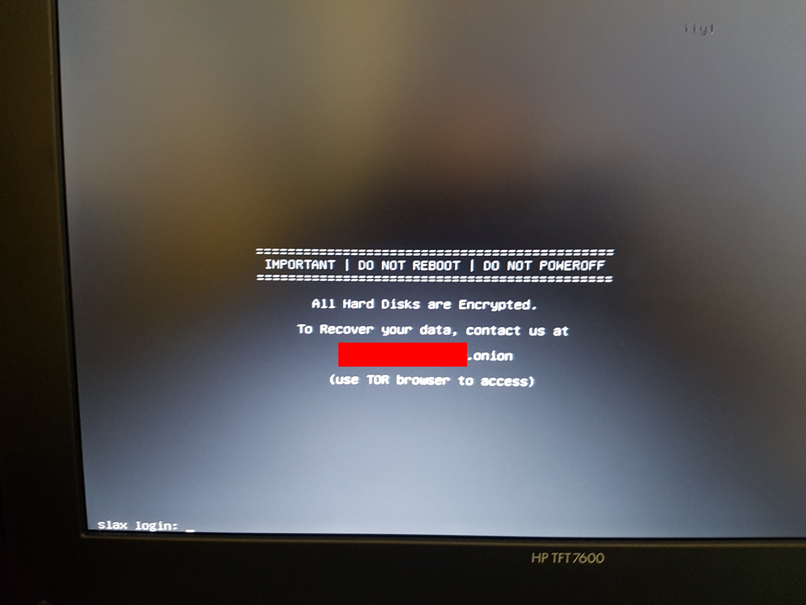
Ransomeware infected machine
-
Hey all,
Had part of our network go down, went to go hunt the issue down and found a ransomeware message running on what I "beleive" was a 2.4.3 box thats been running fine for a good few years. Other than some password changes admin settings were vanilla, from when it was orignally setup in ~2014. It did have some external ports open for a PBX but thankfully those are on fully segragated hardware.The drive would not boot after a restart, so swapped hardware and am reinstalling now.
Anyone see this before?
-
No, and I've been here for about 5 years.
What exactly leads you to believe there is ransomware on your pfSense? I don't remember ever hearing about any FreeBSD ransomware.
-
First thing I did when I couldn't get on the Web GUI was go to the physical machine in the racks. This is what was coming out of the VGA.
-
Why does it say SLAX LOGIN at the bottom? Slax is a flavour of Linux.
-
I'm assuming that has something to do with whatever got installed on this box.
This was a vanilla PFSense install from 2014 which has had nothing done to it other than upgrades and package installs from the default package manager.
Alas I do not have a list of what has been installed on this box (which I know would probably be useful. -
https://www.slax.org/
If that box was truly running a version of pfsense Id have to believe that someone (probably a disgruntled employee) gained physical access to that box and plugged a USB stick into it and installed that little jewel.
Otherwise- do you have your GUI and ssh ports open on your WAN?
-
What version of pfsense do you believe it had on it?
-
He said he thought it was 2.4.3.
-
If you have a backup of the config or had ACB configured recovering from that is not an issue.
The problem is discovcering how that happened. I would physically examine the hardware. What is it actually booting from?
Is that really the box you think it is? Was is running virtually maybe?
Steve
-
@KOM said in Ransomeware infected machine:
He said he thought it was 2.4.3.
Missed that. I saw-
running fine for a good few years. orignally setup in ~2014.
-
Thanks guys,
Ya I'm pretty sure it was 2.4.3 and it was on physical metal with a physical SSD.Disgruntled employee is a "possibility" have some peeps running CCTV stuff now but our access control to this room is shitty so 50/50. Also if this one individual was trying to be an ass there's much more serious stuff they could have done.
As for admin ports being open from other interfaces, there are/were 2 WANs and 2 LANs on this setup. One pair for regular traffic and one for PBX traffic. There was some concerns back in the day about having open ports for the PBX to work so a fully segmented network was setup but still had a single PFSense box (with 4x Ethernet ports).
I'm not 100% sure if admin was possible through the 2nd LAN/WAN (trying to sort out how to restrict access on the new install now actually). -
Can you post your config.xml Backup here so we can check for Config (Security) mistakes?
-Rico
-
Is this going to be another one of those posts where we talk among ourselves for hours without ever seeing any evidence that pfSense has anything to do with this?
-
@Rico
Would love too but don't have any from this install.
For reference to the uninitiated access to the admin section is all done via firewall rules right? -
Yes, to access the WebGUI or SSH from WAN side would require manual adding of Firewall Rules.
-Rico
-
What happens if your try to login with User root and Password toor at the slax login prompt?
I'd also try to boot some rescue disk and check what is really going on the filesystem. Some ransomware is not even encrypting anything, just telling so.-Rico
-
Even with full remote root ssh/webgui access I struggle to come up with a procedure where such a result would be possible without physical/console access.
Is there IPMI? Is that accessible? Is that secured?
-
19 hours later, still nothing...
-
Slax login? So this pfsense was running on VM?
-
I suspect this entire post is bogus:
- this is his first forum post ever
- he accuses pfSense of being vulnerable to ransomware attack despite no history whatsoever of this happening on FreeBSD
- the provided evidence is non-existent, confusing or irrelevant
- requests for follow-up information go unanswered
If this is as he claims, you would think he would be a little more proactive about reading replies and providing information. Instead, we all seem to care a lot more about his problem than he does.
However, he can feel free to prove me wrong by actually answering questions or providing more detail.