Suricata fails to start after pfSense reboot
-
@kiekar said in Suricata fails to start after pfSense reboot:
I got the same errcode
[2.4.4-RELEASE][admin@host.mydomain.com]/root: suricata -T -c /usr/local/etc/suricata_26546_pppoe1/suricata.yaml 16/1/2019 -- 15:29:42 - <Info> - Running suricata under test mode 16/1/2019 -- 15:29:42 - <Error> - [ERRCODE: SC_ERR_FATAL(171)] - failed to open file: /usr/local/etc/suricata_26546_pppoe1/suricata.yaml: No such file or directory [2.4.4-RELEASE][admin@host.mydomain.com]/root:I will uninstall surcicata and re-install. Could i leave the checkbox to keep current settings?
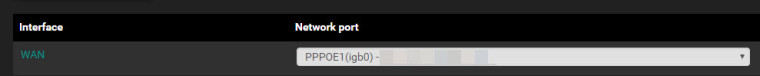
Not having a suricata.yaml file for the interface is very strange. Have you gone to the INTERFACE SETTINGS tab and clicked the Save button? Is that interface (pppoe1) the physical name of your WAN interface where you are running Suricata?
Is there plenty of free disk space? I would assume "yes", but this is a strange issue.
Never seen a case where the suricata.yaml for the interface was missing. That file tells the Suricata binary what to do and how to do it. No surprise it won't start with that file missing.
You can try a full remove and install operation. Just be sure you delete the package and then install it again. DO NOT just click the re-install icon!
-
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
I got the same errcode
[2.4.4-RELEASE][admin@host.mydomain.com]/root: suricata -T -c /usr/local/etc/suricata_26546_pppoe1/suricata.yaml 16/1/2019 -- 15:29:42 - <Info> - Running suricata under test mode 16/1/2019 -- 15:29:42 - <Error> - [ERRCODE: SC_ERR_FATAL(171)] - failed to open file: /usr/local/etc/suricata_26546_pppoe1/suricata.yaml: No such file or directory [2.4.4-RELEASE][admin@host.mydomain.com]/root:I will uninstall surcicata and re-install. Could i leave the checkbox to keep current settings?
Not having a suricata.yaml file for the interface is very strange. Have you gone to the INTERFACE SETTINGS tab and clicked the Save button? Is that interface (pppoe1) the physical name of your WAN interface where you are running Suricata?
Is there plenty of free disk space? I would assume "yes", but this is a strange issue.
Never seen a case where the suricata.yaml for the interface was missing. That file tells the Suricata binary what to do and how to do it. No surprise it won't start with that file missing.
You can try a full remove and install operation. Just be sure you delete the package and then install it again. DO NOT just click the re-install icon!
Yes, wan interface is setup correctly.
I'm going to uninstall suricata with my current settings intacked.
-
@kiekar said in Suricata fails to start after pfSense reboot:
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
I got the same errcode
[2.4.4-RELEASE][admin@host.mydomain.com]/root: suricata -T -c /usr/local/etc/suricata_26546_pppoe1/suricata.yaml 16/1/2019 -- 15:29:42 - <Info> - Running suricata under test mode 16/1/2019 -- 15:29:42 - <Error> - [ERRCODE: SC_ERR_FATAL(171)] - failed to open file: /usr/local/etc/suricata_26546_pppoe1/suricata.yaml: No such file or directory [2.4.4-RELEASE][admin@host.mydomain.com]/root:I will uninstall surcicata and re-install. Could i leave the checkbox to keep current settings?
Not having a suricata.yaml file for the interface is very strange. Have you gone to the INTERFACE SETTINGS tab and clicked the Save button? Is that interface (pppoe1) the physical name of your WAN interface where you are running Suricata?
Is there plenty of free disk space? I would assume "yes", but this is a strange issue.
Never seen a case where the suricata.yaml for the interface was missing. That file tells the Suricata binary what to do and how to do it. No surprise it won't start with that file missing.
You can try a full remove and install operation. Just be sure you delete the package and then install it again. DO NOT just click the re-install icon!
Yes, wan interface is setup correctly.
I'm going to uninstall suricata with my current settings intacked.
Oh! Something I just remembered and I did not notice earlier. Inline IPS Mode and a PPPoE connection will NOT work! You will have to switch to Legacy Mode blocking with a PPPoE connection. You will never get any alerts with PPPoE and Inline Mode. It is a limitation of FreeBSD and Netmap.
