Noob Needs Heeeeelllllllp
-
Hi all, thanks in advance if you can answer these for me. I have spent time reading and watching videos, configuring and trying different things but I am at a loss for yes/no type answers to basic things. For questions 1-4 assume I am sitting in my house and just surfing the internet, watching movies, playing games and initiating everything from my Lan to the Wan (internet).
-
After pfSense install and WAN/LAN setup and enabling the firewall with default stuff (a few items clicked), no additional rules created. Is pfSense protecting me or is it wide open and I am getting bombarded by malicious attacks?
-
From everything I have read pfSense (default install) blocks all incoming Wan traffic unless it was an original request from the Lan, is this correct?
-
If answers are yes, why would i need to run Suricata/Snort? Are they just for additional ability to see what is trying to access my Lan from the Wan? Or to see what is on my Lan requesting stuff from the Wan (internet)?
-
pfblockerng, same questions here if everything is blocked unless it originates from the Lan do I need to extra block China/Russia and all those lists and stuff?
Now for questions 5-6 assume I am venturing out into the world and want to access my Lan and all my IOT devices, server, home security, hvac, lights, cameras, etc from the world as I roam around.
-
Is this when I need all that other stuff so that I can make rules so that I can access these things with the least amount of danger of malicious attacks?
-
Wouldn't just a VPN suffice for this and that is all I need?
As I think you can see I am having trouble figuring out when enough is enough. I read a bunch of posts and articles that say the simple approach is the best, but I have no idea anymore what simple is after reading and watching everything out there on pfSense.
For instance I have pfSense running in Proxmox really easily on an old Xeon E5620 on 4 threads with 8G of ram and it is really happy on my 750/750 internet connection. I just use traffic shaping and the limiter to 725/725 and achieve 0 lost packets while running multiple speedtests at the same time and the cpu goes to 16%. But I turn on Suricata and enable all the stuff people talk about in the articles and videos and my speedtests drop to 350/350 and my cpu is at 80%. So if I need all this stuff I am going to have to build a beast system!
I can understand if I was an organization running web servers and stuff I would want to see if I am getting hammered by malicious IP's and I would want the ability to block them etc, but is there really any advantage for me, a home user with my stuff listed above? Everything is already getting blocked. Or would I just enable these things so I could learn and see what is going on so if I ever wanted, I could use them if the need arises?
Thanks,
Snorf
-
-
@snorf said in Noob Needs Heeeeelllllllp:
-
After pfSense install and WAN/LAN setup and enabling the firewall with default stuff (a few items clicked), no additional rules created. Is pfSense protecting me or is it wide open and I am getting bombarded by malicious attacks?
-
From everything I have read pfSense (default install) blocks all incoming Wan traffic unless it was an original request from the Lan, is this correct?
-
If answers are yes, why would i need to run Suricata/Snort? Are they just for additional ability to see what is trying to access my Lan from the Wan? Or to see what is on my Lan requesting stuff from the Wan (internet)?
-
pfblockerng, same questions here if everything is blocked unless it originates from the Lan do I need to extra block China/Russia and all those lists and stuff?
-
Is this when I need all that other stuff so that I can make rules so that I can access these things with the least amount of danger of malicious attacks?
-
Wouldn't just a VPN suffice for this and that is all I need?
1.) By default, all inbound connections on WAN are blocked. Youre being protected by this.
2.) That is correct. The LAN interface has a default rule to allow LAN out to the internet, unrestricted.
3.) Suricata/Snort are intrusion detection/prevention systems. This allows you to look into what is going on within the network, and if something matches a rule you have defined (or if it is defined by default) it takes actions according to what you set (block for instance). There are a few reasons why you might want to but the most common reason would be:
A.) You host services and allow inbound access to these services, across your WAN. You for example, might want to know if someone is attempting to run a known attack against your service and block it.
4.) pfBlocker_NG can be used for inbound AND outbound connections. If you had a port open on WAN and wanted to restrict access to it by country, you could use pfBlocker_NG to do this. Likewise, if you wanted to stop anything inside your network from accessing IPs located in china/russia, you could also do that as well. To answer your question: No, pfblocker does not add any extra security to filtering your WAN if you are not opening WAN ports, and are not filtering on LAN either.
5.) Yes, if you have open ports on your WAN. Running pfblocker and snort or suricata would help improve security for this instance.
