Newbie question regarding "Disable DNS Forwarder" setting
-
I am new to pfSense and networking in general. Despite this, I have learned so much from the generous people willing to share their knowledge in this forum. By following cookbook instructions, I've actually managed to get my system working for my needs but am troubled by my lack of understanding regarding certain settings. The one that has vexed me the most is the one found under System>General Setup>Disable DNS Forwarder>
 Do not use the DNS Forwarder/DNS Resolver as a DNS server for the firewall. I have read the description underneath this setting a hundred times. It reads:
Do not use the DNS Forwarder/DNS Resolver as a DNS server for the firewall. I have read the description underneath this setting a hundred times. It reads:"By default localhost (127.0.0.1) will be used as the first DNS server where the DNS Forwarder or DNS Resolver is enabled and set to listen on localhost, so system can use the local DNS service to perform lookups. Checking this box omits localhost from the list of DNS servers in resolv.conf."
I am having great difficulty grasping the meaning of this and do not really understand the consequences of enabling this setting. When this setting is enabled, how exactly does this change how the DNS Resolver functions?
Is the DNS Resolver actually "disabled" or is the behavior simply "altered". Does the DNS Resolver continue to resolve local host names? Does it continue to use local cache to resolve public host names?Part of my reason for trying to understand this setting is that enabling it appears to be required if I want to restrict which network interfaces DNS Resolver responds to queries from. This is under Services>DNS Resolver>General Settings>Network Interfaces. When the setting is unchecked, DNS Resolver insists that it respond to queries from either localhost or All network interfaces. I have my system configured so that it uses DNS Resolver (listening on port 53) for certain interfaces and DNS Forwarder (listening on port 54) for others. This has required me to enable the "Disable DNS Forwarder" setting for it to function. Again, I have essentially copied and modified cookbook instructions from other tutorials. Everything seems to work, but I really don't understand the why which really bothers me. I would appreciate any enlightenment that can be offered from the fine members of this forum.
-
@wanabe said in Newbie question regarding "Disable DNS Forwarder" setting:
"By default localhost (127.0.0.1) will be used as the first DNS server where the DNS Forwarder or DNS Resolver is enabled and set to listen on localhost, so system can use the local DNS service to perform lookups. Checking this box omits localhost from the list of DNS servers in resolv.conf."
This is a 'special case' situation. You shouldn't need to check this option.
As said, pfSense itself - all the services - needs a DNS, like your internal networks (LAN's).
These internal networks (LAN's) have there DNS severed assigned by DHCP or a static IP/gateway/DNS setup.
This option is for pfSense itself.
If you had another DNS server/cache somewhere on your network, you could send all 'pfSense' DNS requests to that device instead of using the build in Resolver (Or Forwarder).@wanabe said in Newbie question regarding "Disable DNS Forwarder" setting:
I have my system configured so that it uses DNS Resolver (listening on port 53) for certain interfaces and DNS Forwarder (listening on port 54) for others.
Why using both DNS systems for your networks ?
Using such a setup means often : the way that lead to such a 'solution' is wrong ....@wanabe said in Newbie question regarding "Disable DNS Forwarder" setting:
This has required me to enable the "Disable DNS Forwarder" setting for it to function
Yeah, because both bind also to the ::1 or 127.0.0.1 or localhost, so that pfSEnse itself can resolve, for populating the package list, looking for updates and other resolver stuff.
-
@Gertjan Thank you so much for your generous response. You have certainly supplied an important missing piece to the puzzle of my misunderstanding by explaining that pfSense itself needs a DNS like the other devices on my network. At first I didn't understand why until you later pointed out the need for pfSense to resolve for populating the package list, looking for updates, etc. That makes sense. The question I am left with now is what DNS system does pfSense use if this setting is enabled? My interpretation of the description is that both Forwarder AND Resolver are disabled for the localhost (pfSense).
