Going in the bin.....
-
John
Thanks for replying - just a bit frustrated. I need a simple set up that let's everything IN and OUT- unless it is identified as from a list of GeoIPs. The only other setup is that if the pfsense unit is to be the DHCP server then the gateway has to be 192.168.0.1.
Today I could not even get the things to talk to me on my laptop. I plugged the SG-1000 LAN port to the Laptop LAN port. No other connections at all. Allowed the SG-1000 to act as DCHP server - once (and once only) it set the Laptop address to 192.168.1.100. Then tried to connect with the browser to 192.168.1.1 - just once I got a pfsense log in screen but it did not let me log in. After that I could not even get the login screen.
I did call an expert in the UK - who suggested all sorts of things including VPNs and others, all of which sounded way to complicated and not maintainable by us.
trouble is I am a simple mechanical engineer - nuts, bolts and grease I can work with!
-
Well one thing I could see as being a possible problem with pfblocker, is it can get a bet resource hungry if your using all its bells and whistles and large lists..
The sg1000s are not what you would call over powered ;)
I would bet they could struggle with any of the more resource hungry "packages" especially if using multiple of them all at the same time, etc. While they for sure can get the job done - they are not what you would call rocket ships ;)If we can start back with a clean slate - be happy to walk you through setting up a alias with a specific geoip alias... Which can just use the built in alias feature of pfsense - and update say every day or ever 30 days, whatever you want it to update the list, etc.
Keep in mind any geoip list you use is never going to be 100% accurate - and you could say allow something that is not in country X, or block something you want to allow that is in country X but not listed correctly.
Who exactly do you need to access these ports you have forwarded? Is it always say from your HQ location? Or from a few different company locations, etc.
-
John
I have one SG-1000 which I have not used at all. I managed to install pfblocker on the other unit but thought I did not change anything else.
Our application is simple;
I have an HMI which is also a web server it has a fixed LAN IP of 192.168.1.199. This is connected to a domestic router on which I have set up port forwarding for port 80 to 192.168.1.199. The router WAN is connected to a satellite modem. The satellite company have assigned a static IP for the modem and for the router (I also have the satellite DNS IPs).
Our problem: We need to access the HMI from the Internet for remote control and monitoring. Because the static IP is public it is bombarded with requests from all over the world. This is using up all our data allowance on the satellite link. It also slows down our control to the extent that sometimes we cannot log in at all.
So far none of the attacks have got through the HMI log in. But it will happen one day.
All I want to do is have pfsense silently drop any requests that are not from mainland Europe or European mobile networks (I use vodafone to log in when travelling). Even if we can get rid of 75% of requests that would be better.
We need to retain the domestic router for WiFi in the remote building because the SG1000 won't provide this.
There has to be a simple set up that can do this?
Thanks
Adrian
-
@aloening said in Going in the bin.....:
Because the static IP is public it is bombarded with requests from all over the world. This is using up all our data allowance on the satellite link.
There is nothing you can do at your end to stop that - while you can "slightly" reduce traffic, since if dropped on your end there would be no syn,ack sent back or any sort of bandwidth used in an answer to the unwanted. But the traffic being sent would still go down your pipe to you before it could get dropped, and would yes use of bandwidth... This is what you call internet "noise" and yeah depending it can add up...
Allowing a remote IP to hit any sort of gui or prompt for username/password will just encourage brute force attempts at logging in.. And yeah a gui sending back say logo's and such could be eating up your upload bandwidth.. Such a case might be good reason for changing from standard ports like 80 or 443 just to save bandwidth from scanners.. But doesn't matter what port something listens on for the noise be it you listen or not.. Unless you can get your ISP to only send say port X traffic that you listen on. So while there is lots of "noise" on http (port 80) for example there is going to be far less noise on say port 90.. So if your isp doesn't send traffic on 80 even too you, doesn't use up your bandwidth... And they only send traffic that is going to 90.. This could save on your bandwidth usage..
