domain name pointing to home server blocked on LAN
-
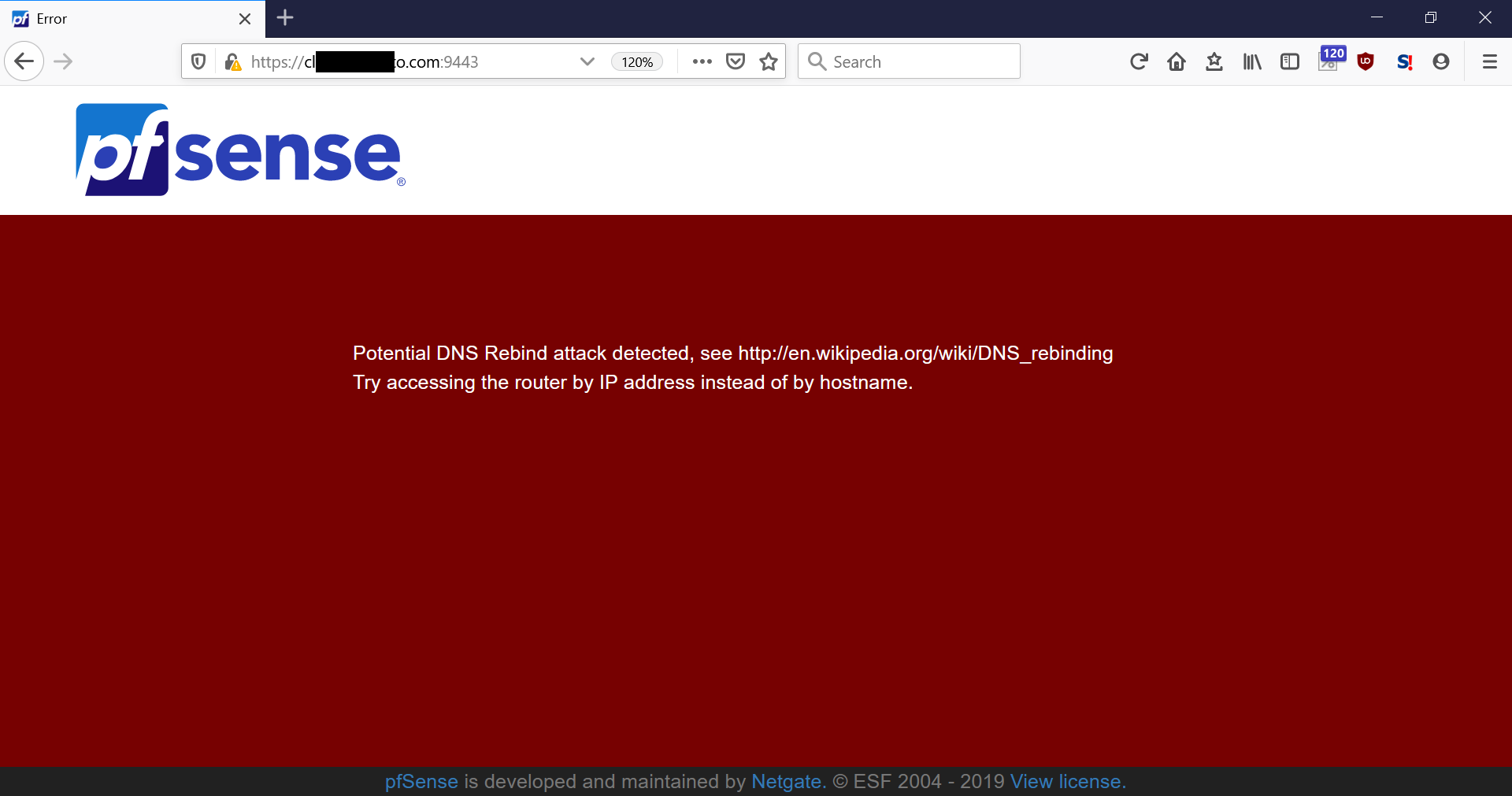
Hopefully this is a common and easily-addressed concern. I have a domain name that points to a server on my my home LAN behind pfSense. I need to be able to access this server both from my LAN and the internet. While I can access my server from the internet using mydomain.com, pfSense blocks the domain name when accessed from the LAN. Is there a pfSense DNS configuration I need to set up to point my domain name on the LAN, or other configuration detail I missed?
The helpful suggestion from pfSense below is not great, unless maybe I put in an IPv6 GUA?
