Help with physical interfaces and VLANs
-
I'm on no cap.. So not something I would have to worry about.. I do about 2TB a month..
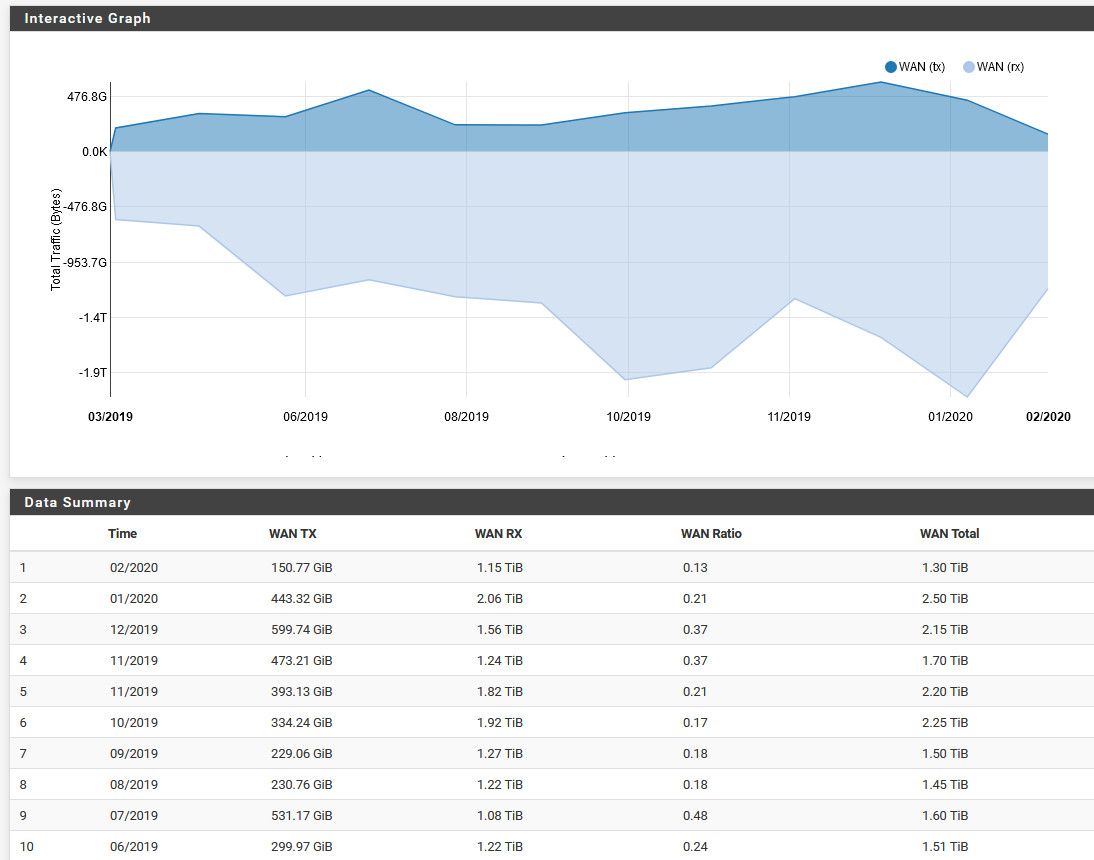
But curious what the next couple of months will be like - work just put us on work from home for next few weeks. Not sure how long that will last with all this virus stuff, sure hope it gets back to normal sooner vs later..
And all friends and family all going to be home more, etc. So sure my plex server will be seeing more traffic ;)
-
holy #)(U% that's alot! I'm in PA and the gov just shut down all schools for two weeks so I got a 6yo and 8yo who'll be home. My wife is also on work from home, she works for a hospital and they do not want anyone in the office who doesn't need to be.
-
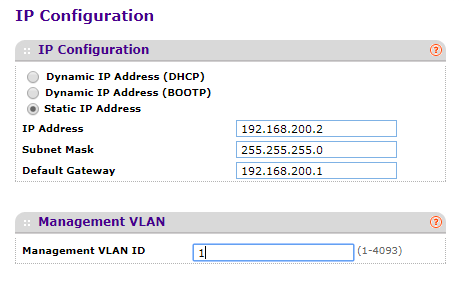
Next question as I try to draw my future topology for the 1000th time. Management switches - the IP's of those switches only matter to be able to manage them, correct? So if my main LAN and management vlan is vl100 192.168.200.0/24 - ALL my managed switches should have an IP in that subnet, correct? It doesn't matter what VLANs are assigned to ports on those switches as long as one is the trunk with vl100?
-
Generally the only layer 3 interface on a managed layer 2 switch is for management, yes.
-
@Derelict said in Help with physical interfaces and VLANs:
Generally the only layer 3 interface on a managed layer 2 switch is for management, yes.
So am I correct in thinking that as I go from my Pfsense box with 4 LAN interfaces, I can put each interface to separate ports on my main, lets call it my "BDM" 16 port managed switch. Then from that BDM switch, I'll go out one wire each to what I'll call my "IDE" managed switches.
-
Just put the management interfaces for your switches on a VLAN you can access from your management workstation.
Just like any other host you want to connect to.
You will find different capabilities in switching gear depending on what you get. Some have to be managed on the untagged VLAN, some allow you to set the VLAN of the management interface. it depends.
It all boils down to just setting an IP address, subnet mask, and default gateway of the management interface though. DHCP can be used if that fits with your network design.