@Gertjan said in Newbie question regarding "Disable DNS Forwarder" setting:
Why using both DNS systems for your networks ?
Using such a setup means often : the way that lead to such a 'solution' is wrong ....This is exactly why I am asking this question. I am concerned that my lack of understanding is leading me to configure things the wrong way. Allow me to explain. I am attempting to configure some devices to use a VPN service (Private Internet Access) and other devices to use my regular internet. I have modeled my configuration on the following tutorial:
https://nguvu.org/pfsense/pfsense-baseline-setup/
In that tutorial he makes use of three sets of DNS servers but I am only using two. He uses DNS Resolver for DNS queries on his VPN network and DNS Forwarder for his non-VPN traffic. I have chosen to do the opposite. I use Forwarder for my VPN and Resolver for my non-VPN traffic. I tried routing ALL of my DNS queries through my VPN using Resolver alone but the latency was unacceptable. I accept latency on the devices that I have assigned to the VPN. I do not claim that this is either the best or proper way of configuring this type of setup. However, it does appear to work. At least, I think it does. My DNS queries from my VPN assigned devices use DNS Forwarder (dnsmasq) and do not appear to leak and my non-VPN assigned devices seem to be resolving through the root servers using DNS Resolver (Unbound). I am not sure what pfSense itself is using given your explanation. I would be most interested in receiving feedback regarding this setup. If there is a better or more proper way to do this I would like to know. I am happy to provide more details including screenshots of my setup if anyone is interested.
-
@wanabe said in Newbie question regarding "Disable DNS Forwarder" setting:
That makes sense. The question I am left with now is what DNS system does pfSense use if this setting is enabled? My interpretation of the description is ...
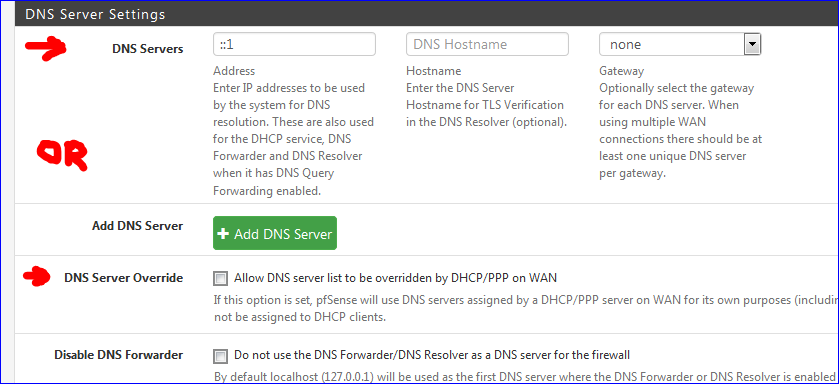
Actually, it's : one of these two option, whatever comes first, just above the "Disable DNS Forwarder"" option :
The mentioned tutorial is rather big : it's a (nearly) complete setup for a system with rather strict needs.
Note : I didn't test drive this tutorial. I missed the mention that using OpenDNS needs an account with OpenDNS and probably a DynDNS setup because OpenDNS needs to know your WAN IP at all times.Btw : this tutorial is probably executing the right steps, in the right order.
But still, you really should need to know what each step does, what it implies and how to test each step. Not knowing how to test each points is like flying that '737' and all goes well as long as there are no non-standard situations.Also : I'm using OpenVPN only myself the other way aground : as a server running on pfSense so I can access my pfSense remotely.
I never felt for the VPN hype that states that I should use a VPN service : I'm living in a free country, so I know for a fact that 'spying is all concentrated these days at a central place ( == how easy : the VPN service endpoints - and these same VPN services have a name and address of every connection ...) - so, no, I'm not going to pay money and make live more easier for them.
But, of course, just my 2 cents. -
@Gertjan Again, Thank you very much for your feedback.
