Is this possible? 1 Internet connection, 2 networks, 2 gateways (default and VPN)
-
@Bob-Dig
I prefer not to assume. In that case, he'll need a virtual Ethernet cable.

-
Thank you all for your responses!
Let see if i can get to them all...
@JKnott , @Bob-Dig is correct. Only one Ethernet cable to the internet modem. The second "gateway" is a virtual gateway created by the VPNClient.
I have tried to setup firewall rules in the SEC interface with source SEC/any destination any/any use VPN gateway (GW2) but alas, this seems to fail the test when i connect to that network and tracert, I see my traffic goes over the default GW1 instead.
As for "machines" on that network, most are VMs and or Dockers. Only one physical device that I have connected becides the PFsense machine.
Long and short of it, I want my VMs and Dockers on the SEC network to route all traffic to the VPN tunnel. The main network uses manages inbound SSL traffic as well as other internal outbound traffic.
-
@Bob-Dig said in Is this possible? 1 Internet connection, 2 networks, 2 gateways (default and VPN):
Just "copy" the Default allow LAN to any rule to "SEC" if it not already exist there and then change the gateway under advanced to the VPN-Client, done.
This is everything you need to do, if the vpn-Client was setup correctly in the first place.
If it was not or is not connected, then traffic would go automatically out to WAN. For this to stop you have to tag that traffic and then block it with a special floating-rule.
-
@Bob-Dig said in Is this possible? 1 Internet connection, 2 networks, 2 gateways (default and VPN):
If it was not or is not connected, then traffic would go automatically out to WAN. For this to stop you have to tag that traffic and then block it with a special floating-rule.
