Setting up a VLAN with pfSense, Ubiquiti, and ESXi
-
@pfSenseUser78 said in Setting up a VLAN with pfSense, Ubiquiti, and ESXi:
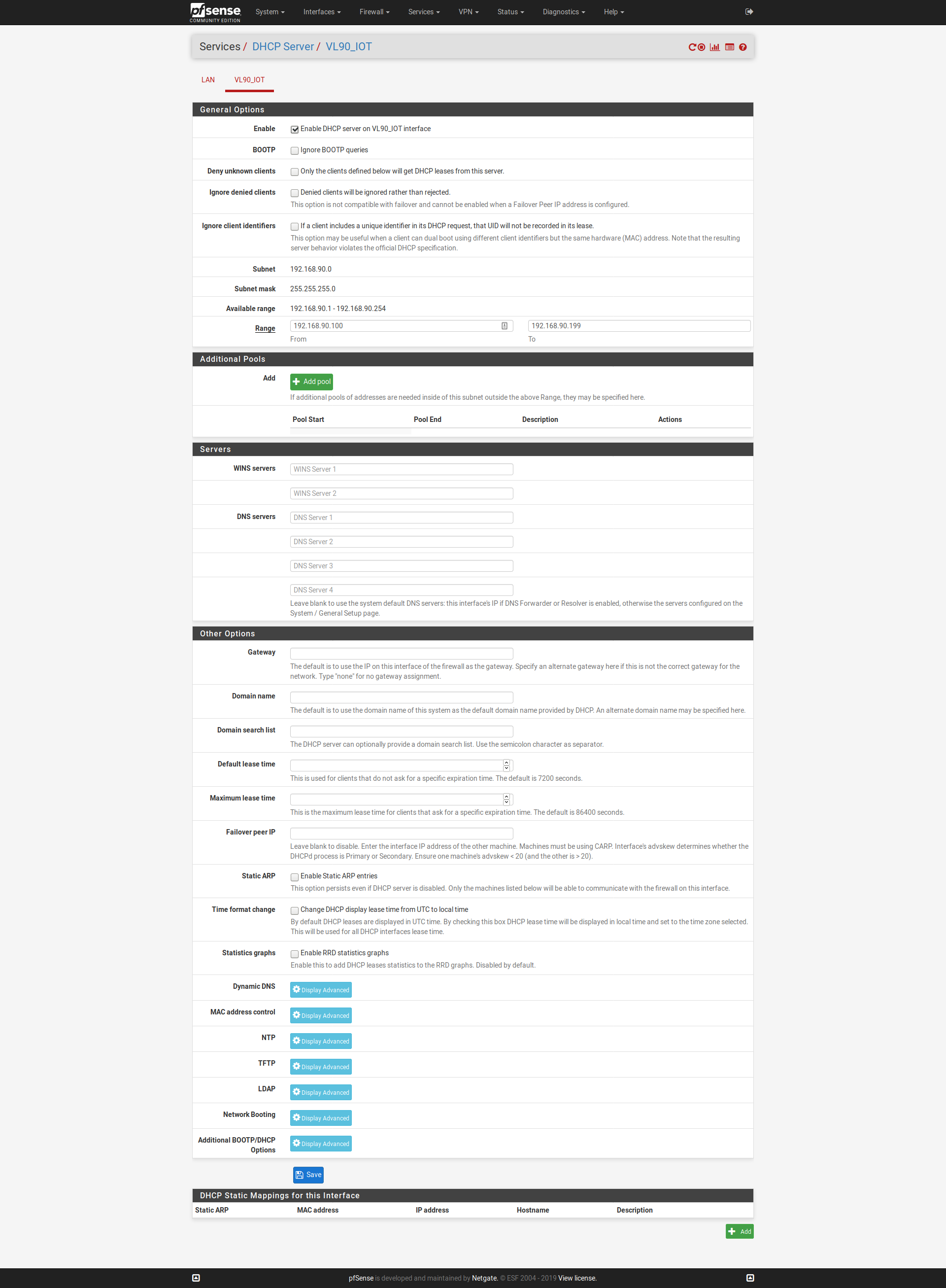
For the internal NON-IoT network DHCP is handled by a windows domain controller. For the VLAN being setup for the IoT devices I do NOT need DHCP handled by a windows DC; I was saying that this can be handled by pfSense directly.
