IPSec issues
-
But does it impact traffic flow across the VPN?
-
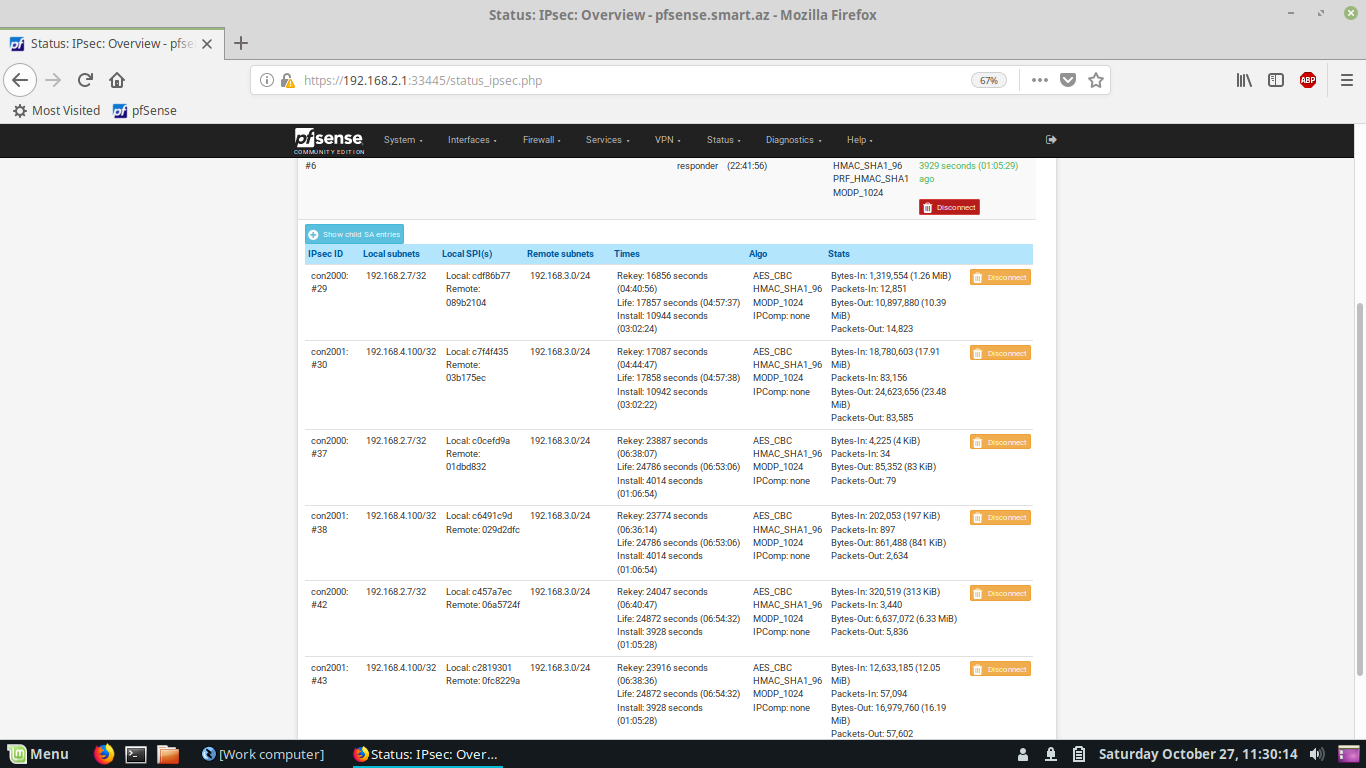
I ping remote server, it is going okay, sometimes it shows "Request timed out". As you can see it duplicates phase 2.
-
Those are harmless. They are rekeyed tunnels. They are not the cause of any traffic flow issues. They will disappear when their lifetimes expire. They are there in case the other side sends traffic to the rekeyed SAs so it can be decrypted.
Running the shell command
ipsec statusallwill reveal them as rekeyed.If you have traffic problems over the VPN I would not spend any more time on that and focus on other reasons you might be seeing what you are seeing.
-
Thank you. The problem is, when phase 2 rekey expires it creates a new one, but it also duplicates phase 2. Then there are two same phase 2, they expire and create new same ones.I have 4 ipsec connections, one with Palo Alto, the rest with Mikrotik routers. Ipsec with Palo Alto and one of Mikrotik is working normal. Though the rest two Mikrotik have the same configurations as others, we see these issues.
You think it is because of Mikrotik?
What if I disable rekey? Then it will not work?
Why there are 15 minutes difference between rekey and life?
Is it okay if I add margin time for example 5 seconds, because of decreasing 15 minutes to 5 seconds?
Why phase1 in IKEv2 expires, it removes all phase 2 and creates phase 2 again? This doesn't happen in IKEv1. -
@emammadov said in IPSec issues:
Thank you. The problem is, when phase 2 rekey expires it creates a new one, but it also duplicates phase 2. Then there are two same phase 2, they expire and create new same ones.I have 4 ipsec connections, one with Palo Alto, the rest with Mikrotik routers. Ipsec with Palo Alto and one of Mikrotik is working normal. Though the rest two Mikrotik have the same configurations as others, we see these issues.