-
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
I got the same errcode
[2.4.4-RELEASE][admin@host.mydomain.com]/root: suricata -T -c /usr/local/etc/suricata_26546_pppoe1/suricata.yaml 16/1/2019 -- 15:29:42 - <Info> - Running suricata under test mode 16/1/2019 -- 15:29:42 - <Error> - [ERRCODE: SC_ERR_FATAL(171)] - failed to open file: /usr/local/etc/suricata_26546_pppoe1/suricata.yaml: No such file or directory [2.4.4-RELEASE][admin@host.mydomain.com]/root:I will uninstall surcicata and re-install. Could i leave the checkbox to keep current settings?
Not having a suricata.yaml file for the interface is very strange. Have you gone to the INTERFACE SETTINGS tab and clicked the Save button? Is that interface (pppoe1) the physical name of your WAN interface where you are running Suricata?
Is there plenty of free disk space? I would assume "yes", but this is a strange issue.
Never seen a case where the suricata.yaml for the interface was missing. That file tells the Suricata binary what to do and how to do it. No surprise it won't start with that file missing.
You can try a full remove and install operation. Just be sure you delete the package and then install it again. DO NOT just click the re-install icon!
Yes, wan interface is setup correctly.
I'm going to uninstall suricata with my current settings intacked.
Oh! Something I just remembered and I did not notice earlier. Inline IPS Mode and a PPPoE connection will NOT work! You will have to switch to Legacy Mode blocking with a PPPoE connection. You will never get any alerts with PPPoE and Inline Mode. It is a limitation of FreeBSD and Netmap.
Ok Thanks for all your help. I will try to move the pppoe authenication from the firewall to the vsdl modem
-
@kiekar said in Suricata fails to start after pfSense reboot:
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
I got the same errcode
[2.4.4-RELEASE][admin@host.mydomain.com]/root: suricata -T -c /usr/local/etc/suricata_26546_pppoe1/suricata.yaml 16/1/2019 -- 15:29:42 - <Info> - Running suricata under test mode 16/1/2019 -- 15:29:42 - <Error> - [ERRCODE: SC_ERR_FATAL(171)] - failed to open file: /usr/local/etc/suricata_26546_pppoe1/suricata.yaml: No such file or directory [2.4.4-RELEASE][admin@host.mydomain.com]/root:I will uninstall surcicata and re-install. Could i leave the checkbox to keep current settings?
Not having a suricata.yaml file for the interface is very strange. Have you gone to the INTERFACE SETTINGS tab and clicked the Save button? Is that interface (pppoe1) the physical name of your WAN interface where you are running Suricata?
Is there plenty of free disk space? I would assume "yes", but this is a strange issue.
Never seen a case where the suricata.yaml for the interface was missing. That file tells the Suricata binary what to do and how to do it. No surprise it won't start with that file missing.
You can try a full remove and install operation. Just be sure you delete the package and then install it again. DO NOT just click the re-install icon!
Yes, wan interface is setup correctly.
I'm going to uninstall suricata with my current settings intacked.
Oh! Something I just remembered and I did not notice earlier. Inline IPS Mode and a PPPoE connection will NOT work! You will have to switch to Legacy Mode blocking with a PPPoE connection. You will never get any alerts with PPPoE and Inline Mode. It is a limitation of FreeBSD and Netmap.
Ok Thanks for all your help. I will try to move the pppoe authenication from the firewall to the vsdl modem
If you want to use Inline IPS Mode, you need to have either a static WAN IP or DHCP on the WAN. PPPoE won't work. A PPPoE connection totally bypasses the Netmap pipe set up by Inline IPS Mode.
-
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar said in Suricata fails to start after pfSense reboot:
I got the same errcode
[2.4.4-RELEASE][admin@host.mydomain.com]/root: suricata -T -c /usr/local/etc/suricata_26546_pppoe1/suricata.yaml 16/1/2019 -- 15:29:42 - <Info> - Running suricata under test mode 16/1/2019 -- 15:29:42 - <Error> - [ERRCODE: SC_ERR_FATAL(171)] - failed to open file: /usr/local/etc/suricata_26546_pppoe1/suricata.yaml: No such file or directory [2.4.4-RELEASE][admin@host.mydomain.com]/root:I will uninstall surcicata and re-install. Could i leave the checkbox to keep current settings?
Not having a suricata.yaml file for the interface is very strange. Have you gone to the INTERFACE SETTINGS tab and clicked the Save button? Is that interface (pppoe1) the physical name of your WAN interface where you are running Suricata?