Then we're back to my original question, did you set up the DHCP config on the VLAN? In the DHCP config, there are pages for each interface. The way I read your original post, it sounded like you just added an address pool to the main interface.
-
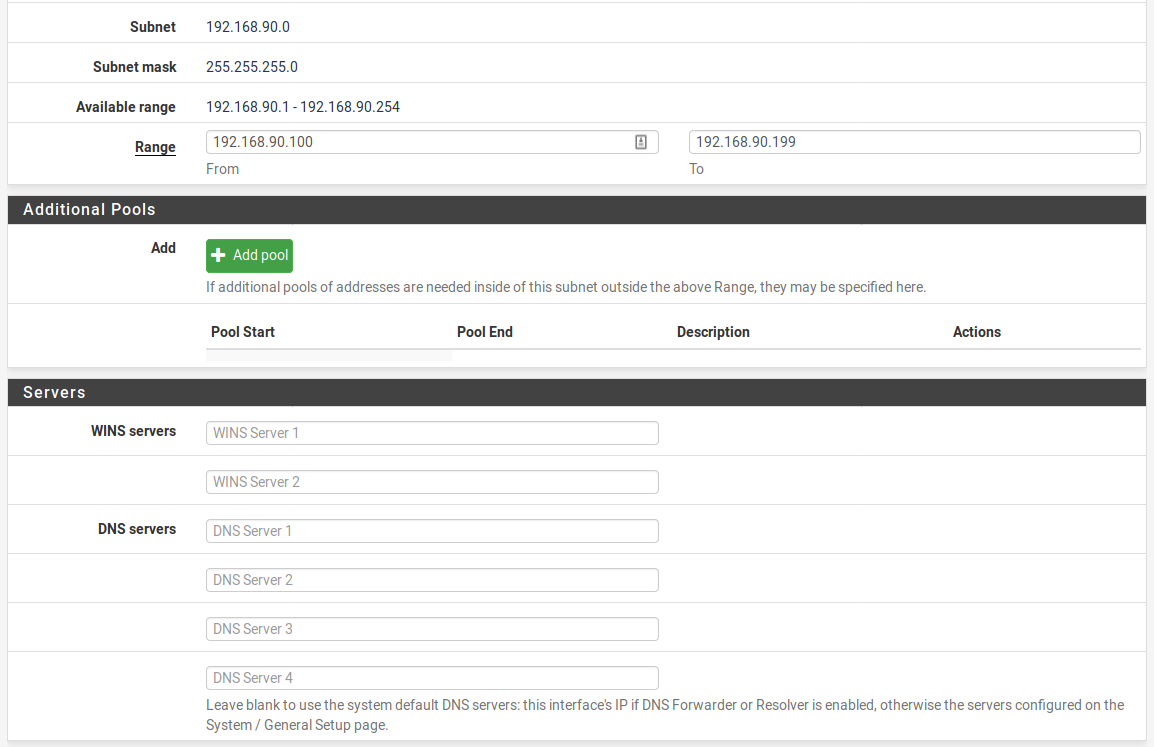
So this is what I have for DNS in the VLAN DHCP config:
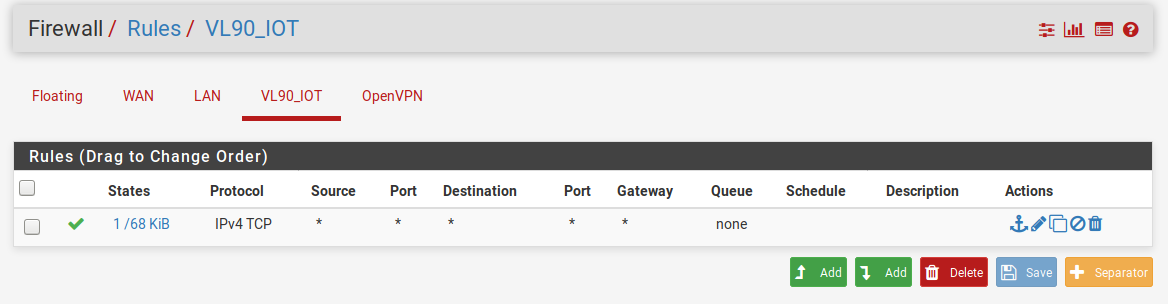
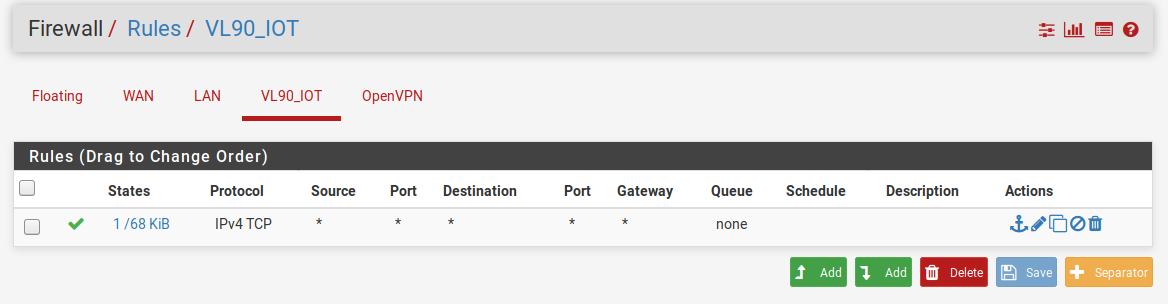
I have this as a firewall rule:
When I connect to the network on my iPhone I connect and get an IP address, however, the spinny thing next to the network name never goes away. If I try to load a website, nothing happens. If I manually specific a DNS server, nothing happens. Note that on my non-VLAN network I have a rule blocking all DNS traffic that doesn't originate from one of the two internal servers; not sure if this would