Ping and Traceroute basics
-
@johnpoz Sorry. I think I made an error in my response showing you gateways and not routes. And you are right, I'm pretty sure I copied configs initially from the VPN service I had set up, and adapted where needed. There is nothing yet set in the static routes config (if that's what you originally wanted).
I have changed the NAT rule to hybrid.
-
@stephenw10 Ok good. That was a fear of mine that any traffic originating at the interface IP will not be subject to rules of the interface subnet.
Also, I'm assuming setting a single default gateway would not achieve the result I want as, as you've figured out, I'm trying to have a way to troubleshoot routing from all subnets through all gateways I have set up? Should I not be creating a rule for each interface to pass through a suitable gateway? Though I tried setting a rule on LAN2 for ICMP from "LAN2 address" to any destination through WAN gateway, which still failed.
-
Your default route should always be out your wan... You then can policy route traffic you want to go out your vpn connection.
Most of the guides out there are just BS... they have you switch to manual outbound nat and pull routes from the vpn service.. Zero reason to do any of that.
-
@johnpoz said in Ping and Traceroute basics:
Most of the guides out there are just BS... they have you switch to manual outbound nat and pull routes from the vpn service.. Zero reason to do any of that.
<Sarcasm On>
Yes, there is a great reason for them to do that if the VPN provider wants to collect all of your traffic for possible use in some other revenue stream of theirs ...
</Sarcasm Off> -
@johnpoz I suppose it may depend on the context of the instructions. In a commercial context you may not want any other rules to exist than what was manually created for security and compliance reasons. But I digress. :-)
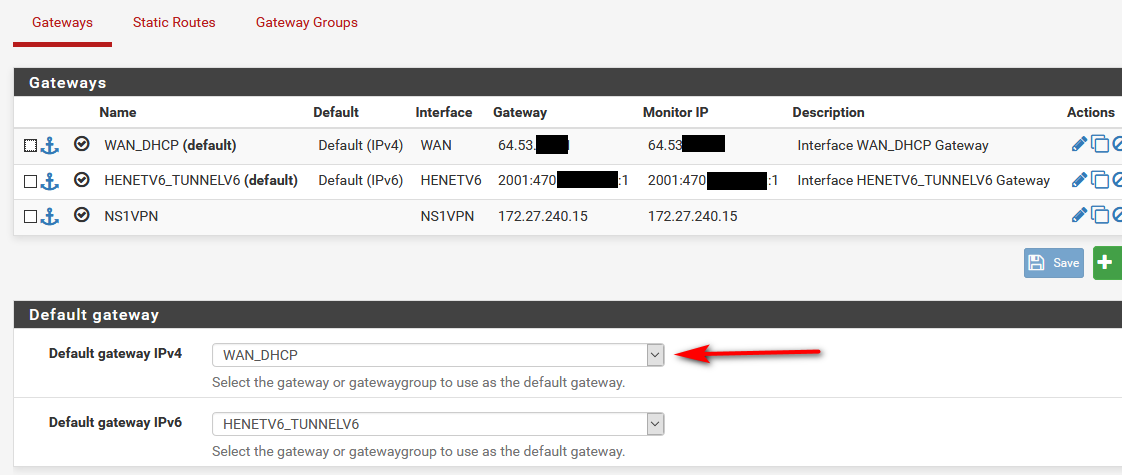
So.... I've changed the outbound NAT mode to hybrid. I've set the default gateway to the WAN gateway. This all makes sense.
Now what?
Is it as in my message to @stephenw10 where I need to create an ICMP rule for each interface to route through a specific gateway? I tried setting up such a passrule as follows:
Protocol: IPv4 ICMP any
Source: I tried both "LAN2 address" and "any"
Gateway: Now left at default.
The rest of the options were left.This didn't work. Hopefully someone can help with the next step(s).
-
You have yet to show your routes dude. If your default route is your wan, and your outbound nat is correct then you would be able to ping from that as source.
You don't need any rules on the interface to ping with pfsense using that as source.
