Local Network can't ping VPN IPv6 remote
-
Hi guys, hope all is going well
Hoping you can give me a hand I have an issue I am not being able to get around.
I have IPv4 and IPv6 working well. I added a new config for OpenVPN, everything is working with IPv4, but not with IPv6.
The IPv6 connection is up:
-
I have a local address attributed and from WAN and VPN interface I can ping IPv6 destinations outside from both;
-
From my LAN interface I can ping the local IPv6 address attributed to the VPN interface;
-
From my LAN interface I cannot ping the remote IPv6 address/gateway.
I have been around my NAT config, it seems OK afaik, firewall rules the same are identical on LAN I have two rules one for IPv4 and another for IPv6. Firewall logs show nothing in this regard.
Maybe its the hour but I'm out of ideas. Anyone got a clue?
Thanks!
-
-
Why are you using NAT for IPv6?
-
Well that's an interesting question I didn't give much thought.
So I followed a tutorial, and the tutorial says:
In menu, go to Firewall >NAT > Outbound
Click on Manual Outbound mode. (I chose hybrid)
Press Save and after that Apply ChangesYou will get a set of rules in Mappings.
You have to duplicate each of them, and change Interface from WAN to VPN_CON.
The duplicate icon is the two squares one over another next to the pencil icon.
Press Apply Changes.And so I duplicated each of them, so this is what I got:
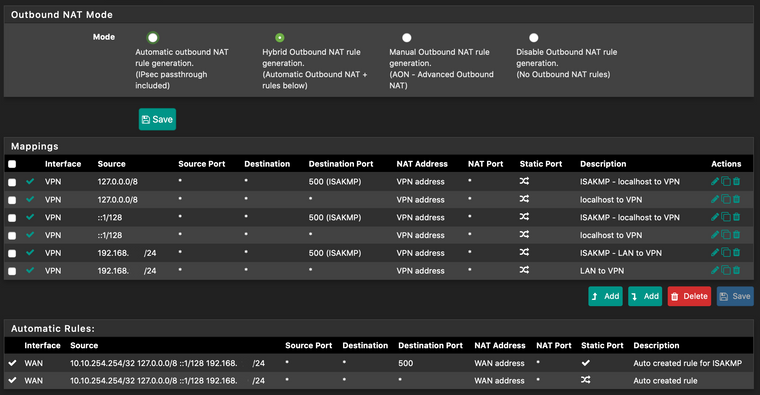
So, I didn't really think of it. I simply duplicated existing rules.
Why is an IPv6 rule there in the first place?Anyway, I disabled the ipv6 rules, and I can't ping outside IPv6 from LAN.
-
Was that tutorial for IPv6 or IPv4? I run OpenVPN between my notebook computer and home network and have no need for NAT on IPv4 or IPv6. I have NAT only on my WAN connection for IPv4. Between my VPN and home network it's just plain routing.
-
The tutorial was for IPv4 but the v6 entry was already there (one, that I then duplicated as per the tutorial mentioned), I assumed OK since I am using IPv6.
As I mentioned previously, I simply applied the same logic. And I repeat, I have tested disabling those rules, and it makes no difference what so ever.I don't run OpenVPN on my machine. the VPN is established on the router to an external provider and all the network traffic goes there.
So all of these are from the router to an external provider.This configuration on IPv4 has been working for an year without issues, with that configuration as shown above.
Now my VPN provider recently added IPv6 support, and I changed the configuration of the OpenVPN client accordingly. It connects successfully, AND:
- I can ping, from my computer, the IPv6 address set to local VPN interface;
- From the local VPN IPv6 I can ping the remote peer IPv6;
- From either my machine or local LAN interface I CANNOT ping the remote IPv6.
And again, I must repeat, I disabled the two ::1/128 rules, made no difference.
-
You didn't mention you were going through a provider. That is a critical point, when we're trying to help you.
-
Ok, now you got it. Sorry if I wasn't clear in that.
-
Problem solved.
I had to add a new rule to NAT alike the previous for my IPv4 LAN, but with the /64 attributed to me.
