Isolating VLANs from each other and management interface
-
It really is very simple..
Rules are evaluated as traffic enters an interface from the network the interface is attached too..
Rules are evaluated top down, first rule to trigger wins, no other rules are evaluated..
Lets see your rules and we can discuss what your doing wrong.
So think of what your traffic is you want to allow or deny.. And walk through the rules..
You have a source IP, dest IP and Port.. Which rule will trigger as you work down top to bottom? If any, etc.
Since you want to block access to all other vlans you prob want to create a alias that contains all the rfc1918 space, or atleast your networks in use. The whole rfc1918 is easier, and keep in mind the "this firewall" built in alias as well. Which includes all pfsense IPs on any lan or vlan interfaces along as its wan IP.. So this is good to use to make sure clients can not talk to pfsense after you allow what they need to talk to pfsense for, like dns, ntp, ping
Here from my quick read these rules would work for what you asked for.
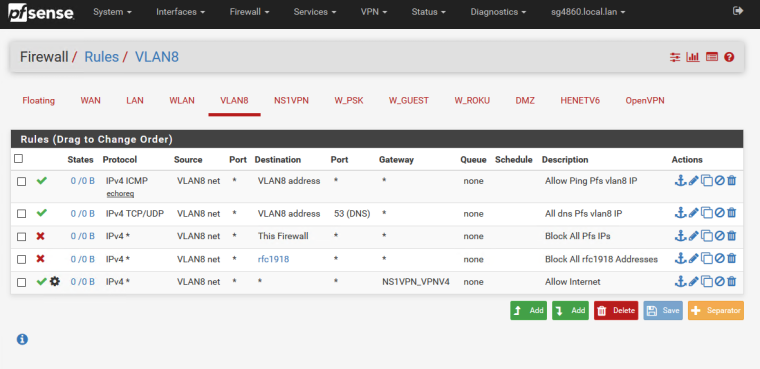
1st first rule allows ping of pfsense IP on that vlan - for testing connectivity.
2nd Rule allow to ask pfsense for DNS... Not sure why really if your forcing everything out your vpn, your clients should really point to some vpn or outside dns if your forcing all their traffic out a vpn.3rd rule - blocks ALL access to any firewall IP not allowed by 1st 2 rules. This would also be blocked by 4th rule, except for the pfsense WAN ip, etc.. But it makes it easy to understand that all access to any firewall IP is blocked.
4 Rule blocks all access to any rfc1918 address = all your other vlans.
5th rule shoves anything not allowed blocked by above 4 rules out the VPN.. -
Much thanks for the reply, and it's starting to make sense to me. After reading it, I suspect my issue is an allow rule on the rfc1918 space which I probably misunderstood when I read it in one of the guides. I'll get my rules posted for inspection tonight. I've become fearful that I allow too much traffic.
-
Okay, thanks again for your help. I very much appreciate any review of what I have, as its a hodgepodge cobbled together from various guides and my limited knowledge.
After Johnpoz's help earlier, I have a setup that appears to satisfy my bullets 1-4.

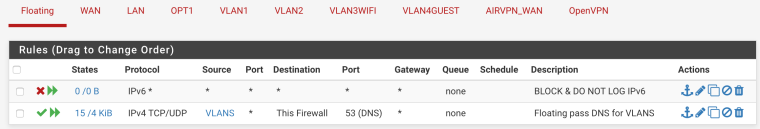
My floating rules, where "VLANS" has all 4 of my VLANs in the alias.
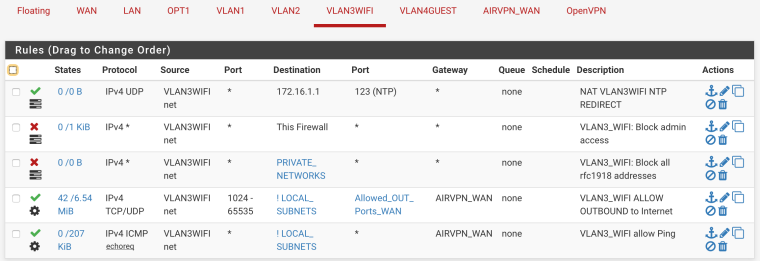
The VLAN3_WIFI interface I setup as a Wifi AP, where "PRIVATE_NETWORKS" represents the RFC1918 address space, "LOCAL_SUBNETS" is all 4 VLANs + OPT1 + root at 172.16.1.0/24, and "Allowed_OUT_Ports_WAN" is ports 80, 443, and the ephemeral range. I'm not sure that NTP line is useful, it's a holdover from what I thought was correct for redirects...more on that in a bit.
