Assign 3rd interface to Pfsense
-
-
Ok that should be fine then.
So set a continuous ping running to 4.2.2.2 then check the state table in Diag > States. Filter by 4.2.2.2.
You should see a state on the new interface and a state with NAT on the WAN interface.
Steve
-
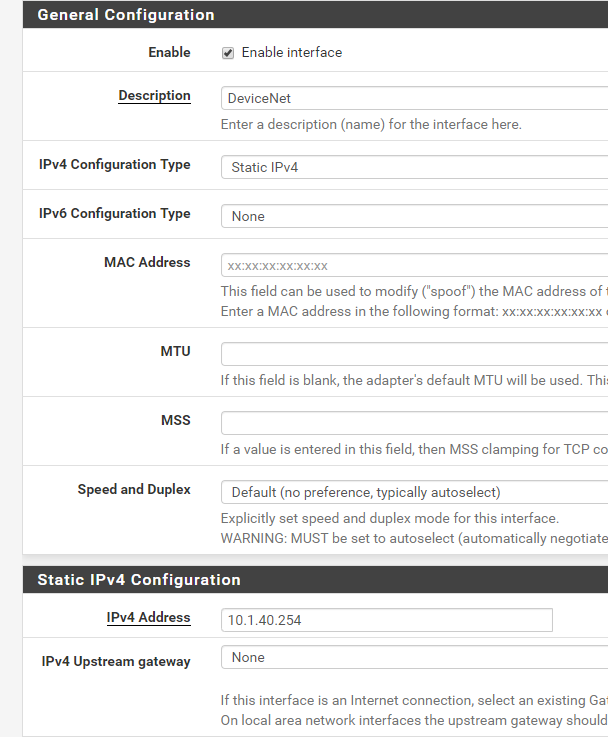
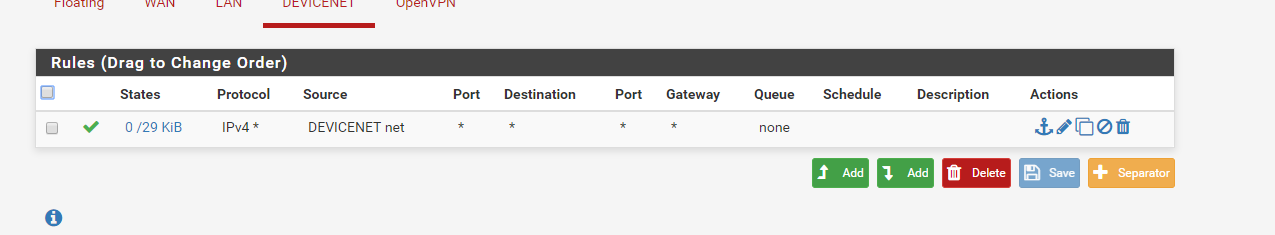
Thanks Steve for your reply, I checked the states and filtered by 4.2.2.1, unfortunately it showed nothing. The firewall rule looks as below.
-
@techman2005
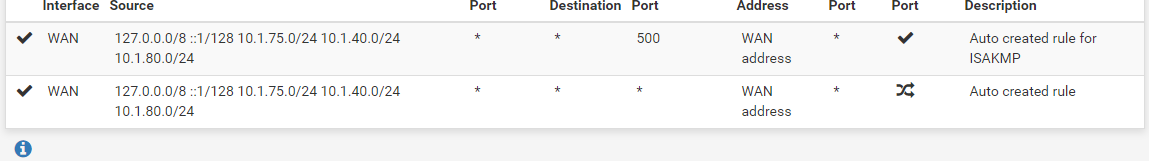
Outbound NAT is configured for 10.1.40.0/24 ???? -
it appears to be there. Is there another good way to look at the logs? NAT is auto generated.
