Isolating VLANs from each other and management interface
-
Huh? Lan is just your first network behind your firewall - no different than any other vlan/network you create..
-
Right, but from a firewall rule standpoint, it doesn’t seem much goes on there, as traffic originates either from a VLAN or the WAN, right?
-
Huh? Most of my traffic comes from LAN, since that is where my main machine and nas sit.. If you don't put anything on that specific network - then no there wouldn't be much traffic there.
But your typical user might only have that 1 lan network, and not have any other network segments/vlans..
Not getting what your question is exactly?
All your vlans/interfaces other than wan connections would be considered LAN side interfaces..
-
Maybe if I take the example of what I did with that floating rule and DNS. My configuration is that each port in the 'LAN' is a VLAN. I took your advice and moved my 'pass DNS' rule to individual VLAN segments and it seems to work fine.
Would putting a 'pass DNS' rule on the LAN interface, instead of each individual VLAN interface, have the same result, such that the 1 rule covers all the segments below it?
-
I still have no clue to what your talking about with LAN... That out of the box would be just local side network that is not tagged. This would normally be your physical interface say em1 or igb1
Wan em0
Lan em1Wan igb0
Lan igb1Or those could be the other way around.
If you do not put a network on em1 or igb1, and just put vlans sitting on the physical interface.. There is would be NO rules or even a untagged network on that interface...
Post up your interface assignment page..
example
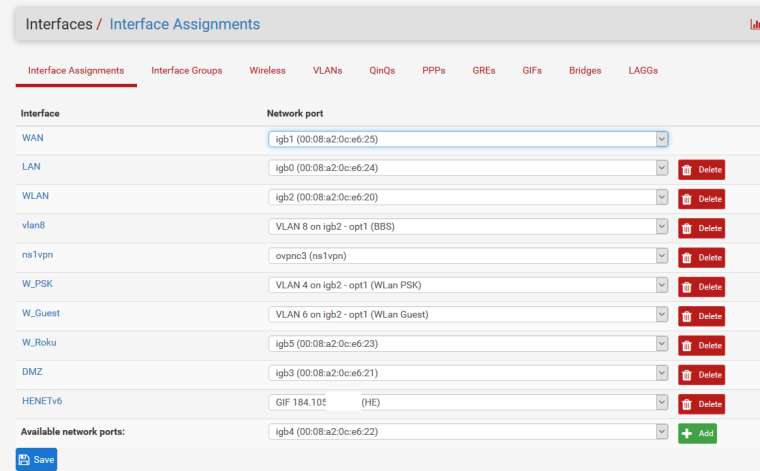
See my lan is attached is on igb0, I also have another network wlan that is on igb2 untagged, and then have VLANS on igb2 as well.
Here I changed its name from LAN to something else
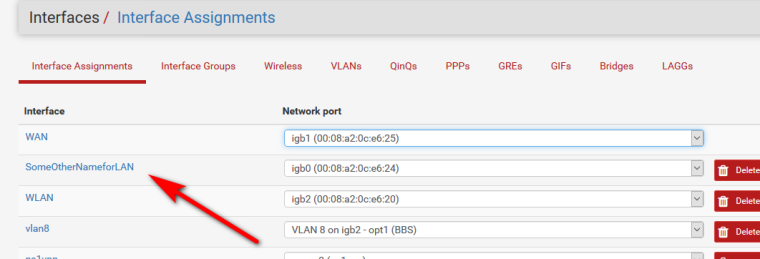
Lan is not really anything special..
Its just the NAME that pfsense gives to the first local side network. That is not a WAN connection, ie it does not have a gateway.
That interface is also the interface that pfsense would put the antilock out rules on - unless you disabled them.
-
I can get the actual interfaces screen shot tonight.