be affecting a VLAN on a different IP range or not (the greyed out rule was a failed attempt to redirect errant DNS queries back to one of the two internal DNS servers at 105 or 106 - 78 & 79 are there for other reasons):

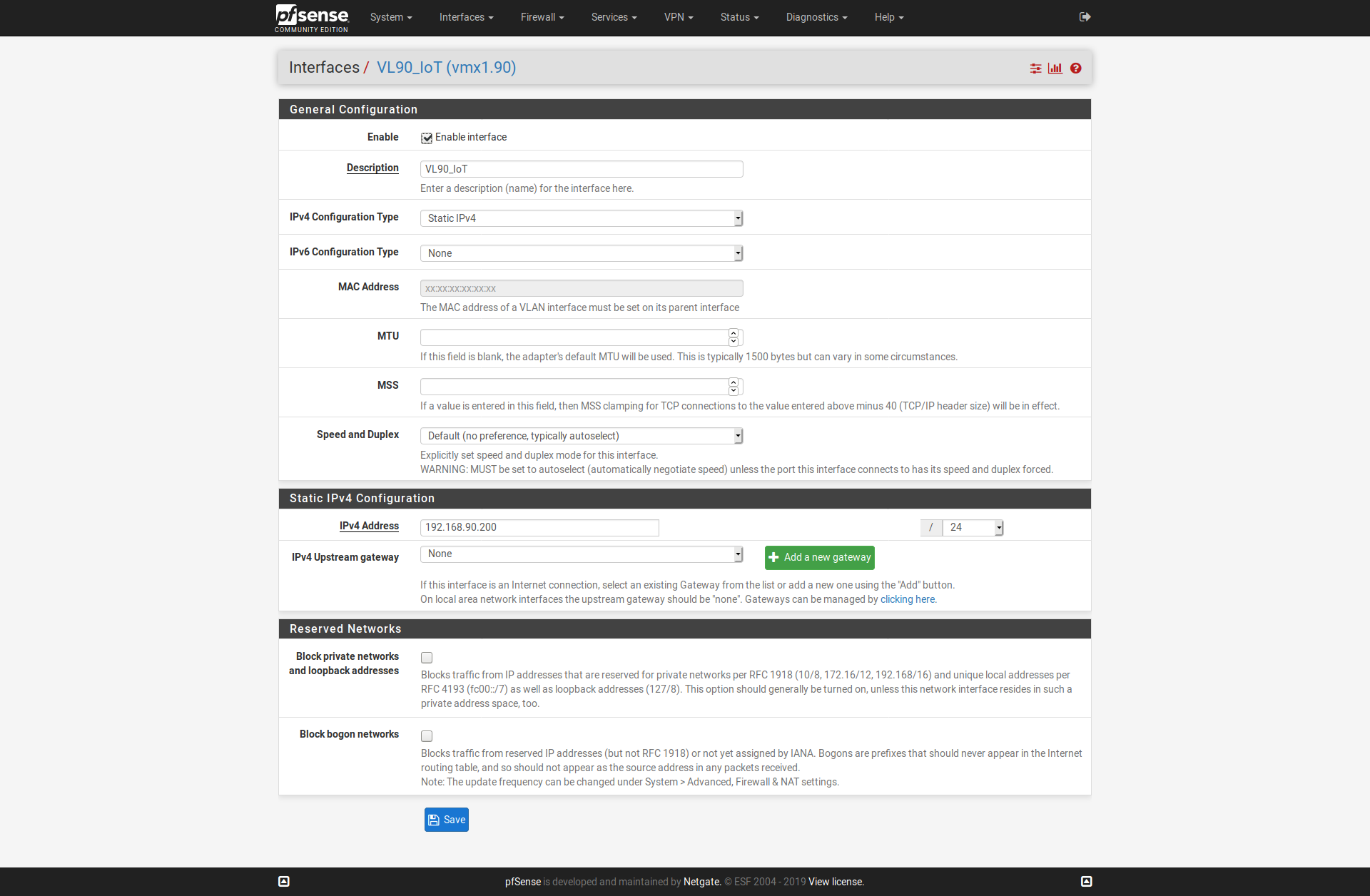
And here is the DNS servers setup in general:

Please let me know if there is any additional information I can provide; I greatly appreciate everything so far.
-
@JKnott said in Setting up a VLAN with pfSense, Ubiquiti, and ESXi:
@pfSenseUser78 said in Setting up a VLAN with pfSense, Ubiquiti, and ESXi:
For the internal NON-IoT network DHCP is handled by a windows domain controller. For the VLAN being setup for the IoT devices I do NOT need DHCP handled by a windows DC; I was saying that this can be handled by pfSense directly.
Then we're back to my original question, did you set up the DHCP config on the VLAN? In the DHCP config, there are pages for each interface. The way I read your original post, it sounded like you just added an address pool to the main interface.
.
..
Hope this helps - if not let me know what else I can provide a screenshot of.
-
You are not setting DNS servers in the DHCP configuration so this is what DNS servers will be sent to the clients (just like it says right there):
Leave blank to use the system default DNS servers: this interface's IP if DNS Forwarder or Resolver is enabled, otherwise the servers configured on the System / General Setup page.
So it depends on whether or not you have the resolver or forwarder configured, in which case the clients will get 192.168.90.200 as their DNS server. If DNS forwarder/resolver are NOT configured, they'll get whatever is configured in System > General.