Its easy enough to setup pfsense to forward say traffic that hits your public IP on port 90, to port 80 on your hmi server so that nothing has to be altered on its config, etc.
If all you want is the domestic router to do is provide "wifi" then your best option would be to just use that as a AP (accesspoint) and let pfsense be your edge router - this way you do not have a double nat..
So you would setup something like this.
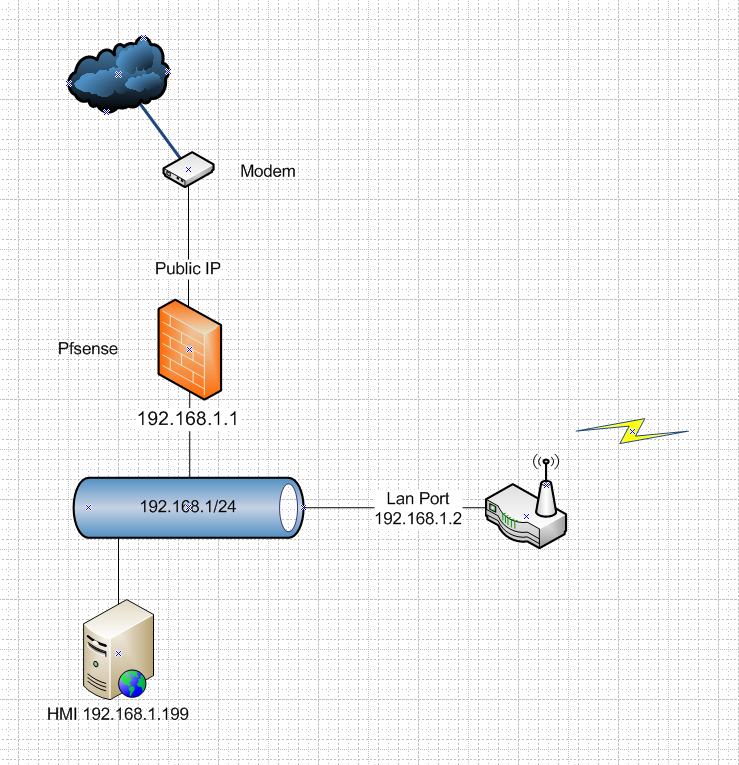
Your domestic router - just turn off its dhcp server, and give its "LAN" IP an address on your 192.168.1 network say .2 and now everything is on pfsense lan network of 192.168.1/24
We can then work out how to create your aliases either using the built in alias feature of pfsense, or pfblocker - you can use pfblocker to just maintain your alias lists for you - but I would really turn off all its other bells and whistles to reduce resource use.
Since your on sat connection your NOT going to want to resolve out of the box in pfsense, your going to need to forward your dns requests to your sat isp provided dns. Resolving and high latency sat connections never going to be a good idea..
But if all you ever do is login in from your "phone" Or known other locations - the whole blocking on geoip could be put away with a simple vpn setup... Now ALL traffic would be blocked other than the vpn traffic, and with correct setup of the vpn your "noise" would be drastically reduced.. Simple app you put on your phone to make the secure connection to pfsense when you need to do something on this remote network.
If what your after is reduction of bandwidth - I sure wouldn't want anything updating large lists of IPs every so often using up bandwidth to maintain the list... You would be better of creating static lists of the IP ranges you want to allow.
-
Yes - now that is beginning to make sense.
I appreciate that blcoking at our end will only stop the 'syn/ack' replies but that is at least something. I have talked to the satellite provider (Avanti) about blocking at their end. They say there is nothing they are prepared to do and certainly nothing that we can adjust ourselves.
As far as updating lists - we have 5GB per month on the satellite and our own usage is very low. So it would be OK to allow pfblocker to update occasionally even if this is not very efficient. Again if I could reduce the traffic by a little that would help.