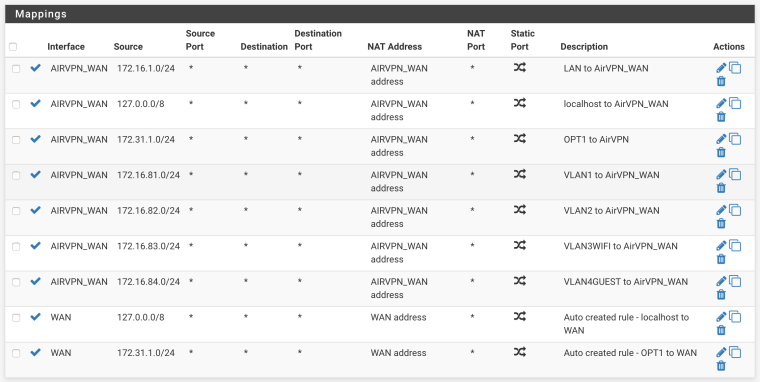
I ended up removing all my port forwarding entries, as they didn't seem useful. I had gotten the idea for locking down DNS based on the "nguvu.org" guide. I kept all these from Firewall/NAT/Outbound:
-
@octoberfest said in Isolating VLANs from each other and management interface:
Allowed_OUT_Ports_WAN" is ports 80, 443, and the ephemeral range.
So how exactly are clients suppose to do dns.. Where is your rule that allows it to talk 53?
Oh - in your floating... Yeah that is why I don't do stuff in floating... Because when your looking at an interface and trying to figure out why something doesn't work.. You can not walk down the tree correctly..
And your doing your block OUTBOUND on the floating or inbound? Or any... Why not just put the rule on the interface so you can easy see them as you look at a specific interface.
Also setting rule for 1024-65 for source ports? Dude just use ANY... Same as your dest... I mean really What do you think your going to stop there? If you only want to allow 80 and 443, then just allow those.. If your going to do 80,443 and >1024 might as well just say ANY..
-
@johnpoz said in Isolating VLANs from each other and management interface:
And your doing your block OUTBOUND on the floating or inbound? Or any... Why not just put the rule on the interface so you can easy see them as you look at a specific interface.
Umm...because I'm a n00b trying to learn.

Also setting rule for 1024-65 for source ports? Dude just use ANY... Same as your dest... I mean really What do you think your going to stop there? If you only want to allow 80 and 443, then just allow those.. If your going to do 80,443 and >1024 might as well just say ANY..
See my previous comment about being a n00b. My goal is the best privacy & security possible, and it seems I'm misunderstanding the risk profile of different scenarios. Perhaps I am trying to think too much of my network firewall as similar to a client-side firewall that blocks certain applications from accessing the internet (because really, many programs that want internet access don't need it, i.e. privacy exposure).
-
One other thing I don’t quite understand — where does LAN fit into all this based on the SG-3100 and my VLAN topology? It seems to me as an interface from a firewall perspective, it is transparent and “rule-less.” Is that correct?
-
Huh? Lan is just your first network behind your firewall - no different than any other vlan/network you create..
-
Right, but from a firewall rule standpoint, it doesn’t seem much goes on there, as traffic originates either from a VLAN or the WAN, right?
-
Huh? Most of my traffic comes from LAN, since that is where my main machine and nas sit.. If you don't put anything on that specific network - then no there wouldn't be much traffic there.
But your typical user might only have that 1 lan network, and not have any other network segments/vlans..
Not getting what your question is exactly?
All your vlans/interfaces other than wan connections would be considered LAN side interfaces..
-
Maybe if I take the example of what I did with that floating rule and DNS. My configuration is that each port in the 'LAN' is a VLAN. I took your advice and moved my 'pass DNS' rule to individual VLAN segments and it seems to work fine.
Would putting a 'pass DNS' rule on the LAN interface, instead of each individual VLAN interface, have the same result, such that the 1 rule covers all the segments below it?
-
I still have no clue to what your talking about with LAN... That out of the box would be just local side network that is not tagged. This would normally be your physical interface say em1 or igb1
Wan em0
Lan em1Wan igb0
Lan igb1Or those could be the other way around.
If you do not put a network on em1 or igb1, and just put vlans sitting on the physical interface.. There is would be NO rules or even a untagged network on that interface...
Post up your interface assignment page..
example
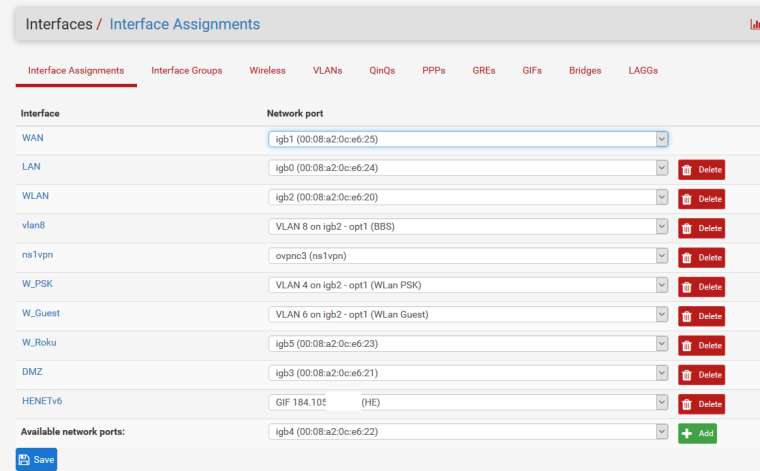
See my lan is attached is on igb0, I also have another network wlan that is on igb2 untagged, and then have VLANS on igb2 as well.
