"Poor man" home network first try
-
That setting is for the PPPoE connection only. Many DSL providers require traffic is tagged.
It looks like that is on a separate port on the 2640, eth0. The switch is on eth1 and in standard for will be unconfigured so it might pass VLAN tagged traffic. But you would still need an access point that can use a VLAN directly. I doubt the 2750 can do that with it's default firmware.
Steve
-
@stephenw10 said in "Poor man" home network first try:
That setting is for the PPPoE connection only. Many DSL providers require traffic is tagged.
It looks like that is on a separate port on the 2640, eth0. The switch is on eth1 and in standard for will be unconfigured so it might pass VLAN tagged traffic. But you would still need an access point that can use a VLAN directly. I doubt the 2750 can do that with it's default firmware.
Steve
alright, thank you very much for the patience and the answers with me, i'll give feedback after exêrimùenting with it ^^
-
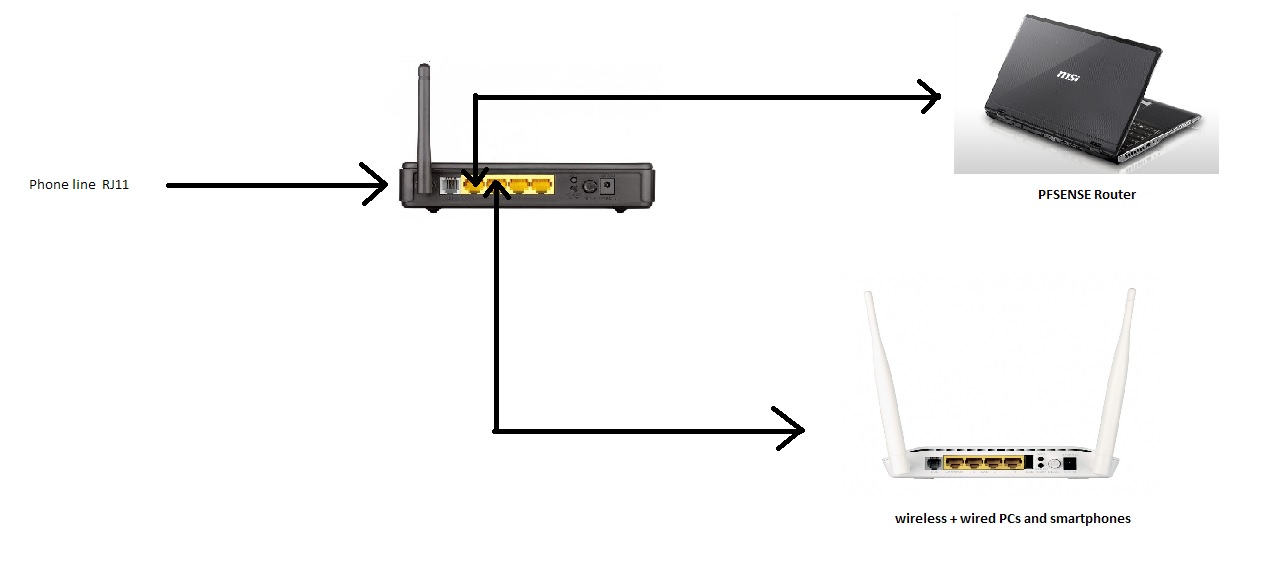
Ok so after some fiddling around i decided to swap it a little around so thatit's only one modem router , the 2750 with all the devices connected to it
i disabled its DHCP and did set it on adress 192.168.1.9 while pfsense is still on 192.168.1.1, tried connecting a laptop with ethernet, and a phone with the wifi, and they both got assigned an IP adress by Pfsense, so that's a step forward for my project.
Also i did setup the same modem as "bridge" for my internet access over the phone line, so i need Pfsense now to dial.
The question i have is, will this "bridging mode" work with my type of ISP way of giving us internet access (over phone line connected to the RJ11 on the modem) ? all the informations i find on the net are for people who gets a direct ethernet cable from their ISP.
and if it does work, can Pfsense establish the internet connection and the redistribute it to the rest of the connected devices ? since it is the the one DHCP that devices connects to THROUGH the modem/router which is acting as an access point so far. if yes, a guide to help me set that up (where to put the vpi//vci and username/password for it to establish the internet connection).
P.S: i can access both PFsense and the 2750 web interface through their respective IP adresses, but PFsense does not show the modem on its DHCP leases tab, whether i set it to 10 or 9, and the phone and laptop were assigned 100 and 101 in the leases tab.
-
Yes, the bridge mode should work. You can pass through the PPPoE connection from the DSL.
The modem should not show on the DHCP leases tab unless it's actually using DHCP which is unlikely. I imagine you set it statically. It will show in Diag > ARP though if pfSense has connected to it recently.
This is an interesting setup if it works. With the PPPoE session passed to pfSense it will have the public IP as it is terminating PPPoE. It will be using the same interface to talk to LAN clients.
The modem should not have any upstream connectivity since it does not have a public IP itself.Steve
-
Interesting is not the term I would use ;) your running your internet and local traffic over the same layer 2.. Doesn't matter that the internet is in a PPPoE or not..