-
@techman2005
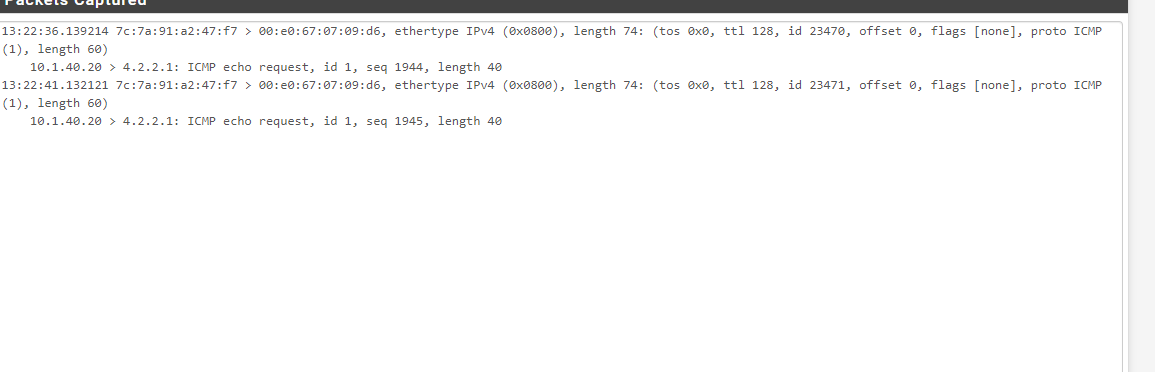
Try to run Packet Capture or tcpdump on the wan interface to see what's going on
interface WAN
Protocol ICMP
Host 4.2.2.2Ideally , you should see this result
21:09:16.501092 IP XXX.XXX.1.96 > 4.2.2.2: ICMP echo request, id 25266, seq 0, length 64
21:09:16.556329 IP 4.2.2.2 > XXX.XXX.1.96: ICMP echo reply, id 25266, seq 0, length 64 -
-
If this is the wan interface, you can see that nat outbound does not work correctly
Try to use Manual Outbound NAT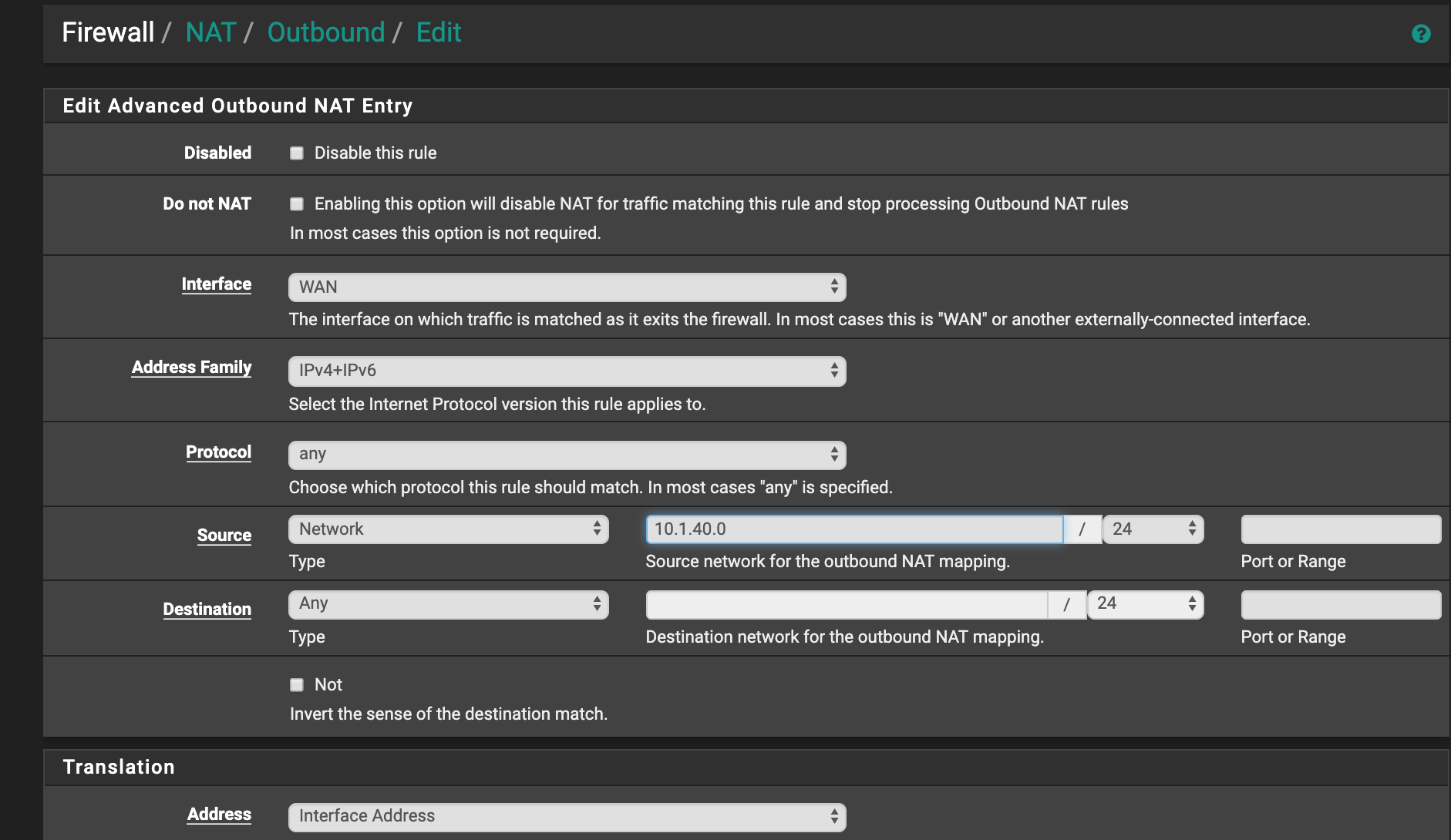
