Captive Portal with AD - LDAP authenticates without a password !!,
-
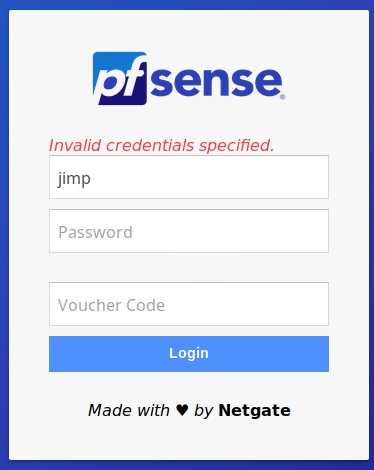
I can't replicate the problem here. Set to check against LDAP, I get a login failure if I do not provide a password.
-
@jimp for me this works only with local database, LDAP still allow access without password
-
Then it must be your AD server returning a successful auth message. The LDAP client on pfSense is working properly as far as I can tell.
Run a packet capture of the LDAP exchange and run it through Wireshark, see what the AD server is returning to you.
-
@jimp said in Captive Portal with AD - LDAP authenticates without a password !!,:
see what the AD server
Probably set up as a " Yes-Ok-Proceed" server ...
Btw : AD Server log should tel you what happens.
-
Hello guys. All right?
Until I found a definitive solution, I made an adjustment in the /var/etc/captiveportal_wifi_myportal.html file to not continue if the password field is empty.
Before
<input type = "password" name = "auth_pass" placeholder = "Password" id = "auth_pass">After
<input type = "password" name = "auth_pass" placeholder = "Password" id = "auth_pass" required>That's it for now.
Thank you.
-
Hi.
I have 3 firewall PfSense 2.4.4-RELEASE-p2 with a LDAP Authentication Servers (Windows Server 2008 R2 Forest) and i can confirm the same behavior reported by vicentezago.
Captive Portal accept authentication with a blank password (to be correct, the authentication is successful with the blank password only if the user is in the required AD Groups filtered by an extended query set in the ldap authentication server).
The strange things is that the "Authentication Tool" in Diagnostic Menu don't accept the blank password.For now I have edited the CP page as vcentezago.
I found a post in the OPNSense Forum that say that the bug is resolved with the 741082208 patch. I post the link.
https://forum.opnsense.org/index.php?topic=4605.0
Is it possible to implement same patch in PfSense?
-
Their code just prevents attempting to login with a blank password. While OK, that seems like a bad workaround. If your LDAP server is allowing someone to login with a blank password, you should fix the server instead.
-
Ok, but I don't understand where is the problem in my Windows server.
All users that I tested have a NOT blank password in Active Directory (Windows client PCs and the Authentication test in Diagnostic confirm this because return error if I try to authenticate with blank password ("Simple! It is the wrong password! :-))).
Why CP accept this username/password_blank pairing?Thanks
-
CP is not deciding to pass it with a blank password. It passes the authentication request off to your AD server. CP is only accepting it because AD returns a response that says the authentication was successful.
You need to figure out why that is and change the server so it doesn't happen. Anonymous binds are one potential source of problems here, but it's definitely something on your AD server that needs fixed.
The problem is that even if CP or pfSense in general is patched to stop this, that does nothing to prevent other services that also authenticate against your AD structure from also performing the same kind of binds and succeeding without a password. The problem needs solved at the source, you can't patch away this kind of security problem.
-
Thank You.
You give me a great hand to direct me in the right way.
I think that the problem is that the Base DN or the Search Base DN (I will try) are set as the rootDSE of the domain for which anonymous binds should be allowed by design.
Thank You very much -
@dimoz
Hi dimoz
I have that exact same issue.
Did it fix something to change the search base OU? -
@brinch, I've folloved the adjustment in the /var/etc/captiveportal_wifi_myportal.html proposed by @vicentezago.
