DNS Resolve Domain Overrides do not work after pfsense restart
-
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
If you just use localhost, then it will nat to the interface it needs to use to get somewhere... Be it your wan IP to talk to public servers.. Or your vpn interface IP to talk down your vpn..
And when unbound nats to the interface it needs to use, that's a good thing? Why not use the interfaces directly? Sorry, I'm still not getting the point. I mean I know both of these work but I'm curious about the differences.
On the listening end, if when unbound starts and the vpn is not up - how could it bind to that IP? It might work with any.. But why point to the vpn IP as destination in your domain overide... This IP could change, and your route doesn't point to vpn tunnel network, it points to the remote lan network, etc.
If you do these 2 things you shouldn't have any issues - as long as the tunnel is actually up when you try and query.
Right but won't it be the same thing? When unbound starts and vpn is not up, then how can it bind to the lan IP on the other side of the tunnel too? If you think of it, the vpn IP will always go up first compared to the lan IP on the other side of the tunnel.
Also, my site-to-site vpn IP network uses static IP's so those won't change.
-
dude if you tell unbound to use interface X, and interface X is not UP when unbound starts - then you have issue... If you tell unbound to use loopback.. Which is going to be UP!! then doesn't matter if the other interface goes up down, up down, etc.. As long as its up - you will be able to use it for outbound query.
Same thing for when unbound starts... The LAN IP should always be up.. .But will your site2site be up when unbound starts and wants to bind to your vpn IP??
You don't bind to a remote IP..
edit: Ok got baseline setup sim your setup.
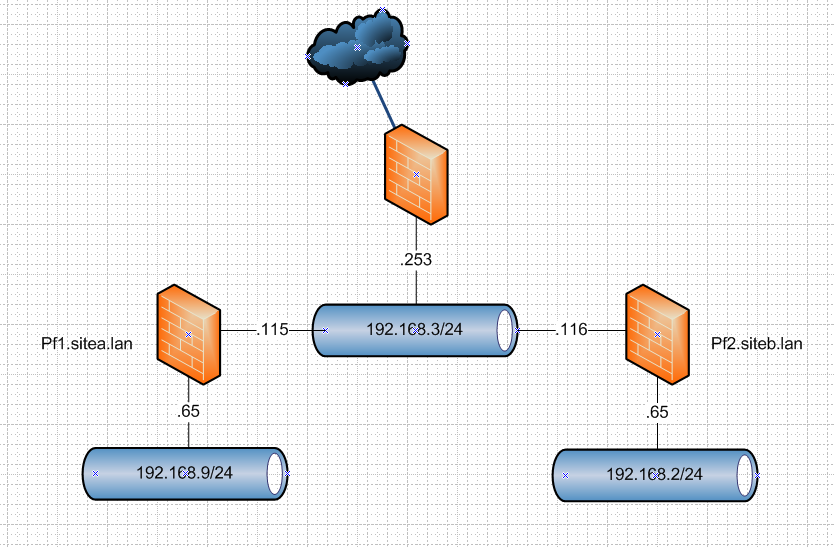
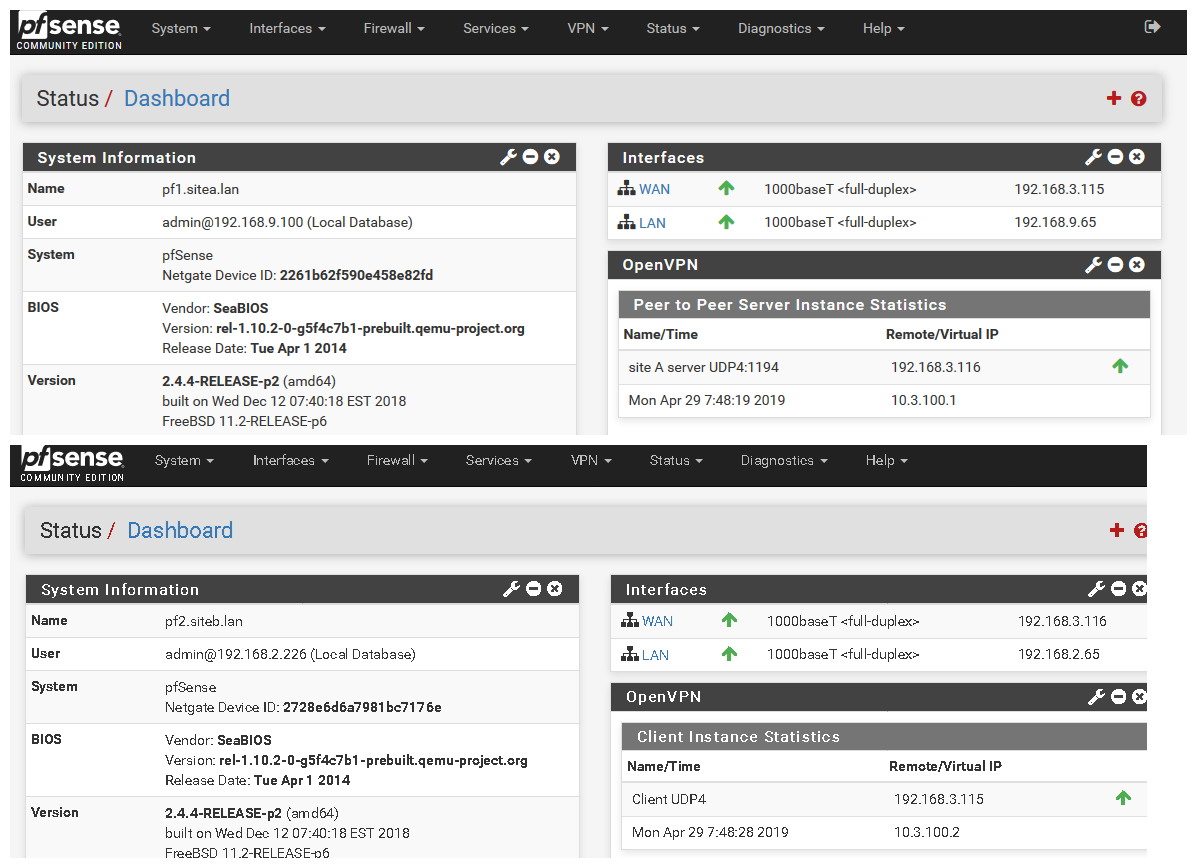
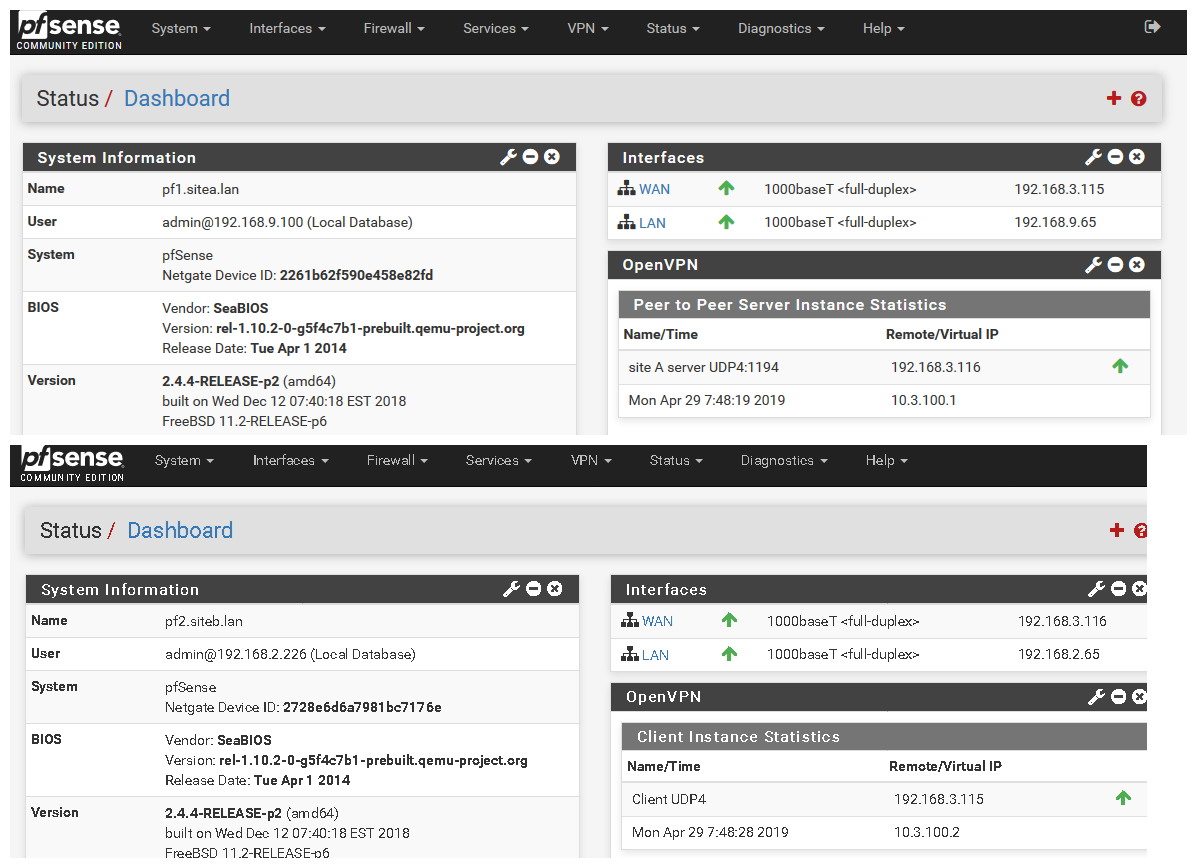
So I will fire up a s2s vpn between these 2 vms (2.4.4p2) over their wan networks (192.168.3/24) and then create domain overrides pointing to the other domain sitea or b, and create some records in there and validate the can be queried after reboot of them, etc.