-
Here's what's set as my DNS servers in System > General:
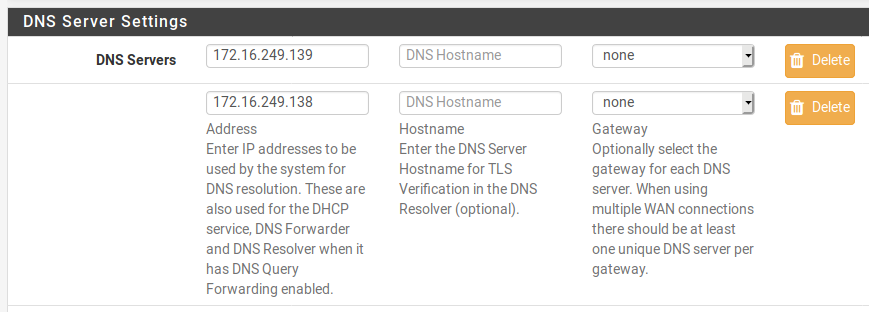
Could it be that the VLAN devices can't connect to the DNS servers?
-
Look at the DNS servers the clients are being assigned. Can the resolve names from them? If not, then yest that's a problem.
-
@Derelict DNS server being assigned to the clients is the firewall itself (172.16.249.200).
-
Can they resolve names using that?
-
Ok. I can connect to the network (via WiFi) with my laptop. I get an IP address on the VLAN range. From there, I cannot ping 8.8.8.8 and I can't ping 192.168.90.200 (which should be the VLAN Firewall).
Not being able to ping 8.8.8.8 tells me I might have a rule issue somewhere. I know I have one to block DNS queries on my main network (172.16.249.1/24) that don't originate from one of two DNS servers (on that same network) but that shouldn't block me from pinging 8.8.8.8.
-
Vlans when created have zero rules on them - so not being able to do anything would be default.. What rules did you put on your vlan interface? Just that tcp rule, well no you wouldn't be able to do dns which is udp normally, and no you wouldn't be able to ping which is icmp..
-
Two things:
- Rules on the new interface passing traffic from the hosts on that interface.
- Outbound NAT on the WAN for the new interface source addresses if you strayed from Automatic or Hybrid outbound NAT.
Those two things are installed by default on the LAN but not for any interfaces you might subsequently create.
-
@johnpoz Makes sense, where would I find the rules I need to create? I've searched but I've not been able to find what they are.
Edit: I've also looked at the default rules and don't see what get setup to try and duplicate on the VLAN.
-
@Derelict I've read and reread these a couple of times and am having a hard time understanding. I have an "ok" grasp of networking but these just don't make sense.
Is there somewhere I can read more about these two points?
-
They would be what you want - there is no possible way to show someone the rules that they would want.. Everyones setup is going to be different. I would start with an any any rule to validate connectivity works, and then set them how you want them.. My rules are going to be different than your rules, etc.
edit?
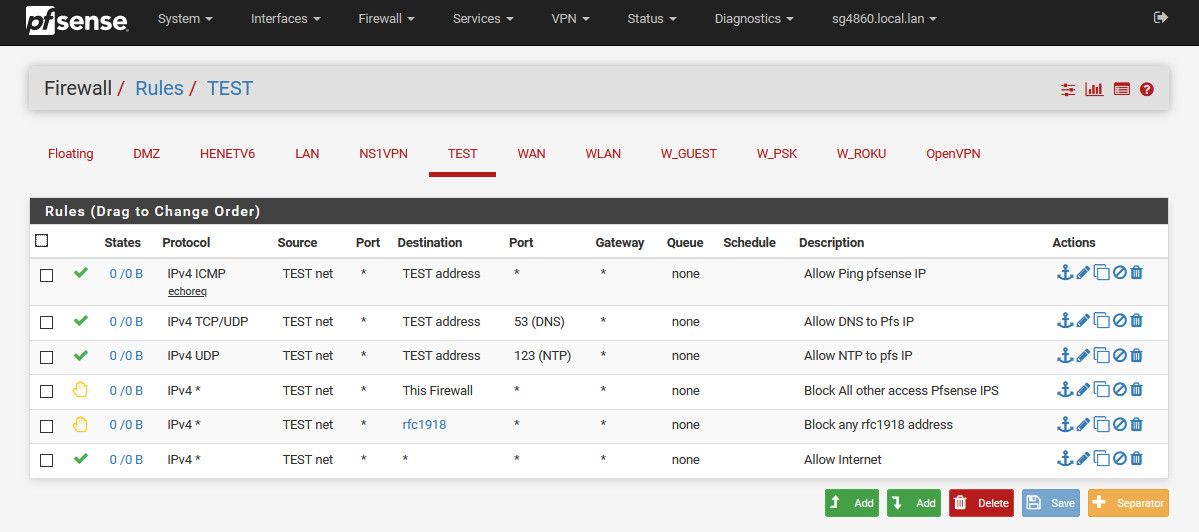
You don't know how to setup a any any rule??Here is basic vlan rules that allows basic services but blocks access to all other vlans (rfc1918)..