-
Ok, in my Netgear I can set it to any vlan. So if my main lan is vl100, which will only have my main pc's on it, I should set that to 100 and give it the required IP info from vl100. And every other switch will be the same way with different IP's, most likely sequentially numbered... 192.168.200.3, 192.168.200.4, etc.
-
Depends. I do not work for Netgear. I would expect that to need to be set to VLAN 100 though if you are accessing that interface from VLAN 100.
-
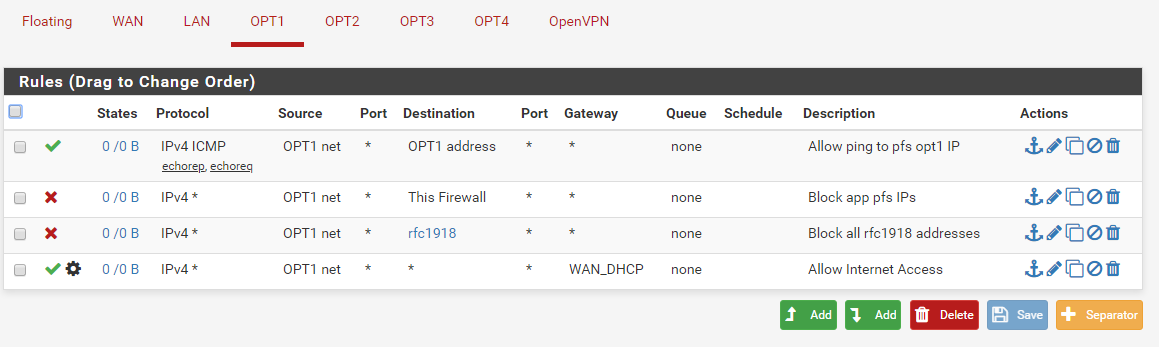
Now that I have my VLANs designated, I understand pfsense is default deny for everything. So for any VLAN that I only want to be able to access the internet, all I need is a pass rule from that VLAN net to WAN net ? Everything else to anything else is default blocked, correct?
-
No.
WAN net is not the internet. any is the internet.
You need to block the destinations you do not want them to have access to then pass everything else (the internet).
-
@Derelict said in Help with physical interfaces and VLANs:
No.
WAN net is not the internet. any is the internet.
You need to block the destinations you do not want them to have access to then pass everything else (the internet).
I would want everything blocked but the Internet so would I need to create a block rule to every other VLAN and then change WAN net to "any"?
-
Found some pointers from johnpoz in another thread.
How's this look:
-
fine if This Firewall and rfc1918 cover everything you don't want them to be able to access.
-
So I take it they are going to use external dns?
-
@Derelict said in Help with physical interfaces and VLANs:
fine if This Firewall and rfc1918 cover everything you don't want them to be able to access.
Well, I don't want them accessing anything on pfs other then ping their gw. And my alias of rfc1918 includes all private networks. I think that should work?
-
@johnpoz said in Help with physical interfaces and VLANs:
So I take it they are going to use external dns?
That is what I want to happen, I want dhcp to provide external dns servers from my isp. Whether or not I have it configured that way .... 'Nother story lol
-
Regarding DHCP on my VLANs, if everything is setup correctly on the interface, dhcp server, vlan, etc., should I be able to grab an address by plugging a PC directly into that interface on pfs? I am trying to troubleshoot not getting the correct DHCP address downstream. I am only getting the main LAN address after configuring my switch port VLANs. Obviously something is not correct or it'd be working. When I plug a pc directly into the interface, I do not get any address.
-
@BlankSpace said in Help with physical interfaces and VLANs:
Regarding DHCP on my VLANs, if everything is setup correctly on the interface, dhcp server, vlan, etc., should I be able to grab an address by plugging a PC directly into that interface on pfs? I am trying to troubleshoot not getting the correct DHCP address downstream. I am only getting the main LAN address after configuring my switch port VLANs. Obviously something is not correct or it'd be working. When I plug a pc directly into the interface, I do not get any address.
Well I got it working, not sure if it's how it's supposed to be but it works. Not a pfs issue - I changed the pvid of the device port and marked it untagged on the downstream switch to match the VLAN and it got an address from that VLAN.
-
I done did it now. I somehow locked myself out of pfs except for console. I was trying to troubleshoot why one of my VLANs (100) was not giving DHCP and I found that igb0 did not have VLAN100 assigned, it was just the physical NIC under interfaces. So when I assigned VLAN100 to igb0, I no longer could access pfs. I would assume that's because I have something screwed up downstream and its not tagging my port with vl100?
Any ideas how to remove the VLAN 100 from igb0 and just have igb0 be the physical interface using the console?
-
@BlankSpace said in Help with physical interfaces and VLANs:
I done did it now. I somehow locked myself out of pfs except for console. I was trying to troubleshoot why one of my VLANs (100) was not giving DHCP and I found that igb0 did not have VLAN100 assigned, it was just the physical NIC under interfaces. So when I assigned VLAN100 to igb0, I no longer could access pfs. I would assume that's because I have something screwed up downstream and its not tagging my port with vl100?
Any ideas how to remove the VLAN 100 from igb0 and just have igb0 be the physical interface using the console?
Got pfs reverted to igb0 being the physical nic and not VLAN100 by assigning the PVID on the switch to 100, reconnecting and changing it back.