But I will use what I think is correct way to do this and that is use localhost for outbound, and override pointing to the lan IP in my test setup that would be 192.168.9.65 for sitea, and 2.65 for site b.
edit2: ok up and running
using this guide
https://docs.netgate.com/pfsense/en/latest/book/openvpn/site-to-site-example-configuration-shared-key.html
-
I'm having this issue as well; though no domain overwrite. Just a simple OpenVPN connection; I need the interface for some firewall rules.
I was able to test choosing different interfaces, including all, specific and localhost.
Basically to get mine working after a reboot; (restarting the service doesn't appear to work) I have to assign the default gateway to WAN and then back to OPENVPN interface
-
@burny02 said in DNS Resolve Domain Overrides do not work after pfsense restart:
ult gateway to WAN and then back to OPENVPN
That is has ZERO to do with this sort of setup... Your default gateway should NEVER be your openvpn interface..
Please create your own thread with your own details of what you think is a problem... Using some vpn service has nothing to do with a site2site setup and dns overrides.
I have to run for work -- but using localhost doesn't seem to work for going down the vpn... But if set it to all it works... When set it to localhost get servfail...
$ dig @192.168.9.65 test.siteb.lan ; <<>> DiG 9.14.1 <<>> @192.168.9.65 test.siteb.lan ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 49807 ;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;test.siteb.lan. IN A ;; Query time: 2 msec ;; SERVER: 192.168.9.65#53(192.168.9.65) ;; WHEN: Mon Apr 29 09:06:17 Central Daylight Time 2019 ;; MSG SIZE rcvd: 43But if set to any as outgoing then works..
$ dig @192.168.9.65 test.siteb.lan ; <<>> DiG 9.14.1 <<>> @192.168.9.65 test.siteb.lan ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 31728 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;test.siteb.lan. IN A ;; ANSWER SECTION: test.siteb.lan. 3600 IN A 192.168.2.222 ;; Query time: 5 msec ;; SERVER: 192.168.9.65#53(192.168.9.65) ;; WHEN: Mon Apr 29 09:05:06 Central Daylight Time 2019 ;; MSG SIZE rcvd: 59But now that have this test best setup... Can see what is going on... And figure out best configuration for this...
Did you actually create an interface for your openvpn? The guide I linked does have you assign and interface to your openvpn s2s..
-
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
dude if you tell unbound to use interface X, and interface X is not UP when unbound starts - then you have issue... If you tell unbound to use loopback.. Which is going to be UP!! then doesn't matter if the other interface goes up down, up down, etc.. As long as its up - you will be able to use it for outbound query.
Ok, this makes sense.
Same thing for when unbound starts... The LAN IP should always be up.. .But will your site2site be up when unbound starts and wants to bind to your vpn IP??
You don't bind to a remote IP..
I thought you wanted me to point my override to the "LAN IP on the other side of the tunnel" which is also a remote IP? So in your setup, you point the siteA override to 192.168.2.65 and siteB override to 192.168.9.65. So how will those LAN IP "be always up" if they're remote IP's when unbound starts? Sorry if I misunderstood anything you've said but this is what I thought you meant.
edit: Ok got baseline setup sim your setup.