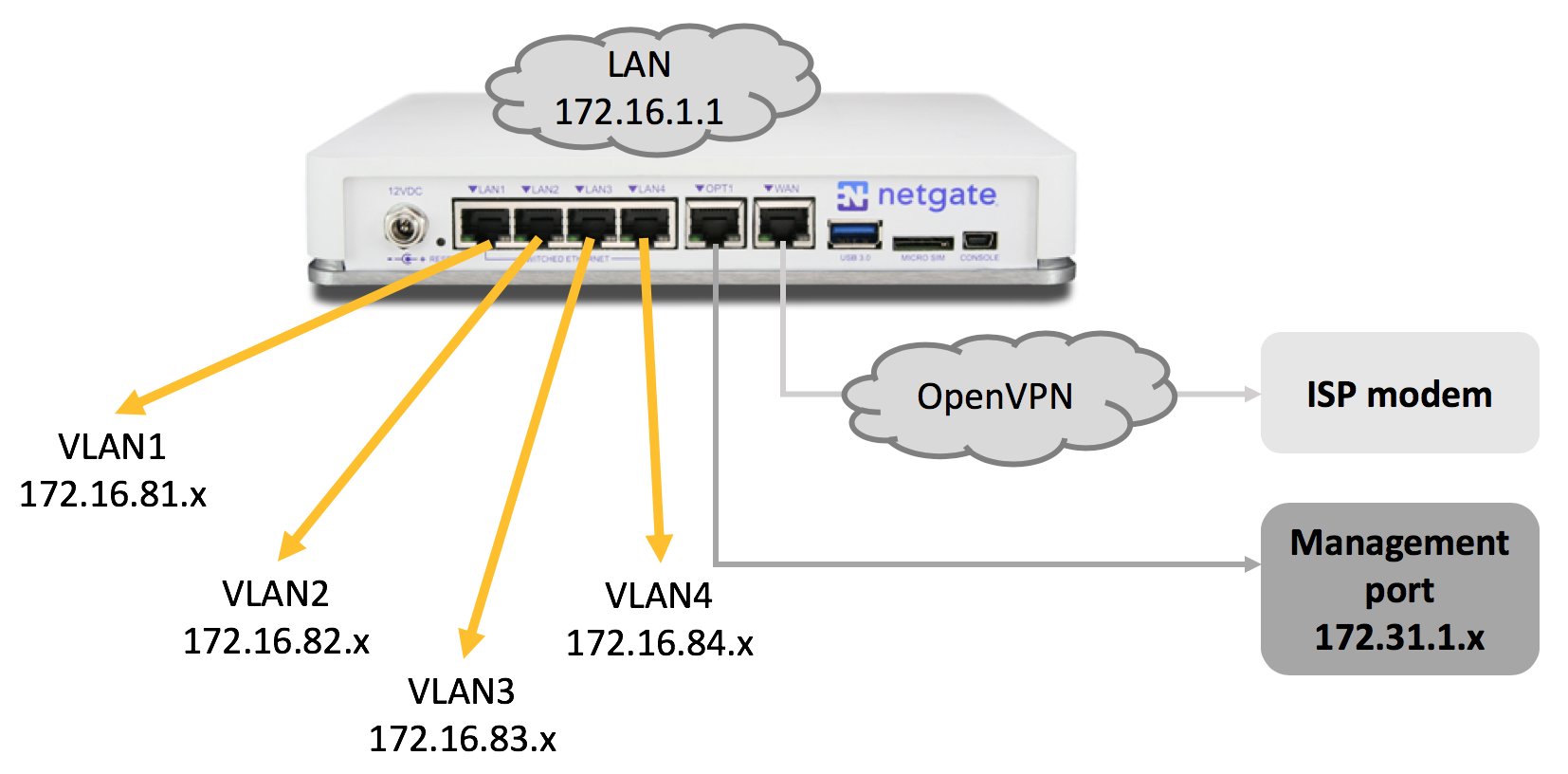
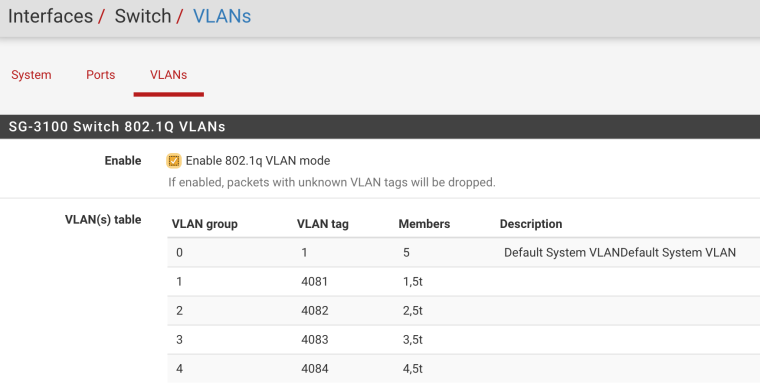
What I can recall and dig from the setup guide of the SG-3100, is the following:
WAN: mvneta2
OPT1: mvneta0
LAN : mvneta1
VLAN1: 4081 on mvneta1
VLAN2: 4082 on mvneta1
VLAN3: 4083 on mvneta1
VLAN4: 4084 on mvneta1For the VLANs, they're setup with 802.1Q and each of the VLAN1-4 segments has as members itself untagged and the LAN uplink tagged.
-
Again you can assign "LAN" to whatever you be it the actual interface or the switch ports, etc.
If you don't want to use the "LAN" network then don't.. Did you assign a IP to it?
-
I'll probably need to dig up some stuff from the unit tonight. I think I have it set to 172.16.1.1. What I don't understand well is in this topology how the tagged trunk fits into things. I probably don't understand enough to ask the right question(s)....
-
The tagged trunk is the connection from the "switch" to pfsense..
-
Right, that makes sense to me. From a firewall rule standpoint, does applying rules to that connection cover all the VLANs (similar to, but different from, a 'floating' rule)? Or in my case is the LAN something that basically I ignore and I just focus on each VLAN interface?