The ports accessed seem to be random - here is an example;
[LAN access from remote] from 185.102.219.23:27712 to 192.168.1.199:80, Friday, October 06, 2017 11:27:42
[LAN access from remote] from 185.102.219.23:27425 to 192.168.1.199:80, Friday, October 06, 2017 11:27:30
[DoS Attack: RST Scan] from source: 218.23.104.186, port 41076, Friday, October 06, 2017 11:26:20
[DoS Attack: RST Scan] from source: 5.101.66.252, port 56008, Friday, October 06, 2017 11:21:52
[LAN access from remote] from 107.180.3.117:37095 to 192.168.0.131:80, Friday, October 06, 2017 11:17:01
[DoS Attack: RST Scan] from source: 77.72.85.10, port 49592, Friday, October 06, 2017 11:16:52
[DoS Attack: RST Scan] from source: 5.101.66.252, port 56008, Friday, October 06, 2017 11:15:23
[DoS Attack: ACK Scan] from source: 103.58.116.8, port 47600, Friday, October 06, 2017 11:04:19
[DoS Attack: RST Scan] from source: 5.188.10.242, port 43646, Friday, October 06, 2017 11:00:42
[DoS Attack: RST Scan] from source: 121.10.143.226, port 41467, Friday, October 06, 2017 11:00:40
[DoS Attack: RST Scan] from source: 77.72.85.10, port 49592, Friday, October 06, 2017 10:58:46
[DoS Attack: RST Scan] from source: 117.61.7.249, port 25609, Friday, October 06, 2017 10:57:38
[DoS Attack: ACK Scan] from source: 117.61.7.249, port 25609, Friday, October 06, 2017 10:57:37On limiting to certain IPs and using a VPN - that is not going to work for us. We have a number of (non techy) people who need access and that could come from many different networks. So as a first step just getting rid of unlikely IPs would be a start.
So chaps - how am I going to do this? there is a chance I could set the SG-1000 up on our office network which also has a static IP and one of you clever people could set it up for me? I am happy to pay for time and effort.
-
@aloening said in Going in the bin.....:
[DoS Attack: RST Scan] from source: 218.23.104.186, port 41076, Friday, October 06, 2017 11:26:20
[DoS Attack: RST Scan] from source: 5.101.66.252, port 56008, Friday, October 06, 2017 11:21:52Where are you seeing that? Is that on your domestic router? Pfsense would not report such a thing.
Looks to be false sort of positive to me... Could be cause by out of state traffic being seen where not expected.
Is your domestic router a netgear by chance? To be honest the so called "firewalls" in those soho routers report garbage.. For such an alert to be actual useful it should report both ports used in the packet, ie the source and dest.. That could be normal return traffic from traffic started on your end, and that IP just sending back a RST or ACK in the last one.. The informative info would be the source of the traffic port to your destination Port.. Lets say you sent traffic to that 5.101.66.252 on port 80 from some random port (that is how tcp works) and that IP sent you back a RST.. Saying hey sorry but we do not want to talk to you.. You might determine what traffic on your end was sending traffic to that IP on the source port (80 in my example)
Non techy people are so stupid they can not click a little vpn icon on their phone before connecting to the resource they want to connect to at this location?
You could hire netgate/pfsense to help you - with a support contract or professional services. You could get lucky and someone here "might" be willing to remote in and help you set it up..
I would be happy to walk you through a setup.. Once all the details are in order... you really really should put pfsense on the edge, so we can use its features to determine the actual nature of the traffic, and look to see what clients on your end might actually be sending out.. This can be done with simple setting your firewall rules to log the outbound traffic, and or sniff on the wan or lan of pfsense to determine exactly what is going on with the packet capture feature built in.
But lets be clear - if some outside IP decides to send you an out of the blue RST packet - there is nothing on your end that you could to reduce that traffic.. Nothing! All you can do with filtering via geoip is prevent something from actually being forwarded to your HMI, and your hmi system sending back a response.