So I will fire up a s2s vpn between these 2 vms (2.4.4p2) over their wan networks (192.168.3/24) and then create domain overrides pointing to the other domain sitea or b, and create some records in there and validate the can be queried after reboot of them, etc.
But I will use what I think is correct way to do this and that is use localhost for outbound, and override pointing to the lan IP in my test setup that would be 192.168.9.65 for sitea, and 2.65 for site b.
edit2: ok up and running
using this guide
https://docs.netgate.com/pfsense/en/latest/book/openvpn/site-to-site-example-configuration-shared-key.html
Thanks for setting this up to get to the bottom of this. I really appreciate it!
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
@burny02 said in DNS Resolve Domain Overrides do not work after pfsense restart:
ult gateway to WAN and then back to OPENVPN
That is has ZERO to do with this sort of setup... Your default gateway should NEVER be your openvpn interface..
Please create your own thread with your own details of what you think is a problem... Using some vpn service has nothing to do with a site2site setup and dns overrides.
I have to run for work -- but using localhost doesn't seem to work for going down the vpn... But if set it to all it works... When set it to localhost get servfail...
$ dig @192.168.9.65 test.siteb.lan ; <<>> DiG 9.14.1 <<>> @192.168.9.65 test.siteb.lan ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 49807 ;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;test.siteb.lan. IN A ;; Query time: 2 msec ;; SERVER: 192.168.9.65#53(192.168.9.65) ;; WHEN: Mon Apr 29 09:06:17 Central Daylight Time 2019 ;; MSG SIZE rcvd: 43But if set to any as outgoing then works..
$ dig @192.168.9.65 test.siteb.lan ; <<>> DiG 9.14.1 <<>> @192.168.9.65 test.siteb.lan ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 31728 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;test.siteb.lan. IN A ;; ANSWER SECTION: test.siteb.lan. 3600 IN A 192.168.2.222 ;; Query time: 5 msec ;; SERVER: 192.168.9.65#53(192.168.9.65) ;; WHEN: Mon Apr 29 09:05:06 Central Daylight Time 2019 ;; MSG SIZE rcvd: 59But now that have this test best setup... Can see what is going on... And figure out best configuration for this...
Did you actually create an interface for your openvpn? The guide I linked does have you assign and interface to your openvpn s2s..
So for now, do you recommend setting outgoing interface to All?
Yes, I did create an interface for my s2s VPN so that I can assign a gateway for it in case I need to route special traffic to one site or the other. The guide you've linked to does not instruct us to add an openvpn interface. It tells you to create a rule in the OpenVPN tab that is created automatically when you establish the s2s openvpn connection. What I'm saying is to explicitly add the openvpn interface as an opt interface in Interfaces -> Assignments so you will end up with this in the Rules tab:
The OpenVPN tab there is the one that gets automatically created. The OPENVPN tab is the one I manually add under Interfaces so that I can use it as a gateway. This is a common setup with s2s openvpn in pfsense.
-
Why would you need/want to policy route something down your s2s connection... If the remote networks at either site change, then you would just update your vpn setup to reflect the netblocks at each site, etc.
When I get some free time again I will look to why it wasn't working with localhost as outgoing for down the tunnel.. My guess is something is not being natted in that case..
I had not had chance to reboot anything or take the vpnoffline, etc. But I got the queries working using all as outgoing..
But all should work for the outgoing.. even during a reboot or bounce in the vpn, etc... But your override should point IP on the other end of the tunnel, not the actual tunnel IP or tunnel interface IP, etc.
When you create this actual interface, ie your OPT.. your not giving it an IP are you?
