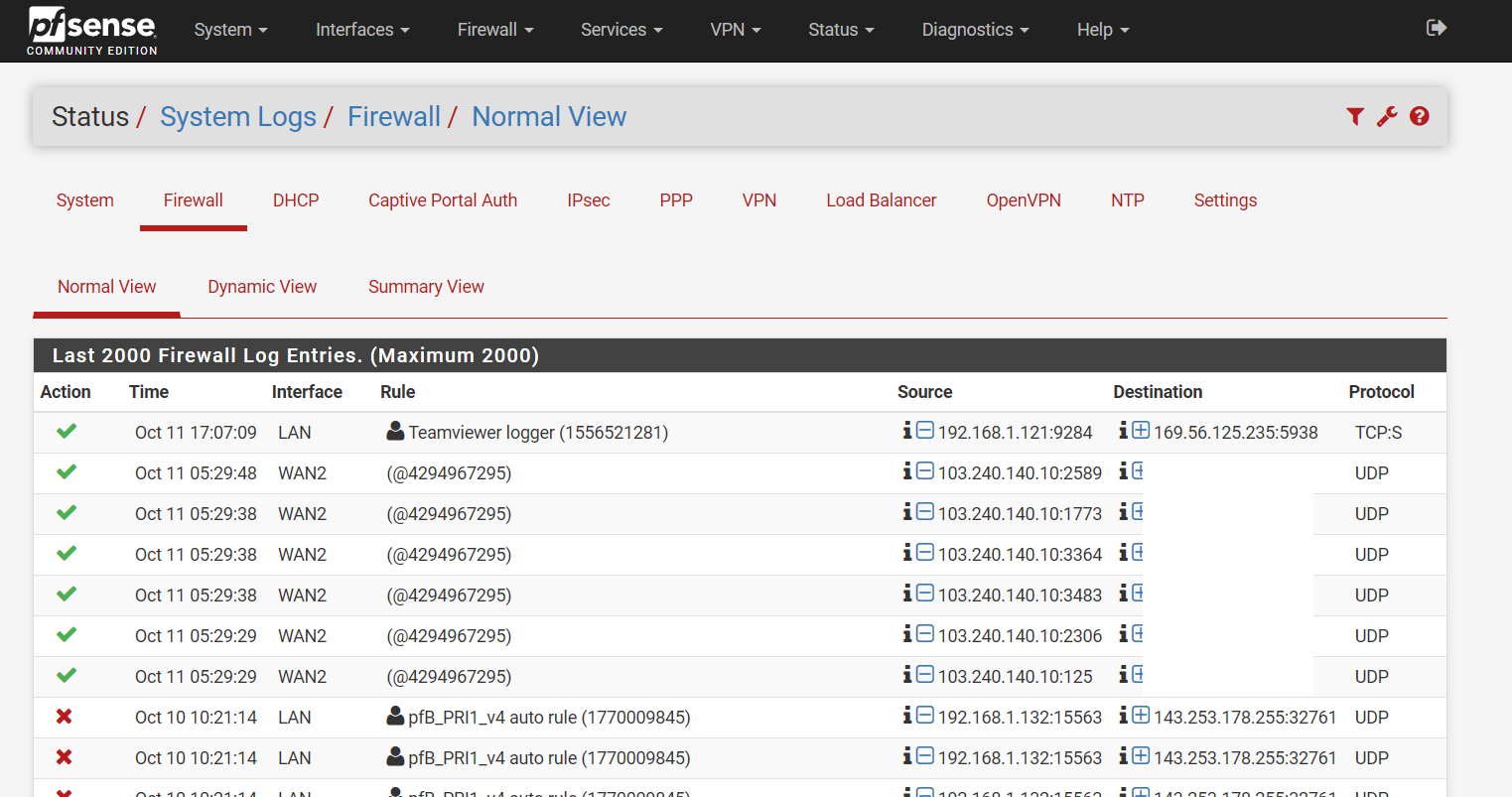
Had my pfSense been compromised?
-
@ASIC said in Had my pfSense been compromised?:
short,
I have no idea what that means... Have never seen that in the logs before.