If it doesn't belong there, I'll wait for someone that is able to explain why there is space for v6 NAT rules and why after adding my /64 all started working.
-
Perhaps you can start by explaining why you think you need to use NAT. Do you not have multiple /64 prefixes available, so that you can assign 1 to the VPN? I get a /56 from my ISP, which is 256 /64s. I use 1 for my LAN, 1 for the VPN and 1 for testing. PfSense supports doing that and it is the proper way to set things up.
-
Dude I don't need to start explaining a thing. You're the one saying things are wrong, I followed a tutorial, I have a /64 attributed for my LAN, I don't assign nothing to the VPN, as that both the peer IPv6 remote and local are dynamically attributed by the provider's server.
You came saying those rules didn't belong there that was the problem, giving example of your notebook and whatnot which wasn't even remotely close to what was going on here, if you had read the first post correctly you'd probably get that first hand.
So no, I do not have multiple /64 prefixes, I have one for my LAN that works perfectly without VPN, and upon shifting the VPN to also support IPv6 I lost connectivity. All you did was flooding this topic with zero info, zero debug suggestions, kept insisting on the NAT, or insisting in saying nothing useful, where actually there was an issue, as there was one needed rule that wasn't there.
Now if you have nothing useful to say (as you didn't), please remain quiet. I don't have to explain nothing because in fact I am no expert in IPv6, but found the issue and solved it, which is much better than just saying ... what was the great feedback you provided, really?
“It is better to remain silent at the risk of being thought a fool, than to talk and remove all doubt of it.”
Maurice Switzer -
Using NAT on IPv6 is wrong. NAT is a hack to get around the IPv4 address shortage and it breaks some things in the process. Using NAT because you don't know better is not an excuse. I could understand using NAT for a VPN, if you only had a single /64 from your ISP and that's why I asked if your ISP provides more than 1 /64. This is a perfectly valid question, to clarify your situation, so that we can provide a solution.
As for being an expert, I have been working with IPv6 for almost 10 years. Further, when I had a problem with my ISP last year, I was having to educate the ISPs tier 2 support and senior tech on IPv6, because their knowledge was lacking. I am also a Cisco CCNA.
BTW, if you want to learn about IPv6, the book IPv6 Essentials is an excellent reference.
-
Foh sure. I never asked for credentials. You're very well educated except you never seem to give a right answer around here, from what i've seen, but honestly, I don't care.
My issue here was exclusively by how pfSense handles this. The tutorials of my provider are absolutely correct on how to configure the OpenVPN client, takes 5 minutes, it was configured for over an year, the change I added was setting "both [IPv4 & IPv6]" option on the client, the VPN interface gets a gateway, and attributed address, I can reach my local attributed address, can't ping the remote from my machine, can ping from the local attributed address to the remote, and can ping the local attributed from my machine. So for traffic flow, something was missing.
I don't give a rats ass if you're CCNA which isn't that big of a deal that's the entry level test, but maybe you should stick to replying about Cisco then, because clearly (and given some of your other answers) you like to say "your notebook" a lot and add noise to conversations.
When you are able to explain, since you're such an educated genius on IPv6 AND pfSense, what was the constrain here, since by your words (here and on other topics) everything "it's just plain routing" - but the plain routing doesn't work our of the box.A good professional makes the right questions. You made no questions, only assumptions, didn't even understood the Original Post, which I asked a couple of people in the meanwhile and all understood that was between a pfSense router and an external provider. Again, as you talk more and more, the more we get to know you.
Take care.
-
Your original post included NAT. NAT is a bad idea that really shouldn't be used. As another regular here often says, that sort of solution is "borked". As for pfSense vs Cisco, it makes no difference. NAT is a bad idea either way. You say you know little about IPv6. Well maybe you should be listening to someone who has lots of experience with it.
-
Yeah for sure. Next time try to be useful bc nothing you say is a solution, nor with such a genius you have exposed how to attain the correct configuration without adding the routes to NAT. But you won't, cause all you do is noise. Take the bicycle and have a merry xmas, i'm done with you. ffs.