Lets be clear as well if some outside IP just sent a RST packet or an ACK packet out of the blue - pfsense would do nothing with that packet, it would just be dropped.. Unless there was active state already in your table for such conversation started by your end.. Out of state traffic is always dropped.. And would never be forwarded to something behind pfsense in the in the first place.. The only way pfsense would forward traffic is if the packet is (SYN) - this is start of a conversation.
Here for example...
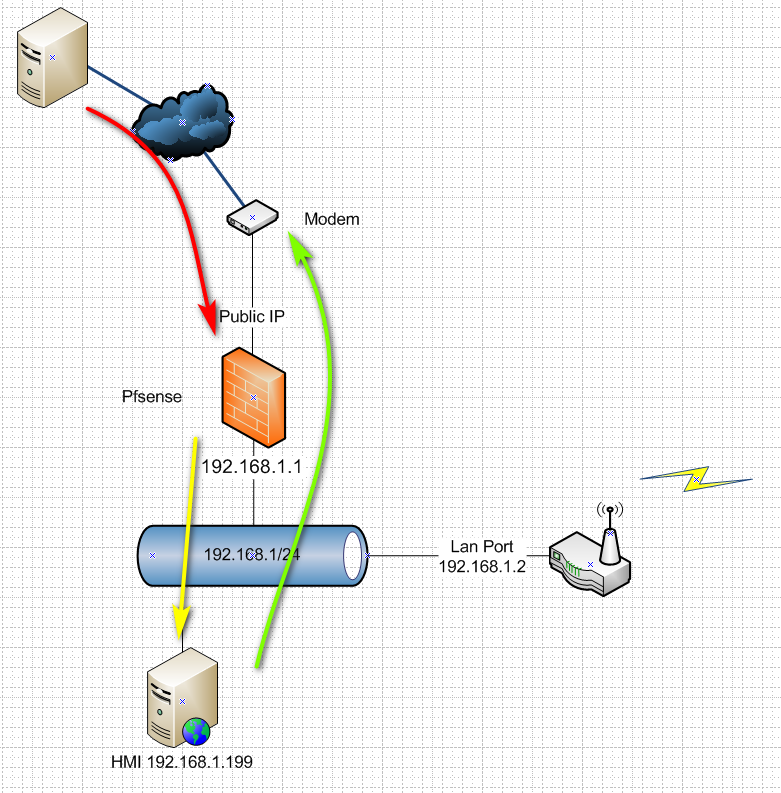
So nothing you can do to stop the RED arrow traffic.. Only your ISP could prevent such traffic sent to your public IP on port X.. What you could do is tell pfsense not to send the traffic on to your HMI, unless the source of the traffic IP is in an alias that is allowed. But the yellow doesn't cost you any isp bandwidth.. So until HMI sends its answer, the green no other extra bandwidth is used.. So you could stop hmi from ever seeing the traffic, so it would never answer.. Or you could say on the HMI system itself set it not to answer unless the source of the traffic is from an allowed IP..
The best you can do with pfsense or any system is to stop the yellow from being sent, and then the green answer.. You can not stop the red traffic from using up your internet bandwidth.
Can you do the sort of example setup I posted, or can you draw your actual setup.. If using your other router behind pfsense it would be something like this.
