls to 1.1.1.1, or block traffic to some known vpn service..
So you just fire up some vps somewhere on the internet, then either run some vpn or dns via tls on that vps box you... Highly unlikely they would block say port 443 to some what amounts to some rando IP on the internet..
-
This post is deleted! -
Try this:
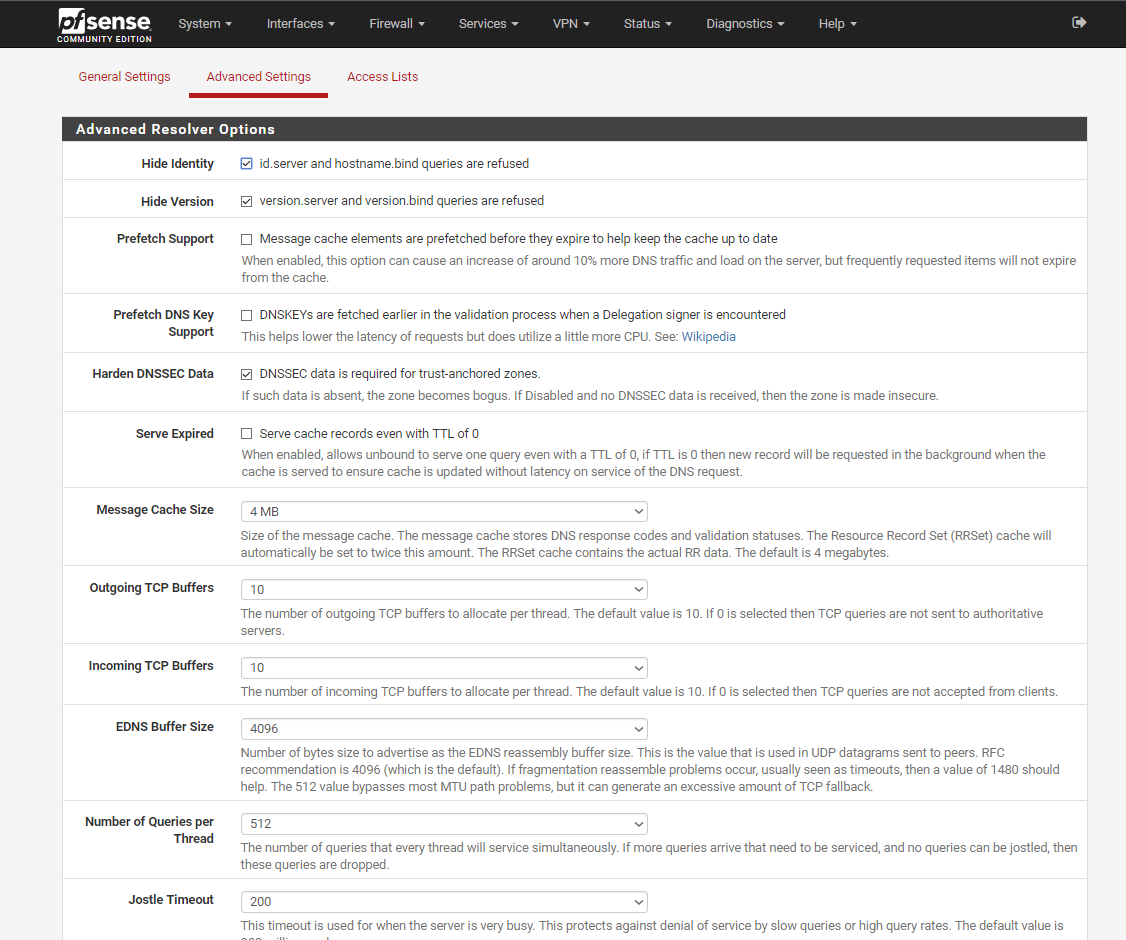
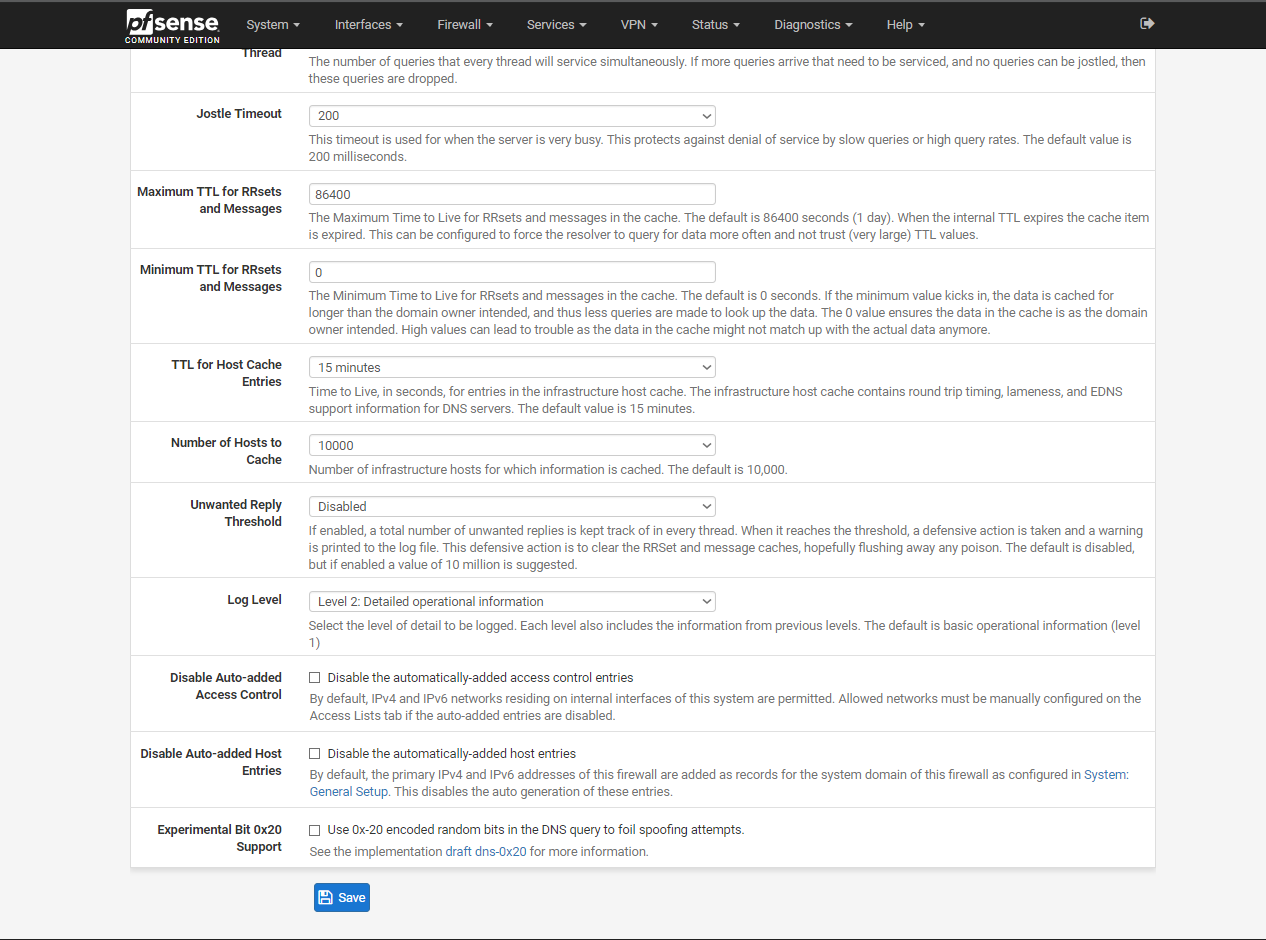
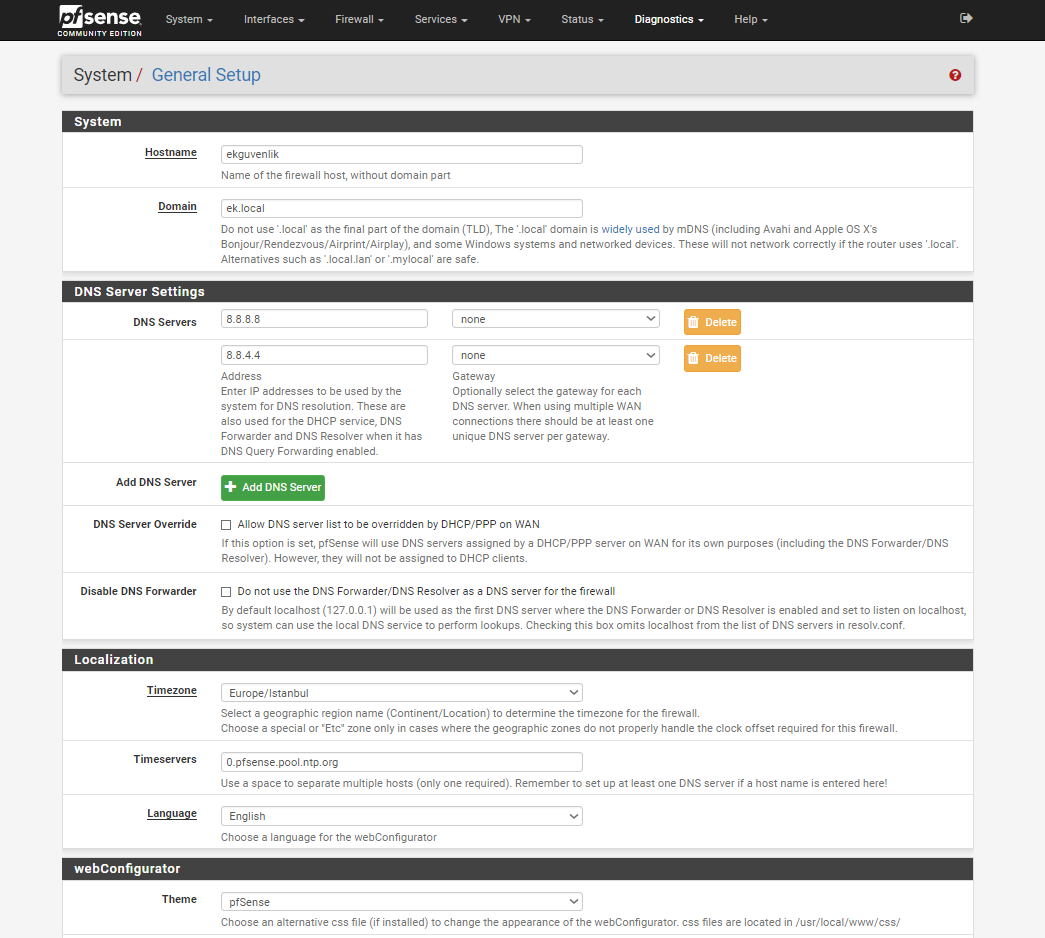
Turn off forwarding mode, and DNS over TLS in unbound, because you are going to configure it manually at the top of the "custom options" box.
Add the following text to the "custom options" box:
### TESTING DNS OVER TLS ON PORT 443 server: tls-cert-bundle: /usr/local/share/certs/ca-root-nss.crt forward-zone: name: "." forward-ssl-upstream: yes ### SERVERS on non-standard ports from: ### https://dnsprivacy.org/wiki/display/DP/DNS+Privacy+Test+Servers ### ^^^ THREE EXAMPLES FOR PORT 443, CHECK LINK FOR MORE ^^^ forward-addr: 145.100.185.15@443#dnsovertls.sinodun.com forward-addr: 145.100.185.16@443#dnsovertls1.sinodun.com forward-addr: 89.234.186.112@443#dns.neutopia.org ### QUAD9 SERVERS #forward-addr: 2620:fe::fe@853#dns.quad9.net #forward-addr: 9.9.9.9@853#dns.quad9.net #forward-addr: 2620:fe::9@853#dns.quad9.net #forward-addr: 149.112.112.112@853#dns.quad9.net ### CLOUDFLARE SERVERS #forward-addr: 2606:4700:4700::1111@853#cloudflare-dns.com #forward-addr: 1.1.1.1@853#cloudflare-dns.com #forward-addr: 2606:4700:4700::1001@853#cloudflare-dns.com #forward-addr: 1.0.0.1@853#cloudflare-dns.comTurn logging up to level 4 on the advanced options page so that you can check that server authentication is taking place. Be sure to turn logging down when you are done. I think that authentication failures may not preclude service, so it is possible that someone could MITM your connection until unbound adds functions to prevent communicating with spoofed servers. At least I recall having read at some point that the functionality isn't there yet.