-
If you're seeing packets come in but no states generated either on DEVICENET or WAN (you should see both) then something is blocking that traffic. Do you see it blocked in the firewall logs? Which rule is blocking it?
If not you may have something set to block without logging like maybe pfBlocker or Snort.Steve
-
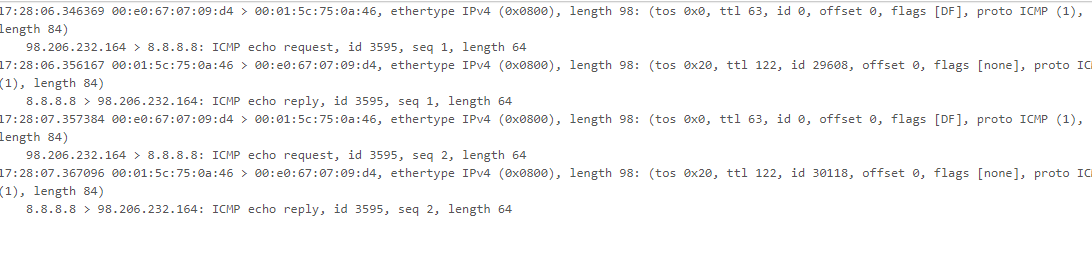
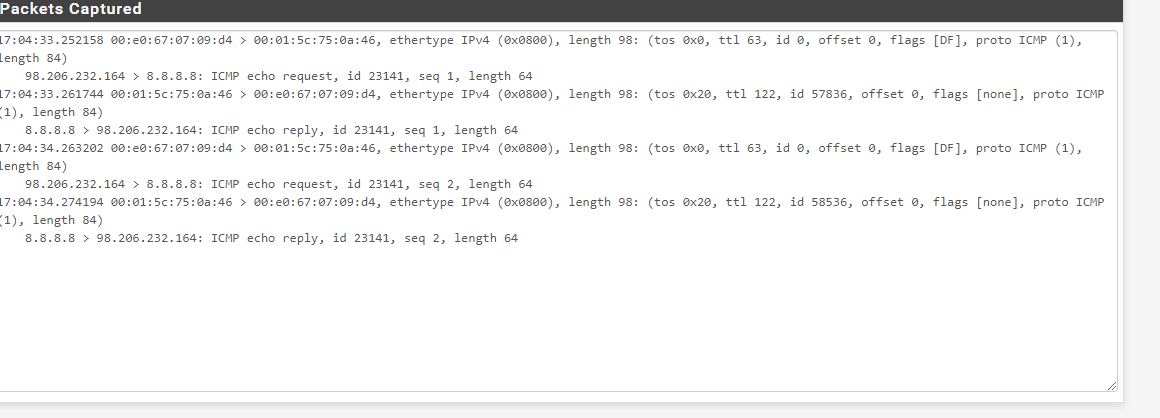
I was able to get packet captures from both WAN and D net. where do I go from here? all your help is greatly appreciated.