edit:
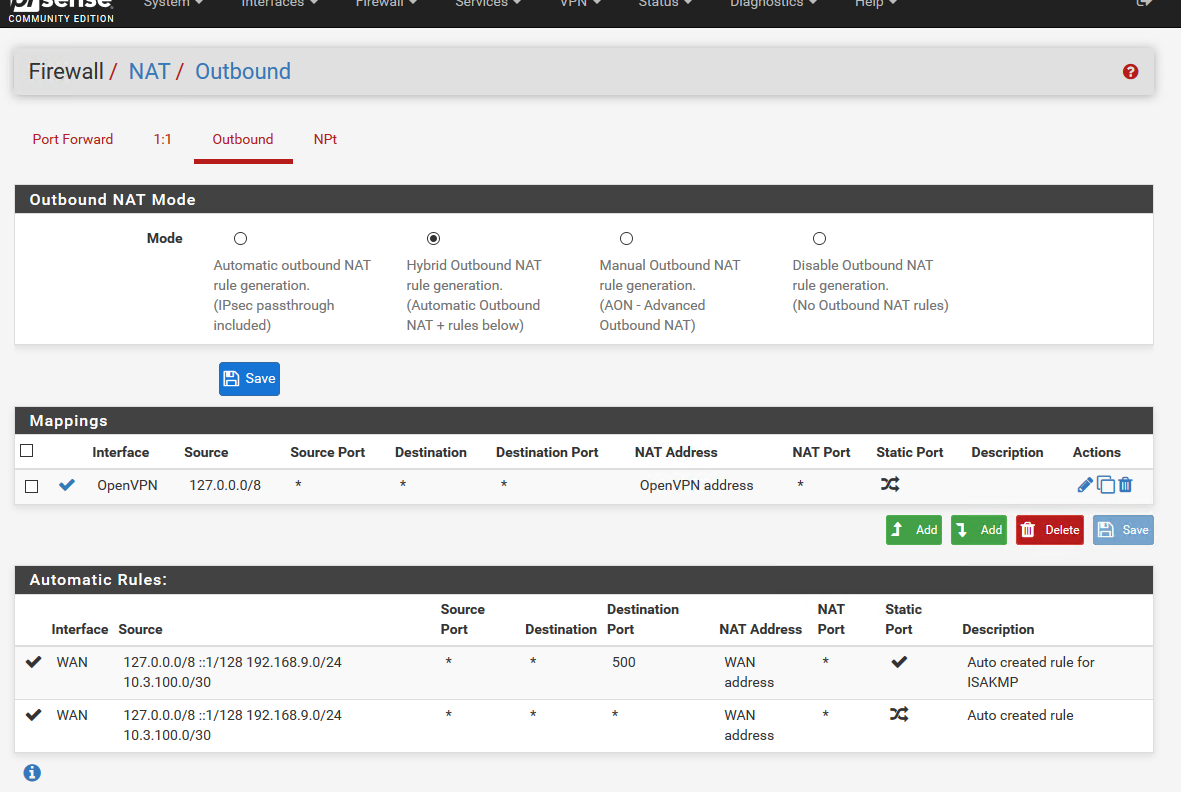
yeah just a nat thing... So changed over to hybrid nat, created a outbound for 127/8 to use the openvpn interface... I never assigned this to opt..And working now just using localhost as outgoing interface, where listen is only lan and localhost on both pf boxes.
Apr 29 10:37:12 unbound 51768:0 info: 10.3.100.1 test.siteb.lan. A IN Apr 29 10:37:12 unbound 51768:0 info: 10.3.100.1 test.siteb.lan. A IN NOERROR 0.000000 1 59I setup logging on siteb, and see that my query came from the tunnel IP of pf1
so let me reboot these vms, and should just be up and working as soon as they finish booting.
edit2: Yup working just fine... rebooted both of them...
$ dig @192.168.9.65 test.siteb.lan ; <<>> DiG 9.14.1 <<>> @192.168.9.65 test.siteb.lan ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 2172 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;test.siteb.lan. IN A ;; ANSWER SECTION: test.siteb.lan. 3600 IN A 192.168.2.222 ;; Query time: 3 msec ;; SERVER: 192.168.9.65#53(192.168.9.65) ;; WHEN: Mon Apr 29 10:44:16 Central Daylight Time 2019 ;; MSG SIZE rcvd: 59So that would be how I would suggest you set it up... Since now unbound is never going to have to bind to anything to use it for query or listen on a vpn interface that may or may not be up when unbound starts or restarts.
Here is outbound nat example.
So as long as your vpn is up.. And unbound is running on both sides you should be fine to resolve the remote domain.
-
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
Why would you need/want to policy route something down your s2s connection... If the remote networks at either site change, then you would just update your vpn setup to reflect the netblocks at each site, etc.
One of the reasons for this s2s openvpn is because one side of the tunnel has a public static WAN IP and the other is behind a CGNAT (dynamic private IP). So effectively, the network with the public static IP is acting as a proxy for incoming requests to whatever service I host on both networks. There are also special traffic that I need to route from the CGNAT network to the public IP network, hence I use policy routing.