-
-
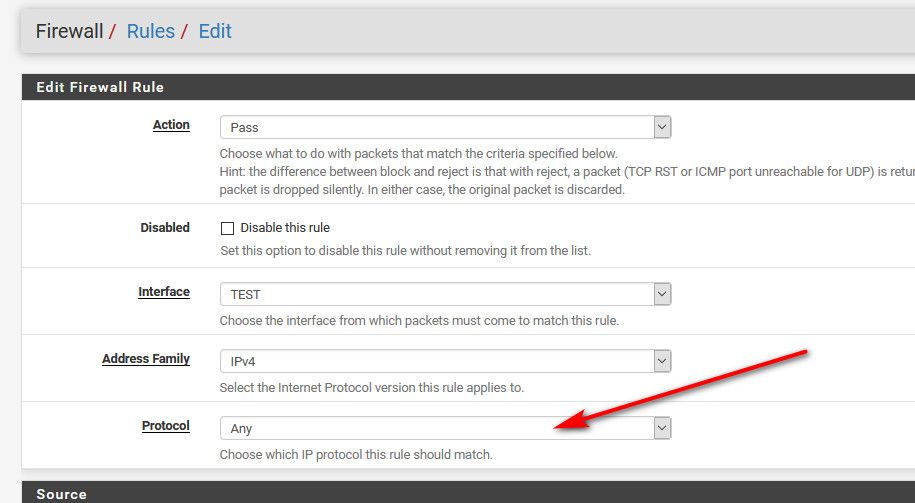
That is not an ANY rule - its only allowing tcp.. So no dns which is udp, and no ping which icmp.
-
Got it now.
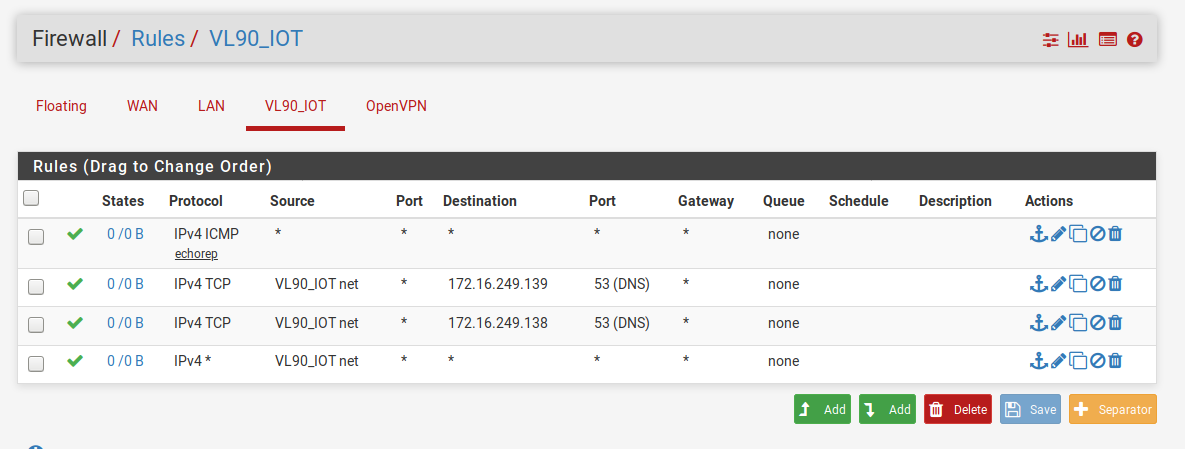
I've created this an will test tomorrow; the goal is to allow the devices on this VLAN access to the internet and access to the specified DNS servers on the local LAN (I hope that term is correct):
-
You have dns set to TCP only - while dns CAN use tcp, it defaults to UDP... You reallly should make those rules UDP/TCP
But since you have any rule there at the bottom those 2 allow rules for dns are pretty pointless.
