When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface
-
When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface, from the LAN can be ping without problems. This causes that HAPROXY only works with ipv6 from the LAN interface, and is not the scenario that I would like. It also causes the installation of packages to take too long, up to half an hour each package, and only installing by command line, the web installation does not work. This is caused because not manages to access the package repositories through Ipv6, which is predetermined in the WAN interface, and until it manages to download by ipv4, it has been a long time.
I get native Ipv6 through my ISP and that way it was working without problems, in LAN and in WAN, until this update.
The environment is bare metal in production, but there are I have the same problems in virtualized environments under XEN, most have been solved by making a clean installation and generating new configurations from scratch, which is already a huge annoyance with preconfigured snort rules, example. But the most annoying problem with the ipv6 connection from wan follows, from a clean installation, without packages installed.
Thanks and sorry for my english
-
I'm sure it's a bug in version 2.4.4, which came out in a hurry. I reported this and other failures at the site where the bugs were reported and I was told that I should report it through this way. I'm doing it, but I do not see any interest either over here. In Pfsense there is not even a way to install a previous version.
-
I have no problem pinging an IPv6 address from pfSense.
-
@jknott I do have problems. Would someone like to investigate it?
-
@jknott If you tell me what additional information you need, I gladly provide it. The problem arose with this update and in two different environments. All the configuration worked in previous versions of Pfsense for more than a year. I also tried it with the default configuration and with the same result.
-
From WAN:
PING6(56=40+8+8 bytes) 2800:bf0:9fff:xxxx:xxx:xxxx:xxxx:xxxx --> 2606:4700:30::681c:d34--- rebelion.org ping6 statistics ---
3 packets transmitted, 0 packets received, 100.0% packet lossFrom LAN:
PING6(56=40+8+8 bytes) 2800:bf0:xxxx:xxxx:xxx:xxxx:xxxx:xxxx --> 2606:4700:30::681c:d34
16 bytes from 2606:4700:30::681c:d34, icmp_seq=0 hlim=53 time=96.966 ms
16 bytes from 2606:4700:30::681c:d34, icmp_seq=1 hlim=53 time=97.079 ms
16 bytes from 2606:4700:30::681c:d34, icmp_seq=2 hlim=53 time=96.010 ms--- rebelion.org ping6 statistics ---
3 packets transmitted, 3 packets received, 0.0% packet loss
round-trip min/avg/max/std-dev = 96.010/96.685/97.079/0.480 ms -
I am seeing the same thing with my SG-3100 applicance running on 2.4.4...
I can ping6 from LAN devices without a problem, but I cannot from a shell on the router.
And same as you, software updates take a long time as the router tries IPv6 first and only when it times out does it try IPv4. -
me too no problems. check your 4th okted, maybe there is something wrong? traceroute?
-
@yellowbrick Thanks for your report. That helped someone ask questions, the questions are important for the discovery, answering only that you do not have the problem is not very helpful. A hug.
-
@pfadmin A huge thank you for your questions. I know you do not have the problem, but I do and I'm not the only one, as you can see in the previous comment.
Traceroue output:
traceroute from wan:
1 2800:bf0:9fff:f110::1 2.702 ms 1.517 ms 2.673 ms
2 2800:bf0:9fff:f100::1 2.790 ms 2.471 ms 2.793 ms
3 fc00:0:0:600::1 1.756 ms 1.622 ms 1.733 ms
4 * * *
5 * * *
6 * * *
7 * * *
8 * * *
9 * * *
10 * * *
11 * * *
12 * * *
13 * * *
14 * * *
15 * * *
16 * * *
17 * * *
18 * * *Traceroute from LAN:
1 2800:bf0:9fff:f111::1 4.482 ms 1.862 ms 3.859 ms
2 2800:bf0:9fff:f100::1 3.641 ms 2.359 ms 2.915 ms
3 fc00:0:0:600::1 1.691 ms 3.023 ms 1.492 ms
4 * * *
5 2800:2a0:10:101:11::211 72.568 ms 77.331 ms 74.598 ms
6 2001:1900:2100::238d 70.480 ms 70.430 ms 72.982 ms
7 2001:1900::3:132 75.741 ms 76.288 ms 75.676 ms
8 2001:1900:4:3::18e 88.305 ms 75.839 ms 70.418 ms
9 2001:41a8:4020::13 84.835 ms 70.486 ms 70.600 ms
10 2001:41a8:4020:2::c2 97.255 ms 97.499 ms 93.197 ms
11 2400:cb00:17:1024::a29e:79b2 96.907 ms
2400:cb00:17:1024::a29e:784d 100.754 ms
2400:cb00:17:1024::a29e:7805 100.615 msAs I said above I tried with the factory settings and the result is the same. The current configuration had no problems and I have not changed it since version 2.4.2.
