AWS NAT. Private Subnet not originating traffic
-
I am having an issue within my AWS environment. I followed these instructions below to setup PFSense with AWS.
https://docs.netgate.com/pfsense/en/latest/solutions/aws-vpn-appliance/prepare-your-vpc.html
Following this guide you get to the page called Forwarding traffic from VPC subnets through the instance. It states.
**Common ways to manage private hosts
Allowing private hosts to connect to the Internet
To allow private hosts to be able to connect to the Internet, you can allow any traffic from the LAN in your firewall rules, there should be a rule like this in place by default.Next, set up NAT rules to cause addresses in the private subnet to be NATed to the IP address of the WAN interface:
Under the Firewall heading on the left, click on the NAT link.
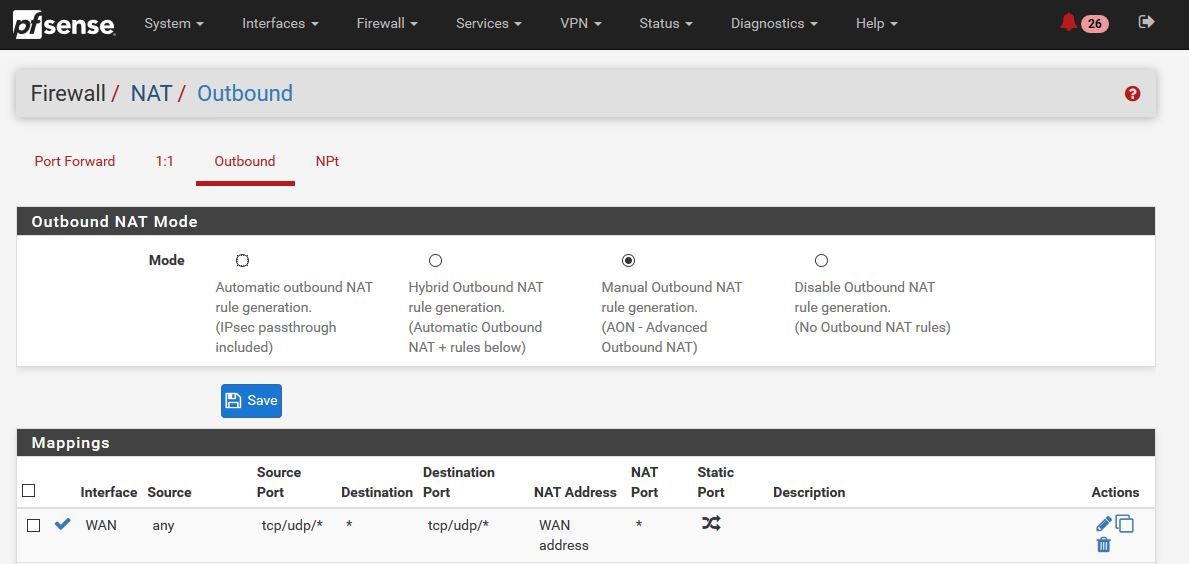
On the Outbound tab click the radio button for Manual Outbound NAT rule generation (AON - Advanced Outbound NAT)
Click the Save button.
Click on the Aliases link under the Firewall heading on the left.
Add your private subnet to the Networks_to_NAT alias.**
I have found this to be untrue. The ONLY way I have gotten private hosts to be able to connect to the internet is by manually setting up this Mapping under NAT. If I add my private host network for source it doesn't work either. It seems to be all or nothing. What am I doing wrong here?
Thanks!
-
Did you have to make any other changes? I have the same setup and can send a request from the private subnet, via pktcapture I can see it get through the LAN interface, out the WAN and the response back, but the client never gets the response back through the NAT.