Sorry, if im kinda newbish, but how would i go about this?
-
@rottonpeech said in Is this possible? 1 Internet connection, 2 networks, 2 gateways (default and VPN):
Sorry, if im kinda newbish, but how would i go about this?
You won't. You would first setup a working VPN-Client.
-
yes. i figured out what you meant, and i also found a few other things that did some magic (like not making a change, but re-saving and committing all my interfaces)
Now I see that all the interfaces are up, and the Client is up... but still cannot route across the VPN client.
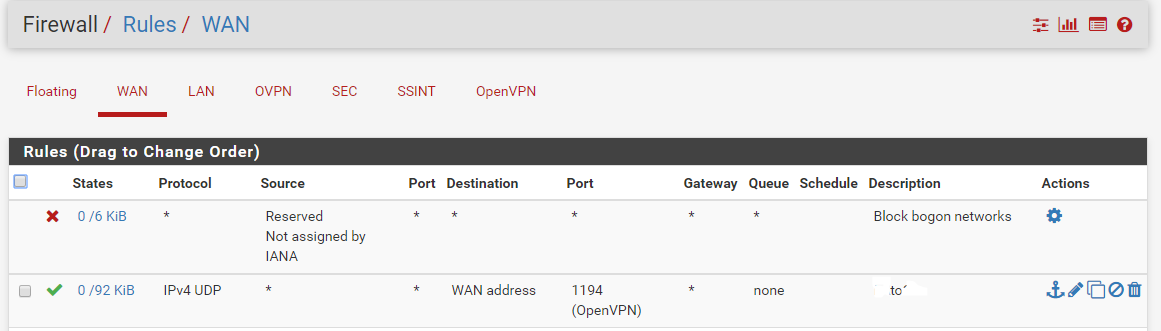
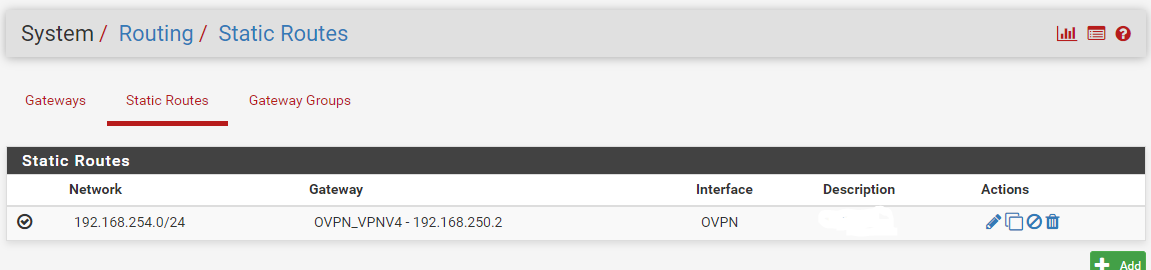
Here is a pic if it helps at all
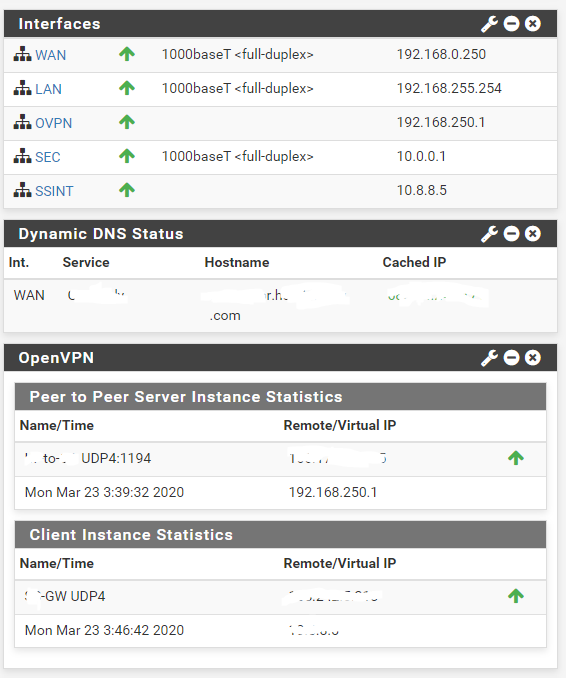
P.S. i also have a open VPN site-to-site that is working, where i am hosting the server side. 
-
Please show what you got under