For now, It solved (or bypassed ;-) ) the problem -
@dimoz
Thanks, i did the same trick.
As we dont use blank password on our domain it's fine -
@brinch I think it's too late now...but could you try to make a packet capture on the interface where your AD is, when you are authenticating with an empty password? then could you give me the packet capture by private message ?
I am very surprised by this kind of LDAP bug. I would like to check if it entirely related to your AD configuration or is pfsense part of the issue
(Warning / big Disclaimer : this packet capture will contain username/password of the account used in pfSense for binding to the AD, and the username that you are trying to login with on the captive portal. Depending on how critical this data is, you could change passwords or use temporary usernames)
-
@free4 Ok i send you the capture file
-
Well, I have some news,
I could analyze the pcap @brinch sent me. I can confirm that the problem comes from his Active Directory server which successfully bind when user provides an empty password.
I did some research, and apparently it seems to be a microsoft "feature" called unauthenticated bind : https://blog.lithnet.io/2017/01/ad-lds-and-ldap-unauthenticated-binds.html
Unlike anonymous bind, unauthenticated binds are enabled by default in Microsft Active directory.
It is also apparently impossible to disable unauthenticated binds on Microsoft AD : https://serverfault.com/questions/947428/how-to-disable-unauthenticated-binds-in-active-directory2016
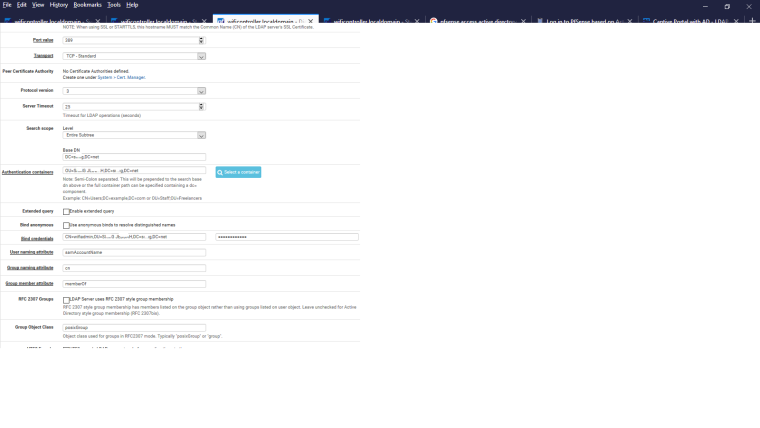
I wasn't aware of this controversy. @jimp perhaps we should add an option for forbidding unauthenticated binds?
-
Hello,
For information, I made a patch for it: https://github.com/pfsense/pfsense/pull/4116
@brinch @dimoz @olakara could you please try this patch and tell me if it is working for you ?
The process :
- Install the patch package
- Go to the menu "system-> Patch".
- Create a new patch. In "URL/Commit ID", enter "https://github.com/pfsense/pfsense/pull/4116.diff". Leave other fields to default values/empty, and click submit
- Go to your LDAP server settings. A new field (dis)allowing unauthenticated LDAP binds will appear.
Regards,
Augustin -
Thankyou @free4
Give me some days to implement a laboratory clone because I have all the firewalls in production environment. -
@free4
Hi Augustin.
I apologize for the delay but I have been quite busy.
I created a test firewall and tried to apply the patch, but in testing (before installation) it gives me these errors.
PfSense 2.4.4p3Patch Test Output apply
/usr/bin/patch --directory=/ -t -p2 -i /var/patches/5e2ab70eea69c.patch --check --forward --ignore-whitespaceHmm... Looks like a unified diff to me...
