HA Config BIND DNS sync setup problem
-
Today i will do a swap again from the primary server, and look around it but i think yesterday there was nothing special in the logs.
bolvar
-
Sadly nothing in the logs.I saw in the firewall logs that i get a dns query from outside but it gets an answere.
-
i usually use dig to test my bind9, i don't have HA though
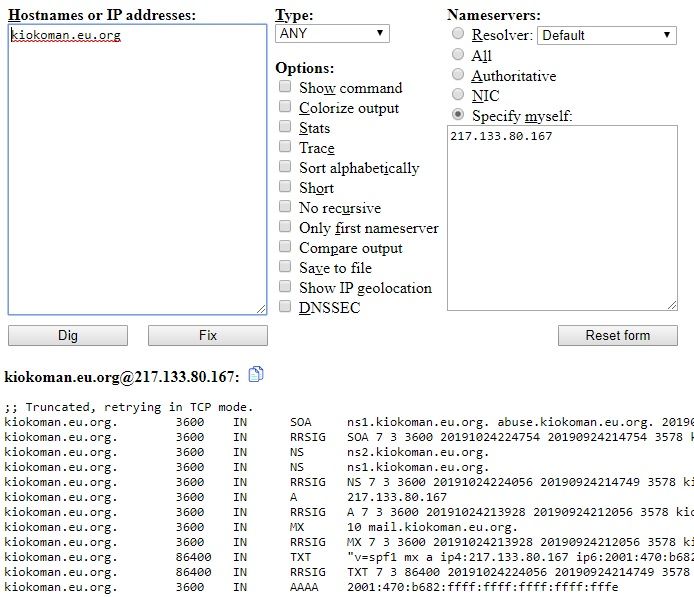
try with https://www.digwebinterface.com/
put your host and your ns ip (specify myself:)
and see if it's answering or not
something like this
-
Thanks but i cannot se how can this help me :D
An mxtoolbox is the same, and the problem is when i change to the secondary node, my dns is not respondig, cant test with this tool. My backup name server runing only. -
Here is the log:
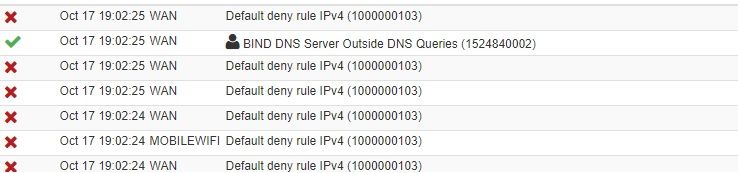
When i test from mxtoolbox i get a pass, but on the web page it says unreacheble.
Nobody has any ide what am i doing wrong? :/
-
Nobody expert on this problem?
The question is that im thinking on that now i have the ha cfg with one master server and in another site i have a slave cfg-ed.
In this case in the HA cfg i need to setup my backup node bind dns to master? -
I think i found the problem.
In slave state the zone file didnt get generated.
If i sate the state on my secondary node to master to zone file get generated, and mxtoolbox query workes.Someone can give advise about this?
-
you should check allow-transfer / allow-notify / allow-update statement, make a screenshot of your configuration if you can, just hide sensitive information, hard to tell without more info
-
Under Bind dns advanced future custom option i have allow notify and update,i need here the allow transfer to?
-
idk i don't have bind installed on pfsense, i have a dedicated server for bind9 and to transfer from my master to the slave i have it configured like this:
server 172.17.0.100 { keys { rndc-key; }; }; server 2001:470:b682:ffff:ffff:ffff:ffff:fffe { keys { rndc-key; }; }; .................. zone "kiokoman.eu.org" { type master; allow-transfer {151.3.106.211; 2001:470:b4e1:ffff:ffff:ffff:ffff:fffe; 192.168.10.202; 2001:470:26:5dc:ffff:ffff:ffff:fffd;}; also-notify {151.3.106.211; 2001:470:b4e1:ffff:ffff:ffff:ffff:fffe; 192.168.10.202; 2001:470:26:5dc:ffff:ffff:ffff:fffd;}; file "/etc/bind/external/pri.kiokoman.eu.org.signed"; auto-dnssec maintain; update-policy local; };on one of the slave:
server 172.17.0.100 { keys { rndc-key; }; }; server 2001:470:b682:ffff:ffff:ffff:ffff:fffe { keys { rndc-key; }; }; ............................... zone "kiokoman.eu.org" { type slave; masters {172.17.0.100; 2001:470:b682:ffff:ffff:ffff:ffff:fffe;}; file "/etc/bind/external/pri.kiokoman.eu.org.signed"; };under xfer-out.log and xfer-in.log ( channel xfer-in_file / channel xfer-out_file)
3c81316a0 192.168.10.202#56101/key rndc-key (kiokoman.home): view trusted: transfer of 'kiokoman.home/IN': IXFR ended 23-Jan-2020 20:13:25.430 client @0x7f53d0141340 192.168.10.202#43941/key rndc-key (2.168.192.IN-ADDR.ARPA): view trusted: transfer of '2.168.192.IN-ADDR.ARPA/IN': IXFR started: TSIG rndc-key (serial 2018046843 -> 2018046844) 23-Jan-2020 20:13:25.430 client @0x7f53d0141340 192.168.10.202#43941/key rndc-key (2.168.192.IN-ADDR.ARPA): view trusted: transfer of '2.168.192.IN-ADDR.ARPA/IN': IXFR ended 23-Jan-2020 20:56:05.485 client @0x7f53c81221e0 192.168.10.202#48387/key rndc-key (kiokoman.home): view trusted: transfer of 'kiokoman.home/IN': IXFR started: TSIG rndc-key (serial 2019092987 -> 2019092989) 23-Jan-2020 20:56:05.485 client @0x7f53c81221e0 192.168.10.202#48387/key rndc-key (kiokoman.home): view trusted: transfer of 'kiokoman.home/IN': IXFR endedif something go wrong you should check/rise verbosity of that log
-
After years, new internet provider, same problem, we have managed to switch our rack hosted servert to ha, and the same config worked perfect on the other isp network. So the problem is related to the internet provider, but saddly they say everything is ok...But its workes, so the config is okay, just need a good isp endpoint :D