Here I changed its name from LAN to something else
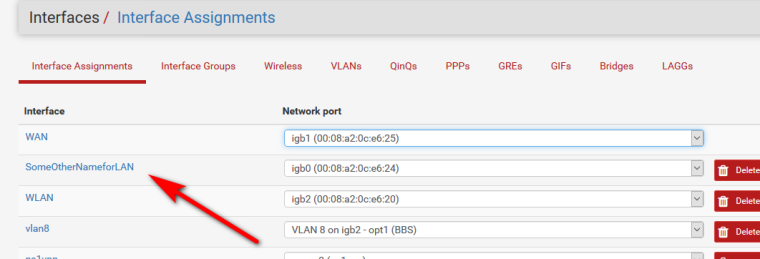
Lan is not really anything special..
Its just the NAME that pfsense gives to the first local side network. That is not a WAN connection, ie it does not have a gateway.
That interface is also the interface that pfsense would put the antilock out rules on - unless you disabled them.
-
I can get the actual interfaces screen shot tonight.
What I can recall and dig from the setup guide of the SG-3100, is the following:
WAN: mvneta2
OPT1: mvneta0
LAN : mvneta1
VLAN1: 4081 on mvneta1
VLAN2: 4082 on mvneta1
VLAN3: 4083 on mvneta1
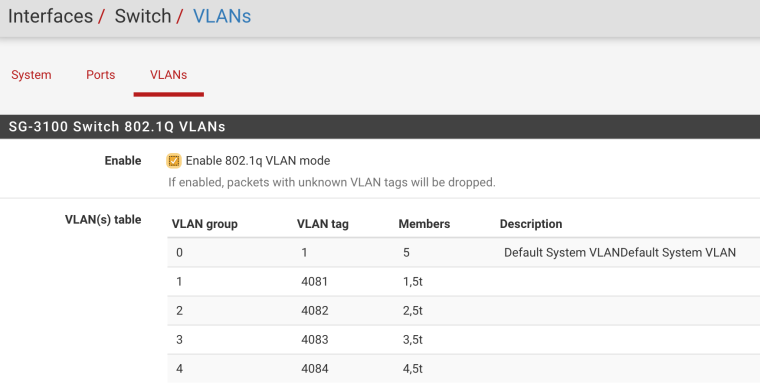
VLAN4: 4084 on mvneta1For the VLANs, they're setup with 802.1Q and each of the VLAN1-4 segments has as members itself untagged and the LAN uplink tagged.
-
Again you can assign "LAN" to whatever you be it the actual interface or the switch ports, etc.
If you don't want to use the "LAN" network then don't.. Did you assign a IP to it?
-
I'll probably need to dig up some stuff from the unit tonight. I think I have it set to 172.16.1.1. What I don't understand well is in this topology how the tagged trunk fits into things. I probably don't understand enough to ask the right question(s)....
-
The tagged trunk is the connection from the "switch" to pfsense..
-
Right, that makes sense to me. From a firewall rule standpoint, does applying rules to that connection cover all the VLANs (similar to, but different from, a 'floating' rule)? Or in my case is the LAN something that basically I ignore and I just focus on each VLAN interface?
-
Much thanks for your patience trying to understand my ignorance and naivete.
Here's my interfaces tab:
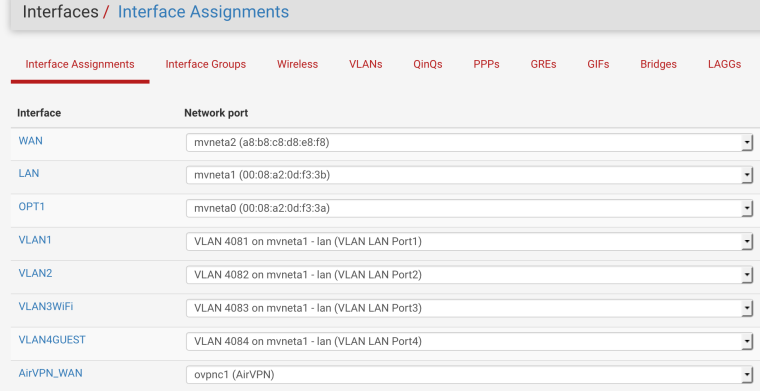
And my VLANS:
I presently have no firewall rules on the 'LAN' interface, given my topology, and things basically seem to work. I am just so novice at this (it's like moving from an automatic to a manual transmission, quite simple once you know what you'e doing, but hard when you don't) I'm hoping the experts can help me avoid doing something stupid.
From a management standpoint, my original gravitation toward floating rules was based on the idea of applying something in 1 place that affects many, since I have the VLAN segments. My goal with VLAN segments is to allow rigid partitioning of the network and get to a point I have private & guest WIFI access via AP's and that nothing can see anything else. I have no trust for IoT devices, so they end up on their own isolated segment.
And I want it all routing through VPN (including DNS and anything else) since my ISP is questionable at best. I pay for service, I am a customer, not a product whose privacy doesn't matter. (stepping off soap box)