Best ransomware detection application
-
Hi mates,
I would like to use pfsense as a valid intrusion detection system.
Which is the best package combination to do this?Squid+pfblocker+snort?
Thanks ;)
-
Generally speaking, best ransomware detection application is the human brain.
-Rico
-
@rico said in Best ransomware detection application:
Generally speaking, best ransomware detection application is the human brain.
AHAHAHAH Yep Rico you are right.
Generally the problems are between the chair and the keyboard, but my work is to prevent these kind of problems (and, be honest, if all the users may have an high skill like ours I would have to plant tomatoes for job ;) )
My users like to click everywhere....and I think the problem is not only mine.So I re-ask the same question
-
When all this ransomware stuff started some years ago we did two simple things:
- disable all Microsoft macro shit global by GPO
- ban all nasty e-mail attachments like .doc .docx .xls .xlsx .zip and so on.
Thats it, no problems.
-Rico
-
@pama said in Best ransomware detection application:
if all the users may have an high skill like ours I would have to plant tomatoes for job
There is a freaking HUGE difference between design a network sort of skills and not click on the email that says its from your boss and he loves you ;) hehehe
How hard is not to click the EXE that says it that invoice you weren't expecting, etc..
I don't know about you - but seems I will be retiring early since bill gates wants to give me 5 mil ;)
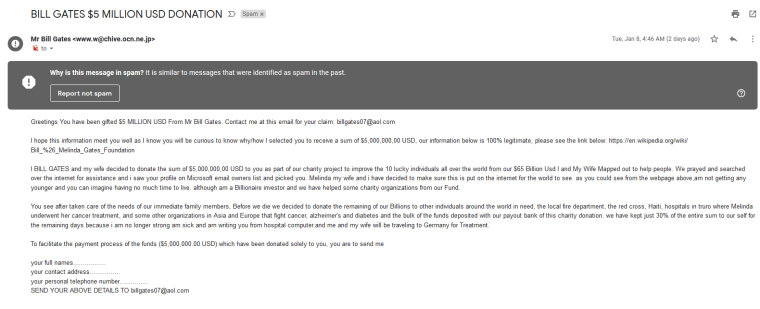
Damn google marking this as spam - almost missed out ;) heheheeh ROFL
-
@johnpoz said in Best ransomware detection application:
There is a freaking HUGE difference between design a network sort of skills and not click on the email that says its from your boss and he loves you ;) hehehe
How hard is not to click the EXE that says it that invoice you weren't expecting, etc..
I don't know about you - but seems I will be retiring early since bill gates wants to give me 5 mil ;)
Damn google marking this as spam - almost missed out ;) heheheeh ROFL
You are lucky! 5 mil from Bill Gates!!!
My users like to click on the delivery package links even if they didn't order anything
-
You can't defend against ransomware with a firewall, the infection starts inside of the LAN and so is already past the firewall. You could segment the LAN, but unless you put every PC in their own L2 it will always hit at least one of your LAN segments.
To have a chance at defending against it you have to work with your Users and the OS on the devices:
- Regularly educate your users on the current risks and how to handle email attachments/downloads.
- Lock down the user permissions on all the devices to the absolute minimum possible/required for them to do their work.
-
@grimson said in Best ransomware detection application:
put every PC in their own L2 it will always hit at least one of your LAN segments.
This is actually why its good idea to put enterprise type user machine on private vlans.. There is almost never a reason that enterprise pcs need to talk to their neighbor machines..
What is odd is you almost never see this sort of configuration.. But this could prevent/slow down many a corp type worm.. Say something like wannacry... Why does billy machine need to talk smb to susans machine in the next cube?
Firewall has zero to do with keeping your machines patched either ;)
Thinking they are going to stop these sorts of issues with some UTM that does DPI is just nuts.. Traffic doesn't even go across the UTM when devices in the same L2 talk to each other.
Regularly educate your users on the current risks and how to handle email attachments/downloads.
If I can train my wife to ask about odd emails, or anything asking for any sort of info.. Then anyone can be trained ;)
A fun thing to do is send out test emails to your users, track who clicks on them and then put them up on a SHAME wall ;) Sadly HR frowns upon the use of IT Shaming as a training tool ;) Even though it can be very effective!!
The worse is when you get the user that clearly knew something was not right with whatever it is, but wanted to see what it would do, or if the system would stop it, etc. etc. I think some of them try and get infected on purpose.. Since if they loose their machine for a while they don't have to do any work..
We had one customer where users would get infected, they would be notified to shut down their machine, etc. etc. And they wouldn't do it - help desk would have to contact network to shutdown their connectivity even when the help desk guy is there in their cube telling them to shutdown, we had an issue where there was physical altercation when the help desk guy tried to unplug the users machine because it was spewing out garbage..
-
@grimson said in Best ransomware detection application:
You can't defend against ransomware with a firewall, the infection starts inside of the LAN and so is already past the firewall. You could segment the LAN, but unless you put every PC in their own L2 it will always hit at least one of your LAN segments.