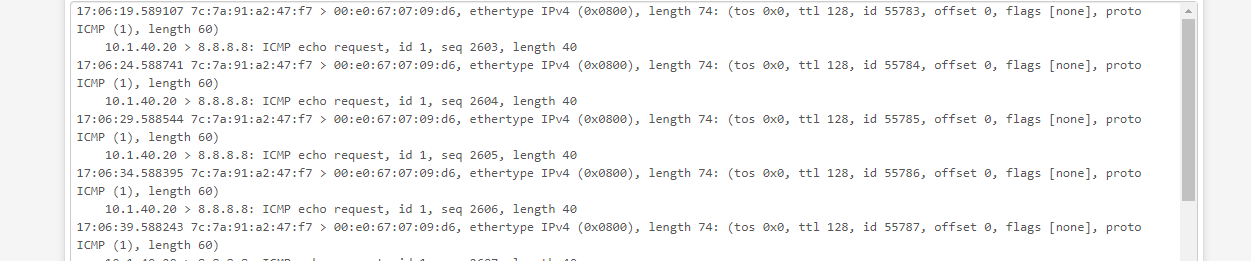
-
Are you using 8.8.8.8 as the monitoring IP for the WAN? Or pinging it from anywhere else?
Because those pings on DEVICENET are at ~5s internals but on WAN are at 1s intervals. I don't think that's the same traffic.
You were seeing no open states and they will be there is traffic is being passed.
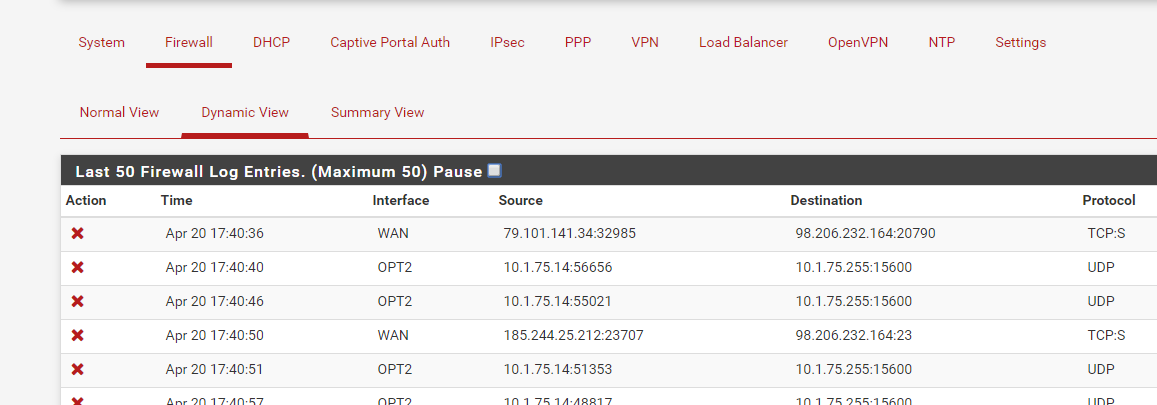
Check the firewall logs.
Do you have any packages installed?
Steve
-
-
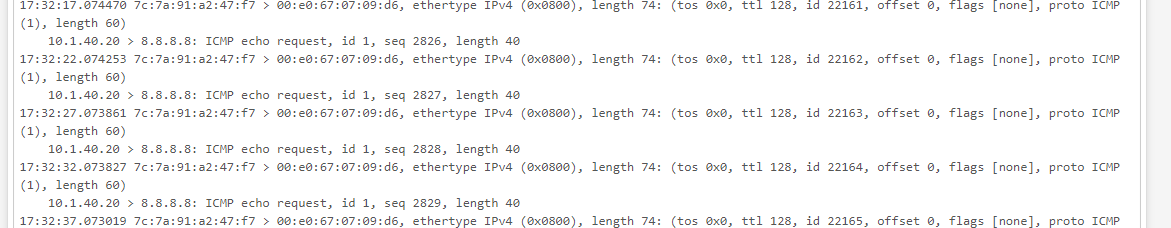
Still 1s intervals on WAN and 5 internally. Use a different IP that isn't in use anywhere else.