On 4th okted I would appreciate you explain to me to verify. I do not find information on this on the internet.
-
@fabianburpf said in When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface:
2606:4700:30::681c:d34
From one of my customer boxes. Comcast connection.
PING6(56=40+8+8 bytes) 2001:558:xxxxxxxxxxxxxxxxxxxx --> 2606:4700:30::681c:d34
16 bytes from 2606:4700:30::681c:d34, icmp_seq=0 hlim=58 time=16.638 ms
16 bytes from 2606:4700:30::681c:d34, icmp_seq=1 hlim=58 time=12.921 ms
16 bytes from 2606:4700:30::681c:d34, icmp_seq=2 hlim=58 time=13.744 ms
16 bytes from 2606:4700:30::681c:d34, icmp_seq=3 hlim=58 time=13.252 ms--- 2606:4700:30::681c:d34 ping6 statistics ---
4 packets transmitted, 4 packets received, 0.0% packet loss
round-trip min/avg/max/std-dev = 12.921/14.139/16.638/1.472 msWorks fine. May be something your ISP is doing??
-
@chpalmer Regarding your question: "Works fine. May be something your ISP is doing???" I can assure you that the problem starts with version 2.4.4. When I have been able to install a previous virtual version, from a snapshot, directly connected to the optical fiber ONT, everything works the way it is expected. I really do not think that event coincides with something the ISP does. I repeat that it worked fine, with the same configuration, before the update to 2.4.4
-
@fabianburpf said in When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface:
fc00:0:0:600::1
https://en.wikipedia.org/wiki/IPv6_address
fc00::/7 is a ULA
What happens if you use the option -s ?
Usage: traceroute [-adDeFInrSvx] [-f first_ttl] [-g gateway] [-i iface]
[-m max_ttl] [-p port] [-P proto] [-q nqueries] [-s src_addr]
[-t tos] [-w waittime] [-A as_server] [-z pausemsecs] host [packetlen][2.4.4-RELEASE][admin@pfsense]/root: traceroute6 -s 2a02:xxxx:xxxx:xxxx::1 2a02:8010:1:0:212:23:3:100
traceroute6 to 2a02:8010:1:0:212:23:3:100 (2a02:8010:1:0:212:23:3:100) from 2a02:xxxx:xxxx:xxxx::1 , 64 hops max, 20 byte packets
1 lo-0.cor2.lond1.ptn.zen.net.uk 10.671 ms 9.486 ms 9.277 ms
2 ae-13.cor2.manc1.ptn.zen.net.uk 17.043 ms 28.985 ms 20.455 ms
3 ae-22.cor1.manc1.ptn.zen.net.uk 16.278 ms 21.254 ms 21.568 ms
4 ae-23.cor1.roch1.ptn.zen.net.uk 20.429 ms 16.365 ms 16.597 ms
5 2a02:8010:0:a00:: 14.285 ms 28.466 ms 15.194 ms
6 2a02:8010:0:207::2 14.772 ms 14.343 ms 14.794 ms
7 cache01.dns.zen.net.uk 15.447 ms !P 14.768 ms !P 14.754 ms !P
[2.4.4-RELEASE][admin@pfsense]/root:Maybe do a packet capture on the WAN and open it in wireshark.
