PFSENSE randomely blocking ports....
-
Hi, Using ver 2.3.5.
I have Nat rules in place to allow SMTP on port 587 (SUBMISSION) from a Printer/Scanner to a mail server over an OPENVPN setup between two sites.
PFsense randomly stops allowing the connections from this printer to the mail sever! If I reboot the PF box, it fixes itself for a time, then it starts to happen again.
I turned on logging for the NAT rule, but I do not see any logs of whats happening, even what it passes?
I have 2 other machines set up the exact same way with different rules and they work fine.
How do I diagnose this please?
Thanks,
MP
-
why would you need nat rules?
-
Hi Heper,
I am using the rules to only allow SMTP port 587 from specific IPs through because if not i have a bunch of spammers trying to hit my SMTP server.
Thanks,
-
That's what firewall rules are for... Not nat rules
-
Yeah why would you need nat rules for something coming in via nat rules? And why would it be open from the internet if its your devices from a vpn location sending?
-
@johnpoz said in PFSENSE randomely blocking ports....:
nat rules for something coming in via nat rules?
Hi, well that's because the remote networks are on different subnets. No rules, no passage.
The bottom line is that is works, then just stops. PFSense reboot fixes it.
Thx,
-
Again if you have a site to site and your networks on on different subnets there is NO need for natting..
You need in a coma or something - this thread is 4 months old ;) If your going to want help to find your problem your going to have to give some actual details of your config.
If I have
Site A 192.168.1/24
Site B 192.168.2/24
Tunnel 172.16.0/24
Printer 192.168.1.50 in site A needs to send traffic to SMTP 192.168.2.100 there is no use for NAT here. -
@mrpushner said in PFSENSE randomely blocking ports....:
I am using the rules to only allow SMTP port 587 from specific IPs through because if not i have a bunch of spammers trying to hit my SMTP server.
Spammers hitting port 587 ?? That's the "smtp with authentication first" port. And that's not typical at all.
This port is reserved for people that have a mailbox on your server, these people have a login ID (typically : their email address) and a password.
Software clients like Thunderbird and Outlook (or the build in "10" mail client "courrier") could use port "587".
Because certs are free, port "587" starts to fade out, it's port "465" (smtps or smtp over SSL, with identification) these days.If spams come in on port "587" you have a user who's mail account is hacked. Lock him out, that will take care of things just fine. They fckd up their security on their device == they handle the cleaning.
Spam traffic is mail coming in on main mail servers port 25.
Use a good mail server - like postfix (runs more then half of all the mail traffic on planet earth) - coupled with amavis setup, some nice rules from, for example http://jimsun.linxnet.com/misc/postfix-anti-UCE.txt - and finalize the thing with a bloody nervous fail2ban filter.Btw : You have a fixed WAN IP, not known or allocated ton an ISP ? (home based mail servers for sending mails using volatile IP's is a no go for the big player like hotmail/msn/outlook/gmail/yahoo/etc)
-
Spammers are constantly trying to brute force usernames and passwords so, if a weak password is guessed, it can be used to send their spam for a bit.
This happens all day every day no days off.
-
not sure what any of that has to do with site A talking to a mail server at site B over a vpn tunnel?
-
@mrpushner said in PFSENSE randomely blocking ports....:
@johnpoz said in PFSENSE randomely blocking ports....:
nat rules for something coming in via nat rules?
Hi, well that's because the remote networks are on different subnets. No rules, no passage.
The bottom line is that is works, then just stops. PFSense reboot fixes it.
Thx,
Snort?
-
@johnpoz Hi, ok so that is basically my setup with two subnets over OPENVPN tunnel in the 172 arena, just reversed:
Site A 192.168.1/24
Site B 192.168.2/24
Tunnel 172.16.0/24
Printer 192.168.2.50 setup w SMTP settings to 192.168.1.100:587 so it can send scan to email jobs to my SMTP server at 192.168.1.100.I set up rules because I am about certain that this traffic would not go thorough PFSense without them. It works with the rules, but then just stops working randomly.
I seem to be having an issues seeing ANY of these going though PFS in the logs, I have the logs turned on for the rules, but do not see ANY entries like:
"Source = 192.168.2.50:XXXX.....Destination = 192.168.1.100:587....TCP" or the like so I can't pick up on why it stops working.
I found that PFS box reboot usually fixes and it starts working again but that is no fix, and SO ANNOYING.
I'm on 2.3.5.
Thank,
MP
-
@derelict Hi, nope no Snort installed (I do use Squid and Squidguard).
-
What rules you setting up this would not be a NAT this would be a simple firewall run on your openvpn interface, which I believe defaults to any any..
-
@johnpoz Hi, ok yes that would be true but I had to open up the SMTP server to a smart phone user as well...and THAT'S why I have the rules to limit any random hits on the server. Sorry if I left that out.
MP
-
If you turn off the NATting and FW rules for the tunnel and just leave the routing in place, does it work? I am a big fan of configuring the most basic requirements to establish communications, test, and then add complexity after each validated test.
Upgrading to the most current pfSense release may help (always a good idea, you are a few versions behind).
-
I'm not even sure how you could use a NAT rule here without breaking something. Can we see a picture of these rules?
Steve
-
@stephenw10 Hi, Here is one that gets messed up:
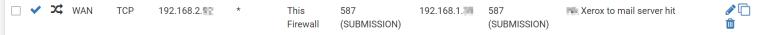
I have another machine that does not have these problems, same setup, but different subnet machine to the 1.x smtp server.
Starting to wonder if its somehow the printer goofing up. I'm looking into getting its logs right now. It works, then stops. I found that the only fix was to reboot the 1.x subnet PFsense box. Other reboots of printer or remote PFS did nothing.
I am going to run the PFS update just to be sure.Thx for the help you guys,
MP
-
Yeah sorry but that rule has ZERO to do with access through your vpn tunnel -- ZERO!!!
-
@johnpoz Humm...I must say I'm feeling a bit dumb....so then how are the packets handled across sub nets? One of my biggest headaches with VPN's was getting them to work across sub nets. Maybe that was my pre netbios days...
I will kill those and see what happens but I SWEAR I could not get this working at all without them.
Thx!