Problem With Forwarding From AD To Resolver
-
I have a Server 2012 AD with DNS. I have a laptop that is a member of the domain. I can join the domain fine and confirm that the DNS server assigned by DHCP to the laptop is set to the IP of the AD server.
The AD server has a forward back to the pfsense IP. Pfsense has resolver enabled with forwarding enabled and TLS encryption enabled. Pfsense general settongs has 2 DNS serves listed, 9.9.9.9 and 149.112.112.112.
The issue I am having is in resolving addresses outside of the domain. For example, if I am browsing the internet on the laptop I might click a link and then get a timeout error in the browser. If I refresh the page it usually loads fine, or at times it takes an additional reload. Sometimes it loads right away.
If I do nslookups in pfsense response times for 9.9.9.9 are typically 8 msec.
-
A timeout is not DNS-specific, and a resolution vs a NXDOMAIN takes milliseconds. Plus, after being resolved, those lookups will stay in cache until they timeout according to their TTL.
Are you using DNSSEC? You might try disabling that. I've seen cases where a DNS that allegedly supports DNSSEC sometimes fails. You could also try just running resolver as is and let it do its job via the roots and authoritative DNS.
-
If your forwarding to resolvers that do dnssec, ie 9.9.9.9 then setting dnssec in unbound is pointless at best all its going to do is slow down your queries asking for dnssec stuff when it makes no sense too.. Since your forwarding to a resolver that is doing dnssec for you..
And forwarding over tls is going to cause you time that is for sure..
Your really going to have to give some specific examples of stuff that might be taking longer to resolve.. So we can see what the ttl's on the records are - and are they popular, etc.. While you might get 8msec when you ask 9.9.9.9 for something the only way that would be possible is if cached by them.. There is no way you can get that for stuff that is not cached, etc.
The only reason you should forward over tls is if your isp is hostile to your dns queries and messing with them.. Or your worried they are sniffing your queries and then using them for nefarious things.. Which to be honest maybe you should loosen your tinfoil hat a bit.. It might be cutting of blood flow ;)
You can also do something to help unbound, set respond with 0 ttl setting, prefetch, etc. There are many sites these days that have a unrealistic ttl on their records of like 60 seconds...
-
@KOM said in Problem With Forwarding From AD To Resolver:
Are you using DNSSEC? You might try disabling that. I've seen cases where a DNS that allegedly supports DNSSEC sometimes fails. You could also try just running resolver as is and let it do its job via the roots and authoritative DNS.
@johnpoz said in Problem With Forwarding From AD To Resolver:
If your forwarding to resolvers that do dnssec, ie 9.9.9.9 then setting dnssec in unbound is pointless at best all its going to do is slow down your queries asking for dnssec stuff when it makes no sense too.. Since your forwarding to a resolver that is doing dnssec for you..
I did have DNSSEC enabled. I disabled it and did get some improvement, but was still experiencing the issue.
@johnpoz said in Problem With Forwarding From AD To Resolver:
The only reason you should forward over tls is if your isp is hostile to your dns queries and messing with them.. Or your worried they are sniffing your queries and then using them for nefarious things.. Which to be honest maybe you should loosen your tinfoil hat a bit.. It might be cutting of blood flow ;)
I've read many of your postings throughout this forum on your thoughts on this issue. Your position is duly noted. My concern is not primarily privacy, it's more the possibility of MITM types of attacks. That being said, I did spend quite a bit of time yesterday researching how Unbound works and am willing to give it a shot.
@johnpoz said in Problem With Forwarding From AD To Resolver:
You can also do something to help unbound, set respond with 0 ttl setting, prefetch, etc. There are many sites these days that have a unrealistic ttl on their records of like 60 seconds...
In trying out Unbound I would like to set it up is the best way possible. Could you please be a little bit more specific as to the things I should be entering in the Resolver best set it up. Thanks!
-
Here are the 2 settings I mentioned about prefetch and serve 0 ttl
In the advanced section of the resolver
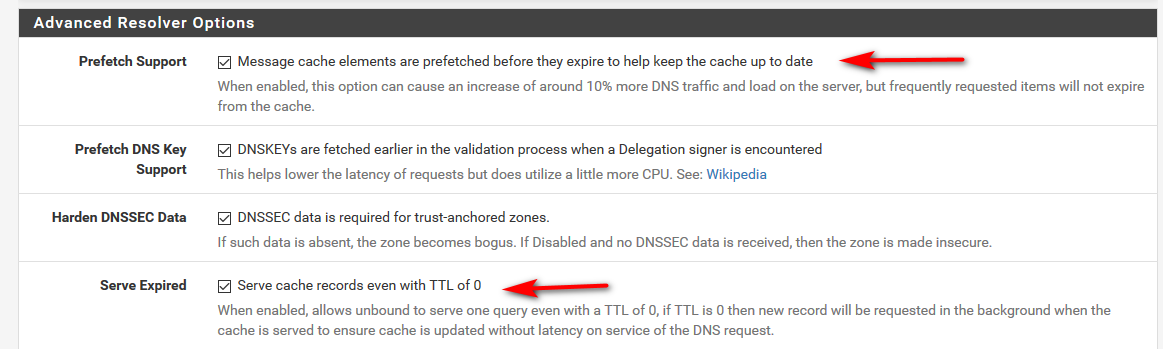
The dnssec settings have no meaning if you don't have dnssec enabled and are in forwarding mode.
It normally is bad to mess with TTLs, and you should use what the authoritative NS has set - but with many sites hosted by aws and the like having ttls of 60 freaking seconds.. I have set min to be 1 hour.. I just do not buy that I need to query for something every 60 seconds... Makes no sense..
So if I am on some website tooling around reading a blog or something for 5 minutes its going to be queried 5 times? Really? Come on!! ;)
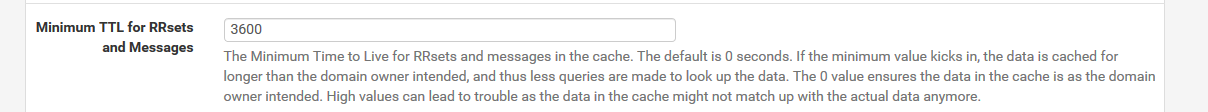
I have not run into any issues with doing that - but your mileage may differ depending on what sort of stuff your visiting, etc.
My unbound has just restarted - doing some testing of stuff... if you run this cmd you can keep an eye on how your cachehit is doing
[2.4.4-RELEASE][admin@sg4860.local.lan]/root: unbound-control -c /var/unbound/unbound.conf stats_noreset | grep total.num total.num.queries=588 total.num.queries_ip_ratelimited=0 total.num.cachehits=220 total.num.cachemiss=368 total.num.prefetch=0 total.num.zero_ttl=0 total.num.recursivereplies=368 [2.4.4-RELEASE][admin@sg4860.local.lan]/root:So with a total 588 queries currently at 220/588 for cache hits.. 37% That will go way up over time.. I will post back latter with hit rate..