Nat
-
And why was it send to you with
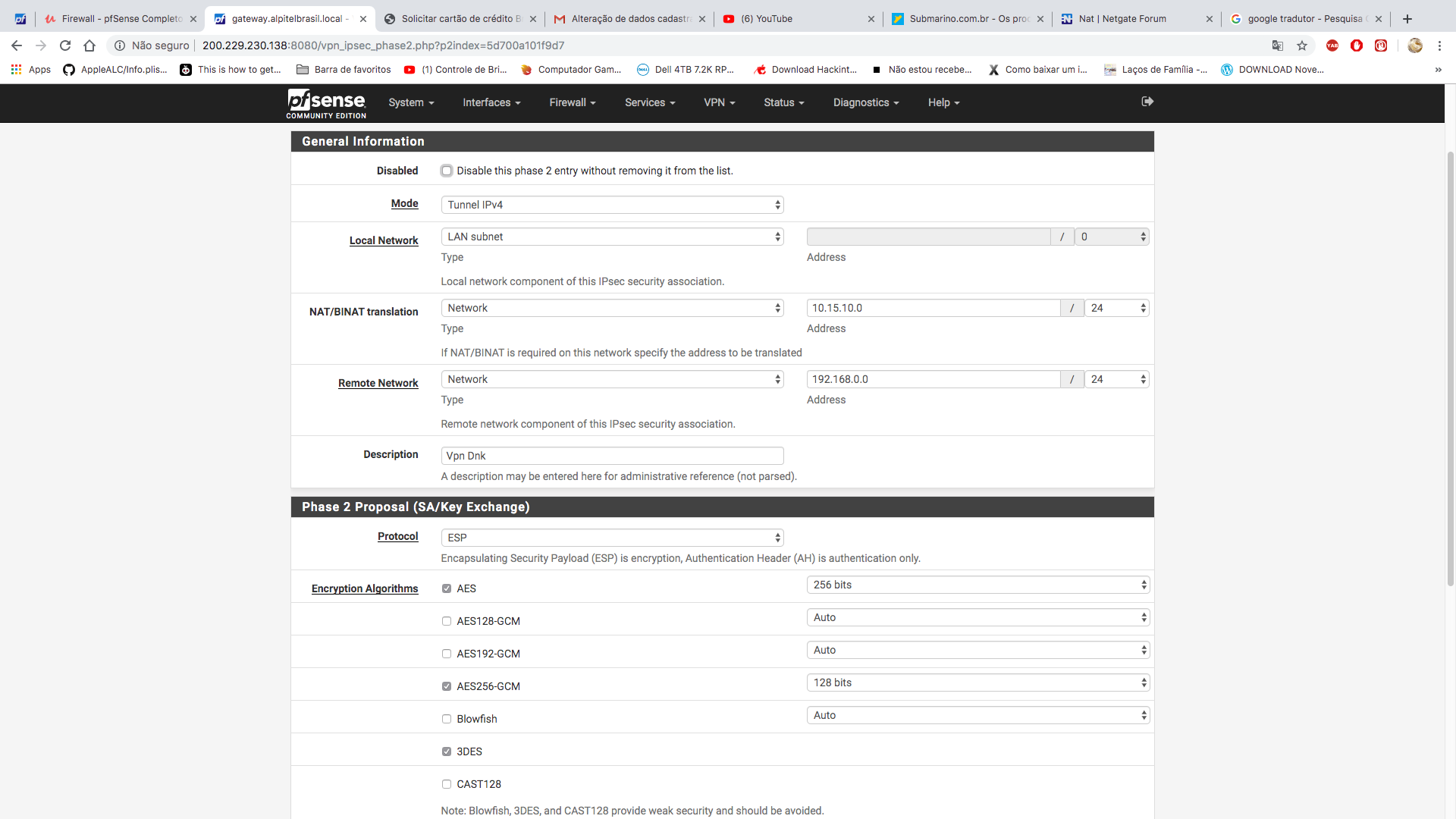
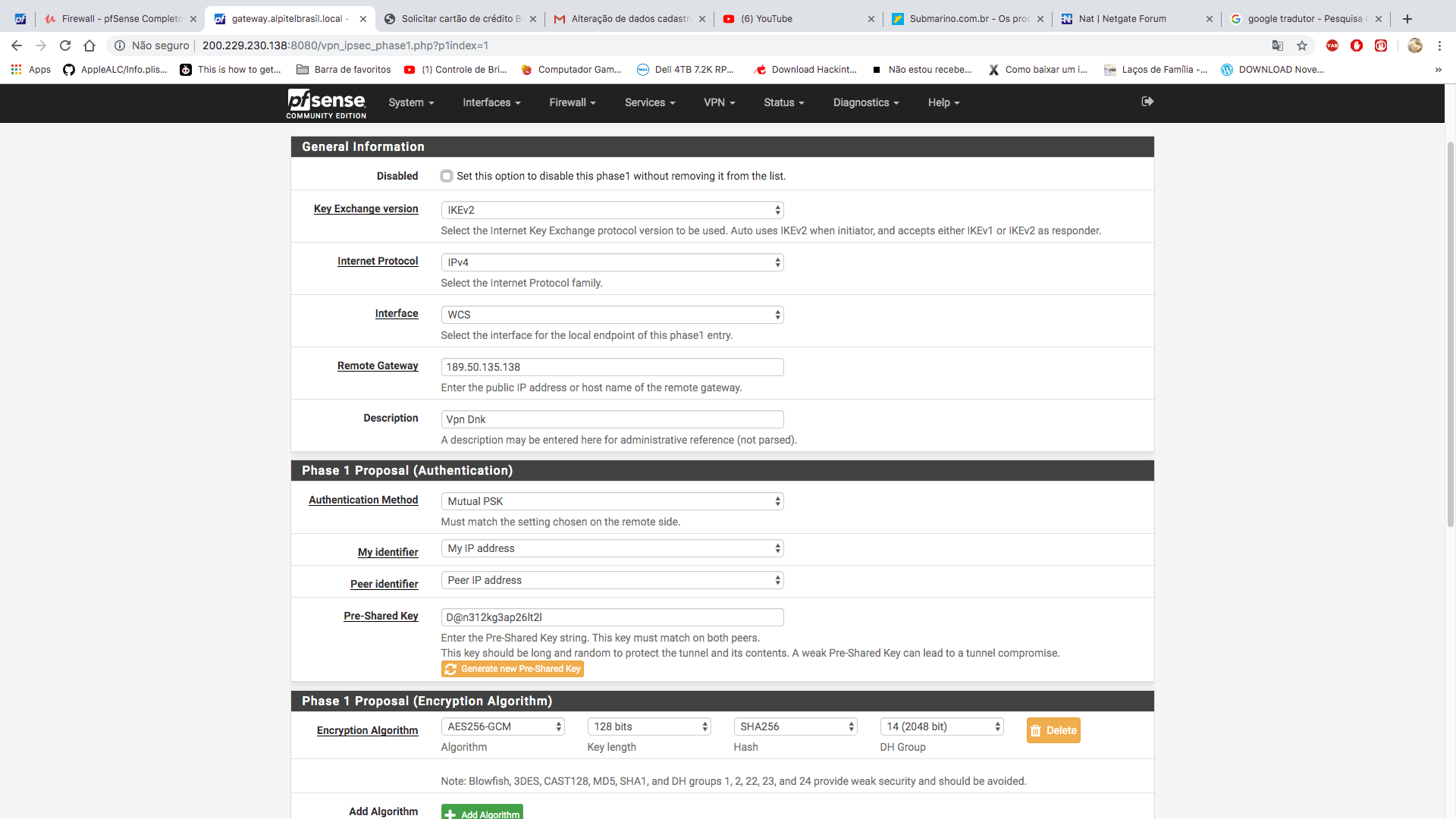
a) such bad settings when there are obviously better settings available!
b) why has the other side configured 10.15.10.0/24 as your remote network if you use 172.30.20.0/24?
c) why do they use bad/weak encryption in phase 2 if there are better possibilities?It simply doesn't make sense. You shouldn't just "mimic" configuration you get sent, if it's wrong or broken, question it instead of trying to bend you configuration in ways it shouldn't.
So I would call back and ask those 3 questions and ask for the settings to be corrected. The only thing that could be right is the "wrong" remote address subnet IF they have already 172.30.20.0/24 in use on THEIR side. Then configuring the BINAT setting in your phase 2 config is right. But unless that is confirmed, I'd reject that configuration as bad/wrong/insecure and ask why.
PS: nothing wrong being a "beginner". Everyone has to start somewhere. But don't try to run a bad/wrong configuration if you can just ask back to correct it (if possible).
-
To be honest, I'm kind of a layman at ipsec, I'm studying to understand better.
I believe the hardest I get, which is dripping 192.168.0.1
-
I will question them, and redo this rule
-
Thank you so much for your help, I will change my security and talked to them too.
-