-
@nogbadthebad
from WAN:
traceroute6 -s 2800:bf0:9fff:xxxx:xxx:xxxx:xxxx:xxxx 2a02:8010:1:0:212:23:3:100
traceroute6 to 2a02:8010:1:0:212:23:3:100 (2a02:8010:1:0:212:23:3:100) from 2800:bf0:9fff:xxxx:xxx:xxxx:xxxx:xxxx, 64 hops max, 20 byte packets
1 2800:bf0:9fff:f110::1 2.599 ms 2.243 ms 2.207 ms
2 2800:bf0:9fff:f100::1 2.394 ms 2.369 ms 2.441 ms
3 fc00:0:0:600::1 1.994 ms 1.637 ms 1.683 ms
4 * * *
5 * * *
6 * * *
7 * * *
8 * * *
9 * * *
10 * * *
11 * * *
12 * * *
13 * * *
14 * * *
15 * * *
16 * * *
17 * * *
18 * * *
19 * * *
20 * * *
21 * * *
22 * * *
23 * * *
24 * * *
25 * * *
26 * * *
27 * * *
28 * * *
29 * * *
30 * * *
31 * * *
32 * * *
33 * * *
34 * * *
35 * * *
36 * * *
37 * * *
38 * * *
39 * * *
40 * * *
41 * * *
42 * * *
43 * * *
44 * * *
45 * * *
46 * * *
47 * * *
48 * * *
49 * * *
50 * * *from LAN:
traceroute6 -s 2800:bf0:81c0:xxxx:xxx:xxxx:xxxx:xxxx 2a02:8010:1:0:212:23:3:100
traceroute6 to 2a02:8010:1:0:212:23:3:100 (2a02:8010:1:0:212:23:3:100) from 2800:bf0:81c0:xxxx:xxx:xxxx:xxxx:xxxx, 64 hops max, 20 byte packets
1 2800:bf0:9fff:f111::1 3.459 ms 2.361 ms 3.280 ms
2 2800:bf0:9fff:f100::1 3.107 ms 2.593 ms 2.265 ms
3 fc00:0:0:600::1 1.763 ms 1.724 ms 1.795 ms
4 * * *
5 2800:2a0:10:101:11::211 71.608 ms 76.455 ms 75.247 ms
6 xe-9-2-0.edge2.LosAngeles9.Level3.net 70.580 ms 71.078 ms 70.428 ms
7 * * *
8 NTT-level3-1x10G.Madrid.Level3.net 70.580 ms 77.561 ms 83.484 ms
9 ae-7.r04.miamfl02.us.bb.gin.ntt.net 72.544 ms 72.455 ms 72.457 ms
10 ae-8.r20.miamfl02.us.bb.gin.ntt.net 70.412 ms 70.779 ms 70.630 ms
11 ae-4.r23.asbnva02.us.bb.gin.ntt.net 100.332 ms 99.949 ms 99.625 ms
12 ae-0.r22.asbnva02.us.bb.gin.ntt.net 94.707 ms 100.264 ms 97.873 ms
13 ae-5.r25.nycmny01.us.bb.gin.ntt.net 99.857 ms 100.454 ms 100.296 ms
14 ae-1.r24.nycmny01.us.bb.gin.ntt.net 97.993 ms 99.637 ms 98.212 ms
15 ae-9.r24.londen12.uk.bb.gin.ntt.net 165.782 ms 165.254 ms 169.869 ms
16 ae-8.r02.londen03.uk.bb.gin.ntt.net 166.849 ms 165.433 ms 170.634 ms
17 xe-0-1-0-1-7.r02.londen03.uk.ce.gin.ntt.net 176.106 ms 163.838 ms 164.328 ms
18 ae0.cr1.th-lon.zen.net.uk 189.817 ms 196.175 ms 202.502 ms
19 ae4-0.cr1.wh-man.zen.net.uk 180.254 ms 180.711 ms 214.937 ms
20 ae0-0.dr1.sp-roch.zen.net.uk 183.841 ms 183.225 ms 183.929 ms
21 2a02:8010:0:205::2 176.856 ms 179.267 ms 180.045 ms
22 cache01.dns.zen.net.uk 188.908 ms !P 190.330 ms !P 185.477 ms !P -
@nogbadthebad Please explain the packages you should capture and the way to do it. Thank you
-
@fabianburpf said in When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface:
@chpalmer I really do not think that event coincides with something the ISP does. I repeat that it worked fine, with the same configuration, before the update to 2.4.4
So if mine and everyone else's works why do you think your issue is a problem caused by pfsense other than "it worked before"?
