How to prevent DDOS using Snort?
-
@derelict said in How to prevent DDOS using Snort?:
Attacked how?
Snort can't defend against what is usually called a DDoS (flooding your link with packets from distributed sources) because by the time it arrives it's too late to do anything about it.
do you have any suggestion how i can prevent any attacks sir?
-
If it is a true DDoS there is nothing you can do but go upstream and have them try to block it.
-
this PFBlocker and snort are useless?
-
To a DDoS consisting of traffic overwhelming your interface yes, they are useless.
Look. The traffic is already there. Your "pipe" is already full. Any action taken on your side of the interface cannot change that. All it can do is drop it which is the default behavior of the firewall.
You might get some relief by disabling logging of dropped packets in Status > System Logs, Settings, Log firewall default blocks but that won't do anything to stop the traffic - just might reduce the load on the firewall in processing it.
-
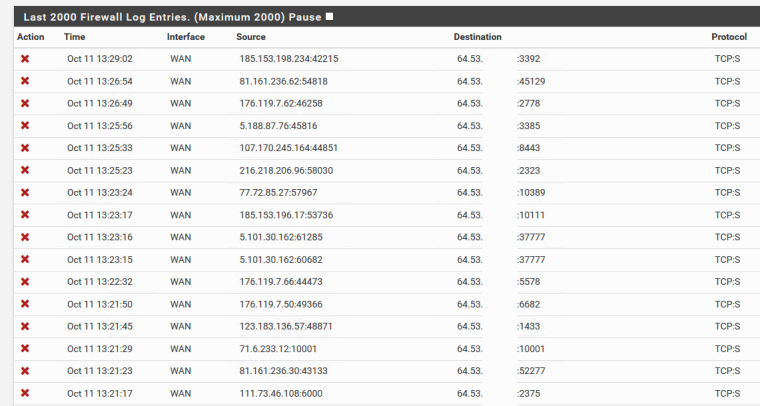
When you say attacked - this means what exactly to you?? You saw some blocked hits in your firewall? How do you know your router was attacked last night?
I could say my router gets attacked every few seconds - if you look in your firewall log and think that every unsolicited hit is an "attack" ;)
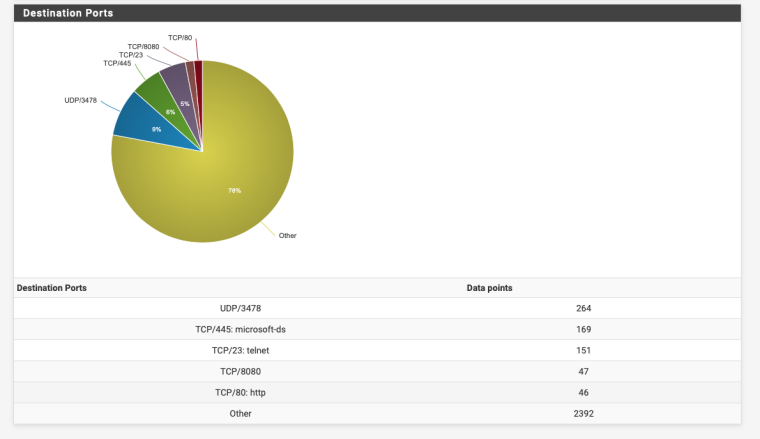
They like to attack the common ports, 23, 22, 3389, 80, 1433 - loads and loads of attacks ;) Or what normal people would call noise.. The internet is FULL of it...
Look at all the noise ;)
-
I saw many TCP connections/IP coming to my WAN public IP port 8080 9pm to 11:30 pm 11:35 pm the internet became normal again. from 30-40 ping my ping goes up to 1000 2000 3000 we are dead last night. my ntopng is not working last night because of the new updates.
I want to know how can i prevent those incoming flood to my WAN public IP.
-
Do you have rules on WAN passing traffic to that port? Do you know what is on 8080 on WAN?
You are getting bad information because you called it a DDoS.
The very first thing I asked was "Attacked how?"