Right. That is normal.
You think it is because of Mikrotik?
No.
What if I disable rekey? Then it will not work?
No. I would not do that.
Why there are 15 minutes difference between rekey and life?
The rekey is set randomly a short interval before the lifetime. This is perfectly normal.
Is it okay if I add margin time for example 5 seconds, because of decreasing 15 minutes to 5 seconds?
I would leave it alone.
Why phase1 in IKEv2 expires, it removes all phase 2 and creates phase 2 again? This doesn't happen in IKEv1.
Because that's how it works. You can see if enabling Make-Before-Break in VPN > IPsec, Advanced helps but read the notes there and understand that will affect all IKEv2 tunnels.
Keep in mind that the IPsec > Status screen can be delayed by several seconds.
Again, those rekeyed SAs are probably NOT the source of any problems you are having as long as the new SA is established on rekey. You are probably chasing a ghost.

-
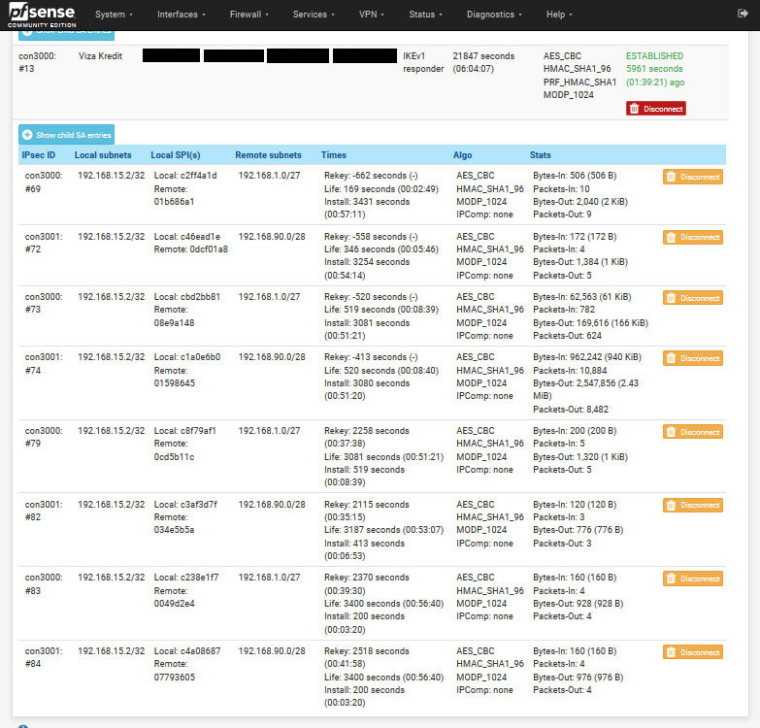
Ok. I have another question. There is ipsec IKEv2 connection. Phase 1 and two phase 2. Phase 1 and two phase 2 is ip. It is also seems to be up in Status / IPSec. But in the dashboard, I mean the home page of pfsense, only one phase 2 tunnel seems to be up.
-
If you look at the actual phase 2 it is probably combined into one with both sets of addresses.
-
In IKEv1, each phase 2 seems separate. Why it is not so in Ikev2. Is it possible do it as Ikev1 in the next update? Because it makes user to get confused.
-
Because IKEv2 can combine them.
If you do not like this behavior you can try enabling Split Connections on that tunnel.
Some devices, notably the Cisco ASA, do not allow multiple traffic selectors on one SA so that option was added.
-
Thank you very much.
-
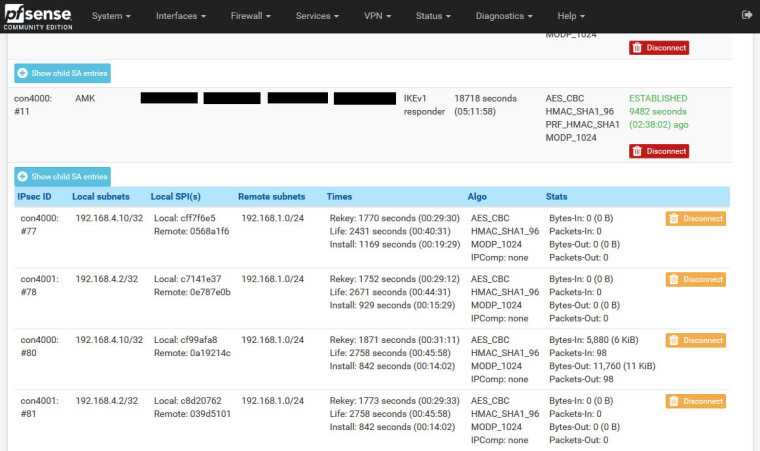
If I enable Make before Break in Advanced settings for IKEv2 in pfsense, then does the remote side should support this? pfSense is responder and Mikrotik is initiator in ipsec. I noticed that Make before Break option is available in Mikrotik settings. Will it create a problem in connection?
-
No idea what the Mikrotik will do but, yes, both sides need to support it. Set a maintenance window, try it, and see.