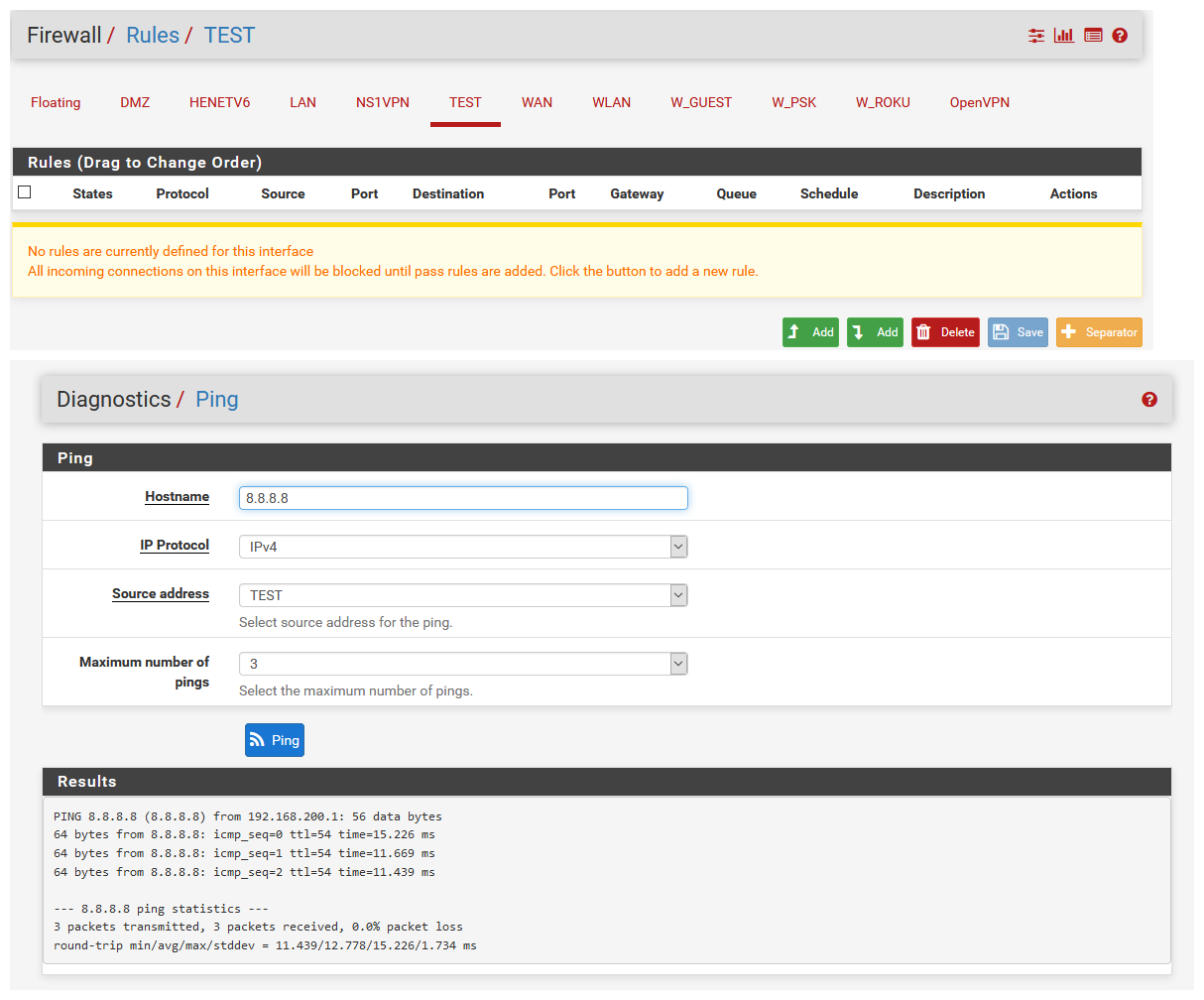
Pfsense itself does not use the rules that are on the interface.
You need rules on the interface to allow or block traffic entering pfsense from that network.
Gateway: Now left at default.
Set your gateway - don't leave it at auto.
-
@johnpoz Thanks for the time you are putting in.
