WAN1<>LAN1, WAN2<>LAN2, no cross traffic allowed
-
Hello all,
i just found very old posts which have similar request
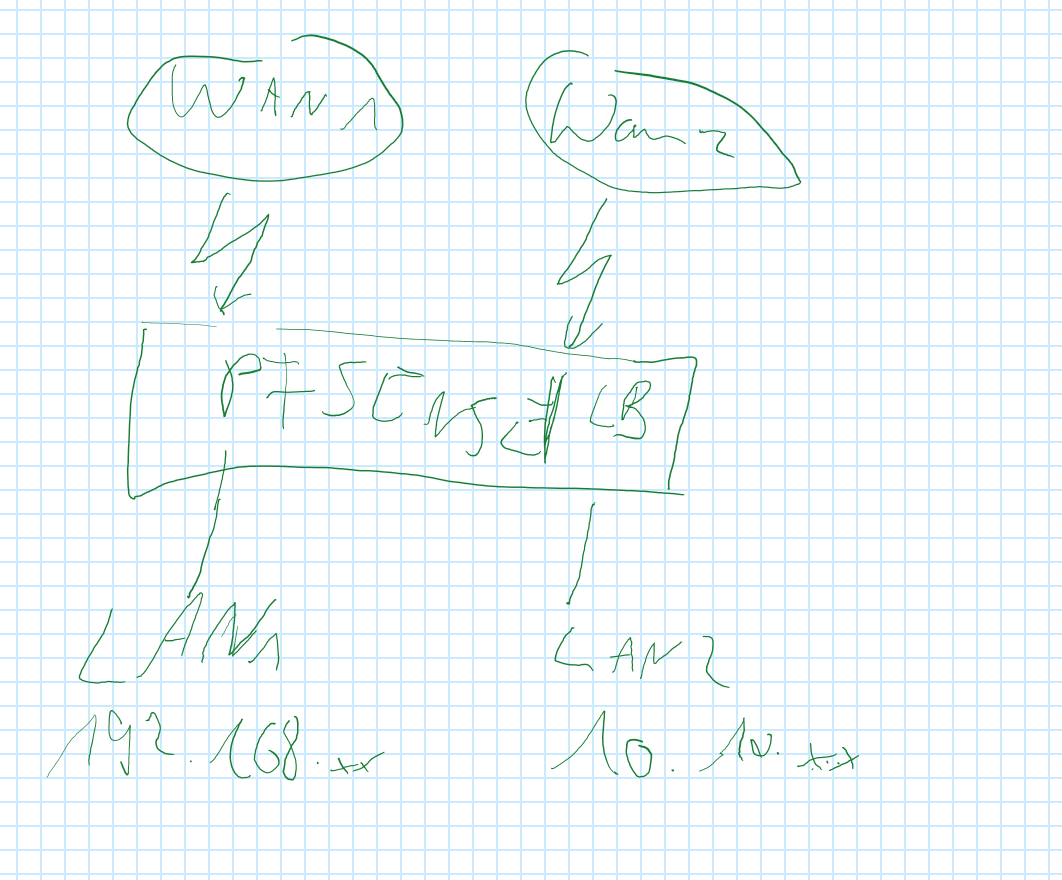
i have 2 WAN Interface (on an ESX, 2 portsgroups which are mapped each to one IP) and 2 LAN (one Prod - 192.168.x.x and the second Test 10.10.x.x with openshift).
the public DNS Zones will be managed by myself. i want now the traffic coming over WAN1 forwarded ONLY to LAN1 and WAN2 to LAN2. no crosstraffic (like if i have 2 separate firewalls). also answer should go over the same Interface as it came from. sure, i have only one gateway address.
i have read some of the pfsense and i am impressed about how many the app can do, so i am pretty confident that this easy challenge should not be a problem.
thx guys -
@pille99 said in WAN1<>LAN1, WAN2<>LAN2, no cross traffic allowed:
also answer should go over the same Interface as it came from. sure, i have only one gateway address.
So you have only one WAN subnet where you have both WAN interfaces connected to?
That makes no sense. The way to go here is configuring both WAN IPs on one interface. Add the second as "IP alias".@pille99 said in WAN1<>LAN1, WAN2<>LAN2, no cross traffic allowed:
i want now the traffic coming over WAN1 forwarded ONLY to LAN1 and WAN2 to LAN2. no crosstraffic (like if i have 2 separate firewalls).
You can forward the one IP to LAN1 and the other one to LAN2 by NAT port forwarding rules. pfSense translates the source IP in responses automatically to the origin destination address. You there is no need to care about.
If you want also separate your outbound traffic, so that upstream traffic from LAN1 gets the one WAN IP and traffic from LAN2 gets the second WAN IP, you can do that by Firewall > NAT > Outbound on pfSense.
By default the outbound NAT is managed automatically and pfSense adds a rule for LAN subnet translating upstream traffic to WAN address. So you have to activate the hybrid mode first. Then add a rule for the WAN interface, with source = LAN2 net and translation address = your second WAN IP.To avoid communication between the two LANs add block rules to both LAN interfaces, blocking access from the particular other LAN.
-
Yes, this should be two IPs. Two interfaces in the same subnet is not valid.
If you really want them completely separate and it's running in ESXi then you could just use two pfSense VMs.
Though I notice you have the firewall labelled as "pfSense LB", is it running as a load-balancer?
Steve