Check the firewall logs.
Do you have any packages installed?
-
That interface doesn't even appear in the firewall logs.
Yes I have a few packages installed screenshot attached.
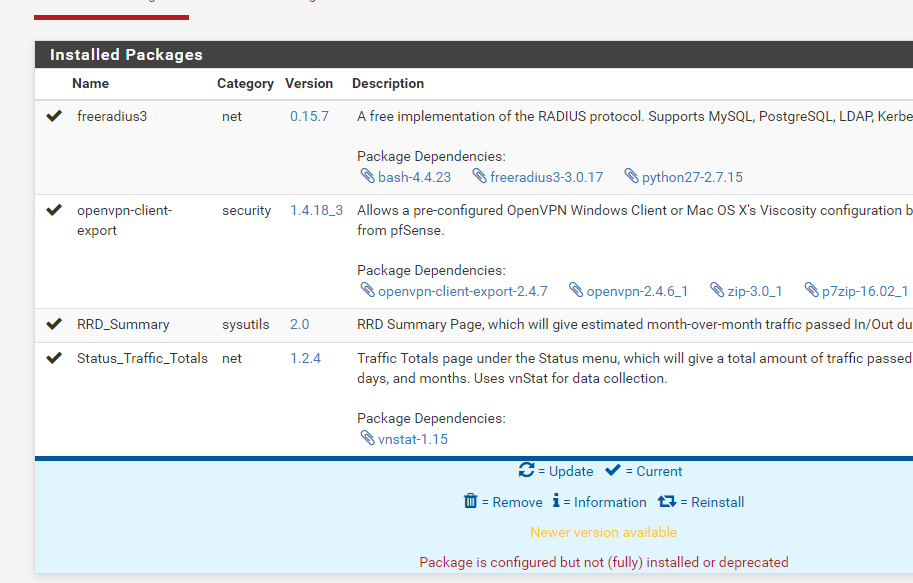
-
Ok, none of those packages should be an issue.
Did you filter the firewall logs by the IP you were trying to ping? Or by the interface you were pinging from?
That screenshot shows 21s of logs so they moght just not be shown there.But, again, try pinging by some other IP that is not used anywhere else. Leave the ping running then check the state table and filter by the target IP. Leave the interfaces set to 'all'. You should see states on both the internal interface and WAN. You can verify that by testing from a working interface so you know what it should look like.
Steve
-
@techman2005
Hey
Show the output of the command ifconfigor
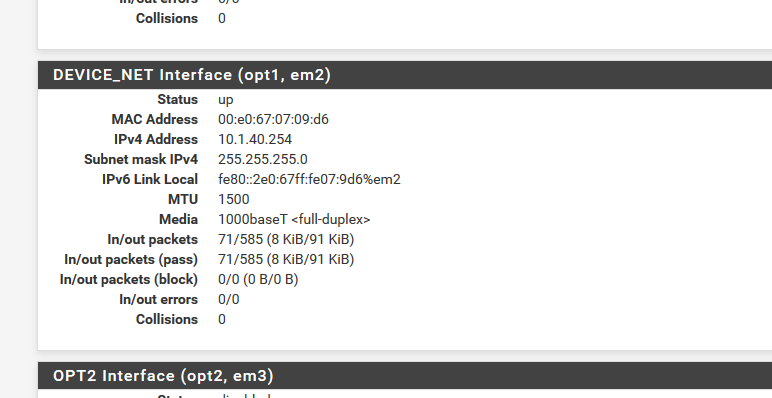
Status/interfaces (Devicenet) -
So I did a ping to 8.8.4.4 from a device on d net and received the following for d net interface and didn't receive anything for wan.