(Please explain the packages you should capture and the way to do it. Thank you) -
/diag_packet_capture.php
[2.4.4-RELEASE][admin@xxxxxx.xxxxxxx.org]/root: traceroute6 -s 2xxxxxxxxx 2a02:8010:1:0:212:23:3:100
traceroute6 to 2a02:8010:1:0:212:23:3:100 (2a02:8010:1:0:212:23:3:100) from 2001:xxxxxxxxxxxxxxxxxxxx, 64 hops max, 20 byte packets
1 2001:558:600a:cf::1 13.859 ms 9.883 ms 9.237 ms
2 po-107-rur01.tumwater.wa.seattle.comcast.net 9.899 ms 9.964 ms 9.775 ms
3 po-2-rur02.tumwater.wa.seattle.comcast.net 8.105 ms 11.319 ms 9.661 ms
4 be-44-ar01.seattle.wa.seattle.comcast.net 13.879 ms 13.628 ms 13.768 ms
5 be-33650-cr01.seattle.wa.ibone.comcast.net 15.052 ms * 16.749 ms
6 *
be-10847-pe02.seattle.wa.ibone.comcast.net 13.869 ms *
7 ae-31.a00.sttlwa01.us.bb.gin.ntt.net 13.663 ms 15.770 ms 13.494 ms
8 ae-9.r04.sttlwa01.us.bb.gin.ntt.net 14.514 ms 13.721 ms
ae-14.r05.sttlwa01.us.bb.gin.ntt.net 14.077 ms
9 ae-2.r22.sttlwa01.us.bb.gin.ntt.net 13.764 ms 14.382 ms
ae-1.r22.sttlwa01.us.bb.gin.ntt.net 17.675 ms
10 ae-0.r24.nycmny01.us.bb.gin.ntt.net 88.579 ms 101.201 ms 85.140 ms
11 ae-9.r24.londen12.uk.bb.gin.ntt.net 156.562 ms 151.233 ms 150.401 ms
12 ae-8.r02.londen03.uk.bb.gin.ntt.net 153.440 ms 153.703 ms 148.896 ms
13 xe-0-1-0-1-7.r02.londen03.uk.ce.gin.ntt.net 156.026 ms 158.485 ms 158.553 ms
14 ae0.cr1.th-lon.zen.net.uk 158.899 ms 153.132 ms 155.254 ms
15 ae4-0.cr1.wh-man.zen.net.uk 166.248 ms 193.078 ms 166.346 ms
16 ae0-0.dr1.sp-roch.zen.net.uk 164.142 ms 184.691 ms 161.297 ms
17 2a02:8010:0:205::2 173.480 ms 168.982 ms 159.820 ms
18 cache01.dns.zen.net.uk 161.215 ms !P 165.877 ms !P 169.071 ms !P
[2.4.4-RELEASE][admin@xxxxx.xxxxx.org]/root: -
@chpalmer said in When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface:
So if mine and everyone else's works why do you think your issue is a problem caused by pfsense other than "it worked before"?
I do not understand this question. I think it is not a help, but it can be a difficulty with the interpretation of the language or culture, if not, I do not see how we move forward.
-
@fabianburpf said in When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface:
@chpalmer said in When making the update to 2.4.4 it is impossible to ping IPV6 from the WAN interface:
So if mine and everyone else's works why do you think your issue is a problem caused by pfsense other than "it worked before"?
I do not understand this question. I think it is not a help, but it can be a difficulty with the interpretation of the language or culture, if not, I do not see how we move forward.
Im trying to reason with you. You obviously have a problem that we do not have. We cannot diagnose your issue because it does not exist for us.
Do you know how to take screen shots and post them?
-
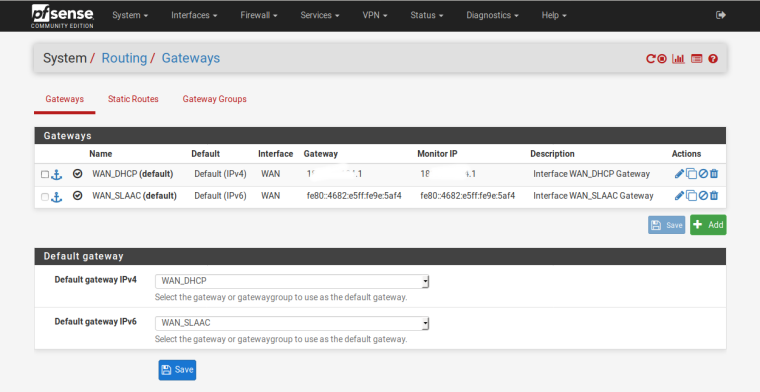
Show us this page.
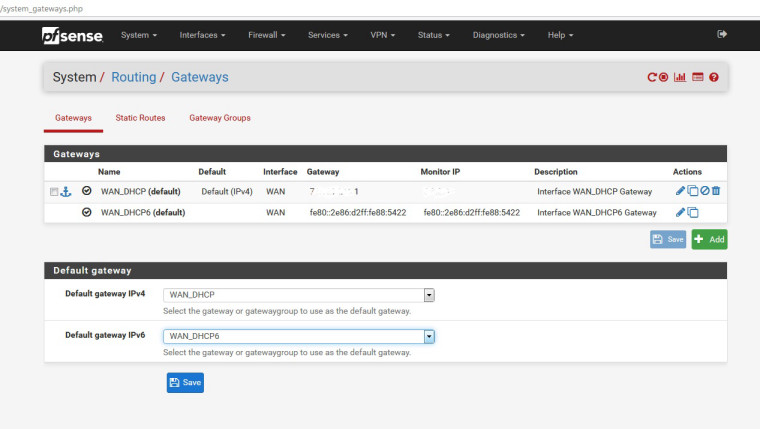
-