Found this;
reason res - the reason that action was taken. Possible reasons are match, bad-offset, fragment, short, normalize, memory, bad-timestamp, congestion, ip-option, proto-cksum, state-mismatch, state-insert, state-limit, src-limit and synproxy.But not sure what "short" actually means?
edit: Ok looks there have been some that match on short (2) - but still not actually finding anything that describes what it actually means
[2.4.4-RELEASE][admin@sg4860.local.lan]/root: pfctl -s info Status: Enabled for 30 days 22:17:00 Debug: Urgent Interface Stats for igb0 IPv4 IPv6 Bytes In 350478233746 69232705 Bytes Out 1405455628533 1128183040 Packets In Passed 466867557 311496 Blocked 8876 1 Packets Out Passed 999590646 1171599 Blocked 0 0 State Table Total Rate current entries 404 searches 3535810440 1323.2/s inserts 15778842 5.9/s removals 15778438 5.9/s Counters match 16542390 6.2/s bad-offset 0 0.0/s fragment 64 0.0/s short 2 0.0/s normalize 21 0.0/s memory 0 0.0/s bad-timestamp 0 0.0/s congestion 0 0.0/s ip-option 125 0.0/s proto-cksum 0 0.0/s state-mismatch 2834 0.0/s state-insert 0 0.0/s state-limit 0 0.0/s src-limit 0 0.0/s synproxy 0 0.0/s map-failed 0 0.0/s [2.4.4-RELEASE][admin@sg4860.local.lan]/root: -
-
@bchan said in Had my pfSense been compromised?:
4294967295
Maybe because 4294967295(Dec) is equal to FFFFFFFF(Hex).
-
Ok so from research so fare
short packets dropped
Is that that is suppose to mean.. but why does it say passed then?
-
So there is no outbound traffic to 103.240.140.10 from some device that creates this return Allow temp rule? Since all return traffic is allowed? Create a rule that allows (but logs) all traffic to 103.240.140.10? (LOL, ignore as needed! :)
-
To be honest I think this is log of traffic that IP or transport header is too short.. But not sure why its saying pass... But I don't think that traffic is actually being passed to anything, not even pfsense.
-
Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35606,0,none,17,udp,27,103.240.140.10,IP_REMOVED,3266,990,7 Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35608,0,none,17,udp,27,103.240.140.10,IP_REMOVED,2427,389,7 Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35605,0,none,17,udp,27,103.240.140.10,IP_REMOVED,1862,1025,7 Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35607,0,none,17,udp,27,103.240.140.10,IP_REMOVED,570,995,7 Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35604,0,none,17,udp,27,103.240.140.10,IP_REMOVED,493,514,7 Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35609,0,none,17,udp,27,103.240.140.10,IP_REMOVED,2375,445,7 Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35602,0,none,17,udp,27,103.240.140.10,IP_REMOVED,162,546,7 Oct 13 09:14:13 pfSense filterlog: 4294967295,16777216,,0,pppoe0,short,pass,in,4,0x0,,245,35603,0,none,17,udp,27,103.240.140.10,IP_REMOVED,3871,547,7Here are the entries from my log file.
-
So it seems these are short, ie something wrong with them... But the question is why are they getting logged as passed.. If they are short - they should just be dropped.
-
@johnpoz if thats all it is it will be a relief as you saw on the screenshot above it looked like something had opened up all those ports.
What do I do now, is it worth reporting this somewhere for investigation?
-
-
I can't remember the last time I saw one marked
short. It might be a fragment. -
But the question is why is marked pass?
-
If it's a fragment that is part of an existing connection, it would be passed. It might be that the state recently expired or was purged for some other reason so it was passed in but NAT didn't get applied, for example.
-
I doubt its frag, since that is a different counter - see my output from
pfctl -s infoabove.
From the logs he lists I doubt its part of an existing connection.. From everything I find short should be dropped, so why is it logged as if it passed?
-
I'm not sure, unless it's being misinterpreted by
filterlog.If you can reproduce it reliably, you could capture the
pflogoutput directly and pipe it throughtcpdump(as described on https://www.openbsd.org/faq/pf/logging.html ) and see if that agrees. -
I can not tried to reporduce it, but you could prob for sure feed short packets via packet creation tool to try and duplicated the problem.
But seems a few users are seeing a bunch of them - as you can see from my counters I have only ever seen 2 of them... But don't recall ever seeming in the the log as pass.. will keep an eye if that counter goes up and see what my log says since feeding all logs to syslog now for retention.. But if get a chance will try and duplicate a short to pfsense and see if can try and see what it logs.