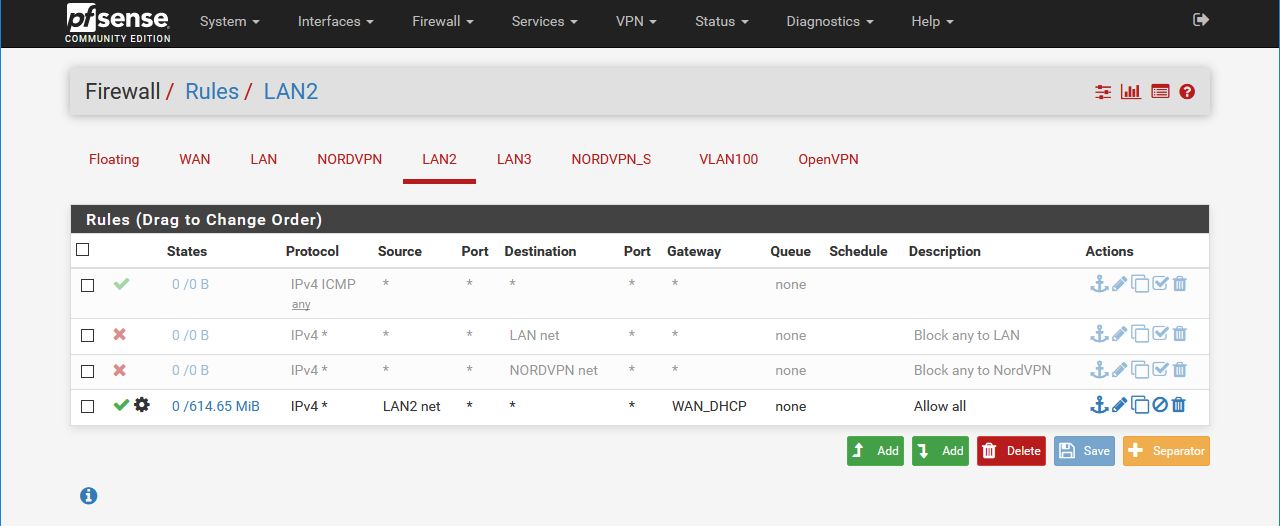
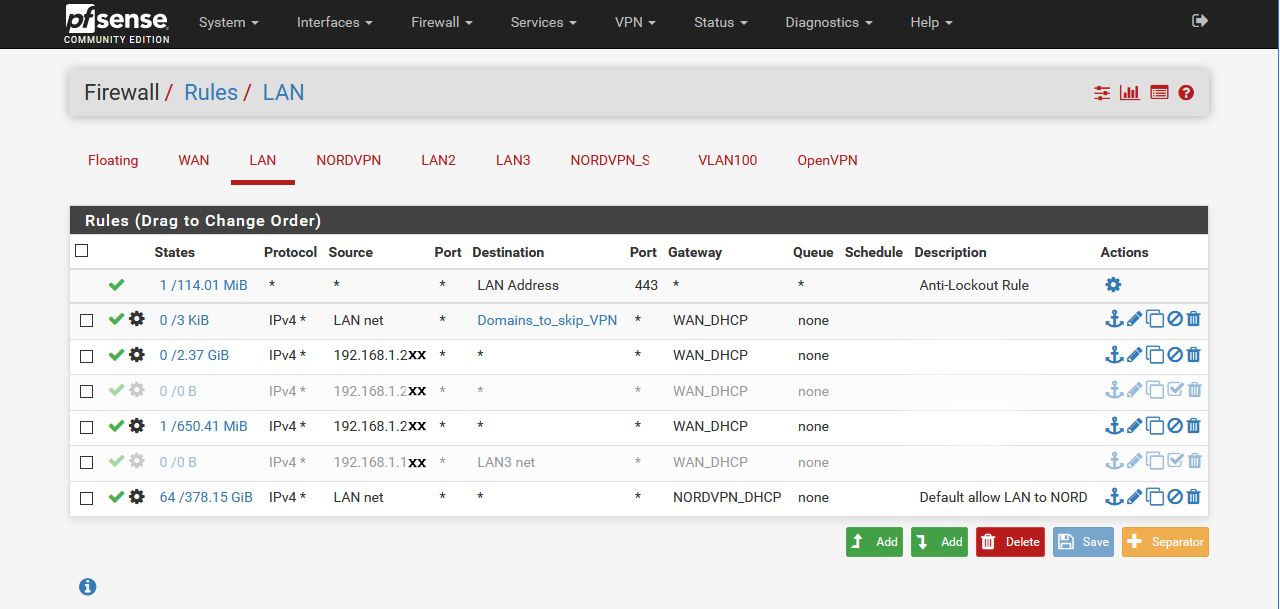
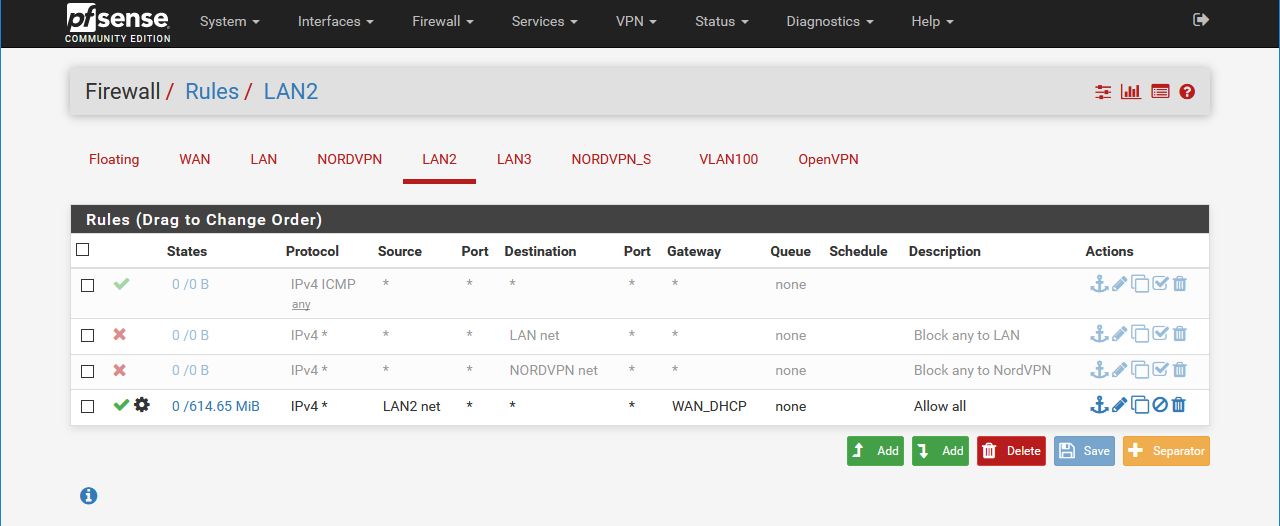
What I meant was under System > Routing > Gateways, I have now set the default gateway as WAN, as in your image above. I then went to Firewall > Rules > LAN2 and set up a rule with the gateway left to default. Though I also tested specifically with WAN set as the gateway. Show below (disabled).
Just to make sure I understand correctly and don't post stuff you don't need, when you say you want the routes, do you mean the rules for each interface (which has rules) under Firewall > Rules?