FirewallNATOutboundMaybe you should do a much simpler setup in the beginning for testing with WAN, LAN, VPN-Client only.
-
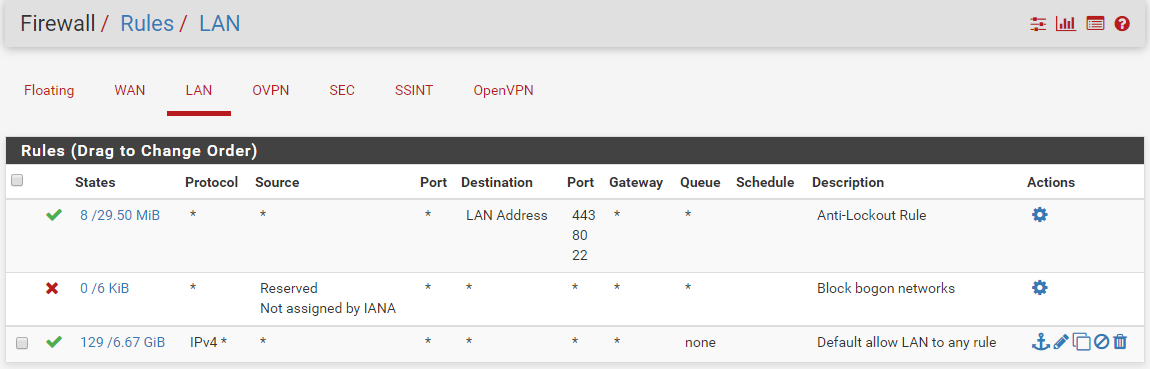
here are a few other screens
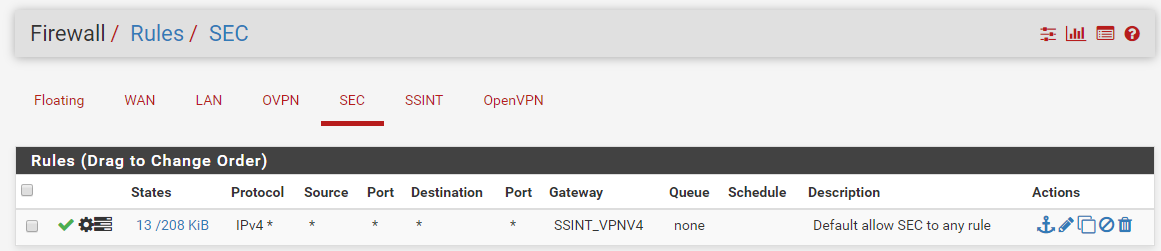
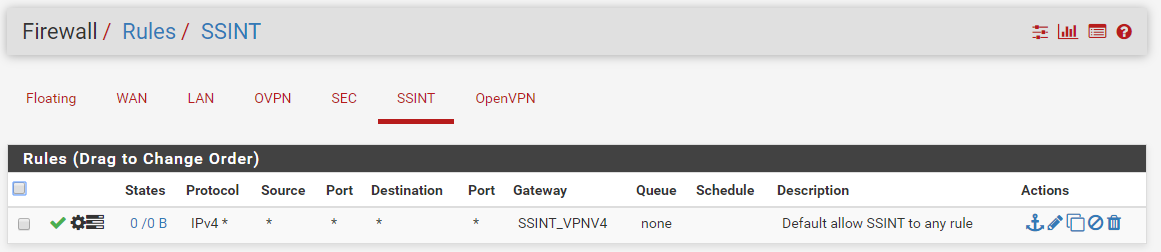
-
@rottonpeech Firewall NATO utbound still missing.
-
missed a few
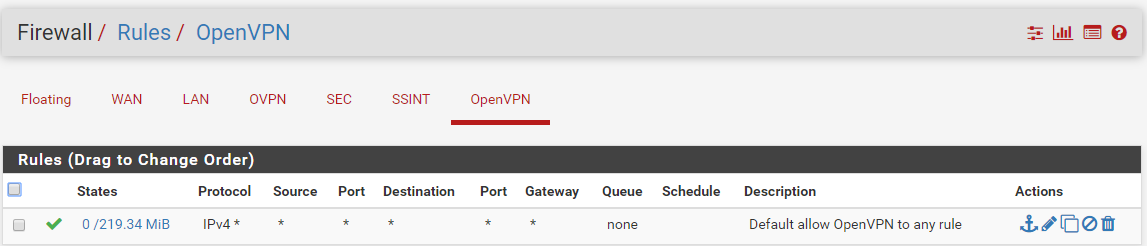
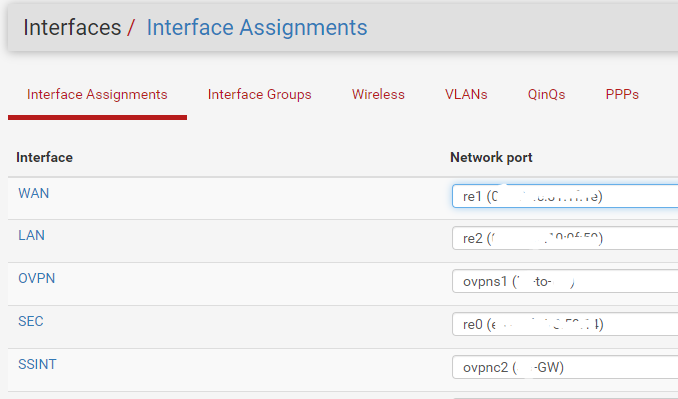
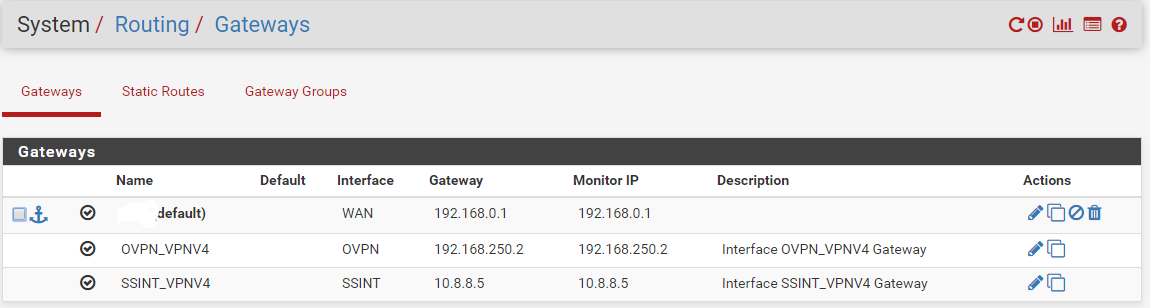
ok, i think thats about all of them
-
@Bob-Dig - Sorry, here it is
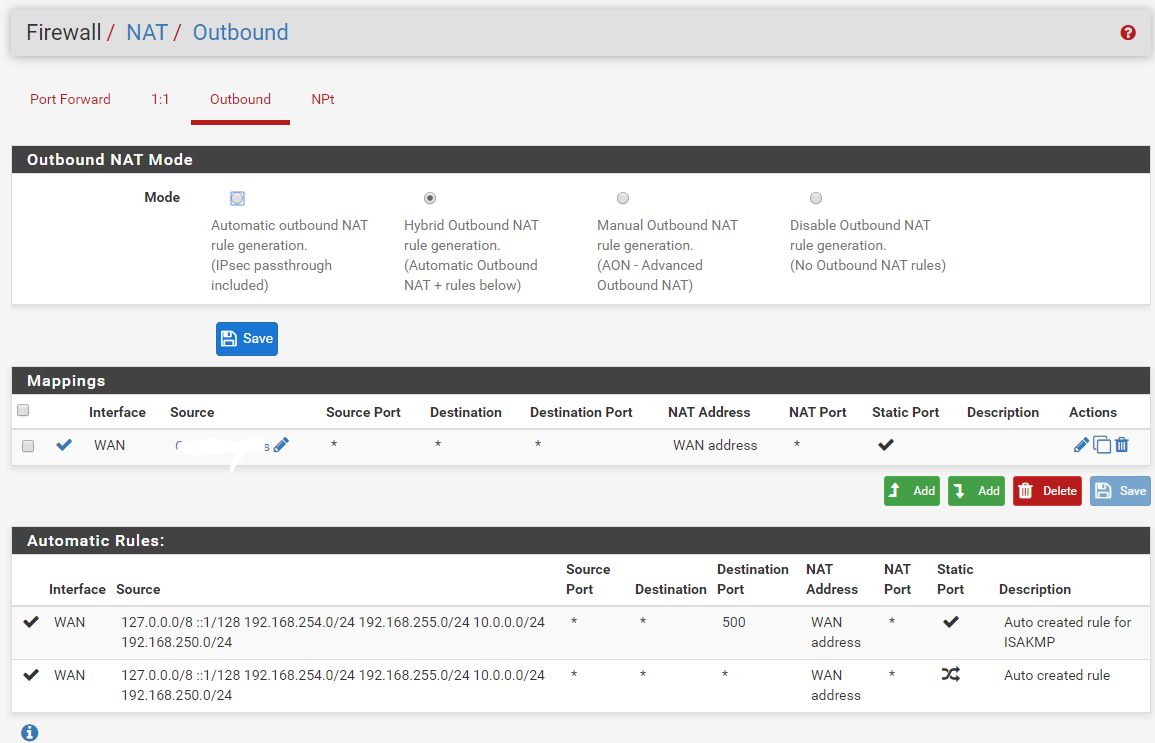
-
@rottonpeech And there is your problem. Your VPN Client Setup isn't complete. It was never working in the beginning.
-
@Bob-Dig
okay, im sorry.. what am i missing? its 4am here and i think my eyes are about to bleed from looking at this stuff so much today. :-\would you be so kind as to outline what im missing?