The text leading up to this was:|diff --git a/src/etc/inc/auth.inc b/src/etc/inc/auth.inc
|index 4139ad22b46..35e9e46ddae 100644
|--- a/src/etc/inc/auth.inc+++ b/src/etc/inc/auth.inc Patching file etc/inc/auth.inc using Plan A... Hunk #1 succeeded at 1370 (offset -1 lines). Hunk #2 failed at 1963. 1 out of 2 hunks failed while patching etc/inc/auth.inc Hmm... The next patch looks like a unified diff to me... The text leading up to this was:
|diff --git a/src/etc/inc/ipsec.auth-user.php b/src/etc/inc/ipsec.auth-user.php
|index 71ed2b6bcbc..cfd48cfc24d 100755
|--- a/src/etc/inc/ipsec.auth-user.php+++ b/src/etc/inc/ipsec.auth-user.php Patching file etc/inc/ipsec.auth-user.php using Plan A... Hunk #1 succeeded at 49 (offset -2 lines). Hmm... The next patch looks like a unified diff to me... The text leading up to this was:
|diff --git a/src/etc/inc/openvpn.auth-user.php b/src/etc/inc/openvpn.auth-user.php
|index 6bb059a458e..abd9accf92a 100644
|--- a/src/etc/inc/openvpn.auth-user.php+++ b/src/etc/inc/openvpn.auth-user.php Patching file etc/inc/openvpn.auth-user.php using Plan A... Hunk #1 succeeded at 51 (offset -2 lines). Hmm... The next patch looks like a unified diff to me... The text leading up to this was:
|diff --git a/src/usr/local/www/diag_authentication.php b/src/usr/local/www/diag_authentication.php
|index 6bd0789441d..5ef3db69553 100644
|--- a/src/usr/local/www/diag_authentication.php+++ b/src/usr/local/www/diag_authentication.php Patching file usr/local/www/diag_authentication.php using Plan A... Hunk #1 succeeded at 38 (offset -2 lines). Hmm... The next patch looks like a unified diff to me... The text leading up to this was:
|diff --git a/src/usr/local/www/guiconfig.inc b/src/usr/local/www/guiconfig.inc
|index b3b21dfdfee..00cb98b0e53 100644
|--- a/src/usr/local/www/guiconfig.inc+++ b/src/usr/local/www/guiconfig.inc Patching file usr/local/www/guiconfig.inc using Plan A... Hunk #1 succeeded at 142 (offset -2 lines). Hmm... The next patch looks like a unified diff to me... The text leading up to this was:
|diff --git a/src/usr/local/www/system_authservers.php b/src/usr/local/www/system_authservers.php
|index 21d107ec03a..b68283f5ab6 100644
|--- a/src/usr/local/www/system_authservers.php+++ b/src/usr/local/www/system_authservers.php Patching file usr/local/www/system_authservers.php using Plan A... Hunk #1 succeeded at 159 (offset -2 lines). Hunk #2 succeeded at 332 (offset -5 lines). Hunk #3 succeeded at 765 (offset -6 lines). Hunk #4 succeeded at 989 (offset -5 lines). Hmm... The next patch looks like a unified diff to me... The text leading up to this was:
|diff --git a/src/usr/local/www/wizards/openvpn_wizard.inc b/src/usr/local/www/wizards/openvpn_wizard.inc
|index 5223ec8bad6..0a20b06f908 100644
|--- a/src/usr/local/www/wizards/openvpn_wizard.inc+++ b/src/usr/local/www/wizards/openvpn_wizard.inc Patching file usr/local/www/wizards/openvpn_wizard.inc using Plan A... Hunk #1 succeeded at 479 (offset -14 lines). Hmm... The next patch looks like a unified diff to me... The text leading up to this was:
|diff --git a/src/usr/local/www/wizards/openvpn_wizard.xml b/src/usr/local/www/wizards/openvpn_wizard.xml
|index e5d154a4693..30649a9cd2c 100644
|--- a/src/usr/local/www/wizards/openvpn_wizard.xml+++ b/src/usr/local/www/wizards/openvpn_wizard.xml Patching file usr/local/www/wizards/openvpn_wizard.xml using Plan A... Hunk #1 succeeded at 302 (offset -2 lines). done