Is there plenty of free disk space? I would assume "yes", but this is a strange issue.
Never seen a case where the suricata.yaml for the interface was missing. That file tells the Suricata binary what to do and how to do it. No surprise it won't start with that file missing.
You can try a full remove and install operation. Just be sure you delete the package and then install it again. DO NOT just click the re-install icon!
Yes, wan interface is setup correctly.
I'm going to uninstall suricata with my current settings intacked.
Oh! Something I just remembered and I did not notice earlier. Inline IPS Mode and a PPPoE connection will NOT work! You will have to switch to Legacy Mode blocking with a PPPoE connection. You will never get any alerts with PPPoE and Inline Mode. It is a limitation of FreeBSD and Netmap.
Ok Thanks for all your help. I will try to move the pppoe authenication from the firewall to the vsdl modem
If you want to use Inline IPS Mode, you need to have either a static WAN IP or DHCP on the WAN. PPPoE won't work. A PPPoE connection totally bypasses the Netmap pipe set up by Inline IPS Mode.
Ok Thanks, I'm going to have to do some reading how to setup using static IP's or DHCP. I have a block of IP's from my provider and I have been running my current setup for several years now.
-
@kiekar
Running the Legacy Blocking Mode is fine, and is really just about the same in terms of security. True there may be a leaked packet or two, but in most situations that is of no consequence. You can use all of the SID MGMT features and "alert" and "drop" actions in Legacy Mode. Just check the box on the INTERFACE SETTINGS tab that enables the "block-on-drops-only" option. That will mimic Inline IPS Mode whereby only rules with DROP as the action will actually block traffic. Rules with ALERT as the action will only generate alerts but no blocks.And finally, if you are using NAT on pfSense, then I recommend putting Suricata on your LAN interface so that the internal host addresses you see will reflect reality. Otherwise, with NAT, all internal hosts seen on the WAN side will have the WAN external IP and you won't be able to tell which internal host generated the alert. This is assuming you use NAT. If you don't use NAT on the firewall, then you can place Suricata either on the WAN or LAN without the IP masking issue.
-
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar
Running the Legacy Blocking Mode is fine, and is really just about the same in terms of security. True there may be a leaked packet or two, but in most situations that is of no consequence. You can use all of the SID MGMT features and "alert" and "drop" actions in Legacy Mode. Just check the box on the INTERFACE SETTINGS tab that enables the "block-on-drops-only" option. That will mimic Inline IPS Mode whereby only rules with DROP as the action will actually block traffic. Rules with ALERT as the action will only generate alerts but no blocks.And finally, if you are using NAT on pfSense, then I recommend putting Suricata on your LAN interface so that the internal host addresses you see will reflect reality. Otherwise, with NAT, all internal hosts seen on the WAN side will have the WAN external IP and you won't be able to tell which internal host generated the alert. This is assuming you use NAT. If you don't use NAT on the firewall, then you can place Suricata either on the WAN or LAN without the IP masking issue.
I've seen some brief topics on SID MGMT, but I have to say I'm a little lost on the function of it. Could you be so kind an point me in the right direction on some good reading on the SID MGMT. Your help would be much appreciated.
Thanks,
-
@kiekar
Start with these two Sticky Posts here in the IDS/IPS sub-forum.How Automatic SID Management and User Rule Overrides Work in Snort and Suricata
About the New Block-on-Drops-Only Option in SuricataTo get some examples of SID MGMT, go to the SID MGMT tab and click the "enable" checkbox. That will populate the page with content. Open any of the example files and you will find comments inside each that explain the options. The internal syntax is copied from PulledPork, so you can Google the PulledPork utility used with Snort to get some examples of what you can do with the enablesid.conf, disablesid.conf and dropsid.conf files.
-
@bmeeks said in Suricata fails to start after pfSense reboot:
@kiekar
Start with these two Sticky Posts here in the IDS/IPS sub-forum.How Automatic SID Management and User Rule Overrides Work in Snort and Suricata
About the New Block-on-Drops-Only Option in SuricataTo get some examples of SID MGMT, go to the SID MGMT tab and click the "enable" checkbox. That will populate the page with content. Open any of the example files and you will find comments inside each that explain the options. The internal syntax is copied from PulledPork, so you can Google the PulledPork utility used with Snort to get some examples of what you can do with the enablesid.conf, disablesid.conf and dropsid.conf files.
Great, thanks so much. You've been a great help