6.) Yes, yes, and YES. A VPN setup would be highly recommended over port forwarding and running snort/suricata. You can also run pfblocker and deny connections from outside of your country that are headed for your VPN if you wanted. This isn't required, but it would help improve the security (worth noting that this isnt a magic 'unhackable' solution. this only helps improve security, it doesnt make it infallible)I'd also like to mention that Snort/Suricata are both great solutions, but they are not 'set and forget'. IDS/IPS requires some serious tuning if you plan on implementing it, and simply turning it on isnt enough.
Creating a VPN, and access your devices is typically the simpler and recommended option in this instance.
-
-
@snorf said in Noob Needs Heeeeelllllllp:
...and enable all the stuff people talk about in the articles and videos...
Exactly what is that because that's a dramatic reduction in speed?
I have run Suricata at 1Gbps with basic rules on far lesser hardware. As you say as a home user you may decide you don't want/need it or can run with basic rules at least to start off with.
Are you running on both interfaces? That's not necessary in most environments IMO.Steve
-
Big thank-you for the responses!
This confirms a lot about what I thought was happening. Hopefully you can answer a couple of more questions that are still bugging me.
As stated in my original post I have a 750/750 fiber connection. It terminates into my ISP box with an SFP Transceiver. I have successfully managed to get rid of their box and stick the SFP transceiver into my pfSense build and pull dhcp ipv4 and ipv6 ip's. So I can just keep their box for troubleshooting, or using while upgrading my equipment etc.
-
Comparing my ISP box and pfSense as a firewall only (no additional packages or rules in pfSense), my ISP box has the typical Off, Nat Only, Low, Medium, High settings for firewall. I would usually set it to medium and just forget about it. If we were to compare the ISP box and the default pfSense firewall as described, how much more secure is my pfSense build or is it more secure?
-
Which option is the best between these. I have a NordVPN subscription. When I travel I use it when doing stuff that I want to stay private (banking/etc). Lets say I am travelling to Asia and I want to access my home network in North America. Would it be better to hook up to a local Asia NordVPN server and then access my pfSense enabled VPN, or would it be just as secure to just access my pfSense enabled VPN? I have not setup a VPN on pfSense but I am sure when connected to it from anywhere in the world I could use my home internet connection or I could set my device to use the local (Asia) internet connection while using the VPN to my home Lan. What is best practice to be secure, what are the risks and are they worth worrying about?
Thanks again!
Snorf
-
-
It's hard to compare high-medium-low with pfSense. pfSense blocks all incoming connections by default. On WAN that means all unsolicited traffic from the internet. On the LAN a rule is provided to allow LAN clients to reach external hosts by default. That is only on LAN, if you add other interfaces you need to allow any traffic you need.
I'm sure your ISP router will employ IP chains or IP tables at it's core. Without knowing what those are actually set to when you choose 'medium' it's hard to say.If you use our own VPN directly then where ever you are can see the remote IP you are connecting to and your ISP can see the IP you're connecting from. They can't see what's inside the VPN of course. And you can choose the port and protocol you use so it's not obviously a VPN at all. Or even do this:
https://docs.netgate.com/pfsense/en/latest/vpn/openvpn/sharing-a-port-between-openvpn-and-a-web-server.html
Or go further like OpenVPN over DNS etc. You control both end points so can do whatever.However if you use a commercial VPN both ends see only the connection to the VPN provider so you don't reveal the end points. But commercial VPNs are often used for malicious activity and their public IPs get blacklists etc. The provider themselves can see the traffic inside it also.
Personally I use a combination depending where I am. Either direct to my home pfSense or a pfSense instance hosted in the cloud.
Steve
-
@snorf said in Noob Needs Heeeeelllllllp:
Low, Medium, High settings for firewall
This is NONSENSE term... Mean NOTHING in relation to a firewall... low med high WHAT?
Do they list what these settings actually do?
-
Much appreciated on the responses again. It is slowly sinking in.
I am thinking of just having 2 interfaces, one for Wan and 1 for Lan. The Wan will be a 1G SFP connection while the Lan will be a 10G SFP+ connection. I am thinking of having a few vlans, are vlans treated like additional interfaces?