As said above, try to insist to use at least
- AES-256 (CBC) or AES-256-GCM (better)
- IKEv2 (seems available)
- SHA-256 or SHA-384
- DH Group 20 (nist ecp384)
and the same in phase 2. Lifetimes 28800 and 3600 are OK.
@jimp or @johnpoz or any other global mods: Please move that topic to IPSEC as the NAT part is pretty much nonexistent and/or subject to a IPSEC connection - so nothing to do with classical inbound or outbound NAT settings :)
-
I already fixed

-
Remove the checkbox in front of 3DES so your connection will not simply downgrade if the other side wants to speak 3DES. Otherwise you'll still connect with that :)
Also many peers don't run IPSEC with AES-GCM yet (even in 2019 - a shame!) so be prepared to select AES256 (CBC) instead. Not that performant but secure nontheless. -
Thank you for your help.
unchecked the 3d
I already questioned the other side about the settings. -
@felipe_antocheski said in Nat:
protocol
OpenVPN is fast, flexible, and secure you should give it a try.
-
I already have and use the problem that when I connect with it I can't use my local network
-
Somehow I suspect that that answer was some spam-bot as it isn't related to anything written here. But
when I connect with it I can't use my local network
That would just be a simple OVPN configuration mistake. If that's still a problem - just ask in another topic and we'll deal with it then ;)