-
Much thanks for your patience trying to understand my ignorance and naivete.
Here's my interfaces tab:
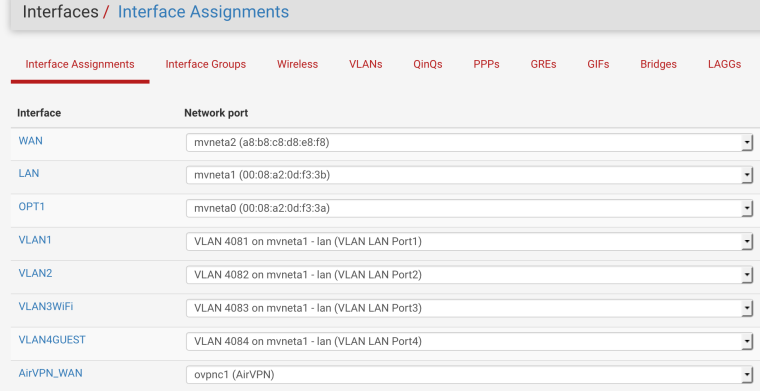
And my VLANS:
I presently have no firewall rules on the 'LAN' interface, given my topology, and things basically seem to work. I am just so novice at this (it's like moving from an automatic to a manual transmission, quite simple once you know what you'e doing, but hard when you don't) I'm hoping the experts can help me avoid doing something stupid.
From a management standpoint, my original gravitation toward floating rules was based on the idea of applying something in 1 place that affects many, since I have the VLAN segments. My goal with VLAN segments is to allow rigid partitioning of the network and get to a point I have private & guest WIFI access via AP's and that nothing can see anything else. I have no trust for IoT devices, so they end up on their own isolated segment.
And I want it all routing through VPN (including DNS and anything else) since my ISP is questionable at best. I pay for service, I am a customer, not a product whose privacy doesn't matter. (stepping off soap box)