Again, my remote networks don't change. I use the 10.0.0.0/30 network for my tunnel.
When I get some free time again I will look to why it wasn't working with localhost as outgoing for down the tunnel.. My guess is something is not being natted in that case..
I had not had chance to reboot anything or take the vpnoffline, etc. But I got the queries working using all as outgoing..
But all should work for the outgoing.. even during a reboot or bounce in the vpn, etc... But your override should point IP on the other end of the tunnel, not the actual tunnel IP or tunnel interface IP, etc.
Right. But my question still stands. If you point your override to a lan IP that is on the other side of the tunnel (a remote IP), how will unbound bind to it if the vpn is not yet up? You said that unbpund should bind to an interface that is always up.
When you create this actual interface, ie your OPT.. your not giving it an IP are you?
No, I'm not and you can't anyway. A note is there saying:
This interface type does not support manual address configuration on this page.
edit:
yeah just a nat thing... So changed over to hybrid nat, created a outbound for 127/8 to use the openvpn interface... I never assigned this to opt..Ok, this makes sense. I forgot about specifying an outbound nat rule for when the source IP is localhost and the packet exits through the openvpn interface.
And working now just using localhost as outgoing interface, where listen is only lan and localhost on both pf boxes.
Apr 29 10:37:12 unbound 51768:0 info: 10.3.100.1 test.siteb.lan. A IN Apr 29 10:37:12 unbound 51768:0 info: 10.3.100.1 test.siteb.lan. A IN NOERROR 0.000000 1 59I setup logging on siteb, and see that my query came from the tunnel IP of pf1
so let me reboot these vms, and should just be up and working as soon as they finish booting.
Great!!
-
@kevindd992002 said in DNS Resolve Domain Overrides do not work after pfsense restart:
If you point your override to a lan IP that is on the other side of the tunnel (a remote IP), how will unbound bind to it if the vpn is not yet
Your not Binding to anything.. its just the IP your pointing your domain override too...
Its the other sides unbound that needs to bind to something to LISTEN on for queries.. when unbound starts up on that side B, and the vpn is not up... How does it bind to listen... But have to assume if pfsense is up and running that the LAN ip is up.. So then unbound can bind and listen to this interface..
-
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
@kevindd992002 said in DNS Resolve Domain Overrides do not work after pfsense restart:
If you point your override to a lan IP that is on the other side of the tunnel (a remote IP), how will unbound bind to it if the vpn is not yet
Your not Binding to anything.. its just the IP your pointing your domain override too...
Its the other sides unbound that needs to bind to something to LISTEN on for queries.. when unbound starts up on that side B, and the vpn is not up... How does it bind to listen... But have to assume if pfsense is up and running that the LAN ip is up.. So then unbound can bind and listen to this interface..
Gotcha!! I understand what you mean now. Thanks.
-
Ok think we can call this solved then ;) Going to leave my vms... I can use these to lab almost anything ;)
Proof is in the pudding though.. Let us know how it works out after your next reboot..
-
So far so good until I noticed that the unbound service of one of my pfsense boxes is down, just this morning. I'm not really sure what happened but this is what I saw in the system logs:
May 7 07:36:24 unbound 29511:0 fatal error: Could not read config file: /unbound.conf. Maybe try unbound -dd, it stays on the commandline to see more errors, or unbound-checkconfIs there a reason for this?
Also, there are a lot of restarts during normal unbound operation like so:
ay 7 05:12:20 unbound 29511:0 info: start of service (unbound 1.8.1). May 7 05:12:20 unbound 29511:0 info: service stopped (unbound 1.8.1). May 7 05:12:20 unbound 29511:0 info: server stats for thread 0: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting May 7 05:12:20 unbound 29511:0 info: server stats for thread 0: requestlist max 0 avg 0 exceeded 0 jostled 0 May 7 05:12:20 unbound 29511:0 info: server stats for thread 1: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting May 7 05:12:20 unbound 29511:0 info: server stats for thread 1: requestlist max 0 avg 0 exceeded 0 jostled 0 May 7 05:12:20 unbound 29511:0 info: server stats for thread 2: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting May 7 05:12:20 unbound 29511:0 info: server stats for thread 2: requestlist max 0 avg 0 exceeded 0 jostled 0 May 7 05:12:20 unbound 29511:0 info: server stats for thread 3: 0 queries, 0 answers from cache, 0 recursions, 0 prefetch, 0 rejected by ip ratelimiting May 7 05:12:20 unbound 29511:0 info: server stats for thread 3: requestlist max 0 avg 0 exceeded 0 jostled 0 May 7 05:12:20 unbound 29511:0 notice: Restart of unbound 1.8.1.Is this also normal?