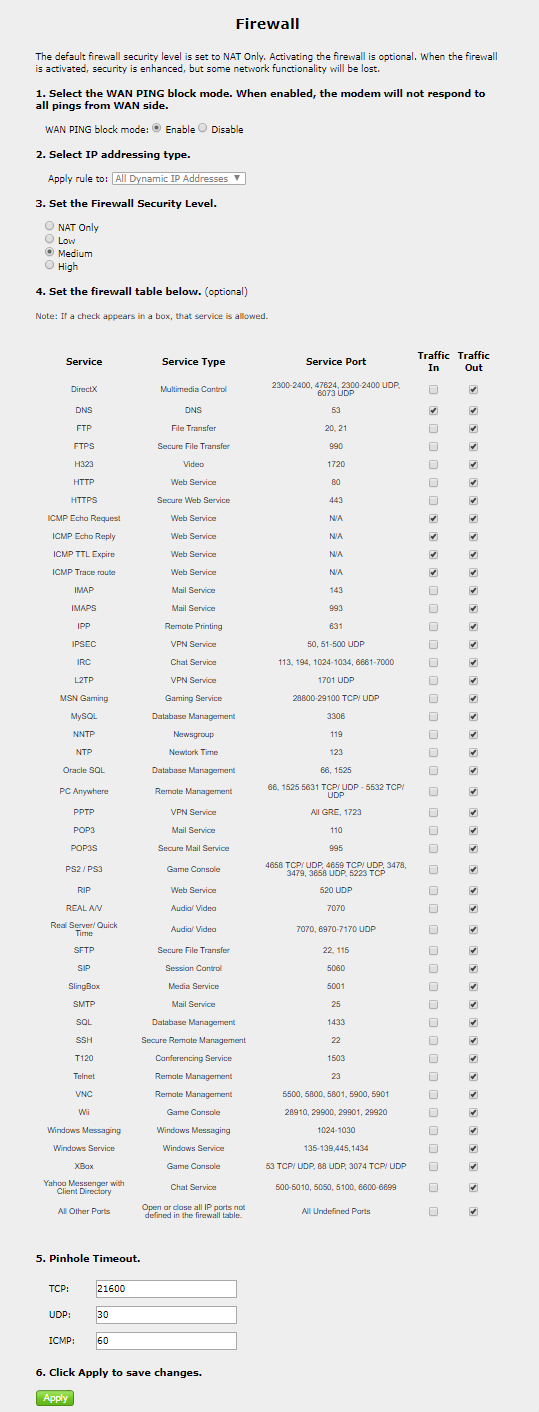
In regards to the Low, Medium, High, yes I understand how subjective this can be. However, linksys, netgear, tplink, asus, routers I have used employ this type of click and set firewall as does every ISP box that I have ever had. Below is a snapshot of medium settings. Nat Only allows only pinhole timeout settings. Low checks all the boxes. Medium is as shown below. High is the same as medium from what I can tell. How would this compare?
Thanks again,,
Snorf
-
@snorf said in Noob Needs Heeeeelllllllp:
as does every ISP box that I have ever had
And its ALL NONSENSE!! And SAD would be the other term I would use to describe any company that would try and use such term to describe firewall settings..
It means NOTHING!!!
So when you set these levels it changes but "shows you" the rules that it does?
In what freaking scenario would you need inbound 53??? Are you hosting dns? That is their med setting?
Curious to see the changes between low, med and high if that page changes the settings per what you select.
-
I am glad that you edited and added to your post I was starting to think your name should be salty johnpoz :).
I am surprised you have never seen this before. As I stated in my post this is typical of every consumer grade device that I have ever owned and configured, and all the ISP devices that I have ever used for ADSL/Cable/ and now Fiber. There have been a bunch since 1998 until now.
I did state the results from the different settings above in my post. I just posted the medium settings. I was wondering why I would need 53 open (not hosting anything) and the ICMP as well, but I am no expert.
Yes when I select the different settings nat only, low, medium, high, it changes the allowable settings and checked boxes as referenced above.
Thanks for everyone's help. I will keep reading and changing configurations until I feel confident that I can put my test pfSense box into full time operation, with vlans, dhcp, firewall, vpn, etc.
As a take away I am glad that from this discussion it seems confirmed that the default configuration of the pfSense firewall is better than my ISP box on it's high.
Thanks!
Snorf