And that any rule at the end is going to allow access to your lan as well.. You need to put a block rule above the any and below your dns rules, that blocks access your LAN net, if you dont want your vlan to talk to your lan..
Rules are evaluated as traffic enters the interface from the network its attached too, top down, first rule to trigger wins, no other rules are evaluated.
-
Ok, I think I'm getting closer. Here's the new rules:
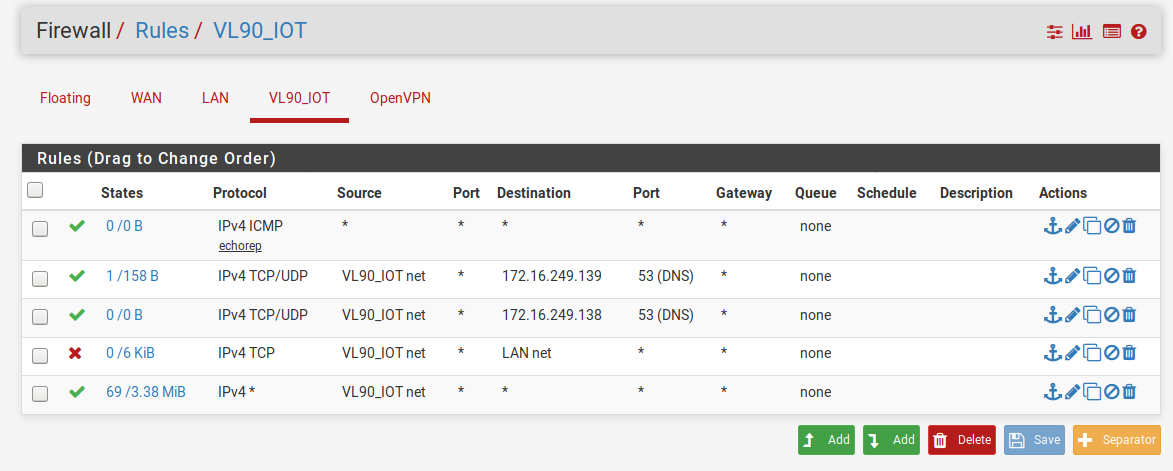
If I understand correctly the rules flow from the top down to the bottom. I'm allowing (on the VLAN90):
-
Ping responses anywhere (but should probably tighten this up to only allow responses out to the internet if I'm trying to segregate this traffic from my internal LAN)
-
DNS traffic ONLY to 172.16.249.139 and then .138
-
Blocking all communication from the VLAN90 to the local LAN
-
All connectivity out to the internet (although, like rule 1, I'm guessing that this rule is too broad and can be tightened up).
For rules 1 and 4, to "tighten" them up to be just applicable to the internet would I change the destination to "WAN net"?
-
-
Wan net is not the internet - its just the network connect to your wan.. It would be something/mask like mine is 64.53.x.x/23 The internet is really anything.. There is no way to tighten that up... Can you put in all address blocks that make up the internet ;)
If you don't want clients on your vlan to ping stuff on your lan, then put a rule that blocks that before you allow ping any..
If you want to tighten it up more, you might want to use the "this firewall" alias to prevent access to your wan IP, this alias includes all IPs that firewall has, a block rule to that on your vlan would prevent access to say the pfsense gui via the wan IP.. See my example rules.
If you ever have a question to if something is allowed or deny, just run through the rules with where your going and what protocol.. Is it denied or allowed in the rules - if it gets to the end without being allowed then it would be denied.. Since the default is denied (not shown).