-
Mmm, security wise it's poor.
Interesting in a 'can it work at all' sort of way though.. to me at least.

Steve
-
@aoikite said in "Poor man" home network first try:
And lastly i'm a total newbie in this kind of networks
So from such a statement why are we discussing BAD PRACTICE.. that no sane network person would ever do with someone that is new to the game.. Talk about instilling bad practice..
Yeah you can run multiple layer 3 over the same layer 2 - doesn't mean you SHOULD.. Especially when that layer 2 is the public side, etc..
Get yourself a vlan capable switch so you can correctly isolate your different networks. Even discussing how best to put together something with chewing gum and sticks that "works" is wasting everyone's time.. This isn't a topic about how can I get this to work since the network is DOWN and I need it UP with these shitty parts since the correct parts will be here tmrw, etc..
Sorry but I don't buy the "poor" excuse.. There is no excuse for doing something in a non secure ______ rigged fashion.. Use your network with the device your isp gave you until such time as you can correctly put in a different router/firewall that doesn't compromise security and isolate layer 2 traffic.
-
@stephenw10 said in "Poor man" home network first try:
Yes, the bridge mode should work. You can pass through the PPPoE connection from the DSL.
The modem should not show on the DHCP leases tab unless it's actually using DHCP which is unlikely. I imagine you set it statically. It will show in Diag > ARP though if pfSense has connected to it recently.
This is an interesting setup if it works. With the PPPoE session passed to pfSense it will have the public IP as it is terminating PPPoE. It will be using the same interface to talk to LAN clients.
The modem should not have any upstream connectivity since it does not have a public IP itself.Steve
thank you for your answers, i'll keep experimenting and see how it goes .
@johnpoz said in "Poor man" home network first try:
@aoikite said in "Poor man" home network first try:
And lastly i'm a total newbie in this kind of networks
So from such a statement why are we discussing BAD PRACTICE.. that no sane network person would ever do with someone that is new to the game.. Talk about instilling bad practice..
Yeah you can run multiple layer 3 over the same layer 2 - doesn't mean you SHOULD.. Especially when that layer 2 is the public side, etc..
Get yourself a vlan capable switch so you can correctly isolate your different networks. Even discussing how best to put together something with chewing gum and sticks that "works" is wasting everyone's time.. This isn't a topic about how can I get this to work since the network is DOWN and I need it UP with these shitty parts since the correct parts will be here tmrw, etc..
Sorry but I don't buy the "poor" excuse.. There is no excuse for doing something in a non secure ______ rigged fashion.. Use your network with the device your isp gave you until such time as you can correctly put in a different router/firewall that doesn't compromise security and isolate layer 2 traffic.
I'm sorry if i sound like a stupid person but all the terms you have used, as in layer 2 and layer 3 network are completely stranger to me, and i came here because i'm a person who "learn by breaking stuff and practicing", this is in no way an "optimal setup nor an "oh snap 0$ build you can do at home" kind of project, just a learning experimenting project, and the "poor excuse" is not there an excuse to not buy new hardware at all, new hardware will be used in the future project in 2-3 months when i'll wanna install afully functional network.
Maybe i failed to express that this is just a test subject, and not a permanent solution for a network at home, i'm sorry about that too.
Networking was never my forte in the IT side of things so i came here with the mindset of learning by doing, and if i'm doing something wrong, i would be told that is wrong in the way i'm doing it, learn from it keep on improving.
I did state in my first post that this is just a prototype and theorical project, done with the "junk" i have to see if it can be done, fiddling , reconfiguring and ultimately maybe killing everything is part of the fun fror it as i am learning how to do this in its good and bad sides.
I know that for a network advanced used like you, all of this seems like a waste of time, and getting the smart router and doing the Vlan thingy and call it a day would be time saving for everyone, but i would have learned zero things and for future installs, i would be in the same state of wondering how does it work, and why it is not working.
And in the end sorry if my post seems like a complete waste of time, i joined the community here as a person who wants to learn that's all.
-
This setup (if it works) is bad because your WAN and LAN traffic are traveling over the same connection and there is no separation between them such as VLANs which would create 2 layer 2 segments.
https://en.wikipedia.org/wiki/OSI_modelThat said it could be worse, at least one connection is PPPoE.
If this is just for your own use/experimentation then just be aware of that issue.
Steve
-
@stephenw10 said in "Poor man" home network first try:
This setup (if it works) is bad because your WAN and LAN traffic are traveling over the same connection and there is no separation between them such as VLANs which would create 2 layer 2 segments.
https://en.wikipedia.org/wiki/OSI_modelThat said it could be worse, at least one connection is PPPoE.
If this is just for your own use/experimentation then just be aware of that issue.
Steve
thanks for the article.
This is just a prototype for experimentation, i live in an appartment so it does not really need a network, i just felt like experimenting with what i have to get accustomed to the different things in it and what can be done with it, this is in no way a "red alert" critical thing, but a hobby instead.
i'm doing this to learn the basics and function of pfsense and networking in general since i'm planning to create a full fledged network in the new house for different devices with 2+ nics instead to not use this vlan but it's not the time to talk about hardware really now since it's too early ^^
-
Well break stuff and fix it.