-
dude pfsense will NOT use rules you set on the interface.. Only clients hitting pfsense from that network will use them.
set your gateway as I showed in mine above vs using automatic.
And post up your routes
Do you see the default route there... That is what pfsense will use to talk outbound from itself.
If you wan to test if policy routes are working, etc. then you have to do the ping / trace from a client on that network - not from pfsense.
-
@johnpoz Understood. Also, ping/traceroute is now working from all interfaces. Though I'm not sure why it wasn't working at the time of my last post.
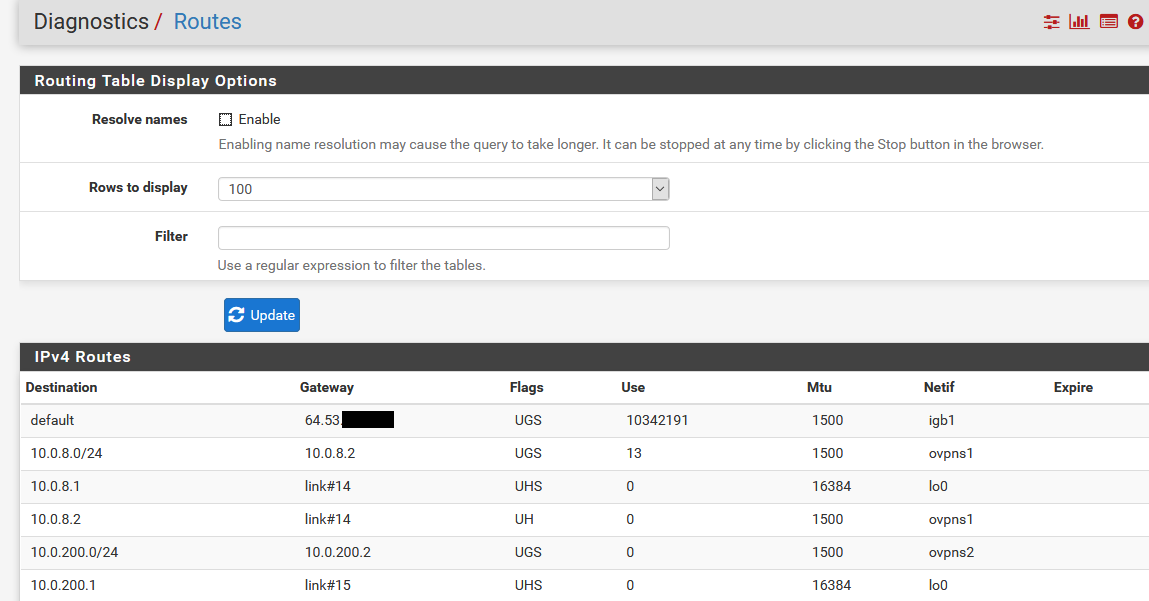
My routes anyway:
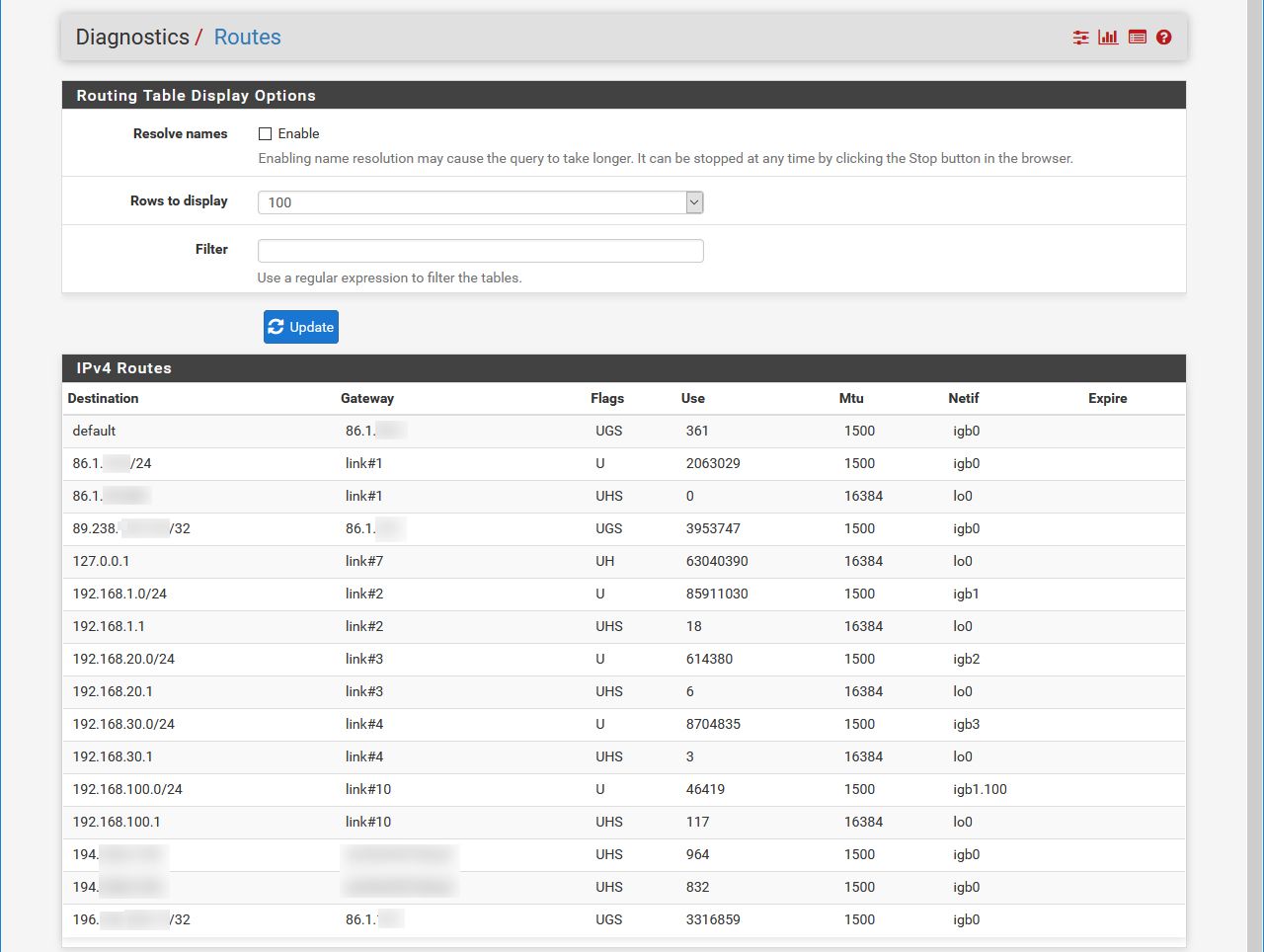
I suppose now I have both answers of getting ping working on the router and figuring out how to test
routingfirewall rules for each network by using a client in that network. And also a clearer understanding of pinging via interfaces.@johnpoz a hundred thank yous.
-
The only way to validate rules on an interface is to check from client on that network, you can not test them from pfsense directly.