-
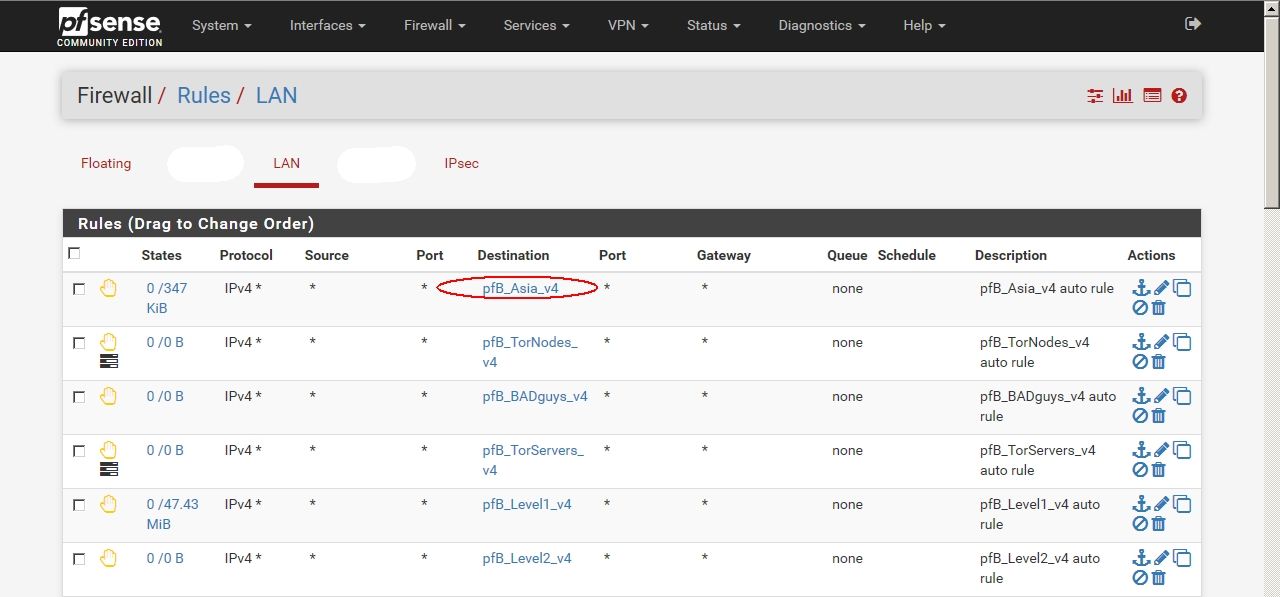
@jimp I have PfBlockerNG installed, and GeoIP Asia IP list, which includes 103.240.140.10, and it is applied as denied outbound connections on LAN, so there cannot be any existing connection to that IP.
-
@ASIC said in Had my pfSense been compromised?:
103.240.140.10
Are you blocking Hong Kong ?
andy@mac-pro ~ % whois 103.240.140.10
% IANA WHOIS server
% for more information on IANA, visit http://www.iana.org
% This query returned 1 objectrefer: whois.apnic.net
inetnum: 103.0.0.0 - 103.255.255.255
organisation: APNIC
status: ALLOCATEDwhois: whois.apnic.net
changed: 2011-02
source: IANAwhois.apnic.net
% [whois.apnic.net]
% Whois data copyright terms http://www.apnic.net/db/dbcopyright.html% Information related to '103.240.140.1 - 103.240.142.255'
% Abuse contact for '103.240.140.1 - 103.240.142.255' is 'abuse@clear-ddos.com'
inetnum: 103.240.140.1 - 103.240.142.255
netname: CTCL-HK
descr: ClearDDoS Technologies
country: HK
admin-c: CTCL1-AP
tech-c: CTCL1-AP
status: ASSIGNED NON-PORTABLE
mnt-by: MAINT-CTCL-HK
mnt-irt: IRT-CTCL-HK
last-modified: 2014-09-28T08:41:28Z
source: APNICirt: IRT-CTCL-HK
address: Flat C, 23/F, Lucky Plaza,, 315-321 Lockhart Road, Wan Chai, Hong Kong, Hongkong Hongkong 999999
e-mail: abuse@clear-ddos.com
abuse-mailbox: abuse@clear-ddos.com
admin-c: CTCL1-AP
tech-c: CTCL1-AP
auth: # Filtered
mnt-by: MAINT-CTCL-HK
last-modified: 2013-08-06T10:03:29Z
source: APNICrole: CLEARDDOS TECHNOLOGY CO LIMITED administrator
address: Flat C, 23/F, Lucky Plaza,, 315-321 Lockhart Road, Wan Chai, Hong Kong, Hongkong Hongkong 999999
country: HK
phone: +86 755 8453 0553
fax-no: +86 755 8453 0553
e-mail: abuse@clear-ddos.com
admin-c: CTCL1-AP
tech-c: CTCL1-AP
nic-hdl: CTCL1-AP
mnt-by: MAINT-CTCL-HK
last-modified: 2013-08-06T10:03:28Z
source: APNIC% This query was served by the APNIC Whois Service version 1.88.15-46 (WHOIS-UK4)
andy@mac-pro ~ %
-
@NogBadTheBad said in Had my pfSense been compromised?:
@ASIC said in Had my pfSense been compromised?:
103.240.140.10
Are you blocking Hong Kong ?
Yes, I am.
-
Just thought I'd check as some people think Hong Kong is China