/beg


-
@rottonpeech For every subnet you want to be able to use the VPN-client, you need something like this:
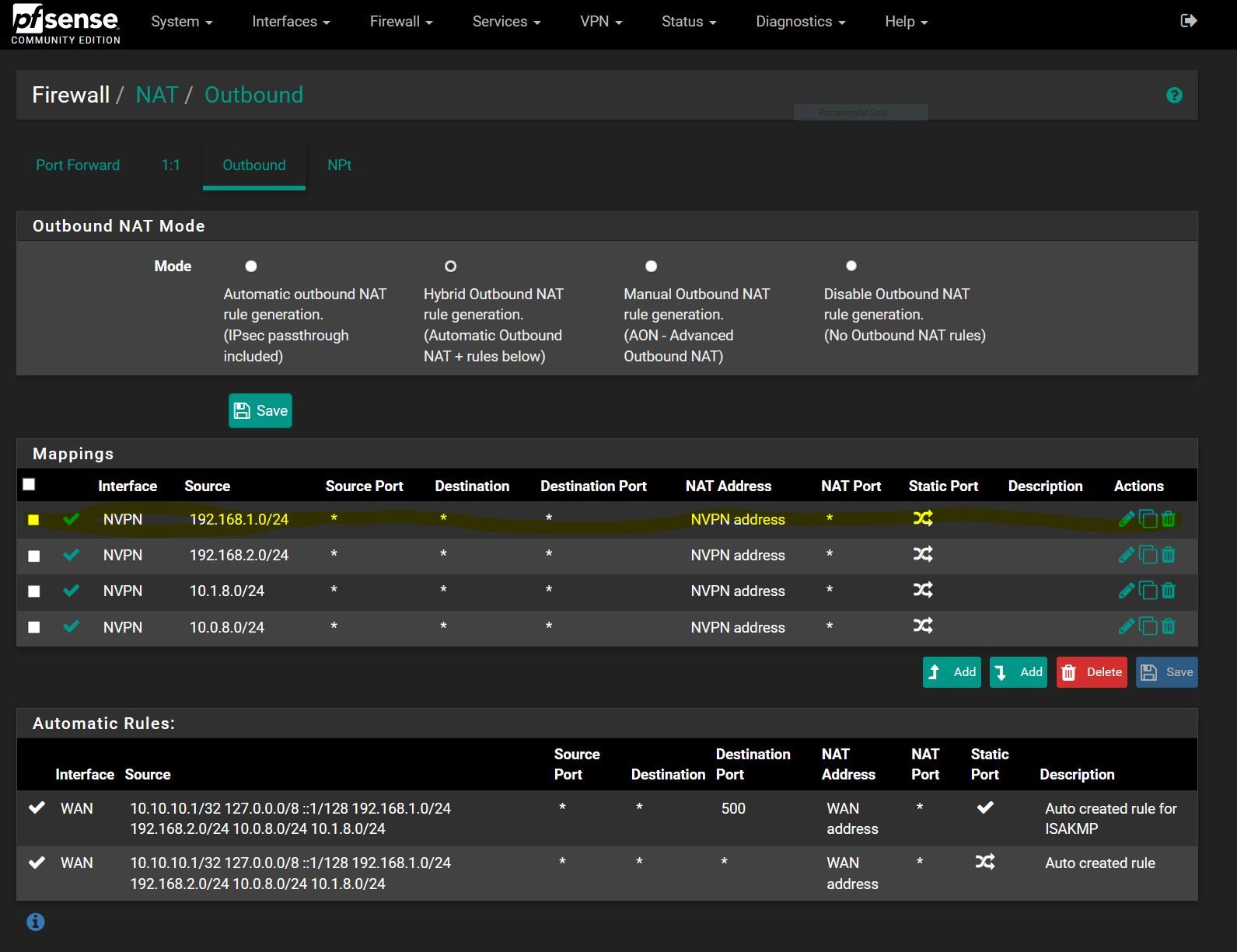
-
@Bob-Dig Well, I'll be a monkeys uncle... or maybe the monkey... definately the goofball who screwed it up.. You are AWESOME!
thank you very much for that!
-
@rottonpeech And the wan rule there in your picture, I don't think it is needed, although I am not sure.
Once your vpn client is working, it is easy like described in my first post.