-
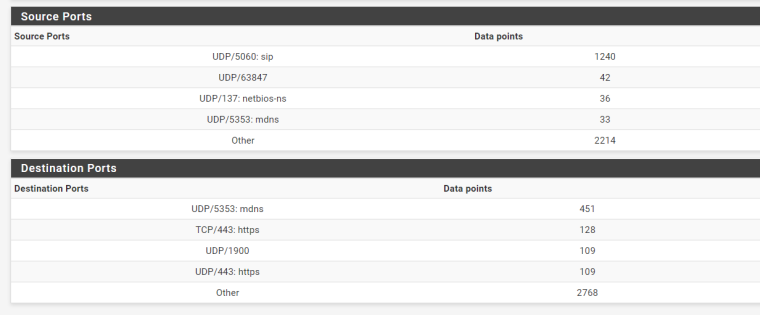
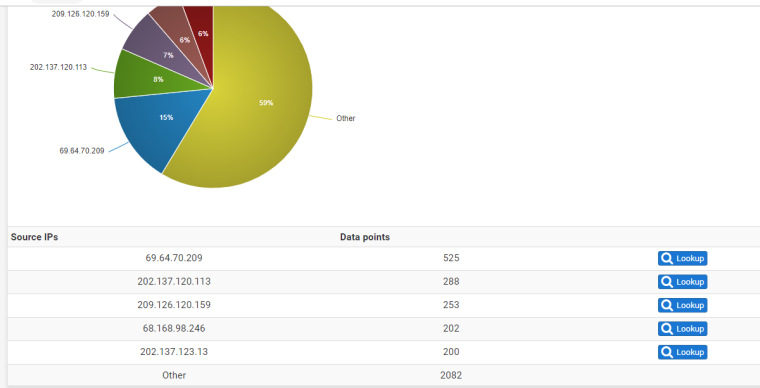
Just to give us an idea post a screenshot of the bottom of Status -> System Logs -> Firewall -> Summary View.
Here's mine I only have 3000 ish drops in total.
-
-
@derelict said in How to prevent DDOS using Snort?:
Do you have rules on WAN passing traffic to that port? Do you know what is on 8080 on WAN?
You are getting bad information because you called it a DDoS.
The very first thing I asked was "Attacked how?"
what should i do sir?
-
Please answer the questions asked for starters.
-
no 8080 there, have you cleared the firewall logs ?
But as Derelict mentioned in his first post if it is a DDoS there isn't much you can do apart from talking to your ISP.
-
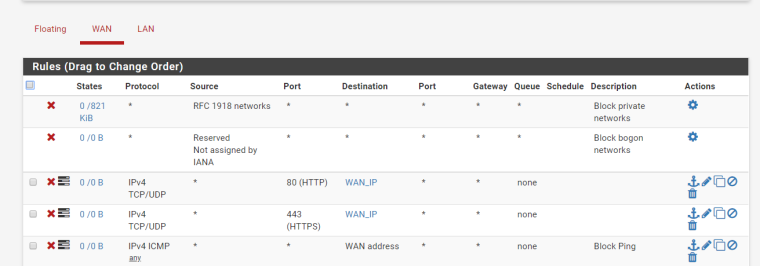
@derelict i dont have a RULES for that port. im using the default rules.
-
Then the connections would have been being blocked and there's not much you can do but talk to upstream to stop it.
Hard to imagine someone sending enough TCP SYNs to a blocked port to be a problem though.
-
@derelict said in How to prevent DDOS using Snort?:
you can do but talk to upstream to stop it
what do you mean by upstream? "you can do but talk to upstream to stop it"
Internet provider? -
Yes.
-
this PFBlockerNG and Snort are useless ? can i just close my WAN ports?
Thank you So much.
-
You said they WERE closed.
Post your WAN rules.
-
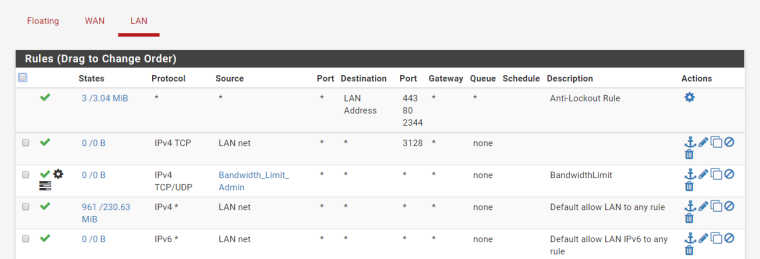
Unless you created a port forward, or running openvpn or something where the wizard would all traffic on your wan to port vpn listen on ALL unsolicited traffic to your wan is dropped/blocked out of the box.
Please post your wan rules as asked, and actually state why you feel you were attacked? A couple hundred hits? Is that even your WAN.. the 5353 and 1900 are most likely broadcast traffic from your lan side.. Or its BS noise from your ISP layer 2 on your wan.
-