@Gertjan said in Newbie question regarding "Disable DNS Forwarder" setting:
@wanabe said in Newbie question regarding "Disable DNS Forwarder" setting:
That makes sense. The question I am left with now is what DNS system does pfSense use if this setting is enabled? My interpretation of the description is ...
Actually, it's : one of these two option, whatever comes first, just above the "Disable DNS Forwarder"" option :
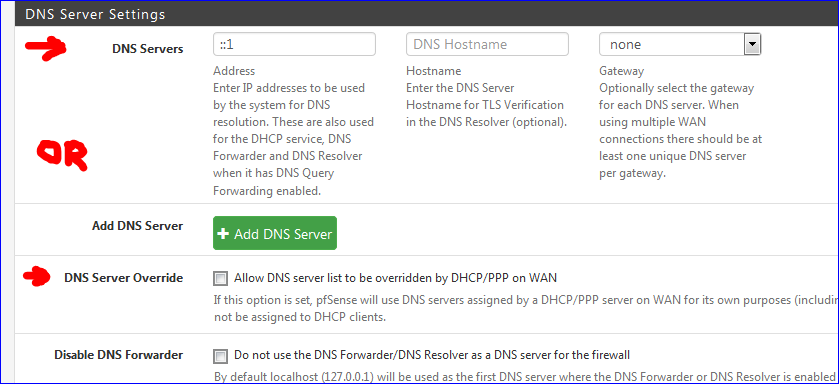
That certainly answers the question for my situation. In my configuration, the DNS server listed is the one provided by my VPN. DNS Forwarder (which is being used to manage queries from my VPN devices) requires that the DNS Server address be listed here. So that means that pfSense itself is using this server as well. I'm curious, though, what happens if no DNS Servers are listed AND DNS Server Override is unchecked. Any thoughts?
The mentioned tutorial is rather big : it's a (nearly) complete setup for a system with rather strict needs.
Note : I didn't test drive this tutorial. I missed the mention that using OpenDNS needs an account with OpenDNS and probably a DynDNS setup because OpenDNS needs to know your WAN IP at all times.Yes, a rather large tutorial. You can skip directly to his discussion regarding how he configures DNS Resolution which is about in the middle of the tutorial. I also do not use OpenDNS. My non-VPN devices are configured to use Resolver (Unbound) and query root servers directly (which I understand is the default behavior). I do NOT have DNS Query Forwarding enabled under DNS Resolver settings.
Btw : this tutorial is probably executing the right steps, in the right order.
But still, you really should need to know what each step does, what it implies and how to test each step. Not knowing how to test each points is like flying that '737' and all goes well as long as there are no non-standard situations.Very valid point and one often repeated by others. I am still actively learning how to test and vet my system. The tutorial provides some information in that regard but I am always interested in learning more. If anyone has any ideas how to "stress test" my set-up I would be most interested in learning
I never felt for the VPN hype that states that I should use a VPN service : I'm living in a free country, so I know for a fact that 'spying is all concentrated these days at a central place ( == how easy : the VPN service endpoints - and these same VPN services have a name and address of every connection ...) - so, no, I'm not going to pay money and make live more easier for them.
But, of course, just my 2 cents.I completely agree that a VPN is not going to protect you from being spied upon by a government entity. I am not using the VPN for that purpose. I am not engaged in any nefarious activity and have nothing to hide. I do engage in a lot of legal financial transactions. Although most take place over encrypted connections some do not. The VPN is cheap ($35/year) and can also be used on my mobile devices when I am forced to used public networks.
-
@wanabe said in Newbie question regarding "Disable DNS Forwarder" setting:
Although most take place over encrypted connections some do not.
Web sites or API connections (or any form of mail) that do not use TLS/SSL ? That wasn't been band from the net ??
You're right, if you have to handle financial stuff over 'clear lines' then you should use a VPN that has his end-part "in front of" the site hosting the non-TLS/SSL site. remember : when the traffic leaves the VPN supplier it will go clear over the net.