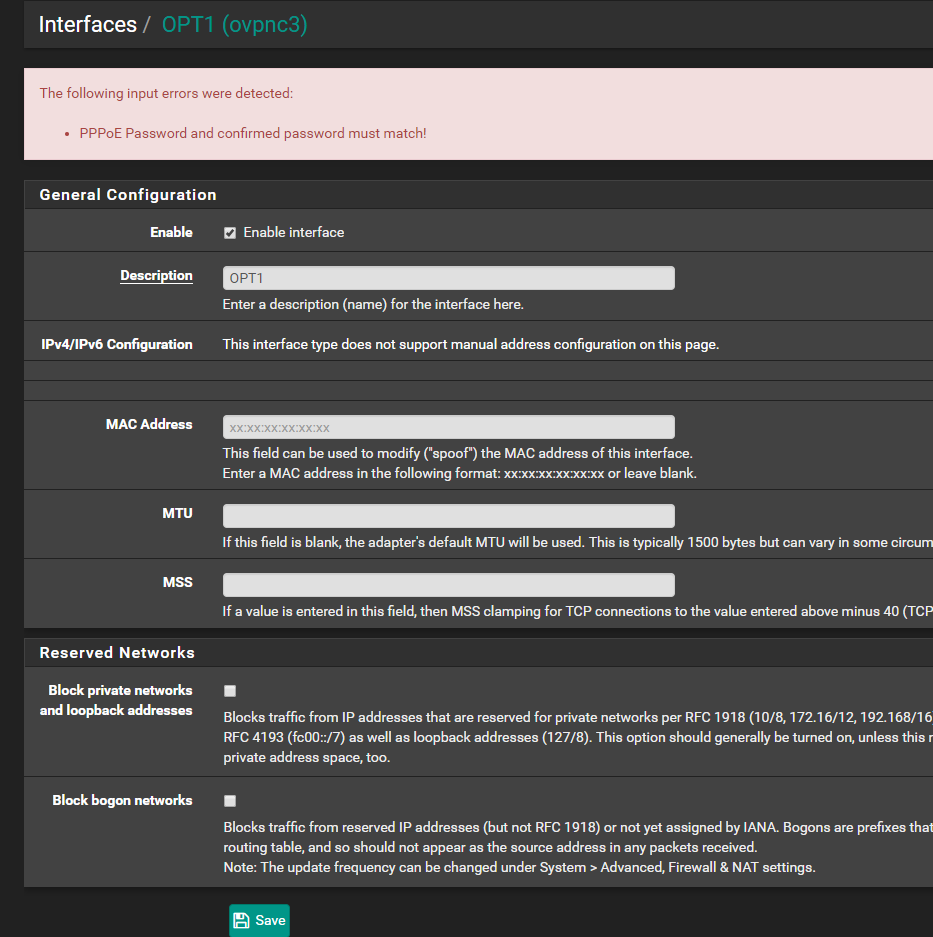
Cannot save Interface settings (PPPoE Password and confirmed password must match)
-
Be sure there are no rules that will pass it on the OpenVPN tab as they are applied first and will not add the reply-to tag.
Also make sure to clear any open states between tests as it may not be using the new rules otherwise.
Steve
-
@stephenw10
Ahh! Open states! That one i did forgot! Thanks! will test otherwise i will create a thread about it.
OpenVPN tab is used for another VPN tunnel though. On that one i have specified 2 remote (internal) networks that traffic will be routed too. That one has a "allow all" rule also. -
Yeah, you can't have an 'allow all' style open rule on the OpenVPN tab. If you have unassigned other OpenVPN instances just make sure to specify source subnets there so it doen't match traffic that needs to be passed on the assigned interface tab.
Steve
-
Ohhh.. i had to read your comment several times to understand it.. So if i have 2 OpenVPN tunnels the openvpn tab will match traffic for both tunnels even if one openvpn tunnel is assigned to an interface (VPN)?
I also noticed i had a allow all on the VPN tab, and removed that now.
So i have 2 OpenVPN tunnels.
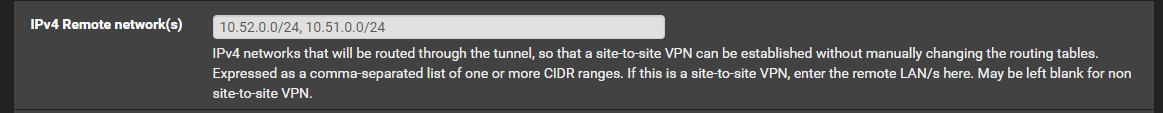
1 tunnel goes to a LAB environment at my work (Network there is 10.52.0.0 and 10.51.0.0)
1 tunnel goes to "internet" via a VPN provider.. This tunnel is assigned an interface called VPN.Are you saying the "internet" VPN tunnel will also use rules on the "OpenVPN" tab even if i assigned it an interface (VPN) ?
My OpenVPN tunnel to the LAB has this settings:
-
@Taz79 said in Cannot save Interface settings (PPPoE Password and confirmed password must match):
Are you saying the "internet" VPN tunnel will also use rules on the "OpenVPN" tab even if i assigned it an interface (VPN) ?
https://docs.netgate.com/pfsense/en/latest/vpn/openvpn/openvpn-traffic-filtering.html
-
@Grimson
ohhhhhhhh :)I like how you instead of typing an answer paste links ;) I will try it by removing all the rules in the OpenVPN tab..
-
@Taz79 said in Cannot save Interface settings (PPPoE Password and confirmed password must match):
I like how you instead of typing an answer paste links ;)
Why should I write things again that are already written in the documentation. That would be wasted time.
-
WOHO! It's working now! ..
So what was happening if i understand this correctly was that incoming traffic from my "internet" VPN was matched by the OpenVPN rule.. So the forwarded port from my internet VPN, where does that get sent if it encounter an "allow all" rule? Since its coming from the internet it would not know where to go?@stephenw10 where do i send the beer keg? :D Give me your BTC address :) :)
I have been over the rules, port forwards and LAN rules over and over and could for my life not understand how it could not work... lol ... -
@Grimson must thank you also for the link ;)
-
Yes, rules on the OpenVPN tab get applied to all incoming traffic coming over OpenVPN and they get applied before and specific rules for assigned OpenVPN interfaces. The behaviour is the same as interface groups and the interfaces in those groups but most people never use interface groups so never hit that.

Traffic coming on on the port forward was hitting the allow all rule on the OpenVPN tab and would have been correctly forwarded to the target. But because it does not get tagged 'reply-to' the replies from the target just go back out the system default route, usually the WAN, so the connection fails.
Steve
-
@stephenw10
Ok and that was exactly what i observed :) Thanks again!