Just be aware that what you're doing is not normal or recommended in a anyway. You will see things that you would not expect to in a correct network setup.
Steve
-
@stephenw10 said in "Poor man" home network first try:
Well break stuff and fix it.

Just be aware that what you're doing is not normal or recommended in a anyway. You will see things that you would not expect to in a correct network setup.
Steve
since you both said that going through the same ethernet port is a bad idea, i started exploring other solutions.
i'm exploring the idea of using the built-in wifi to act as either the lan or the wan part of this network but i doubt this will be functional in any way possible, i'm googling if it is possible in the first place lol.
The other option is somehow getting a second ethernet on this laptop (express34 or usb should suffice)
Any of these methods would fix the security problems right ?
P.S: the future setup will obligatory have a switch and access point to not overcomplicate stuff and for easy management i guess.
-
Yes, any of those options would separate the WAN and LAN of different layer 2 segments.
Wifi support in FreeBSD and hence pfSense is not great. But it may be possible if that is an older device.
What wifi hardware do you have the laptop exactly?Try running
pciconf -lvto see the exact pci vedot and device ID.Steve
-
@stephenw10 said in "Poor man" home network first try:
Yes, any of those options would separate the WAN and LAN of different layer 2 segments.
Wifi support in FreeBSD and hence pfSense is not great. But it may be possible if that is an older device.
What wifi hardware do you have the laptop exactly?Try running
pciconf -lvto see the exact pci vedot and device ID.Steve
in the wireless interface, Pfsense detects it as a Ralink RT3090 and gives the following informations on the command shell :
ral0@pci0:5:0:0: class=0x020000 card 0x68911462 chip=0x30901814 rev=0x00 hdr=0x00 rt3090RT3090 RT3090 wireless 802.11n 1T/1R PCIe
-
That will probably work, and it supports hostap mode (running as an access point).
Don't expect very good performance! But for testing it should be OK.
Steve
-
This post is deleted! -
@stephenw10 said in "Poor man" home network first try:
That will probably work, and it supports hostap mode (running as an access point).
Don't expect very good performance! But for testing it should be OK.
Steve
ok good, i'll go look around how to set everything up ^^
And for a 4/1 or a 8/1 internet speed, no matter what i'll throw as minimum equipments it'll be overkill for it that's for sure
-
@aoikite said in "Poor man" home network first try:
I'm sorry if i sound like a stupid person but all the terms you have used, as in layer 2 and layer 3 network are completely stranger to me,
If you don't know the difference between the two, you're going to have difficulty understanding what you're doing. Perhaps you need a basic course in networking. Layer 2 refers to Ethernet these days, and layer 3 is IPv4 and IPv6. Layer 2 refers only to how the frames move between adjacent devices networks and layer 3 is about how packets move between networks.
It might pass the tagged VLAN packets through the switch
Why do so many people think unmanaged switches will have problems passing VLAN frames? The only difference between a VLAN tagged frame and any other Ethernet frame is the contents of the Ethertype field, along with 4 more bytes. A switch should pass all valid Ethernet frames, no matter what the Ethertype is, though some ancient gear may choke on frames with more than 1500 byte payload. If you ever run into that problem, just reduce the MTU by 4 bytes to work around it.
However, configure VLANs and separate them, you need a managed switch.
-
@jknott said in "Poor man" home network first try:
@aoikite said in "Poor man" home network first try:
I'm sorry if i sound like a stupid person but all the terms you have used, as in layer 2 and layer 3 network are completely stranger to me,
If you don't know the difference between the two, you're going to have difficulty understanding what you're doing. Perhaps you need a basic course in networking. Layer 2 refers to Ethernet these days, and layer 3 is IPv4 and IPv6. Layer 2 refers only to how the frames move between adjacent devices networks and layer 3 is about how packets move between networks.
It might pass the tagged VLAN packets through the switch
Why do so many people think unmanaged switches will have problems passing VLAN frames? The only difference between a VLAN tagged frame and any other Ethernet frame is the contents of the Ethertype field, along with 4 more bytes. A switch should pass all valid Ethernet frames, no matter what the Ethertype is, though some ancient gear may choke on frames with more than 1500 byte payload. If you ever run into that problem, just reduce the MTU by 4 bytes to work around it.
However, configure VLANs and separate them, you need a managed switch.
thank you for your explanations, your explanation and the wiki article posted by Steve did help me understand that concept ^^.
To avoid using Vlans at all, i am experimenting with Wireless now , that will make me avoid using vlans, and hopefully it will work if i can establish a PPPOE over wireless.
-
Because this is not an unmanaged switch. Almost all built in switches in soho routers are VLAN capable and can be configured with internal VLANs to separate ports for a second WAN etc. Except no manufacturer firmware allows you to configure that or even see it.
So if that switch is in port vlan mode then sure I expect it to pass tagged traffic but it might be in dot1Q mode just all on the same VLAN in which case it will not. No way to know.Steve