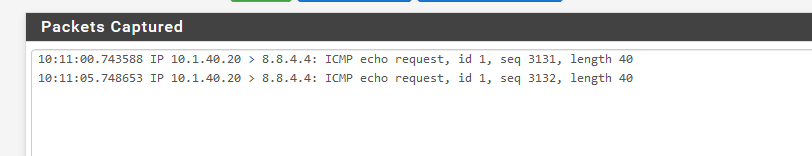
The output for d net interface
-
@techman2005 said in Assign 3rd interface to Pfsense:
Do you have any floating rules ?
And what is Openvpn interface ?
Is it a server or a client ?
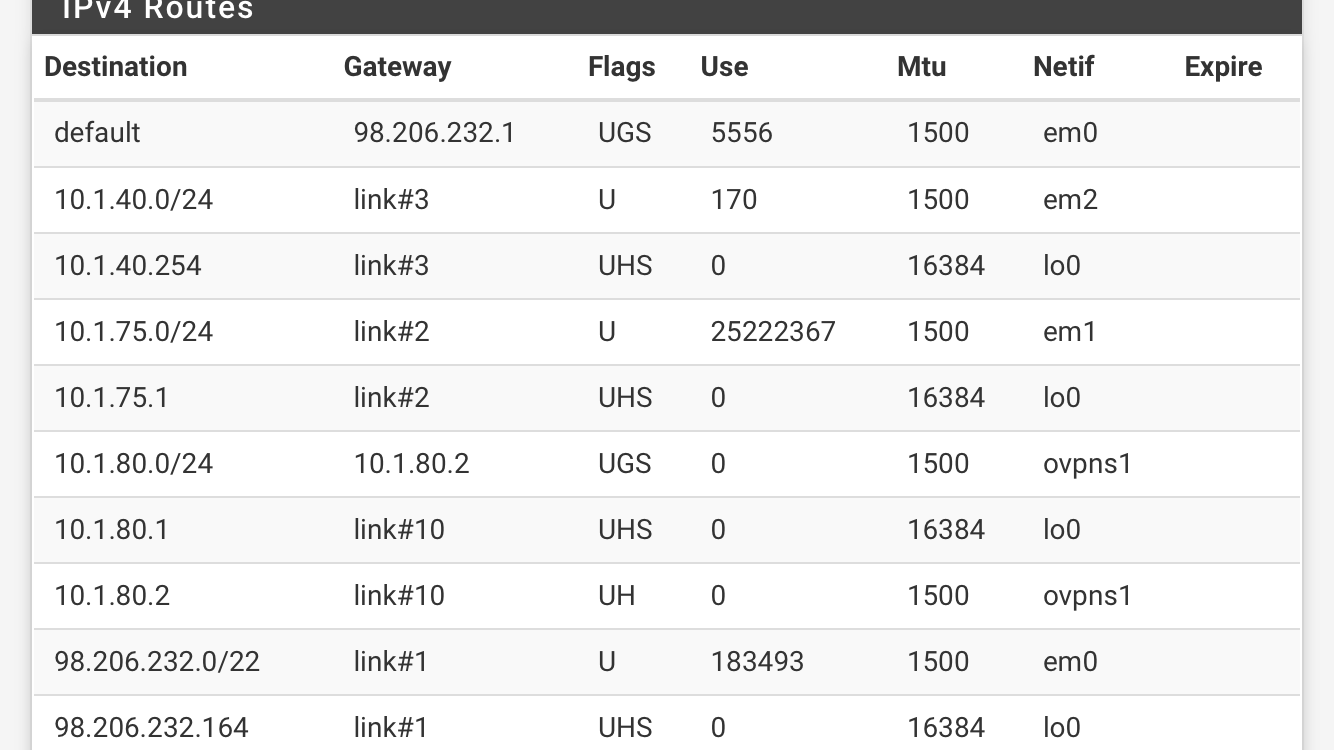
Show routing table -
No floating rules
Vpn server
-
If you are seeing no states on any interface and no packets leaving WAN that traffic is being blocked.
Run the ping again and check the firewall logs. Filter by destination IP 8.8.4.4. If you see logged blocks click the red X to see what rule is blocking it.
Are you seeing any alerts reported on the dashboard?
Steve