-
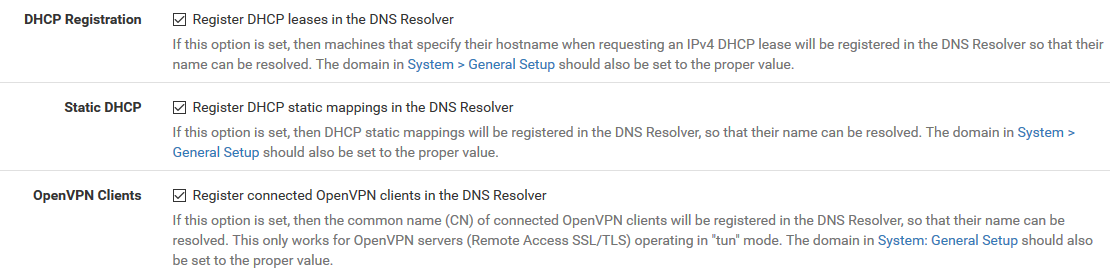
Restart of unbound... Do you have it register dhcp? Do you have pfblocker?
-
-
well yes register dhcp will restart unbound.
-
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
well yes register dhcp will restart unbound.
Ok. Any ideas why the service stopped suddenly though? This is the first time, in many years, that I had unbound stopped without me doing anything.
-
because there was a new dhcp lease/renew or a vpn client.. If you have it register clients (other than static) then yes unbound will be stopped and restarted now and then.
If you don't want that to happen then don't have dhcp clients registered.. I don't really get why you need to do that - how many clients you have? Just setup reservations for those that you "need" to be able to resolve name of.
-
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
because there was a new dhcp lease/renew or a vpn client.. If you have it register clients (other than static) then yes unbound will be stopped and restarted now and then.
If you don't want that to happen then don't have dhcp clients registered.. I don't really get why you need to do that - how many clients you have? Just setup reservations for those that you "need" to be able to resolve name of.
I understand but this time it stopped indefinitely (since this morning) until I went it and saw that the service is stopped. I've had those settings since a few years ago and never had the service stopped. I understand that it restarts if you have dhcp register enabled, but it shouldn't stay stopped.
This is the error in question:
May 7 07:36:24 unbound 29511:0 fatal error: Could not read config file: /unbound.conf. Maybe try unbound -dd, it stays on the commandline to see more errors, or unbound-checkconfunbound-checkconf resulted to:
unbound-checkconf: no errors in /usr/local/etc/unbound/unbound.conf
-
@kevindd992002 said in DNS Resolve Domain Overrides do not work after pfsense restart:
fatal error: Could not read config file: /unbound.conf.
did you have pfblocker installed at one time? Where you playing with it?
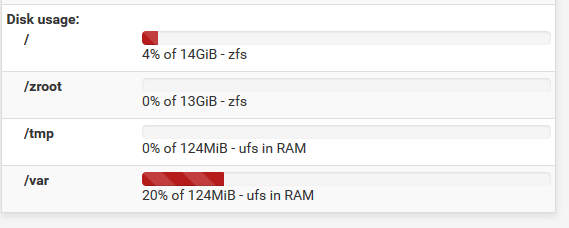
Your disk full? Disk errors?
Did a vpn user vpn at that time? Maybe the command is wrong to restart it when that happens? If you see it happening more up your log level in unbound.
-
@johnpoz said in DNS Resolve Domain Overrides do not work after pfsense restart:
@kevindd992002 said in DNS Resolve Domain Overrides do not work after pfsense restart:
fatal error: Could not read config file: /unbound.conf.
did you have pfblocker installed at one time? Where you playing with it?
Your disk full? Disk errors?
Did a vpn user vpn at that time? Maybe the command is wrong to restart it when that happens? If you see it happening more up your log level in unbound.
No, never.
I don't see my disk being full anytime soon:
My VPN is only set for s2s VPN. Ok, hopefully this does not repeat.
-
It happened again today. I'm turning logging up to level 2, is that enough?
Also, is there a way for pfsense to notify when a service goes down?