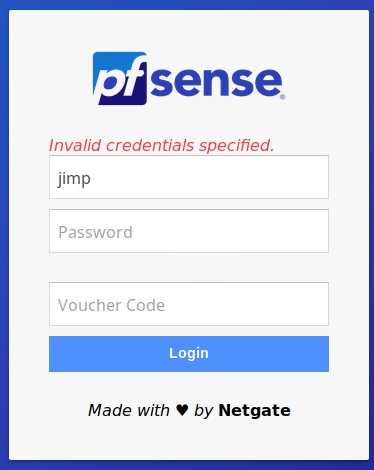
Captive Portal with AD - LDAP authenticates without a password !!,
-
Ok, then I don't understand.
If you have a users like 12345678 and a password, then users can't login without password that belongs to that user.
Are you saying that "12345678" is enough to have access ? -
Duplicate the "log in with no password" behavior with the default login page.
-
@gertjan yes, 12345678 is enough to have access, or 12345678+ password... both will work..
-
Jan 9 10:27:46 logportalauth 20913 Zone: wifitest - ACCEPT: olakara, 00:1f:f3:be:3c:xx, 192.168.11.102
-
I can't replicate the problem here. Set to check against LDAP, I get a login failure if I do not provide a password.
-
@jimp for me this works only with local database, LDAP still allow access without password
-
Then it must be your AD server returning a successful auth message. The LDAP client on pfSense is working properly as far as I can tell.
Run a packet capture of the LDAP exchange and run it through Wireshark, see what the AD server is returning to you.
-
@jimp said in Captive Portal with AD - LDAP authenticates without a password !!,:
see what the AD server
Probably set up as a " Yes-Ok-Proceed" server ...
Btw : AD Server log should tel you what happens.
-
Hello guys. All right?
Until I found a definitive solution, I made an adjustment in the /var/etc/captiveportal_wifi_myportal.html file to not continue if the password field is empty.
Before
<input type = "password" name = "auth_pass" placeholder = "Password" id = "auth_pass">After
<input type = "password" name = "auth_pass" placeholder = "Password" id = "auth_pass" required>That's it for now.
Thank you.
-
Hi.
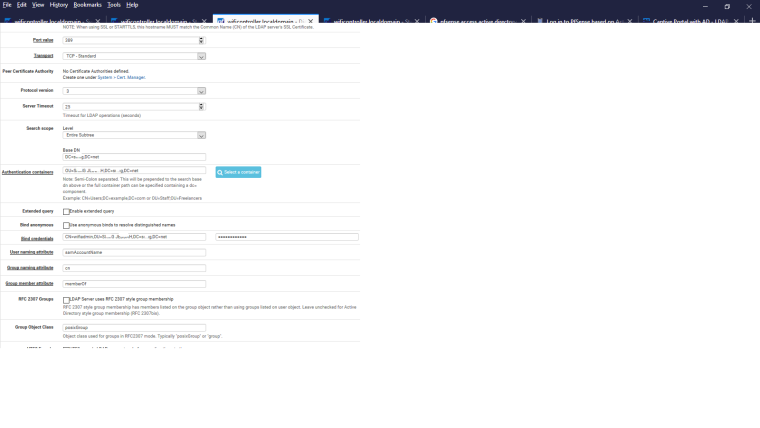
I have 3 firewall PfSense 2.4.4-RELEASE-p2 with a LDAP Authentication Servers (Windows Server 2008 R2 Forest) and i can confirm the same behavior reported by vicentezago.
Captive Portal accept authentication with a blank password (to be correct, the authentication is successful with the blank password only if the user is in the required AD Groups filtered by an extended query set in the ldap authentication server).
The strange things is that the "Authentication Tool" in Diagnostic Menu don't accept the blank password.For now I have edited the CP page as vcentezago.
I found a post in the OPNSense Forum that say that the bug is resolved with the 741082208 patch. I post the link.
https://forum.opnsense.org/index.php?topic=4605.0
Is it possible to implement same patch in PfSense?
-
Their code just prevents attempting to login with a blank password. While OK, that seems like a bad workaround. If your LDAP server is allowing someone to login with a blank password, you should fix the server instead.
-
Ok, but I don't understand where is the problem in my Windows server.
All users that I tested have a NOT blank password in Active Directory (Windows client PCs and the Authentication test in Diagnostic confirm this because return error if I try to authenticate with blank password ("Simple! It is the wrong password! :-))).
Why CP accept this username/password_blank pairing?Thanks
-
CP is not deciding to pass it with a blank password. It passes the authentication request off to your AD server. CP is only accepting it because AD returns a response that says the authentication was successful.
You need to figure out why that is and change the server so it doesn't happen. Anonymous binds are one potential source of problems here, but it's definitely something on your AD server that needs fixed.
The problem is that even if CP or pfSense in general is patched to stop this, that does nothing to prevent other services that also authenticate against your AD structure from also performing the same kind of binds and succeeding without a password. The problem needs solved at the source, you can't patch away this kind of security problem.
-
Thank You.
You give me a great hand to direct me in the right way.
I think that the problem is that the Base DN or the Search Base DN (I will try) are set as the rootDSE of the domain for which anonymous binds should be allowed by design.
Thank You very much -
@dimoz
Hi dimoz
I have that exact same issue.
Did it fix something to change the search base OU? -
@brinch, I've folloved the adjustment in the /var/etc/captiveportal_wifi_myportal.html proposed by @vicentezago.
For now, It solved (or bypassed ;-) ) the problem -
@dimoz
Thanks, i did the same trick.
As we dont use blank password on our domain it's fine -
@brinch I think it's too late now...but could you try to make a packet capture on the interface where your AD is, when you are authenticating with an empty password? then could you give me the packet capture by private message ?
I am very surprised by this kind of LDAP bug. I would like to check if it entirely related to your AD configuration or is pfsense part of the issue
(Warning / big Disclaimer : this packet capture will contain username/password of the account used in pfSense for binding to the AD, and the username that you are trying to login with on the captive portal. Depending on how critical this data is, you could change passwords or use temporary usernames)
-
@free4 Ok i send you the capture file
-
Well, I have some news,
I could analyze the pcap @brinch sent me. I can confirm that the problem comes from his Active Directory server which successfully bind when user provides an empty password.
I did some research, and apparently it seems to be a microsoft "feature" called unauthenticated bind : https://blog.lithnet.io/2017/01/ad-lds-and-ldap-unauthenticated-binds.html
Unlike anonymous bind, unauthenticated binds are enabled by default in Microsft Active directory.
It is also apparently impossible to disable unauthenticated binds on Microsoft AD : https://serverfault.com/questions/947428/how-to-disable-unauthenticated-binds-in-active-directory2016
I wasn't aware of this controversy. @jimp perhaps we should add an option for forbidding unauthenticated binds?