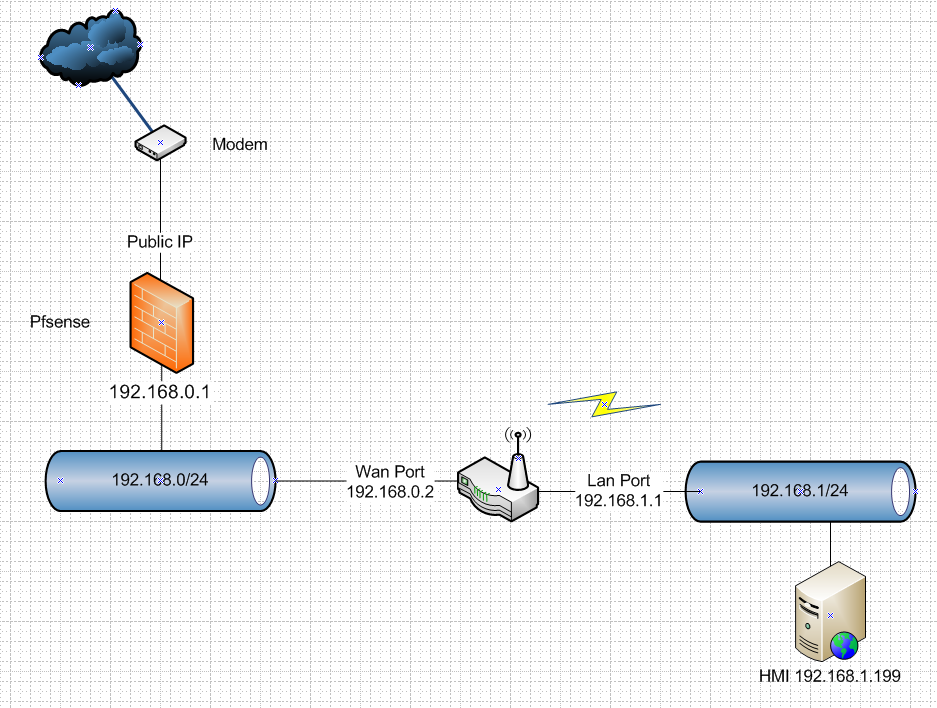
Or do you have your domestic router in front of pfsense?
-
@johnpoz said in Going in the bin.....:
5.101.66.252
John
Yes the router in the example is a netgear and I appreciate it has limitations. The pfsense is not in the system in anyway yet. So the minute the setup is;
(public IP) - Sat Modem - WAN on SOHO router LAN - HMI
SOHO router is DCHP server. The Sat Modem just forwards everything to the router.
I can arrange the system to be either of the ways you have drawn. I would not plan to have the domestic modem in the front, surely better to have the pfsense unit here. I do get the limitations on what traffic can be blocked. If I can get to that stage and still have trouble then a VPN is the next obvious step and I am sure I can get the various users to install a VPN client with some instructions but I would rather not do this initially.
However these are remote sites so I need to go there to change the physical connections. I will be at one site next on Tuesday evening (UK time).
-
Well if possible, use your current router as just AP, per the instructions I gave.
So your sat "modem" is actually doing nat as well.. Yeah you for sure would not a triple nat setup.. So using your domestic router as just AP (accesspoint) would be for sure better setup.
public IP (sat modem) --- private IP (192.168.2/24??) -- wan pfsense lan --- 192.168.0/24 --- wan router lan --- 192.168.1/24 -- hmi box
Is there anyway for your sat "modem" set to bridge mode so that it doesn't do nat, and the public IP is directly on the wan of pfsense?
-
Yup - I think the sat modem is in bridge mode. There are two IP addresses the sat company gave me - one for the WAN and one which the sat company uses if they want to access the modem. These addresses are 185.xxx.xxx.186 (Modem) and 188.xxx.xxx.185 (router). Both respond to a ping from the internet. Sorry for the xxx's but I don't want more probing of these addresses.
-
No problem hiding the public..
If your device has a public IP on its wan, ie say the .185 address then good. I would setup your old router as just AP, and use pfsense as your edge..
Then you wont have to worry about port forwarding at both pfsense and or your other router, and wont have to worry about changing pfsense lan network to not conflict with your other routers and it doing nat, etc.
-
Thanks John - and thanks for the encouragement. I will have another go at this later in the week. Got a couple of other jobs that needs looking at first. I will come back to you for some advice.....
-
I can see why the guy you contacted suggested using a VPN though. If the only reason this port is open is to allow you to monitor or configure the HMI using a VPN to access it would be far safer. You wouldn't need to open any ports to it directly then.
Steve