To have a chance at defending against it you have to work with your Users and the OS on the devices:
- Regularly educate your users on the current risks and how to handle email attachments/downloads.
- Lock down the user permissions on all the devices to the absolute minimum possible/required for them to do their work.
Yes, I know.
Have you ever tried to work with Chinese?
I had trained, explained and tried to update their PCs from Italy, but I am not there and the local IT is lack of knowledge.
So, I am asking at the PFSense forum IFPFsense can act as Ransomware detection (the client inside the LAN has to contact internet to begin the infection) with something like pfblocker and Snort.
I am not asking to train users, to segmentate the network and/or update the clients....Thanks,
Andrea -
@pama said in Best ransomware detection application:
the client inside the LAN has to contact internet to begin the infection
No it does not. It might try to contact a control server to get an updated encryption key (and if it fails it uses the default one) or to report a randomly created key, but it will encrypt the data no matter what. By the time you notice that activity on an IDS your data is already gone.
And to notice it your IDS must first get updated signatures. Which means that the maintainer of these signatures must first get their hands on the current iteration of ransomware and analyse it. If that iteration is specifically targeted at your company, and tailored for it, it's quite unlikely that the signature maintainers get it before it hits your devices.
A firewall based IDS can not protect you against ransomware, plain and simple.
-
@grimson
Let's talk about phising, with a masquerade link. The user has to click on it and download the malware.
In some database (snort or dns blocklist) that link, if old, has to be published and the application on the firewall has to deny that download.
Am I enough clear? -
Sounds more like the work of a proxy and not a IDS, or just plain ole dns protection..
Then you have new stuff like Modlishka making it more FUN ;)
IDS are great for detecting and preventing attacks against your stuff, but if your detecting shit outbound of your network.. Then the inside device has already been compromised.
-
@pama said in Best ransomware detection application:
In some database (snort or dns blocklist) that link, if old, has to be published and the application on the firewall has to deny that download.
Every AV, inlcuding Windows Defender, will protect against old malware. The real threat are the current iterations. Again, if you want to have a real chance at protecting your data you have to secure the OS on the actual devices and most importantly educate your users.
Your attempt will only create a false sense of security and with that increase the risk of someone doing something stupid.
-
@grimson said in Best ransomware detection application:
create a false sense of security
Yup this great point!! Thinking some IDS/IPS tools or DPI is going to protect you from "everything" is part of the problem.. While these tools are fantastic if used appropriately... They are only tiny parts in the overall security policy of the company.
Running such tools is also very labor intensive and can cause in some cases more problems then they are worth if not properly managed. If you think you can just enable some tool and that solves your problem, yeah wouldn't it be nice if it was actually that easy ;)
-
I think the best solution is to limit the damage ransomware can do. I'm using Veeam Endpoint Backup (free, BTW) to back up all machines to NAS. It can use a different set of credentials than the user, so ransomware (which runs with user's permissions) cannot scribble over the backups. Pretty economical on disk space, too (reverse-time delta).
So if somebody's PC gets ransomwared, I can boot from a USB, do a bare metal recovery. Takes maybe 40 minutes - and the user loses whatever they've done since the last backup (run nightly).
Also: easy to recover files deleted or changed up to the earliest backup.Either by me or the users themselves (users have RO access to the backup NAS).We haven't been hit, but I was been able to make sure this all works when a user's SSD failed. And I've taken to making a bare metal recovery when someone gets hit with a virus (can't otherwise be sure it's completely gone - and we're handling clients' private financial data).
I've looked at detecting / stopping ransomware, and, for what we'd lose it just doesn't seem to be worth the extra effort beyond educating users about it
-
@bobkoure
I had a very bad experience, and I want to fire the local IT.
I use Veeam B&R, and the backup over a NAS was crypted because someone gave the administrator password to the user. The tapes were never changed, so I think I have to take a plane every month to load tapes to the changer
That's why I say that is very difficult to train the users.... -
@pama I'm using Synology Diskstations as NASs. Backups go to a backups-only share.Access to that backup share is RO for everyone, including admin - but excepting Veeam backups. If I need to get in there in RW mode, I can connect as Veeam. Nobody knows the Veeam password, except me - and it's in the envelope on my desk labeled "Open in the event of my being run over by a beer truck". I learned about needing to do that by having to break into about a dozen machines managed by an IT guy who fell off a roof and died. Young guy who never thought to write that stuff down.
Those synology boxes have 'backup to AWS' as a built-in (and I have a rule in AWS that 'sweeps' everything into glacier - costs nothing to do that)BTW, why are you using tapes? Why not something like AWS Glacier? After this disaster, mgmt would probably be OK with spending the $ to Glacier (which is AFAIK, the cheapest 'cloud' storage). It would certainly be cheaper than plane tickets.
If you're not using Synology boxes, check out FastGlacier to push stuff up there. -
@bobkoure
Thanks for the suggestions....the problem is always have the best at the cheaper price.
I will for sure take a look at Amazon glacier!