-
How are you resolving the name exactly? Unless you directly asked pfsense for its own name, and it had to resolve or forward to resolve that name - and rfc1918 is returned then yes that would be a rebind issue.
If your going to ask some other NS for a name, it can not return rfc1918 without pfsense being told its ok.. See
https://docs.netgate.com/pfsense/en/latest/dns/dns-rebinding-protections.html
As to the info - its pointing to you to what rebind attack is.. But I agree it should prob also point to the above doc I linked too as well.
-
@johnpoz sorry if I didn't give enough detail. I'm trying to access a web server using a browser, tried both ports 80 and 8080. These ports are forwarded through NAT (IPv4) and firewall rule (IPv4 and IPv6), which are pointed to by mydomain.com. In the case of IPv6 it points directly to the server via prefix delegation.
I turned off the checkbox for DNS re-bind protection, but I suspect I must do something in the DNS resolver, to as you said, "tell pfSense it's OK".
-
So your on the inside trying to access public IP, hoping to get reflected back in - did you enable nat reflection?
What IP does this domain resolve to - public or rfc1918?
If its ipv6, are you on the same prefix with your client? You wold never touch pfsense at all if that is the case, etc.
The reason your getting rebind is last part of what I linked too.. Your hitting an IP of pfsense with a different name - to pfsense that is rebind. So your going to have to go into a bit more detail on your forwards, etc.
-
@johnpoz said in domain name pointing to home server blocked on LAN:
So your on the inside trying to access public IP, hoping to get reflected back in - did you enable nat reflection?
What IP does this domain resolve to - public or rfc1918?
If its ipv6, are you on the same prefix with your client? You wold never touch pfsense at all if that is the case, etc.
The reason your getting rebind is last part of what I linked too.. Your hitting an IP of pfsense with a different name - to pfsense that is rebind. So your going to have to go into a bit more detail on your forwards, etc.
Yes, that is what I'm trying to do. I had heard enabling NAT reflection was not always desirable for some reason, but it does sound like that is what I want. NAT reflection would be enabled in the firewall rules if I remember correctly? Currently NAT reflection is off. I am not yet familiar with pfSense's vast configurability, so feel free to point out the obvious.
mydomain.com resolves to my public IPv4 which is NAT'd to the server, it also resolves to my prefix-delegated IPv6 GUA address. I have confirmed that accessing the server using FTP from a mobile network does so by IPv6 GUA, and also that IPv4 works from the internet using NAT. It all works outside of my network.
If you can point me to the right section of the pfSense GUI or documentation as to what I need to do it would be appreciated, and thanks for your help thus far.
-
Well if your device is actually local have whatever.domain.tld locally just resolve to the local IP.. This is a simple host override setup.. No no nat reflection is needed.
As to internally for ipv6... That should never come into play, since I assume your devices are on the same ipv6 prefix.. So pfsense would never come into play when your device is internally.
Even if they were on different prefixes - it would be a simple firewall rule between your vlans to allow the access via ipv6.
If your trying to nat reflect for ftp - that is going to be problematic at best.. Due to how ftp uses a control channel and a data channel. And the direction of the connection is determined by if active or passive ftp, etc.
-
@johnpoz I need it to work for mobile devices that can be either on LAN or outside on the internet. Various services; web, FTP, media server. Android phones and Windows laptops. I don't think this is an unusual requirement.
-
Its not - when a device joins your network it normally gets handed your dns.. So now it resolves whatever.domain.tld to its local IP, lets call it 192.168.1.100
When the device is outside your network using say google or someone elses local dns and resolves whatever.domain.tld it would resolve the public IP 1.2.3.4, hit your wan IP and get forwarded in.
As to IPv6 - it is a global address, when device is local and on the same network it wouldn't ever talk to pfsense to get to that IP, since it would be on the same network/prefix. Even if your wifi mobile device is on prefix A, and what it wants to get to is on your other prefix B /64 - it would just route through pfsense..
What your doing is very basic shit yes.. But there is ZERO reason for nat reflection or thinking its a good idea to resolve some public IP your natting, when the device on your network... Just resolve it to the rfc1918 address.
What is problematic is if some device locally joins your network and wants to use google for dns, or doh or dot to cloudflare or something vs using the locally provided dns.. This is only a problem with IPv4 - with ipv6 wouldn't matter again.
For those sorts of clients to work, then yes you would have to setup nat reflection! And telling you that is going to be very problematic with ftp... Ftp and NAT just very problematic at even when your not trying to reflect!!
-
@johnpoz well, I don't need FTP to work locally, the problem I'm experiencing now is with http and https.